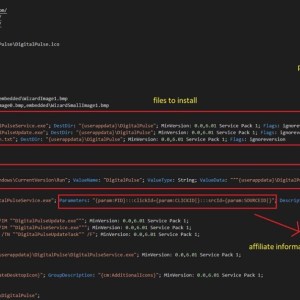
Source: securityaffairs.com - Author: Pierluigi Paganini Researchers discovered a massive campaign that delivered a proxy server...
- Home
- About Us
- Contact Us
- Register to apply for a free CISO2CISO Membership
- CISO2CISO Network
- CISO2CISO Services
- Sitemap
- Submit News
SecurityAffairs.com
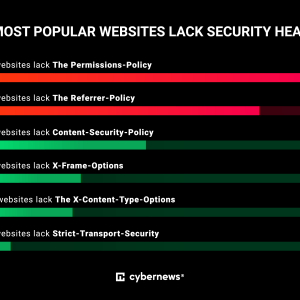
Source: securityaffairs.com - Author: Pierluigi Paganini The world’s most popular websites lack basic cybersecurity hygiene, an...
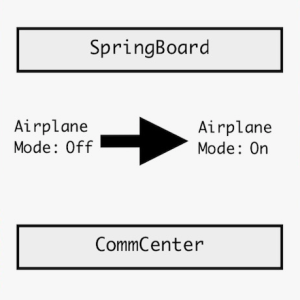
Source: securityaffairs.com - Author: Pierluigi Paganini Researchers detailed a new exploit for Apple iOS 16 that...
Source: securityaffairs.com - Author: Pierluigi Paganini Cleaning products manufacturer Clorox Company announced that it has taken...
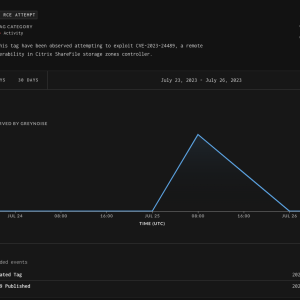
Source: securityaffairs.com - Author: Pierluigi Paganini US CISA added critical vulnerability CVE-2023-24489 in Citrix ShareFile to...
Source: securityaffairs.com - Author: Pierluigi Paganini A phishing campaign employing QR codes targeted a leading energy...
Source: securityaffairs.com - Author: Pierluigi Paganini Ivanti Avalanche EMM product is impacted by two buffer overflows...
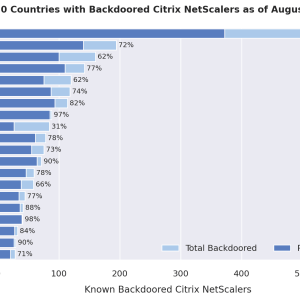
Source: securityaffairs.com - Author: Pierluigi Paganini A threat actor has compromised roughly 2,000 Citrix NetScaler servers...
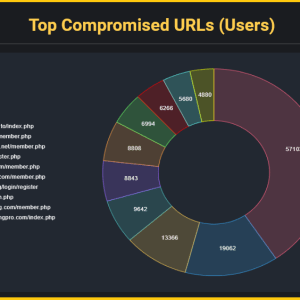
Source: securityaffairs.com - Author: Pierluigi Paganini Researchers discovered credentials associated with cybercrime forums on roughly 120,000...
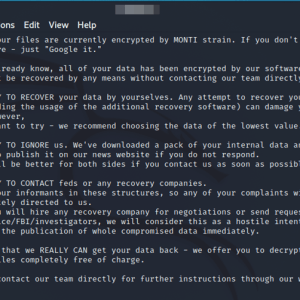
Source: securityaffairs.com - Author: Pierluigi Paganini Monti Ransomware operators returned, after a two-month pause, with a...
Source: securityaffairs.com - Author: Pierluigi Paganini Researchers found several flaws in the ScrutisWeb ATM fleet monitoring...
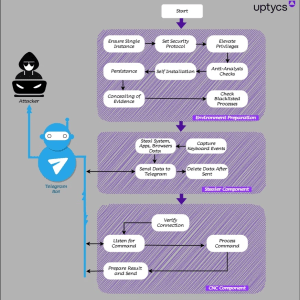
Source: securityaffairs.com - Author: Pierluigi Paganini QwixxRAT is a new Windows remote access trojan (RAT) that...
Source: securityaffairs.com - Author: Pierluigi Paganini Experts warn of ongoing attacks, dubbed Xurum, targeting e-commerce websites...
Source: securityaffairs.com - Author: Pierluigi Paganini The Colorado Department of Health Care Policy & Financing (HCPF)...
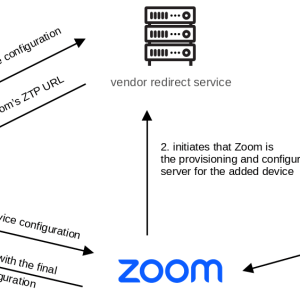
Source: securityaffairs.com - Author: Pierluigi Paganini Multiple flaws in AudioCodes desk phones and Zoom’s Zero Touch...
Source: securityaffairs.com - Author: Pierluigi Paganini Multiple vulnerabilities in CyberPower PowerPanel Enterprise DCIM platform and Dataprobe...
Source: securityaffairs.com - Author: Pierluigi Paganini 16 vulnerabilities in Codesys products could result in remote code...
Source: securityaffairs.com - Author: Pierluigi Paganini Privacy Overview This website uses cookies to improve your experience...
Source: securityaffairs.com - Author: Pierluigi Paganini The DHS’s CSRB will review cloud security practices following recent...
Source: securityaffairs.com - Author: Pierluigi Paganini A joint operation conducted by European and U.S. law enforcement...
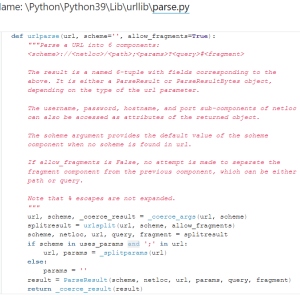
Source: securityaffairs.com - Author: Pierluigi Paganini A severe vulnerability in the Python URL parsing function can...
Source: securityaffairs.com - Author: Pierluigi Paganini UK govt contractor MPD FM left an open instance that...
Source: securityaffairs.com - Author: Pierluigi Paganini Threat actors employed a new variant of the SystemBC malware,...
Source: securityaffairs.com - Author: Pierluigi Paganini API (or Application Programming Interface) is a ubiquitous term in...
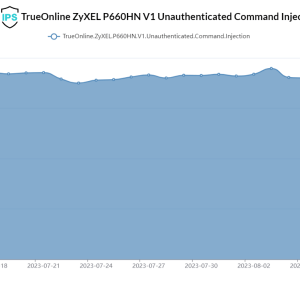
Source: securityaffairs.com - Author: Pierluigi Paganini Researchers warn that the Gafgyt botnet is actively exploiting a...
Source: securityaffairs.com - Author: Pierluigi Paganini Germany’s Federal Office for the Protection of the Constitution (BfV)...
Source: securityaffairs.com - Author: Pierluigi Paganini Experts warn that a new info-stealer named Statc Stealer is infecting Windows...
Source: securityaffairs.com - Author: Pierluigi Paganini The U.S. Cybersecurity & Infrastructure Security Agency (CISA) observed a...
Source: securityaffairs.com - Author: Pierluigi Paganini US CISA added zero-day vulnerability CVE-2023-38180 affecting .NET and Visual...
Source: securityaffairs.com - Author: Pierluigi Paganini The US Government House this week launched an Artificial Intelligence...