Ransomware attacks increased 91% in March, as threat actors find new vulnerabilities
Ransomware attacks skyrocketed last month according to the new monthly cybersecurity report by NCC Group. New threat group Cl0p is behind the increase as it exploited vulnerabilities in GoAnywhere file transfer manager.
We may be compensated by vendors who appear on this page through methods such as affiliate links or sponsored partnerships. This may influence how and where their products appear on our site, but vendors cannot pay to influence the content of our reviews. For more info, visit our Terms of Use page.

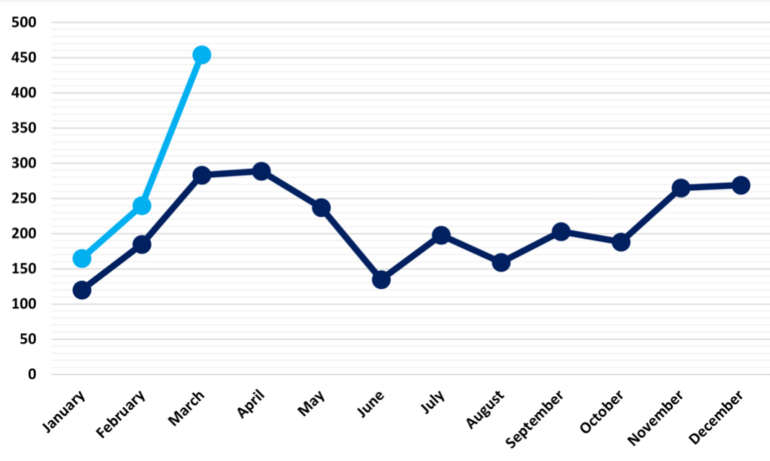
Ransomware attacks have spiked, according to the NCC Group’s Global Threat Intelligence Team. In its monthly threat report, NCC Group reported a 91% increase in ransomware attacks in March versus February and a 62% increase versus the month last year — the highest number of monthly ransomware attacks the group has ever measured (Figure A).
Figure A
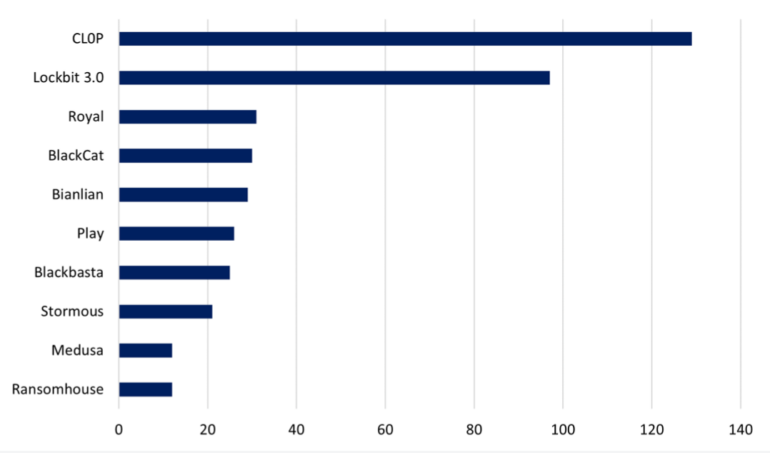
Ransomware-as-a-Service provider Cl0p, the most active threat actor, accounted for 28% of all March victims. NCC Group said it is also the first time Cl0p has been the top RaaS for cybercriminal groups.
Cl0p, a Russian linked entity specializing in double extortion, exfiltrates data then threatens to release it if ransom isn’t forthcoming. The hacking group has been around since 2019, when it successfully attacked major companies like Hitachi, Shell and several other enterprises.
LockBit 3.0 came in second, accounting for 21% of attacks. NCC Group said March 2023 was the second month since September 2021 in which LockBit had not been the top ransomware threat actor. The group’s victims declined 25% from February, per NCC.
SEE: The Royal scam — threat actors promise challenging 2023
The non-aligned attack group Royal, which appeared in September last year targeting the healthcare sector, was the third most active attacker with a 106% increase in attacks in March versus February (Figure B).
Figure B
Cl0p accessed GoAnywhere MFT vulnerability to attack organizations
NCC Group said the increase in attacks by CL0p reflected its exploitation of a vulnerability in Fortra’s GoAnywhere managed file transfer used by thousands of organizations around the world, causing large-scale disruption.
As reported, Fortra found the zero-day vulnerability in January and told only its authenticated users, but it was not assigned a CVE ID on Mitre or patched until early February.
Shields up for organizations using GoAnywhere MFT
According to NCC Group, there are viable tactics for protecting against attacks by Cl0p and other exploiters of third-party tools and services:
- Limit exposure on ports 8000 and 8001, where the GoAnywhere MFT admin panel is situated.
- After logging into GoAnywhere, follow the steps outlined in the GoAnywhere security advisory.
- Install patch 7.1.2.
- Review admin user accounts for suspicious activity, with a special focus on accounts created by systems, suspicious or atypical timing of account creation or disabled super-users creating multiple accounts.
- Contact GoAnywhere MFT support directly via portal, email or phone to receive additional assistance.
SEE: End-to-end encrypted email platforms can thwart attacks.
North American, industrial sector are double bullseyes
Regions
Repeating trends from last month’s analysis, North America was the target of almost half of March’s activity, with 221 victims (48%). Europe (28%) and Asia (13%) followed with 126 and 59 attacks respectively.
Sectors
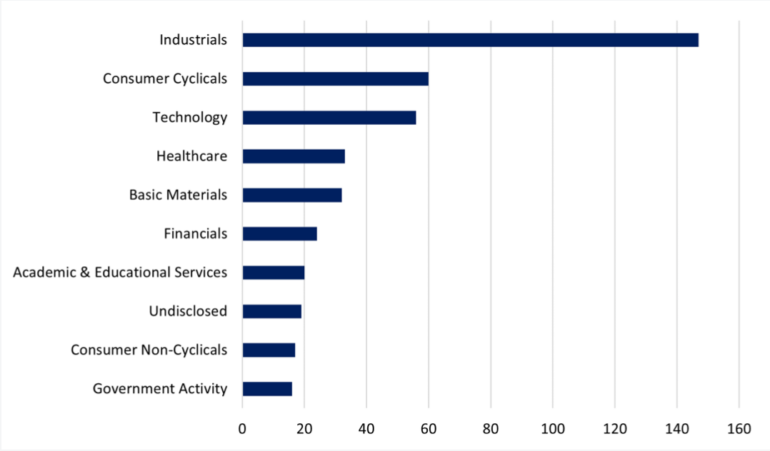
Industrials were by far the most targeted sector last month with 147 strikes, accounting for 32% of attacks. Consumer Cyclicals was the second-most targeted with 60 attacks (13%), followed by Technology, regaining third place with 56 attacks (12%).
In the industrial sector:
- The number of victims in professional and commercial services increased 120%.
- Attacks on machinery, tools, heavy vehicles, trains and ships increased 127%.
- Attacks on onstruction and engineering sectors increased 16% (Figure C).
Figure C
Pace of ransomware attacks likely to remain brisk
Matt Hull, global head of threat intelligence at NCC Group, said the huge surge in ransomware attacks last month is likely to be par for the course this year. “If [Cl0p’s] operations remain consistent, we can expect them to remain a prevalent threat throughout the year. We are keeping a close eye on the actor as it evolves,” he said.
The company previously reported the highest number of ransomware cases in January and February than in the past 3 years.
How to defend against accelerating ransomware threats
With this year likely to feature increased attacks, NCC Group suggests:
- Know if a newly announced vulnerability will affect your organization, as well as know your systems and configurations.
- Patch often. The fact that Log4j is still active shows how un-patched CVEs offer an open door.
- Block common forms of entry: Create a plan for how to quickly disable at-risk systems like VPNs or RDP.
- Look into endpoint security packages to detect exploits and malware.
- Create backups offline and offsite, beyond the reach of attackers.
- Be cognizant: Attackers return to the same victim when they know a hole has not been patched.
If attacked and the outbreak is isolated and stopped, every trace of their intrusion, malware, tools and methods of entry must be removed, assessed and acted upon to avoid being attacked again.
Also See
-
DDoS attacks rise as pro-Russia groups attack Finland, Israel
(TechRepublic) -
With political ‘hacktivism’ rising, Google offers Project Shield to fight DDoS attacks
(TechRepublic) -
Gain an understanding of AI, cybersecurity and more with this $69 resource
(TechRepublic Academy) -
Transmission of sensitive data policy
(TechRepublic Premium)
Views: 3