Source: www.schneier.com - Author: Bruce Schneier HomeBlog Comments Who? • November 21, 2024 7:29 AM Because...
- Home
- About Us
- Contact Us
- Register to apply for a free CISO2CISO Membership
- CISO2CISO Network
- CISO2CISO Services
- Sitemap
- Submit News
Schneier on Security
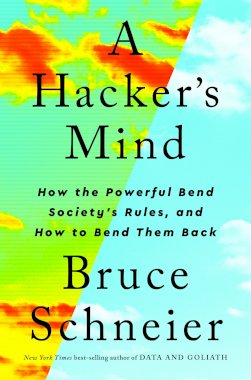
Source: www.schneier.com - Author: Bruce Schneier HomeBlog Steve Bellovin’s Retirement Talk Steve Bellovin is retiring. Here’s...
Source: www.schneier.com - Author: Bruce Schneier Interesting analysis: Although much attention is given to sophisticated, zero-click...
Source: www.schneier.com - Author: Bruce Schneier Zero-day vulnerabilities are more commonly used, according to the Five...
Source: www.schneier.com - Author: Bruce Schneier About Bruce SchneierI am a public-interest technologist, working at the...
Source: www.schneier.com - Author: Bruce Schneier Stuart Schechter makes some good points on the history of...
Source: www.schneier.com - Author: Bruce Schneier Clive Robinson • November 14, 2024 11:01 AM @ Bruce,...
Source: www.schneier.com - Author: Bruce Schneier Menu Blog Newsletter Books Essays News Talks Academic About Me...
Source: www.schneier.com - Author: Bruce Schneier I’ve been writing about the problem with lawful-access backdoors in...
Source: www.schneier.com - Author: Bruce Schneier About Bruce SchneierI am a public-interest technologist, working at the...
Source: www.schneier.com - Author: Bruce Schneier The Open Source Initiative has published (news article here) its...
Source: www.schneier.com - Author: Bruce Schneier Interesting research: “Hacking Back the AI-Hacker: Prompt Injection as a...
Source: www.schneier.com - Author: Bruce Schneier Really interesting research: “An LLM-Assisted Easy-to-Trigger Backdoor Attack on Code...
Source: www.schneier.com - Author: Bruce Schneier Microsoft is warning Azure cloud users that a Chinese controlled...
Source: www.schneier.com - Author: Bruce Schneier I’ve been writing about the possibility of AIs automatically discovering...
Source: www.schneier.com - Author: Bruce Schneier About Bruce SchneierI am a public-interest technologist, working at the...
Source: www.schneier.com - Author: Bruce Schneier About Bruce SchneierI am a public-interest technologist, working at the...
Source: www.schneier.com - Author: Bruce Schneier This is a good point: Part of the problem is...
Source: www.schneier.com - Author: Bruce Schneier Way back in 2018, people noticed that you could find...
Source: www.schneier.com - Author: Bruce Schneier Excellent read. One example: Consider the case of basic public...
Source: www.schneier.com - Author: Bruce Schneier Schneier on Security Menu Blog Newsletter Books Essays News Talks...
Source: www.schneier.com - Author: Bruce Schneier HomeBlog Comments Uwe • October 28, 2024 12:37 PM the...
Source: www.schneier.com - Author: Bruce Schneier About Bruce SchneierI am a public-interest technologist, working at the...
Source: www.schneier.com - Author: Bruce Schneier Researchers at Google have developed a watermark for LLM-generated text....
Source: www.schneier.com - Author: Bruce Schneier An advocacy groups is filing a Fourth Amendment challenge against...
Source: www.schneier.com - Author: Bruce Schneier HomeBlog Comments Who? • October 22, 2024 9:48 AM My...
Source: www.schneier.com - Author: B. Schneier Tax farming is the practice of licensing tax collection to...
Source: www.schneier.com - Author: Bruce Schneier About Bruce SchneierI am a public-interest technologist, working at the...
Source: www.schneier.com - Author: Bruce Schneier HomeBlog The Wall Street Journal is reporting that the CEO...
Source: www.schneier.com - Author: Bruce Schneier About Bruce SchneierI am a public-interest technologist, working at the...