Less Is More: Why One Antivirus Software Is All You Need Personal devices and the information...
- Home
- About Us
- Contact Us
- Register to apply for a free CISO2CISO Membership
- CISO2CISO Network
- CISO2CISO Services
- Sitemap
- Submit News
McAfee
5 Ways to Protect Your Online Privacy When you open your laptop or your mobile device, what...
All-New Ransomware Coverage Opens Up the Path to Recovery Our all-new ransomware coverage is now available,...
7 Tips to Protect Your Smartphone from Getting Hacked There’s little rest for your hard-working smartphone....
Help! I Think My Phone’s Been Hacked “My phone’s been hacked!” Words you probably don’t want...
Credit Lock and Credit Freeze: Which Service Is Best for You? Both! Are you hoping to...
The Optus Data Breach – Steps You Can Take to Protect Yourself Optus, one of Australia’s...
McAfee Secure VPN: Now with WireGuard for Faster Speeds and Enhanced Stability McAfee’s Secure VPN now...
How Do Hackers Hack Phones and How Can I Prevent It? How do hackers hack phones?...
4 Easy Things You Can Do Today to Improve Your Cybersecurity Happy Cybersecurity Awareness Month! ...
See Yourself in Cyber – Five Quick Ways You Can Quickly Get Safer Online With “See...
What Is Smishing? Here’s How to Spot Fake Texts and Keep Your Info Safe Your phone...
57 Million Users Compromised in Uber Leak: Protect Your Digital Privacy and Identity “I’ll just Uber...
Digital Estate Planning – What to Do With Your Digital Assets While we’re enjoying the fruits...
What is Spyware? No one likes the feeling that someone is looking over their shoulder when...
True Security Requires a Holistic Approach In the eyes of hackers, scammers, and thieves, your online...
Toyota Data Breach Exposes Customer Data – What You Can Do to Protect Yourself Automobile manufacturer...
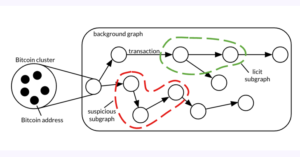
New Malicious Clicker found in apps installed by 20M+ users Authored by SangRyol Ryu Cybercriminals are...
“This Connection Is Not Private” – What it Means and How to Protect Your Privacy Have...
How to Tell Whether a Website Is Safe or Unsafe It’s important to know that not...
Guide: Protecting Your Digital Identity People in their 20s and 30s are losing it online. And...
What Are Tailgating Attacks and How to Protect Yourself From Them Whether you’re spending time on...
What Is Smishing and Vishing, and How Do You Protect Yourself Smishing and vishing are scams...
How to Spot Fake Login Pages Have you ever come across a website that just didn’t...
Top Signs of Identity Theft When it comes to identity theft, trust your gut when something doesn’t feel right. Follow...
Protect yourself from scams this Diwali It’s Diwali, a time of light, a time of togetherness,...
Ransomware Masquerading as Microsoft Update Targets Home Computers A new ransomware threat is currently sweeping its...
Staying safer online from phishing and other attacks When you’re online, the world is at your fingertips....
For some, accounting is more than just spreadsheets! Vernon’s McAfee Journey Vernon has been our Manager...
How Often Should You Change Your Passwords? When it comes to passwords, most of us would...