Source: www.govinfosecurity.com - Author: 1 Nate Kettlewell Principal, Application Security, Coalfire Nate Kettlewell is a specialist...
- Home
- About Us
- Contact Us
- Register to apply for a free CISO2CISO Membership
- CISO2CISO Network
- CISO2CISO Services
- Sitemap
- Submit News
govinfosecurity.com
Source: www.govinfosecurity.com - Author: 1 Thank you for registering with ISMG Complete your profile and stay...
Source: www.govinfosecurity.com - Author: 1 Cybercrime , Fraud Management & Cybercrime , Incident & Breach Response...
Source: www.govinfosecurity.com - Author: 1 Cloud Access Security Brokers (CASB) , Cybercrime , Fraud Management &...
Source: www.govinfosecurity.com - Author: 1 Cyberwarfare / Nation-State Attacks , Fraud Management & Cybercrime BKA Says...
Source: www.govinfosecurity.com - Author: 1 Cloud-Delivered Security Service Edge Solution Gives Efficient Hybrid Work Security Jeff...
Source: www.govinfosecurity.com - Author: 1 Cisco's AJ Shipley on When Generative AI Is Useful and When...
Source: www.govinfosecurity.com - Author: 1 Generative AI will play a role in the future of incident...
Source: www.govinfosecurity.com - Author: 1 Governance & Risk Management , IT Risk Management , Risk Assessments...
Source: www.govinfosecurity.com - Author: 1 Nate Kettlewell Principal, Application Security, Coalfire Nate Kettlewell is a specialist...
Source: www.govinfosecurity.com - Author: 1 Governance & Risk Management , Healthcare , HIPAA/HITECH Attorneys to Get...
Source: www.govinfosecurity.com - Author: 1 Governance & Risk Management , Privacy Tentative Order Issued in Consolidated...
Source: www.govinfosecurity.com - Author: 1 Cloud Security , Next-Generation Technologies & Secure Development , Security Operations...
Source: www.govinfosecurity.com - Author: 1 Critical Infrastructure Security Kaspersky Says APT31 Targeted Industrial Organizations for Spying...
Source: www.govinfosecurity.com - Author: 1 Cybercrime , Fraud Management & Cybercrime Rapattoni-Hosted Multiple Listing Services Can't...
Source: www.govinfosecurity.com - Author: 1 Incident & Breach Response , Legislation & Litigation , Security Operations...
Source: www.govinfosecurity.com - Author: 1 Identity & Access Management , Security Operations Legion Partners Calls on...
Source: www.govinfosecurity.com - Author: 1 API Security The Different Types of API Attacks and Best Practices...
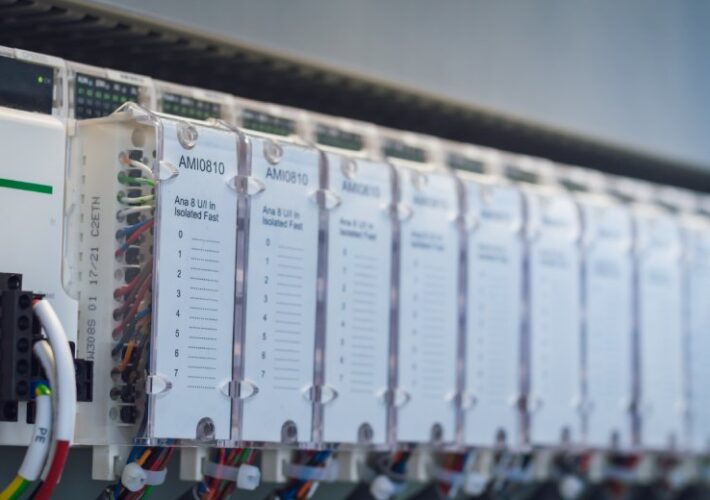
Source: www.govinfosecurity.com - Author: 1 Governance & Risk Management , Patch Management Vulnerabilities Found in CyberPower...
Source: www.govinfosecurity.com - Author: 1 Ilkka Turunen Field CTO, Sonatype lkka Turunen is Field CTO at...
Source: www.govinfosecurity.com - Author: 1 Breach Notification , Security Operations Latest Tally of Clop Campaign Victims:...
Source: www.govinfosecurity.com - Author: 1 Breach Notification , Healthcare , Industry Specific Multiple Challenges Can Delay...
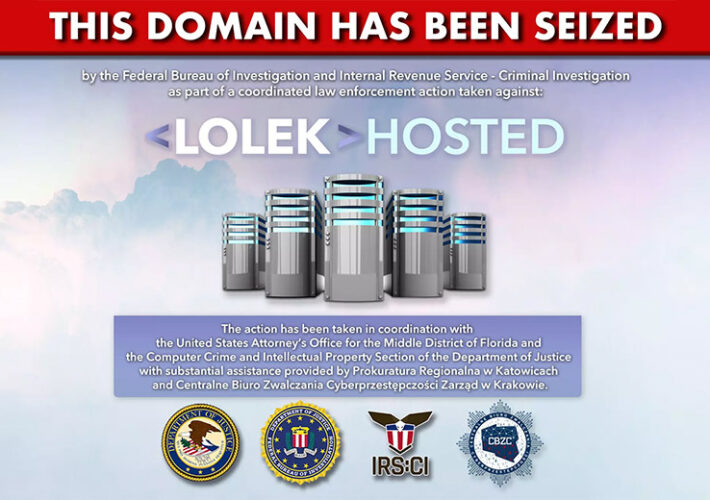
Source: www.govinfosecurity.com - Author: 1 Cybercrime , Fraud Management & Cybercrime , Ransomware NetWalker Ransomware Hackers...
Source: www.govinfosecurity.com - Author: 1 Cybercrime , Fraud Management & Cybercrime Voice and Text Not Secure...
Source: www.govinfosecurity.com - Author: 1 As generative AI has evolved with alarming speed, it has brought...
Source: www.govinfosecurity.com - Author: 1 Artificial Intelligence & Machine Learning , Governance & Risk Management ,...
Source: www.govinfosecurity.com - Author: 1 Fraud Management & Cybercrime , Healthcare , Industry Specific Alberta Dental...
Source: www.govinfosecurity.com - Author: 1 Governance & Risk Management , Operational Technology (OT) Exploitation Could Lead...
Source: www.govinfosecurity.com - Author: 1 Fraud Management & Cybercrime , Social Engineering Phishing Kit Primarily Used...
Source: www.govinfosecurity.com - Author: 1 Endpoint Security , Healthcare , Industry Specific Researcher Deral Heiland of...