Source: www.bleepingcomputer.com - Author: Bill Toulas A threat actor announced on a cybercrime forum that they...
- Home
- About Us
- Contact Us
- Register to apply for a free CISO2CISO Membership
- CISO2CISO Network
- CISO2CISO Services
- Sitemap
- Submit News
Bleeping Computer
Source: www.bleepingcomputer.com - Author: Bill Toulas The U.S. Federal Trade Commission (FTC) has started accepting submissions...
Source: www.bleepingcomputer.com - Author: Ax Sharma Over the holidays, the npm package registry was flooded with more...
Source: www.bleepingcomputer.com - Author: Sergiu Gatlan The Twitter account of American cybersecurity firm and Google subsidiary...
Source: www.bleepingcomputer.com - Author: Lawrence Abrams Orange Spain suffered an internet outage today after a hacker...
Source: www.bleepingcomputer.com - Author: Bill Toulas A Nigerian national was arrested in Ghana and is facing...
Source: www.bleepingcomputer.com - Author: Lawrence Abrams Adult media giant Aylo has blocked access to many of...
Source: www.bleepingcomputer.com - Author: Sergiu Gatlan LastPass notified customers today that they are now required to...
Source: www.bleepingcomputer.com - Author: Bill Toulas HealthEC LLC, a provider of health management solutions, suffered a data...
Source: www.bleepingcomputer.com - Author: Bill Toulas Almost 11 million internet-exposed SSH servers are vulnerable to the...
Source: www.bleepingcomputer.com - Author: Bill Toulas The U.S. Cybersecurity and Infrastructure Security Agency has added two...
Source: www.bleepingcomputer.com - Author: Lawrence Abrams Steam is no longer supported on Windows 7, Windows 8,...
Source: www.bleepingcomputer.com - Author: Bill Toulas Orbit Chain has experienced a security breach that has resulted...
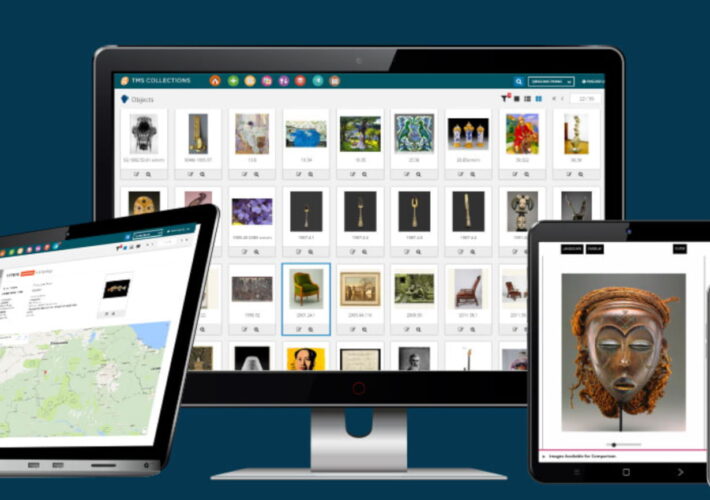
Source: www.bleepingcomputer.com - Author: Bill Toulas Museum software solutions provider Gallery Systems has disclosed that its...
Source: www.bleepingcomputer.com - Author: Bill Toulas The U.S. division of Xerox Business Solutions (XBS) has been...
Source: www.bleepingcomputer.com - Author: Mayank Parmar Google has officially announced it's ceasing support for Usenet groups...
Source: www.bleepingcomputer.com - Author: Bill Toulas Australia's Court Services Victoria (CSV) is warning that video recordings...
Source: www.bleepingcomputer.com - Author: Lawrence Abrams In 2023, we saw numerous law enforcement operations targeting cybercrime...
Source: www.bleepingcomputer.com - Author: Lawrence Abrams 2023 was a big year for cybersecurity, with significant cyberattacks,...
Source: www.bleepingcomputer.com - Author: Bill Toulas Japanese game developer Ateam has proven that a simple Google...
Source: www.bleepingcomputer.com - Author: Lawrence Abrams Researchers have created a decryptor that exploits a flaw in...
Source: www.bleepingcomputer.com - Author: Lawrence Abrams It's been a quiet week, with even threat actors appearing...
Source: www.bleepingcomputer.com - Author: Sergiu Gatlan Two not-for-profit hospitals in New York are seeking a court...
Source: www.bleepingcomputer.com - Author: Bill Toulas Multiple information-stealing malware families are abusing an undocumented Google OAuth...
Source: www.bleepingcomputer.com - Author: Sergiu Gatlan Downfall, a fan expansion for the popular Slay the Spire...
Source: www.bleepingcomputer.com - Author: Sergiu Gatlan Downfall, a fan expansion for the popular Slay the Spire...
Source: www.bleepingcomputer.com - Author: Bill Toulas Eagers Automotive has announced it suffered a cyberattack and was...
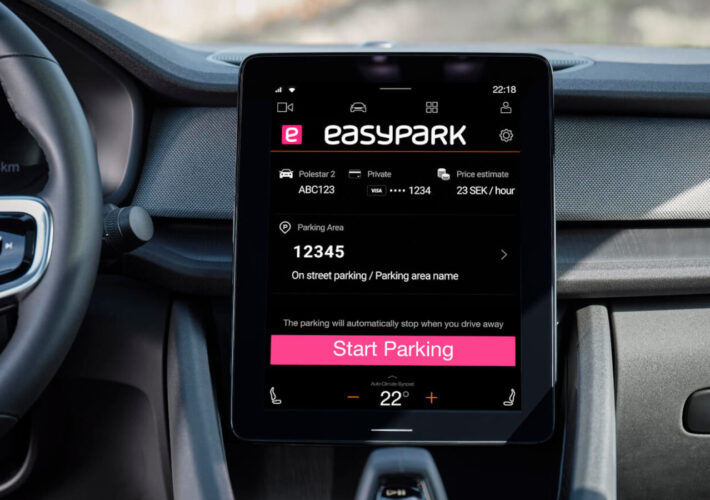
Source: www.bleepingcomputer.com - Author: Bill Toulas Parking app developer EasyPark has published a notice on its...
Source: www.bleepingcomputer.com - Author: Sergiu Gatlan Microsoft has again disabled the MSIX ms-appinstaller protocol handler after...
Source: www.bleepingcomputer.com - Author: Sergiu Gatlan Risk and financial advisory company Kroll has released additional details...