Suspected Russian Money Launderer Extradited to US Man allegedly handled over $400,000 in Ryuk proceedsLeer más...
- Home
- About Us
- Contact Us
- Register to apply for a free CISO2CISO Membership
- CISO2CISO Network
- CISO2CISO Services
- Sitemap
- Submit News
Info Security Magazine
Researchers Find 35 Adware Apps on Google Play Apps have millions of downloads, says BitdefenderLeer más...
Critical Infrastructure at Risk as Thousands of VNC Instances Exposed Researchers find many deployments have authentication...
New Study Reveals Serious Cyber Insurance Shortfalls Most companies do not have enough coverage to recover...
Three Extradited from UK to US on $5m BEC Charges Nigerian nationals accused of targeting US...
#DEFCON: CISA Director Praises Congress and International Cybersecurity Cooperation Jen Easterly discusses the progress and challenges...
#DEFCON: How Sanctions Impact Internet Operators Following government sanctions against Russia, Internet providers have had to...
Dutch Authorities Arrest Tornado Cash Developer Following US Sanctions on Crypto Mixer Firm The Financial Advanced...
Luckymouse Uses Compromised MiMi Chat App to Target Windows and Linux Systems The news comes from...
Software Patches Flaw on macOS Could Let Hackers Bypass All Security Levels After deploying the initial...
Android Banking Trojan SOVA Comes Back With New Features Including Ransomware SOVA v4 features new capabilities...
CISA Unveils Cybersecurity Toolkit to Shield US Elections From Hackers The toolkit protects election infrastructure targeted...
Recovery From NHS Ransomware Attack May Take a Month Managed service provider Advanced publishes update on...
Zeppelin Ransomware Victims May Need Multiple Decryption Keys CISA issues new alert about RaaS variantLeer más...
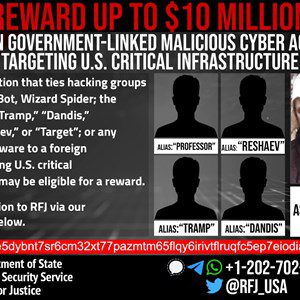
US Unmasks Suspected Conti Ransomware Actor State Department offers $10m reward for info on notorious groupLeer...
#BHUSA: What has Changed in the Post-Stuxnet Era? Investigative journalist Kim Zetter explains that Stuxnet continues...
#BHUSA: Bug Bounty Botox – Why You Need a Security Process First Katie Moussouris explains why...
#BHUSA: Failure to Challenge is a Social Engineering Risk The UK Ministry of Defence is actively...
SolidBit Ransomware Group Recruiting New Affiliates on Dark Web 20% of the earned profit from the...
Meta Tests Encrypted Backups and End-to-End Encryption in Facebook Messenger Meta is also introducing an encrypted...
#BHUSA: New Open Source Group Set to Streamline Threat Detection New open source project set to...
#BHUSA: Russia’s Wiper Attacks Against Ukraine Detailed According to researchers, Russia is rolling out a growing...
#BHUSA: The Cyber Safety Review Board Outlines Log4j Lessons The CSRB concluded that the initial disclosure...
Emotet Tops List of July’s Most Widely Used Malware The Emotet botnet continues to evolve and...
Cyber-criminals Shift From Macros to Shortcut Files to Hack Business PCs, HP Reports The report shows...
DeathStalker’s VileRAT Continues to Target Foreign and Crypto Exchanges The campaign is not only ongoing, the...
Suspected $3m Romance Scammer Extradited to Japan Interpol warns of growing role of money mulesLeer más...
Dozens of universities are being hit with a coordinated cyber-attack that uses news of the Omicron...
The board of directors at Korean electronics company LG Electronics has approved the acquisition of Israel-based vehicle cybersecurity...