Source: www.govinfosecurity.com - Author: 1 3rd Party Risk Management , Governance & Risk Management Data Minimization...
- Home
- About Us
- Contact Us
- Register to apply for a free CISO2CISO Membership
- CISO2CISO Network
- CISO2CISO Services
- Sitemap
- Submit News
govinfosecurity.com
Source: www.govinfosecurity.com - Author: 1 Artificial Intelligence & Machine Learning , Next-Generation Technologies & Secure Development...
Source: www.govinfosecurity.com - Author: 1 Also: 9-Year Prison Sentence for Insider Trading Fueled by Password Theft...
Source: www.govinfosecurity.com - Author: 1 Robert Sawyer Sr. Director of Solutions Marketing, CyberArk Robert Sawyer is...
Source: www.govinfosecurity.com - Author: 1 Thank you for registering with ISMG Complete your profile and stay...
Source: www.govinfosecurity.com - Author: 1 Geo Focus: Asia , Geo-Specific , Government China Cites Apple Security...
Source: www.govinfosecurity.com - Author: 1 Healthcare , HIPAA/HITECH , Industry Specific Inquiry is Latest Move by...
Source: www.govinfosecurity.com - Author: 1 Active Defense & Deception , Fraud Management & Cybercrime , Next-Generation...
Source: www.govinfosecurity.com - Author: 1 Cloud Security , Security Operations Nikko Asset Management's Marcus Rameke Defines...
Source: www.govinfosecurity.com - Author: 1 Critical Infrastructure Security , Cyberwarfare / Nation-State Attacks , Fraud Management...
Source: www.govinfosecurity.com - Author: 1 Governance & Risk Management , Patch Management Patch Contains 59 Bugs...
Source: www.govinfosecurity.com - Author: 1 Fraud Management & Cybercrime , Governance & Risk Management , Healthcare...
Source: www.govinfosecurity.com - Author: 1 Endpoint Security , Governance & Risk Management , Vulnerability Assessment &...
Source: www.govinfosecurity.com - Author: 1 In the a year marked by vulnerabilities being found in the...
Source: www.govinfosecurity.com - Author: 1 Artificial Intelligence & Machine Learning , Next-Generation Technologies & Secure Development...
Source: www.govinfosecurity.com - Author: 1 Andrey Pozhogin Sr. Product Marketing Manager, Endpoint Privilege Security, IT Security...
Source: www.govinfosecurity.com - Author: 1 White House Secures 8 Additional Commitments to AI Pledge Rashmi Ramesh...
Source: www.govinfosecurity.com - Author: 1 Cyberwarfare / Nation-State Attacks , Fraud Management & Cybercrime Hackers Likely...
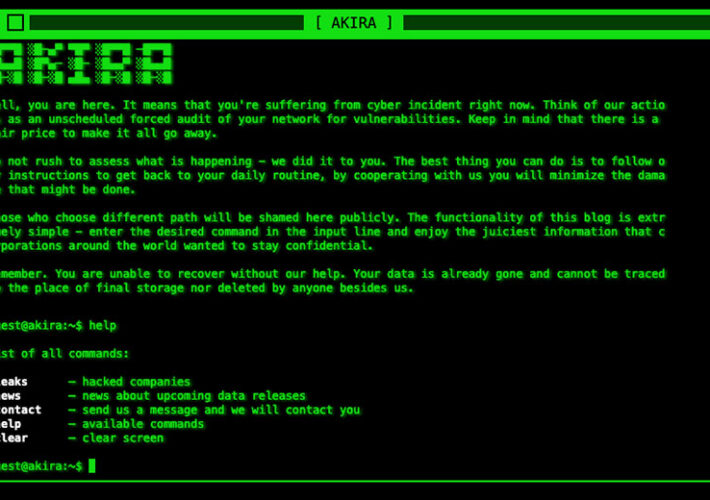
Source: www.govinfosecurity.com - Author: 1 Fraud Management & Cybercrime , Ransomware UK Crime and Cybersecurity Agencies...
Source: www.govinfosecurity.com - Author: 1 Access Management Honeypot Hits Reinforce Need for Strong Passwords and Multifactor...
Source: www.govinfosecurity.com - Author: 1 Fraud Management & Cybercrime , Governance & Risk Management , Healthcare...
Source: www.govinfosecurity.com - Author: 1 Fraud Management & Cybercrime , Social Engineering Vectors Includes Teams Phishing...
Source: www.govinfosecurity.com - Author: 1 General Data Protection Regulation (GDPR) , Governance & Risk Management ,...
Source: www.govinfosecurity.com - Author: 1 Sean Martin Director of Product Strategy, CSI Business Solutions Group for...
Source: www.govinfosecurity.com - Author: 1 In the aftermath of mergers and acquisitions among healthcare entities -...
Source: www.govinfosecurity.com - Author: 1 Governance & Risk Management , Zero Trust Tyler Cohen Wood ,...
Source: www.govinfosecurity.com - Author: 1 Thank you for registering with ISMG Complete your profile and stay...
Source: www.govinfosecurity.com - Author: 1 Endpoint Security 'BlastPass' Can Compromise iPhones Running the Latest iOS Version,...
Source: www.govinfosecurity.com - Author: 1 Cloud Security , Healthcare , Industry Specific Also: Feds Out Hospitals...
Source: www.govinfosecurity.com - Author: 1 Attack Surface Management , Critical Infrastructure Security , Cyberwarfare / Nation-State...