Source: www.bleepingcomputer.com - Author: Bill Toulas The RansomHouse ransomware operation has created a new tool named...
- Home
- About Us
- Contact Us
- Register to apply for a free CISO2CISO Membership
- CISO2CISO Network
- CISO2CISO Services
- Sitemap
- Submit News
Bleeping Computer
Source: www.bleepingcomputer.com - Author: Sergiu Gatlan The FBI took down a botnet of small office/home office...
Source: www.bleepingcomputer.com - Author: Bill Toulas OpenAI has removed accounts used by state-sponsored threat groups from...
Over 13,000 Ivanti gateways vulnerable to actively exploited bugs – Source: www.bleepingcomputer.com
Source: www.bleepingcomputer.com - Author: Bill Toulas Thousands of Ivanti Connect Secure and Policy Secure endpoints remain...
Source: www.bleepingcomputer.com - Author: Sponsored by Outpost24 In today's interconnected world, web application security is crucial...
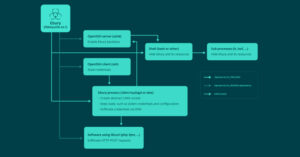
Source: www.bleepingcomputer.com - Author: Ionut Ilascu Security researchers have identified and analyzed new malware they call...
Source: www.bleepingcomputer.com - Author: Bill Toulas The developer of Qakbot malware, or someone with access to the source...
Source: www.bleepingcomputer.com - Author: Bill Toulas A new iOS and Android trojan named 'GoldPickaxe' employs a...
Source: www.bleepingcomputer.com - Author: Sergiu Gatlan Microsoft warned today in an updated security advisory that a critical...
Source: www.bleepingcomputer.com - Author: Ionut Ilascu The LockBit ransomware gang claims to be behind the recent...
Source: www.bleepingcomputer.com - Author: Bill Toulas The Zoom desktop and VDI clients and the Meeting SDK...
Source: www.bleepingcomputer.com - Author: Sergiu Gatlan Update February 14, 16:50 EST: Article and title revised after...
Source: www.bleepingcomputer.com - Author: Sergiu Gatlan Microsoft is automatically enabling Windows Extended Protection on Exchange servers...
Source: www.bleepingcomputer.com - Author: Bill Toulas Battery maker VARTA AG announced yesterday that it was targeted...
Source: www.bleepingcomputer.com - Author: Bill Toulas A logic flaw between Ubuntu's 'command-not-found' package suggestion system and...
Source: www.bleepingcomputer.com - Author: Sergiu Gatlan Trans-Northern Pipelines (TNPI) has confirmed its internal network was breached...
Source: www.bleepingcomputer.com - Author: Bill Toulas The DuckDuckGo browser has unveiled a new end-to-end encrypted Sync...
Hackers used new Windows Defender zero-day to drop DarkMe malware – Source: www.bleepingcomputer.com
Source: www.bleepingcomputer.com - Author: Sergiu Gatlan Microsoft has patched today a Windows Defender SmartScreen zero-day exploited...
Source: www.bleepingcomputer.com - Author: Sergiu Gatlan Prudential Financial has disclosed that its network was breached last...
Source: www.bleepingcomputer.com - Author: Sergiu Gatlan Bank of America is warning customers of a data breach...
Source: www.bleepingcomputer.com - Author: Bill Toulas The FBI dismantled the Warzone RAT malware operation, seizing infrastructure...
Source: www.bleepingcomputer.com - Author: Sergiu Gatlan Starting March 13th, telecommunications companies must report data breaches impacting...
Source: www.bleepingcomputer.com - Author: Lawrence Abrams Microsoft is testing a new "Automatic Super Resolution" AI-assisted upscaling...
Source: www.bleepingcomputer.com - Author: Bill Toulas A phishing campaign detected in late November 2023 has compromised...
Source: www.bleepingcomputer.com - Author: Sergiu Gatlan CISA warns that a Roundcube email server vulnerability patched in...
Source: www.bleepingcomputer.com - Author: Bill Toulas Hackers are exploiting a server-side request forgery (SSRF) vulnerability in...
Source: www.bleepingcomputer.com - Author: Bill Toulas South Korean researchers have publicly disclosed an encryption flaw in...
Source: www.bleepingcomputer.com - Author: Sergiu Gatlan Over two dozen hospitals in Romania have taken their systems offline...
Source: www.bleepingcomputer.com - Author: Bill Toulas ExpressVPN has removed the split tunneling feature from the latest...
Source: www.bleepingcomputer.com - Author: Sergiu Gatlan CISA confirmed today that attackers are actively exploiting a critical...