Source: www.cyberdefensemagazine.com - Author: News team In today’s digital age, the importance of cybersecurity must be...
- Home
- About Us
- Contact Us
- Register to apply for a free CISO2CISO Membership
- CISO2CISO Network
- CISO2CISO Services
- Sitemap
- Submit News
cyberdefense magazine
Source: www.cyberdefensemagazine.com - Author: News team State and local government and education organizations (also known as...
Source: www.cyberdefensemagazine.com - Author: News team Executive summary Many companies face various risks across their supply...
Source: www.cyberdefensemagazine.com - Author: News team As a CEO working alongside cybersecurity product companies, I know...
Source: www.cyberdefensemagazine.com - Author: News team The ever-evolving landscape of data security demands constant vigilance, especially...
Source: www.cyberdefensemagazine.com - Author: News team Picture this: your colleague’s about to click a link that...
Source: www.cyberdefensemagazine.com - Author: News team Cyber risks differ from other more familiar risks in life,...
Source: www.cyberdefensemagazine.com - Author: News team The release of iOS 16.4 has been a game-changer for...
Source: www.cyberdefensemagazine.com - Author: News team In early June, the Ticketmaster breach brought widespread attention to...
Source: www.cyberdefensemagazine.com - Author: News team A few years back, my security team was tasked to...
Source: www.cyberdefensemagazine.com - Author: News team In the wake of a recent breach that compromised sensitive...
Source: www.cyberdefensemagazine.com - Author: Nick by Dan K. Anderson CEO, CISO, and vCISO The cybersecurity landscape...
Source: www.cyberdefensemagazine.com - Author: Stevin It’s often assumed that if the board knew exactly what they...
Source: www.cyberdefensemagazine.com - Author: News team In the modern era of technological advancement, artificial intelligence (AI)...
Source: www.cyberdefensemagazine.com - Author: News team In recent years, video analytics has significantly transformed the interpretation...
Source: www.cyberdefensemagazine.com - Author: Nick by Dan K. Anderson CEO, CISO, and vCISO With the rise...
Source: www.cyberdefensemagazine.com - Author: News team Do you know where all the secrets are? The probable...
Source: www.cyberdefensemagazine.com - Author: News team Cybersecurity compliance is undergoing a massive shift, with regulatory frameworks...
Source: www.cyberdefensemagazine.com - Author: News team E-commerce is poised to account for over 20% of global purchases by...
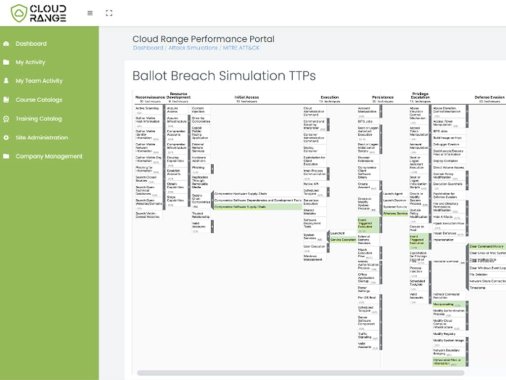
Source: www.cyberdefensemagazine.com - Author: News team Tom MarslandCloud RangeOctober 22, 2024 In the constantly evolving realm...
Source: www.cyberdefensemagazine.com - Author: Stevin In the current cybersecurity landscape, the focus has shifted from merely...
Source: www.cyberdefensemagazine.com - Author: Stevin Data security is more critical than ever as organizations manage vast...
Source: www.cyberdefensemagazine.com - Author: News team We’ve got a hard truth to share with you, and...
Source: www.cyberdefensemagazine.com - Author: News team Zero-Trust Endpoint Security: How a Preventive Approach Can Limit Your...
Source: www.cyberdefensemagazine.com - Author: News team The ongoing prevalence (and rise) of software supply chain attacks...
AI-Powered Fraud Detection Systems for Enhanced Cybersecurity – Source: www.cyberdefensemagazine.com
Source: www.cyberdefensemagazine.com - Author: News team Artificial intelligence (AI) has many applications in cybersecurity. Automated fraud...
Source: www.cyberdefensemagazine.com - Author: News team The modern Security Operations Center (SOC) has morphed and matured...
Source: www.cyberdefensemagazine.com - Author: Stevin In today’s rapidly evolving digital landscape, organizations are increasingly reliant on...
Source: www.cyberdefensemagazine.com - Author: News team More than 70 percent of enterprises have prioritized SaaS security...
Source: www.cyberdefensemagazine.com - Author: News team Security testing plays a critical role in ensuring that applications...