Source: www.databreachtoday.com - Author: 1 Thank you for registering with ISMG Complete your profile and stay...
- Home
- About Us
- Contact Us
- Register to apply for a free CISO2CISO Membership
- CISO2CISO Network
- CISO2CISO Services
- Sitemap
- Submit News
Data Breach Today
Source: www.databreachtoday.com - Author: 1 Artificial intelligence technologies offer tremendous promise in healthcare, but it's crucial...
Source: www.databreachtoday.com - Author: 1 Healthcare is increasingly complex and interconnected, and the push to exchange...
Source: www.databreachtoday.com - Author: 1 Cyberwarfare / Nation-State Attacks , Fraud Management & Cybercrime , Network...
Source: www.databreachtoday.com - Author: 1 Breach Notification , Cybercrime , Fraud Management & Cybercrime Breach Is...
Source: www.databreachtoday.com - Author: 1 Artificial Intelligence & Machine Learning , Next-Generation Technologies & Secure Development...
Source: www.databreachtoday.com - Author: 1 Governance & Risk Management , Government , Industry Specific New Report...
Source: www.databreachtoday.com - Author: 1 Fraud Management & Cybercrime , Ransomware Russian-Speaking Gang Follows Typical Playbook;...
Source: www.databreachtoday.com - Author: 1 3rd Party Risk Management , Cyberwarfare / Nation-State Attacks , Fraud...
Source: www.databreachtoday.com - Author: 1 Critical Infrastructure Security , Leadership & Executive Communication , Training &...
Source: www.databreachtoday.com - Author: 1 Artificial Intelligence & Machine Learning , Governance & Risk Management ,...
Source: www.databreachtoday.com - Author: 1 Fraud Management & Cybercrime , Healthcare , Industry Specific Rubrik's Steve...
Source: www.databreachtoday.com - Author: 1 Cybercrime , Fraud Management & Cybercrime , Government Justice Says Sagar...
Source: www.databreachtoday.com - Author: 1 Fraud Management & Cybercrime , Geo Focus: Asia , Geo-Specific Hackers...
Source: www.databreachtoday.com - Author: 1 Artificial Intelligence & Machine Learning , Governance & Risk Management ,...
Source: www.databreachtoday.com - Author: 1 Artificial Intelligence & Machine Learning , Next-Generation Technologies & Secure Development...
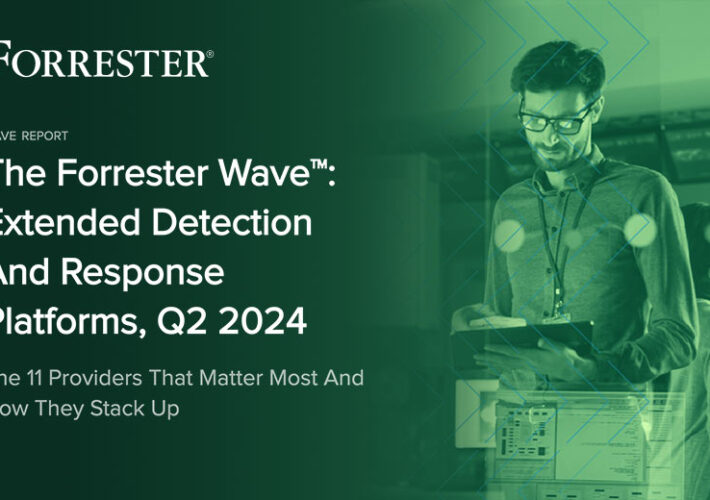
Source: www.databreachtoday.com - Author: 1 Open XDR , Security Information & Event Management (SIEM) , Security...
Source: www.databreachtoday.com - Author: 1 Artificial Intelligence & Machine Learning , General Data Protection Regulation (GDPR)...
Source: www.databreachtoday.com - Author: 1 Geo Focus: Asia , Geo-Specific , Governance & Risk Management Enterprise...
Source: www.databreachtoday.com - Author: 1 Attack Surface Management , Security Operations Researchers Infiltrate Major Organizations Using...
Source: www.databreachtoday.com - Author: 1 Blockchain & Cryptocurrency , Cryptocurrency Fraud , Fraud Management & Cybercrime...
Source: www.databreachtoday.com - Author: 1 Attack Surface Management , Security Operations Acquiring Hubble Means NetSPI Can...
Source: www.databreachtoday.com - Author: 1 Artificial Intelligence & Machine Learning , Next-Generation Technologies & Secure Development...
Source: www.databreachtoday.com - Author: 1 Governance & Risk Management , Government , Industry Specific Agency Seeks...
Source: www.databreachtoday.com - Author: 1 Cybercrime , Cyberwarfare / Nation-State Attacks , Fraud Management & Cybercrime...
Source: www.databreachtoday.com - Author: 1 Endpoint Security , Government , Hardware / Chip-level Security High-Assurance Security...
Source: www.databreachtoday.com - Author: 1 Fraud Management & Cybercrime , Social Engineering CISA Won't Ask You...
Source: www.databreachtoday.com - Author: 1 Nader Zaveri Senior Manager - Incident Response & Remediation, Google Cloud...
Source: www.databreachtoday.com - Author: 1 David Holmes Research Analyst for Zero Trust, Security, and Risk, Forrester...
Source: www.databreachtoday.com - Author: 1 Fraud Management & Cybercrime , Healthcare , Industry Specific Researchers Rahi...