Knowing that insider threats are a risk is one thing. Knowing how to fight them off...
- Home
- About Us
- Contact Us
- Register to apply for a free CISO2CISO Membership
- CISO2CISO Network
- CISO2CISO Services
- Sitemap
- Submit News
SecurityAffairs.com
Hyundai disclosed a data breach that impacted Italian and French car owners and clients who booked...
At least five members of civil society worldwide have been targeted with spyware and exploits developed...
April 12, 2023 By Pierluigi Paganini SAP fixed two critical bugs that affect the Diagnostics Agent and the...
AI company OpenAI launched a bug bounty program and announced payouts of up to $20,000 for...
Microsoft has addressed a zero-day in the Windows Common Log File System (CLFS) actively exploited in...
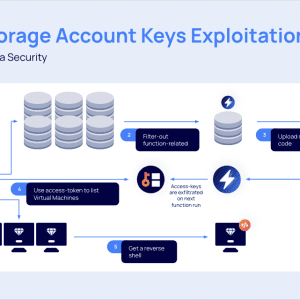
A flaw in Microsoft Azure could be exploited by attackers to gain access to storage accounts,...
Yum! Brands, the company that owns the KFC, Pizza Hut, and Taco Bell brands, disclosed a...
Apple released updates to backport patches addressing two actively exploited zero-day vulnerabilities in older iPhones, iPads, and...
A cyber attack paralyzed the water controllers for irrigating fields in the Jordan Valley that are...
US Cybersecurity and Infrastructure Security Agency (CISA) added two flaws in iPhones, Macs, and iPads to...
Belgian HR giant SD Worx was forced to shut down its IT infrastructure for its UK...
Sophos addressed three vulnerabilities in Sophos Web Appliance, including a critical flaw that can lead to...
Iran-linked APT group MERCURY is behind destructive attacks on hybrid environments masquerading as a ransomware operation. The...
Samsung employees have unwittingly leaked top secret data by providing them to the popular chatbot service...
The development team behind the vm2 JavaScript sandbox library addressed a critical Remote Code Execution vulnerability....
Privacy Overview This website uses cookies to improve your experience while you navigate through the website....
Andrey Shevlyakov, an Estonian national, was charged in the US with conspiracy and other charges related...
US CISA has added Veritas Backup Exec flaws, which were exploited in ransomware attacks, to its...
Apple released emergency security updates to address two actively exploited zero-day vulnerabilities impacting iPhones, Macs, and...
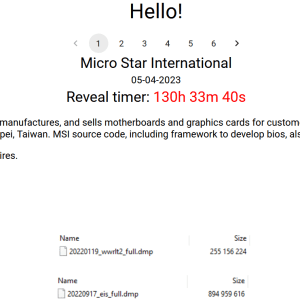
Multinational IT corporation MSI (Micro-Star International) confirms security breach after Money Message ransomware gang claimed the hack....
Microsoft announced it has taken legal action to disrupt the illegal use of copies of the...
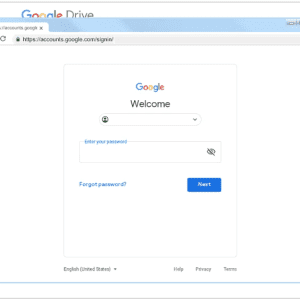
Experts warn that Telegram is becoming a privileged platform for phishers that use it to automate...
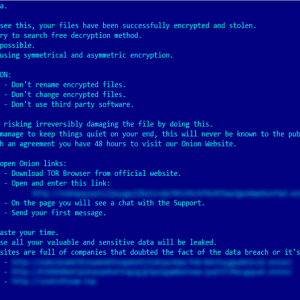
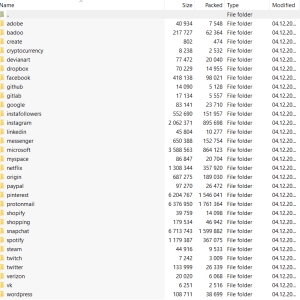
Ransomware gang Money Message claims to have hacked the Taiwanese multinational IT corporation MSI (Micro-Star International). Ransomware gang Money...
A digital identification tool provided by OCR Labs to major banks and government agencies leaked sensitive...
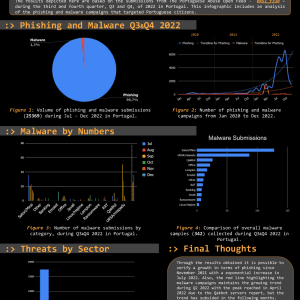
The Threat Report Portugal: H2 2022 compiles data collected on the malicious campaigns that occurred from...
Google’s Threat Analysis Group (TAG) warns of a North Korea-linked cyberespionage group tracked as ARCHIPELAGO. Google’s...
A series of vulnerabilities in multiple smart devices manufactured by Nexx can be exploited to remotely...
The eFile.com online service, which is authorized by the US Internal Revenue Service (IRS), was spotted...
HP would take up to 90 days to address a critical flaw, tracked as CVE-2023-1707, that...