Source: www.govinfosecurity.com - Author: 1 Governance & Risk Management , Patch Management , Vulnerability Assessment &...
- Home
- About Us
- Contact Us
- Register to apply for a free CISO2CISO Membership
- CISO2CISO Network
- CISO2CISO Services
- Sitemap
- Submit News
govinfosecurity.com
Source: www.govinfosecurity.com - Author: 1 Cyberwarfare / Nation-State Attacks , Fraud Management & Cybercrime , Government...
Source: www.govinfosecurity.com - Author: 1 Endpoint Security , Governance & Risk Management , Internet of Things...
Source: www.govinfosecurity.com - Author: 1 Governance & Risk Management , Privacy , Standards, Regulations & Compliance...
Source: www.govinfosecurity.com - Author: 1 Breach Notification , Governance & Risk Management , Privacy Hospital Chain...
Source: www.govinfosecurity.com - Author: 1 Cybercrime , Fraud Management & Cybercrime , Malware as-a-Service New Variant...
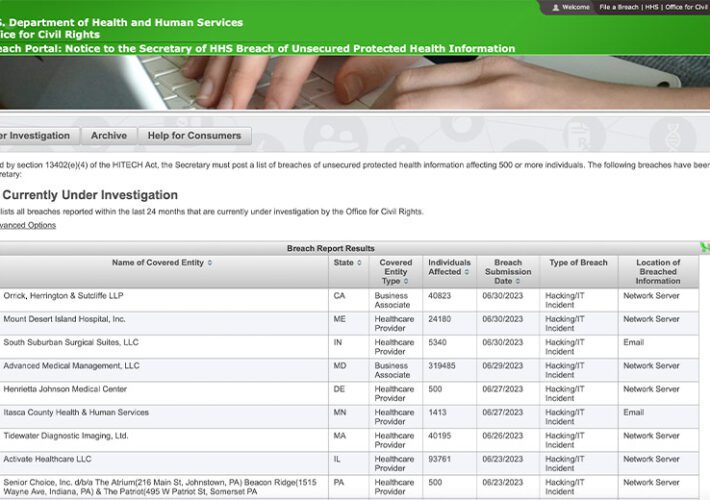
Source: www.govinfosecurity.com - Author: 1 Breach Notification , Fraud Management & Cybercrime , Governance & Risk...
Source: www.govinfosecurity.com - Author: 1 3rd Party Risk Management , Fraud Management & Cybercrime , Governance...
Source: www.govinfosecurity.com - Author: 1 Cybercrime , Fraud Management & Cybercrime , Geo Focus: Asia Researcher...
Source: www.govinfosecurity.com - Author: 1 Governance & Risk Management , Government , Industry Specific Enhanced Police...
Source: www.govinfosecurity.com - Author: 1 Fraud Management & Cybercrime , Healthcare , Industry Specific Hacktivist-Led DDoS...
Source: www.govinfosecurity.com - Author: 1 Cyberwarfare / Nation-State Attacks , Fraud Management & Cybercrime , Social...
Source: www.govinfosecurity.com - Author: 1 Anders Norremo VP of Third Party Risk Products, BitSight Anders Norremo...
Source: www.govinfosecurity.com - Author: 1 Fraud Management & Cybercrime , Governance & Risk Management , Privacy...
Source: www.govinfosecurity.com - Author: 1 Critical Infrastructure Security , Fraud Management & Cybercrime , Ransomware Reported...
Source: www.govinfosecurity.com - Author: 1 Shawn Surber Senior Director, Technical Account Management, Tanium Shawn Surber is...
Source: www.govinfosecurity.com - Author: 1 Artificial Intelligence & Machine Learning , Next-Generation Technologies & Secure Development...
Source: www.govinfosecurity.com - Author: 1 Fraud Management & Cybercrime , Governance & Risk Management , Privacy...
Source: www.govinfosecurity.com - Author: 1 Cyberwarfare / Nation-State Attacks , Fraud Management & Cybercrime , Government...
Source: www.govinfosecurity.com - Author: 1 Cybercrime , Cybercrime as-a-service , Endpoint Security Attackers List Compromised Servers...
Source: www.govinfosecurity.com - Author: 1 3rd Party Risk Management , Cloud Security , Governance & Risk...
Source: www.govinfosecurity.com - Author: 1 3rd Party Risk Management , Cloud Security , Governance & Risk...
Source: www.govinfosecurity.com - Author: 1 Finance & Banking , Fraud Management & Cybercrime , Industry Specific...
Source: www.govinfosecurity.com - Author: 1 Critical Infrastructure Security , Governance & Risk Management , Operational Technology...
Source: www.govinfosecurity.com - Author: 1 Critical Infrastructure Security , Governance & Risk Management , Government Program...
Source: www.govinfosecurity.com - Author: 1 Governance & Risk Management , Network Detection & Response , Next-Generation...
Source: www.govinfosecurity.com - Author: 1 Cyberwarfare / Nation-State Attacks , Fraud Management & Cybercrime , Social...
Source: www.govinfosecurity.com - Author: 1 3rd Party Risk Management , Fraud Management & Cybercrime , Governance...
Source: www.govinfosecurity.com - Author: 1 Andre Labuschagne Global Account Manager, Skyhigh Security Andre is an accomplished...
Source: www.govinfosecurity.com - Author: 1 Cyberwarfare / Nation-State Attacks , Fraud Management & Cybercrime , Standards,...