Understanding a particular Zero Trust journey from the lens of a CISO at an American healthcare...
- Home
- About Us
- Contact Us
- Register to apply for a free CISO2CISO Membership
- CISO2CISO Network
- CISO2CISO Services
- Sitemap
- Submit News
Cyber Talk
AI-based social engineering is the next-generation of hacking humans Keely Wilkins has been in the technology...
7 key considerations: Zero Trust Network Architecture EXECUTIVE SUMMARY: Explore seven key considerations for when you...
The end of DDoS attacks is near, with these mitigation measures David Hobbs currently serves in...
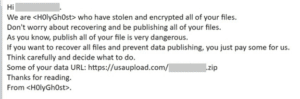
How to prevent Holy Ghost ransomware attacks on small businesses EXECUTIVE SUMMARY: Holy Ghost ransomware operators...
8 highly effective insider fraud prevention tips for 2022 EXECUTIVE SUMMARY: While some threat actors sequester...
Security considerations for telehealth businesses Devin Partida writes about cyber security and technology. She is also...
Amazon might own your doctor’s office after this latest acquisition EXECUTIVE SUMMARY: Amazon is set to...
How new encryption standards can protect your data from the next breach Tilo Weigandt is an...
Security considerations for telehealth businesses Devin Partida writes about cyber security and technology. She is also...
7 key considerations: Zero Trust Network Architecture EXECUTIVE SUMMARY: Explore seven key considerations for when you...
AI-based social engineering is the next-generation of hacking humans Keely Wilkins has been in the technology...
6 easy ways to spot Amazon Prime Day scams EXECUTIVE SUMMARY: As Amazon Prime Day rapidly...
Top tips for building an effective code review checklist EXECUTIVE SUMMARY: Code review represents the best...
Google sends alert about “Hermit” spyware on Android and iOS devices EXECUTIVE SUMMARY: Google has issued...