Source: securityaffairs.com - Author: Pierluigi Paganini Police Service of Northern Ireland (PSNI) mistakenly shared sensitive data...
- Home
- About Us
- Contact Us
- Register to apply for a free CISO2CISO Membership
- CISO2CISO Network
- CISO2CISO Services
- Sitemap
- Submit News
SecurityAffairs.com
Source: securityaffairs.com - Author: Pierluigi Paganini The Balada Injector is still at large and still evading...
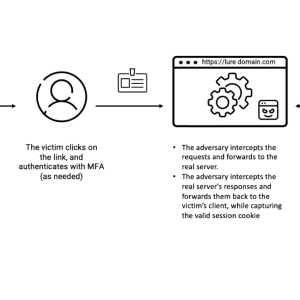
Source: securityaffairs.com - Author: Pierluigi Paganini Cloud account takeover scheme utilizing EvilProxy hit over 100 top-level...
Source: securityaffairs.com - Author: Pierluigi Paganini Google researcher Daniel Moghimi devised a new side-channel attack technique,...
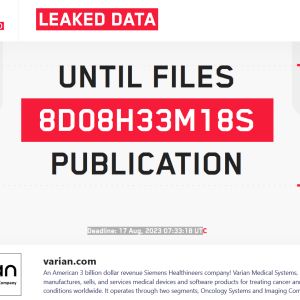
Source: securityaffairs.com - Author: Pierluigi Paganini The LockBit ransomware group threatens to leak medical data of...
Source: securityaffairs.com - Author: Pierluigi Paganini Microsoft Patch Tuesday security updates for August 2023 addressed 74...
Source: securityaffairs.com - Author: Pierluigi Paganini The UK Electoral Commission suffered a data breach that exposed...
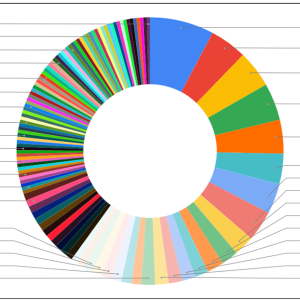
Source: securityaffairs.com - Author: Pierluigi Paganini Experts found 43 Android apps in Google Play with 2.5...
Source: securityaffairs.com - Author: Pierluigi Paganini Zoom changed its terms of service requiring users to allow...
Source: securityaffairs.com - Author: Pierluigi Paganini Two North Korea-linked APT groups compromised the infrastructure of the...
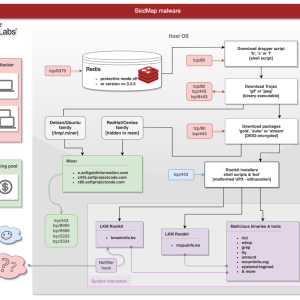
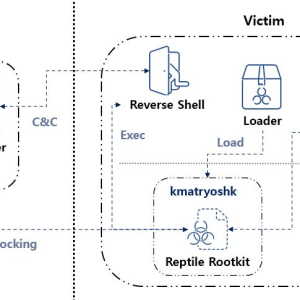
Source: securityaffairs.com - Author: Pierluigi Paganini A new campaign targets Redis servers, this time the malware...
Source: securityaffairs.com - Author: Pierluigi Paganini The FBI is warning about cyber criminals masquerading as NFT...
Source: securityaffairs.com - Author: Pierluigi Paganini Senior official reports a quadruple increase in ransomware attacks against...
Source: securityaffairs.com - Author: Pierluigi Paganini Microsoft announced it has addressed a critical flaw in its Power...
Source: securityaffairs.com - Author: Pierluigi Paganini The Colorado Department of Higher Education (CDHE) finally disclosed a...
Source: securityaffairs.com - Author: Pierluigi Paganini Privacy Overview This website uses cookies to improve your experience...
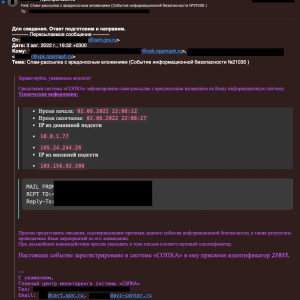
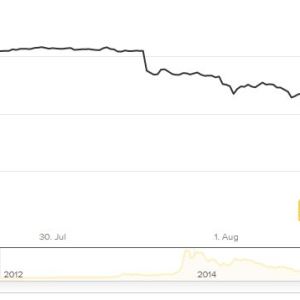
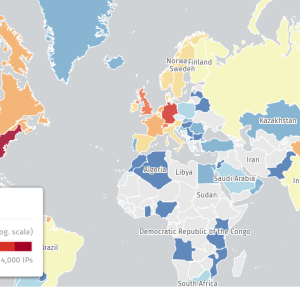
Source: securityaffairs.com - Author: Pierluigi Paganini Russia-linked APT group BlueCharlie was observed changing its infrastructure in...
Source: securityaffairs.com - Author: Pierluigi Paganini Researchers observed threat actors that are using an open-source rootkit...
Source: securityaffairs.com - Author: Pierluigi Paganini Researchers discovered a vulnerability in PaperCut NG/MF print management software...
Source: securityaffairs.com - Author: Pierluigi Paganini A cyberattack has disrupted the computer systems of multiple hospitals...
Source: securityaffairs.com - Author: Pierluigi Paganini A married couple from New York pleaded guilty this week...
Source: securityaffairs.com - Author: Pierluigi Paganini Researchers discovered a new set of malicious packages on the...
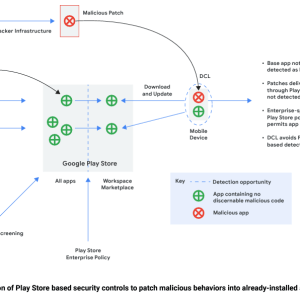
Source: securityaffairs.com - Author: Pierluigi Paganini Threat actors rely on the ‘versioning’ technique to evade malware...
Source: securityaffairs.com - Author: Pierluigi Paganini CISA, the FBI, and NSA, along with Five Eyes cybersecurity...
Source: securityaffairs.com - Author: Pierluigi Paganini Experts warn that decommissioned medical infusion pumps sold via the...
Source: securityaffairs.com - Author: Pierluigi Paganini The OWASP Top 10 for LLM (Large Language Model) Applications version...
Source: securityaffairs.com - Author: Pierluigi Paganini Researchers discovered a bypass for a recently fixed actively exploited...
Source: securityaffairs.com - Author: Pierluigi Paganini Russia-linked APT29 group targeted dozens of organizations and government agencies...
Source: securityaffairs.com - Author: Pierluigi Paganini Researchers warn that hundreds of Citrix servers have been hacked...
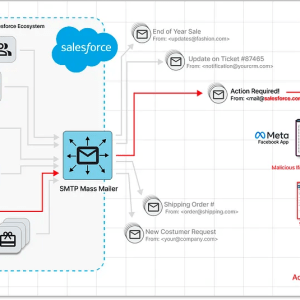
Source: securityaffairs.com - Author: Pierluigi Paganini Experts spotted a spear-phishing Facebook campaign exploiting a zero-day vulnerability...