Source: www.govinfosecurity.com - Author: 1 Artificial Intelligence & Machine Learning , Government , Industry Specific Microsoft,...
- Home
- About Us
- Contact Us
- Register to apply for a free CISO2CISO Membership
- CISO2CISO Network
- CISO2CISO Services
- Sitemap
- Submit News
govinfosecurity.com
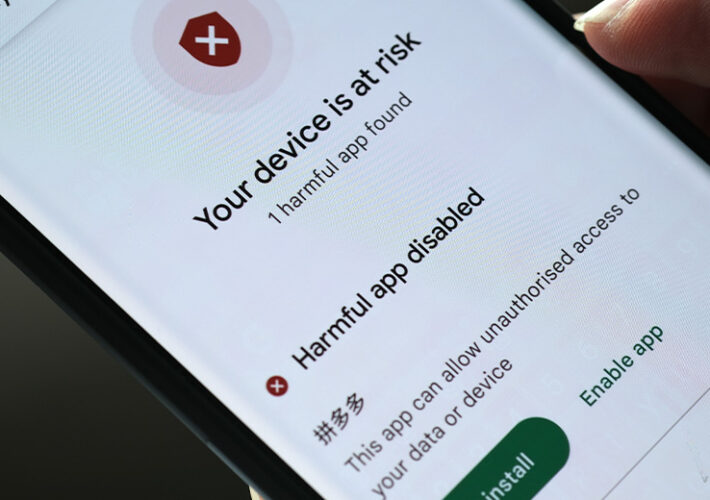
Source: www.govinfosecurity.com - Author: 1 Cyberwarfare / Nation-State Attacks , Fraud Management & Cybercrime , Mobile...
Source: www.govinfosecurity.com - Author: 1 Cyberwarfare / Nation-State Attacks , Fraud Management & Cybercrime , Government...
Source: www.govinfosecurity.com - Author: 1 Developing a Multilayered Defense Strategy for the Most Common Attack Techniques...
Source: www.govinfosecurity.com - Author: 1 Cryptocurrency Fraud , Cyberwarfare / Nation-State Attacks , Fraud Management &...
Source: www.govinfosecurity.com - Author: 1 Cybercrime , Fraud Management & Cybercrime , Social Engineering Malvertising Campaigns...
Source: www.govinfosecurity.com - Author: 1 Application Security , Governance & Risk Management , Next-Generation Technologies &...
Source: www.govinfosecurity.com - Author: 1 Cyberwarfare / Nation-State Attacks , Fraud Management & Cybercrime , Social...
Source: www.govinfosecurity.com - Author: 1 Breach Notification , Security Operations , Standards, Regulations & Compliance Stanley...
Source: www.govinfosecurity.com - Author: 1 Thank you for registering with ISMG Complete your profile and stay...
Source: www.govinfosecurity.com - Author: 1 Cyberwarfare / Nation-State Attacks , Fraud Management & Cybercrime , Governance...
Source: www.govinfosecurity.com - Author: 1 Jim Coyle U.S. PUBLIC SECTOR SECURITY STRATEGIST, Lookout Jim Coyle is...
Source: www.govinfosecurity.com - Author: 1 Endpoint Security , Governance & Risk Management , Internet of Things...
Source: www.govinfosecurity.com - Author: 1 Cyberwarfare / Nation-State Attacks , Fraud Management & Cybercrime , Next-Generation...
Source: www.govinfosecurity.com - Author: 12 Governance & Risk Management , Operational Technology (OT) Compromised Equipment, AI...
Source: www.govinfosecurity.com - Author: 1 David Sinclair spent 30 years working in Eastern Europe, Central Asia,...
Source: www.govinfosecurity.com - Author: 1 Cryptocurrency Fraud , Finance & Banking , Fraud Management & Cybercrime...
Source: www.govinfosecurity.com - Author: 1 Governance & Risk Management , Government , Industry Specific Presented by...
Source: www.govinfosecurity.com - Author: 1 Itzik Alvas CEO and Co-founder, Entro Security Itzik has 15+ years...
Source: www.govinfosecurity.com - Author: 1 Anti-Phishing, DMARC , Cybercrime , Cybercrime as-a-service Police Also Apprehend a...
Source: www.govinfosecurity.com - Author: 1 Cyberwarfare / Nation-State Attacks , Fraud Management & Cybercrime , Geo...
Source: www.govinfosecurity.com - Author: 1 Cryptocurrency Fraud , Fraud Management & Cybercrime , Ransomware Crypto Cybercrime...
Source: www.govinfosecurity.com - Author: 1 Application Security , Application Security & Online Fraud , DevSecOps How...
Source: www.govinfosecurity.com - Author: 1 Cyberwarfare / Nation-State Attacks , Fraud Management & Cybercrime , Government...
Source: www.govinfosecurity.com - Author: 1 Theo Zafirakos CISO, Professional Services Lead, Fortra’s Terranova Security Theo is...
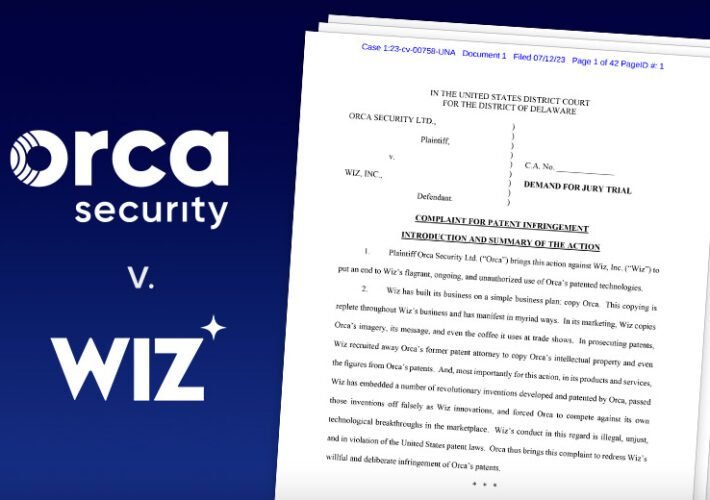
Source: www.govinfosecurity.com - Author: 1 Cloud Security , Security Operations Wiz Says 'Baseless Accusations' Follow Orca's...
Source: www.govinfosecurity.com - Author: 1 Cyberwarfare / Nation-State Attacks , Email Security & Protection , Fraud...
Source: www.govinfosecurity.com - Author: 1 3rd Party Risk Management , Fraud Management & Cybercrime , Governance...
Source: www.govinfosecurity.com - Author: 1 Fraud Management & Cybercrime , Governance & Risk Management , Privacy...
Source: www.govinfosecurity.com - Author: 1 Cybercrime , Fraud Management & Cybercrime , Social Engineering Toitoin Trojan...