Source: heimdalsecurity.com – Author: Adelina Deaconu
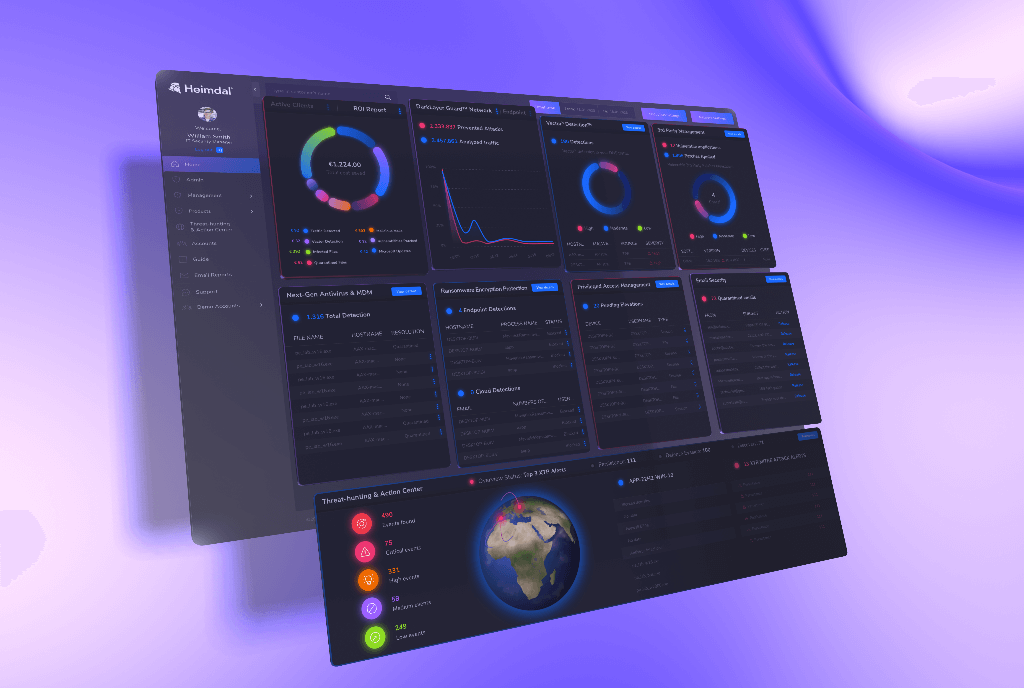
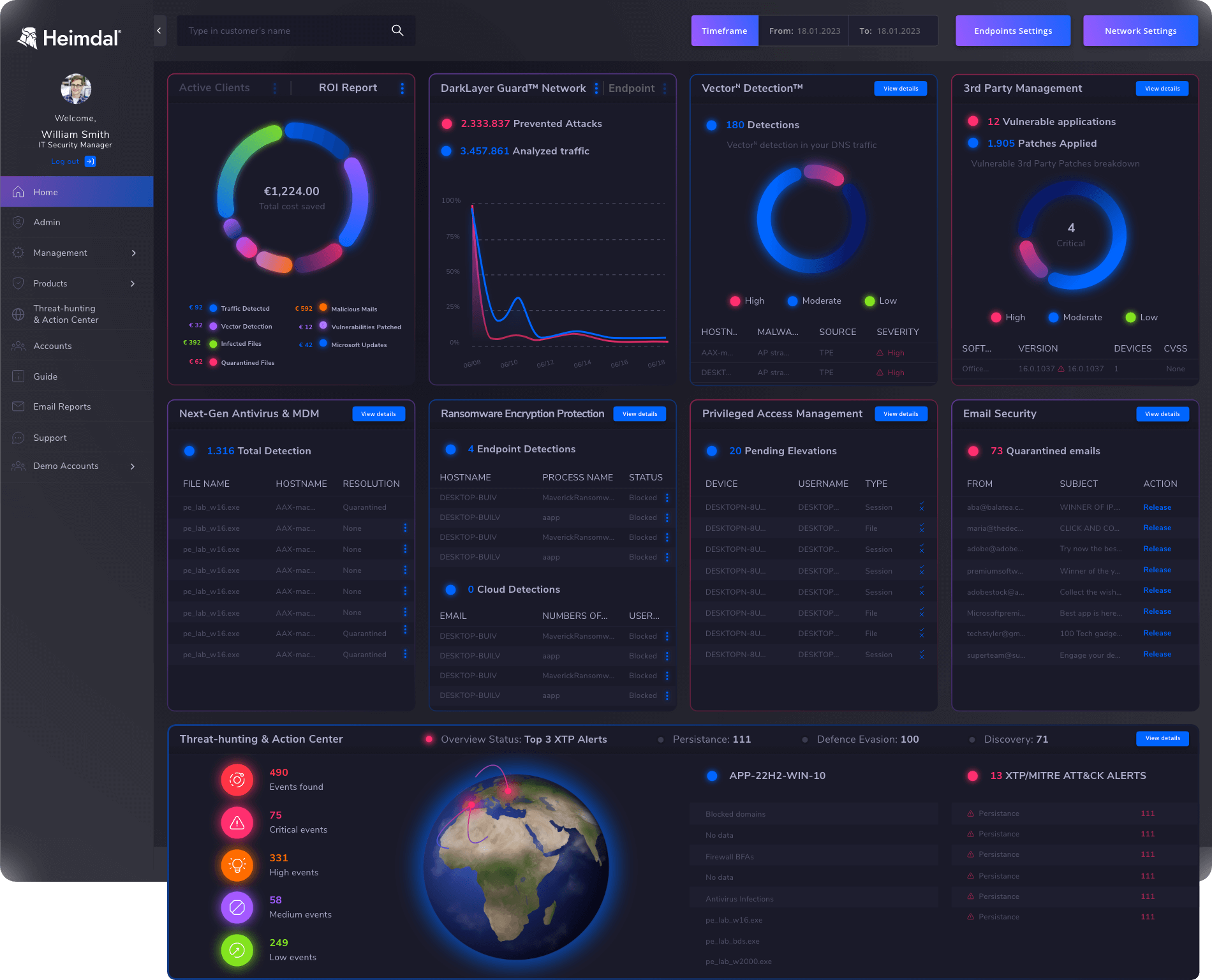
Heimdal XDR offers you full visibility into network traffic, user behavior, and endpoint activity. It makes investigating threats much easier, showing you how threats happened and when they occurred. This means you can quickly figure out why each alert was triggered. Plus, you can take immediate action right from our award-winning unified platform.
By the end of this article, you will know:
- When does Heimdal XDR generate alerts;
- What is Heimdal XDR Agent, and how does it work;
- The best methods for effectively managing alerts using our award-winning Heimdal XDR Dashboard.
With Heimdal XDR, businesses can tighten their defense strategy with little effort. This way, security teams can focus on proactive threat hunting and response
– Nabil Nistar, Head of Product Marketing
When does Heimdal XDR Generate Alerts?
Heimdal XDR generates alerts whenever it finds possible threats on your network, endpoints, or cloud setup. These alerts give you lots of info about the threat such as what kind of threat it is, which system or device it’s impacting, severity level, and much more.
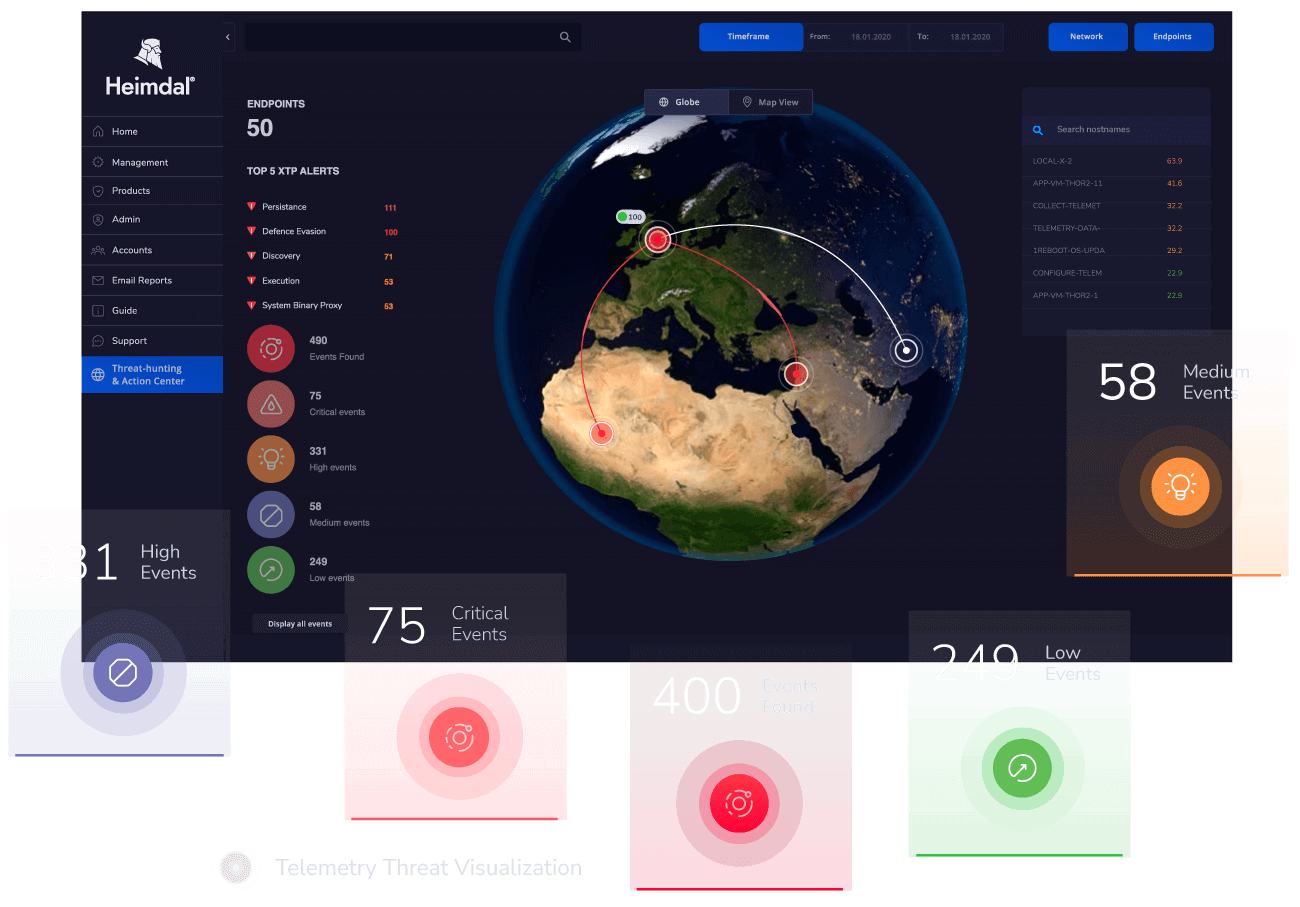
Heimdal XDR Agent
Every individual device, whether it’s on-site or remote, is safeguarded by the Heimdal XDR Agent. This agent gets installed on the device and stays active all the time. It makes sure your security rules are followed and if it spots a threat, it immediately sends you an alert or report about it. The Heimdal XDR Agents are designed to communicate securely with the Heimdal XDR Dashboard through Transport Layer Security (TLS).
Threat Prevention Module
In the Threat Prevention section of the Heimdal XDR Agent, you get an up-close view of how your computer’s file system is being kept safe and secure. The module includes the following views:
Main view
In this view, you will find an overview of the most recent suspicious activity on the endpoint.
DarkLayer Guard view
In the main view, will find information about the Alazyed Traffic Requests, Prevented Attacks, and Prevented Attacks %.
Pressing the See Details button takes you to the following details: Blocked Traffic, Malware Blocked, TTPC, Date, and Action.
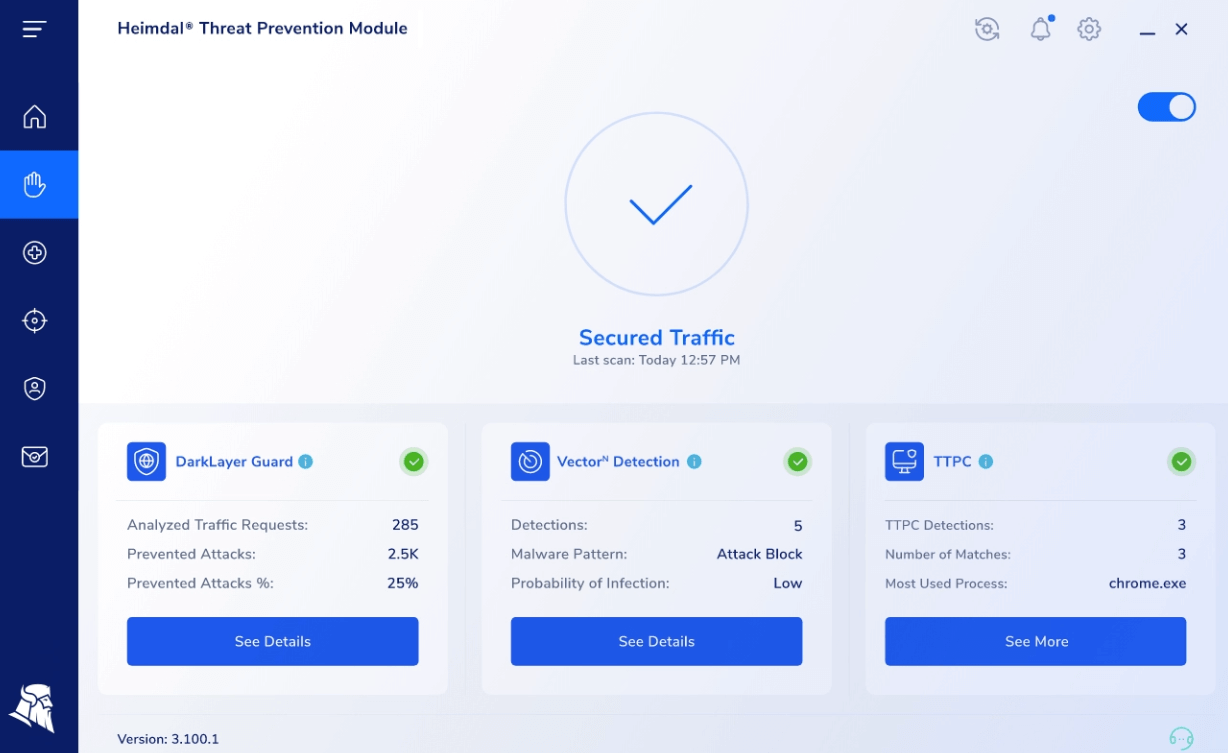
VectorN Detection view
In the main section, you can see the VectorN Detections, Malware Pattern, and Probability of Infection.
Pressing the See Details button takes you to the following details: Probability of infection, Number of Detections, Blocked Malware Pattern, Risk of infection, TTPC, Date, and Action.
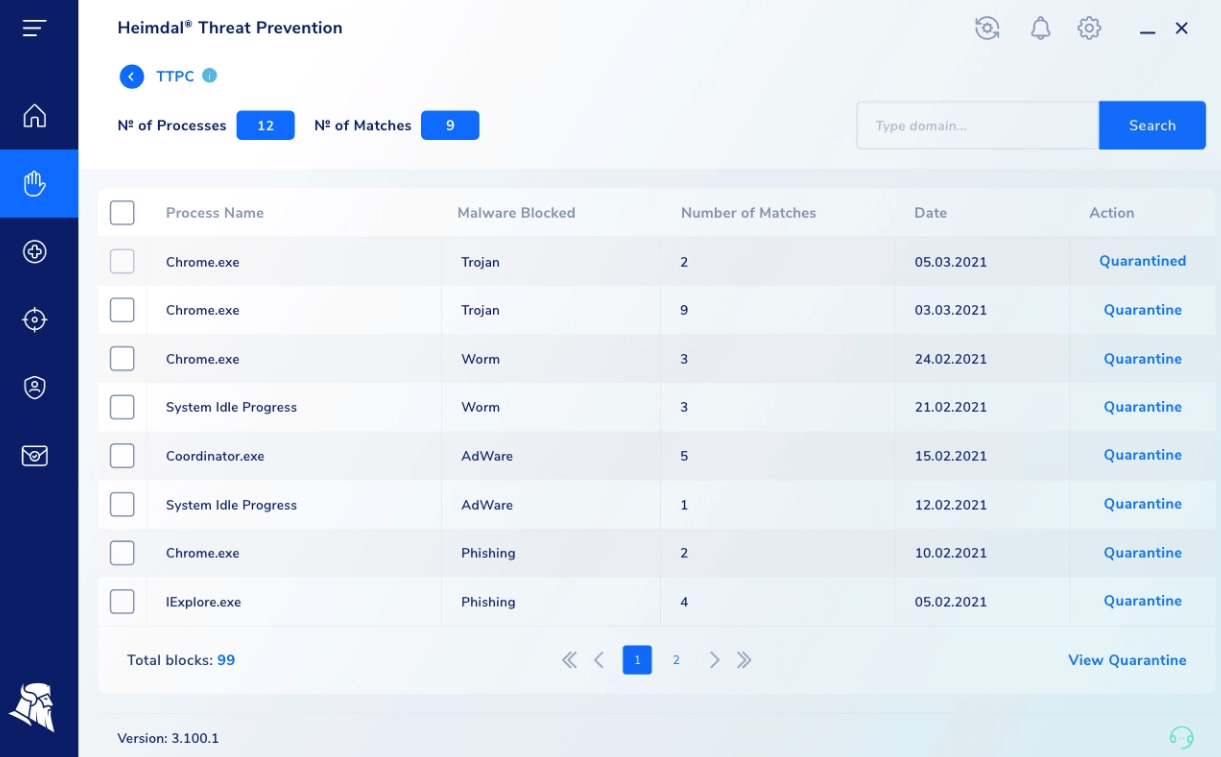
TTPC view
When enabled, whenever a malicious domain is queried, a pop-up window will be shown to you.
While you, as a user, can handle alerts from these views, IT Admins require a more in-depth grasp of endpoint activities. This is why exploring how to manage alerts from our dashboard is essential. Keep reading to discover the details.
Endpoint Detection (EDR)
In the Endpoint Detection section of the Heimdal XDR Agent, you get a big-picture view of how your machine’s file system is being protected. You’ll see useful stats like how many files are quarantined or infected, any Firewall alerts, and even detections of ransomware.
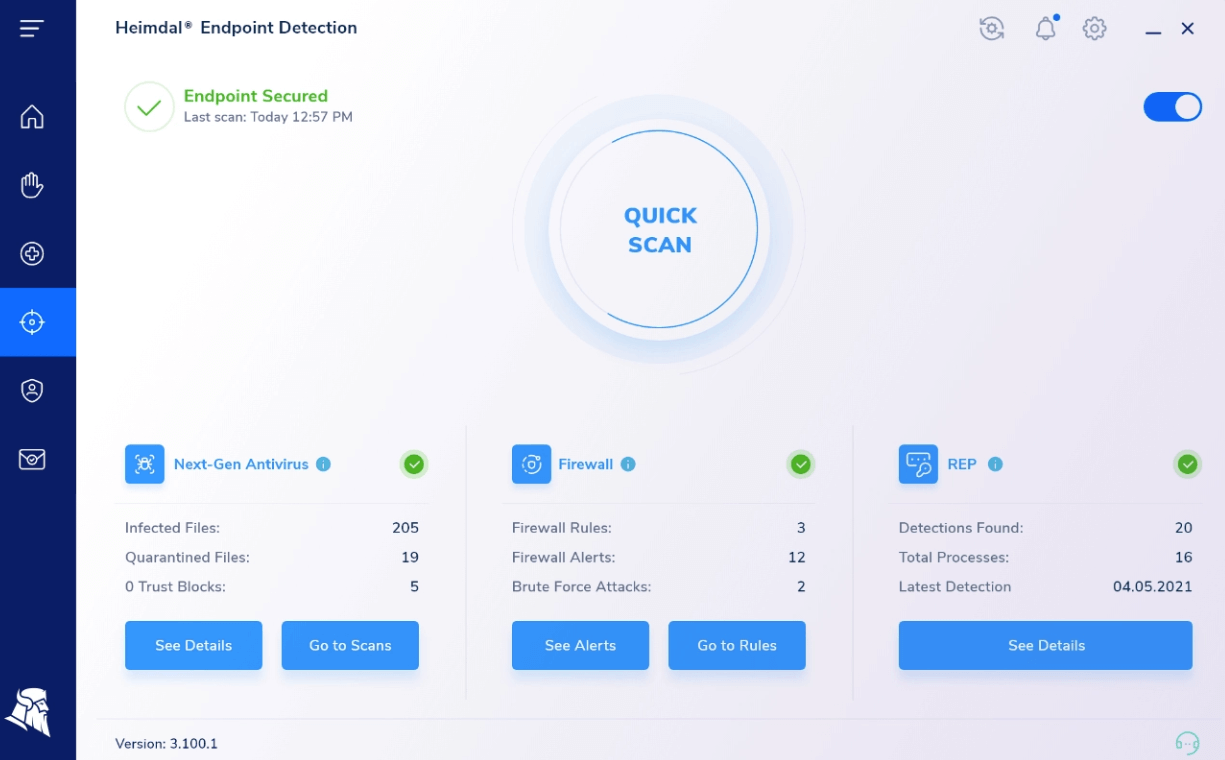
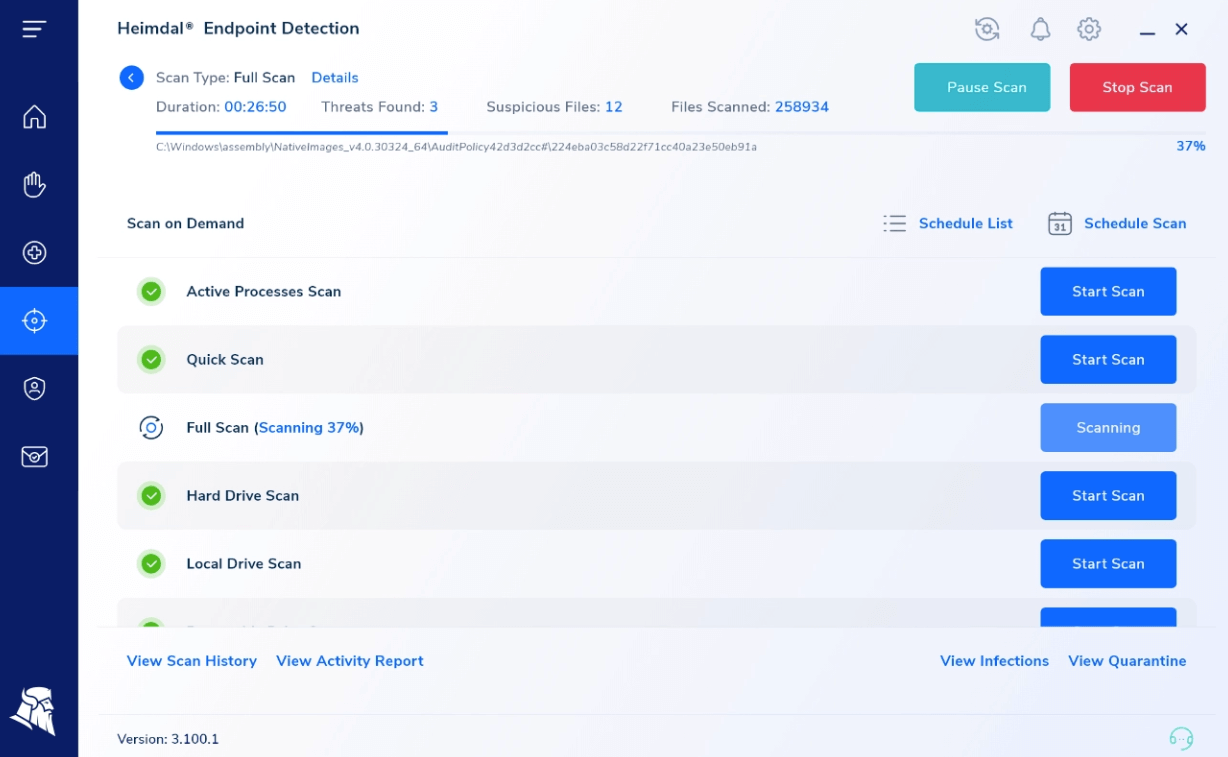
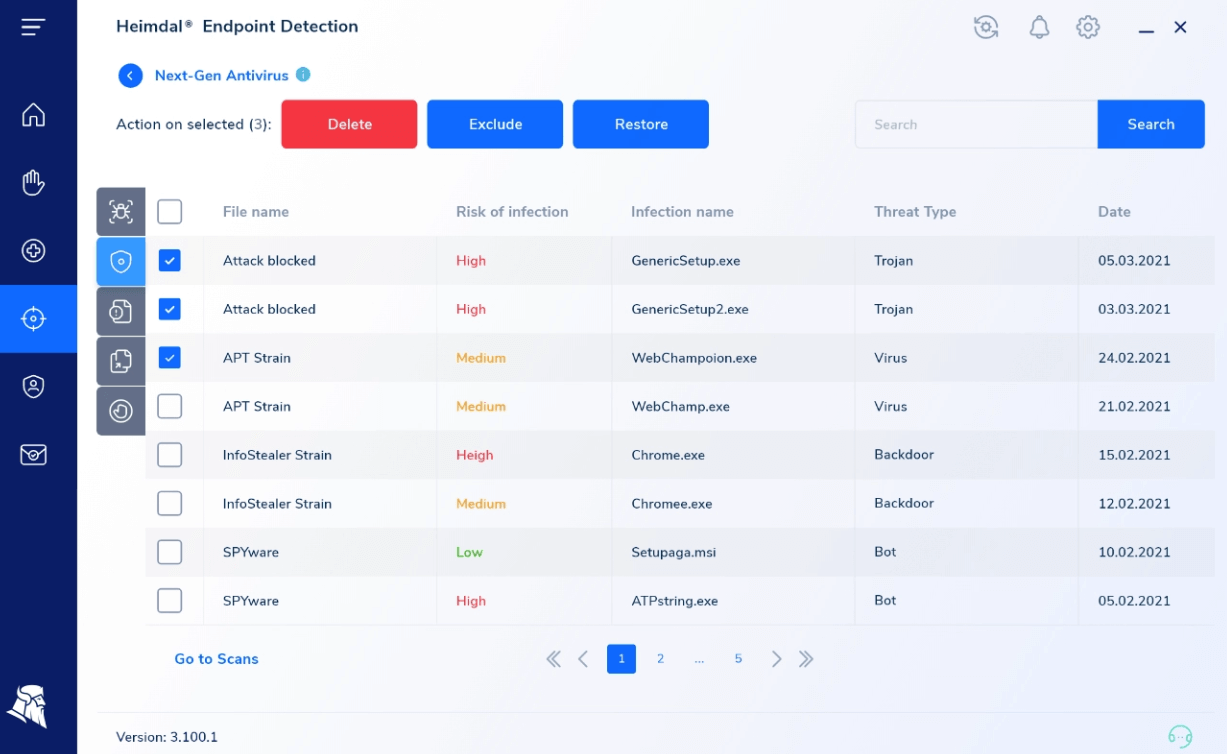
Next-Gen Antivirus view
Next-Gen Antivirus view allows you to run a scan or to stop a scan operation (if allowed in the Group Policy settings) and it also displays information about the detected infections and the quarantined files.
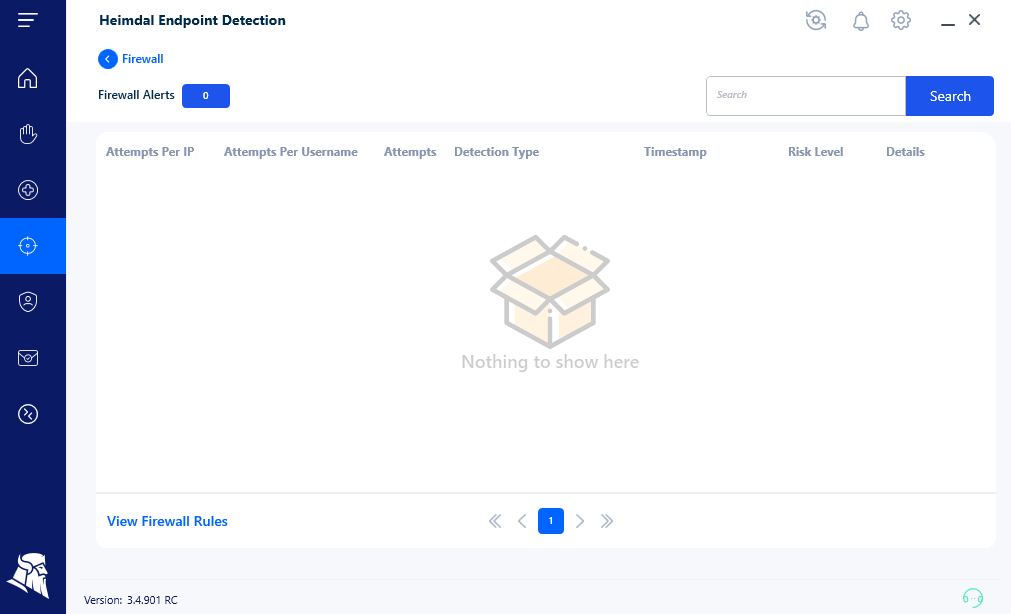
Firewall view
This view provides you with alerts about network activities that are recorded – these could be incoming or outgoing data transfers, potential attacks, or different types of requests. Continue reading to discover how to effectively manage this category of alerts utilizing our fully integrated platform.
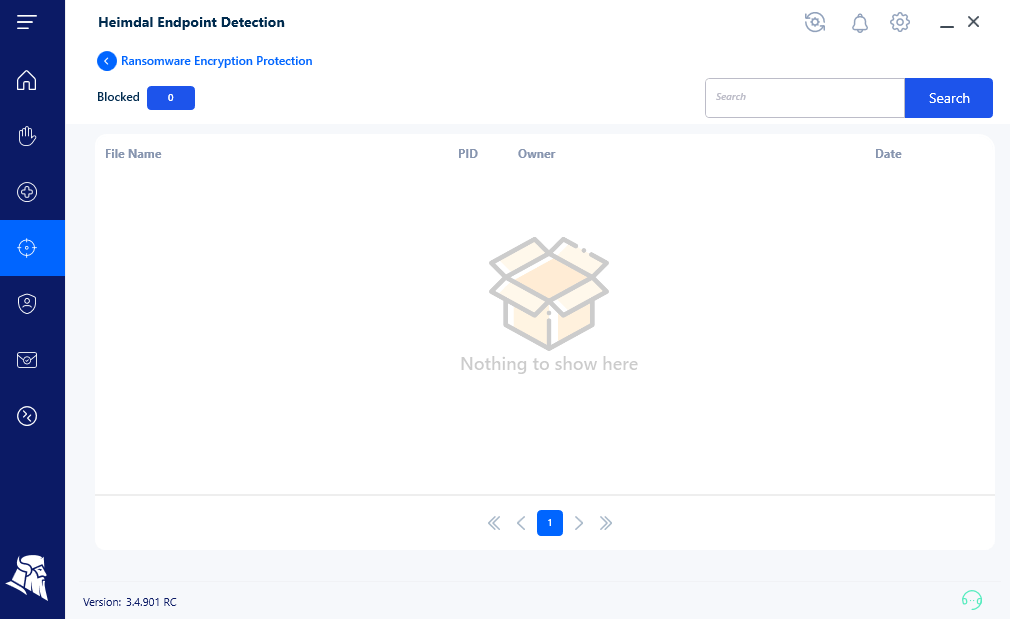
Ransomware Encryption Protection view
This feature plays a crucial role in identifying and preventing any recognized ransomware from locking up your data in a way that makes recovery impossible.
This feature works automatically around the clock, standing by to thwart these harmful events from taking place.
The Heimdal XDR Agent’s findings are effortlessly transmitted to the Heimdal XDR Dashboard. By exploring the next reading, you will learn the best methods for effectively managing alerts with our unrivaled 10-in-1 suite, an award-winning product that raises the standard for cybersecurity.
Heimdal XDR Dashboard
With the Heimdal XDR Unified Dashboard, you can easily view the data gathered from your setup and identify the threats that have been caught in your environment, enabling you to mitigate and act against them.
Threat Prevention – Network View
This view displays all the information collected by the HeimdalXDR Agent/ Heimdal Log Agent that is running on the DNS Server(s) in your organization.
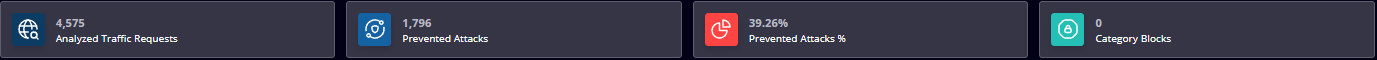
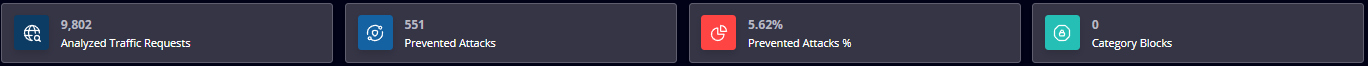
On the top, you see a statistic regarding the number of Analyzed Traffic Requests, Prevented Attacks, Prevented Attacks %, and the number of Category Blocks
The above-mentioned data is placed in the following views:
- Standard
The Standard view displays a table with the following details: Hostname (hostname of the endpoint making the request), IP Address (the local/internal IP Address of the endpoint making the request), Approved Requests, Prevented attacks, and Risk Level (Low, Medium or High.)
- Threat Type
This view displays a table with the following details: Threat Type and number of Hits.
- Latest Threats
This view displays a table with the following details: Hostname, IP Address, Domain, Threat Type, Date, and Time. The data can be filtered using the Latest Threats and Forensics filters.
- Category Blocks
This view displays a table with the following details: Hostname Domain, and Date
- Most Used Domains
This view displays a table with the following details: Domain and Total Hits. The data in this view updates every hour.
You can easily manage the Network alerts by:
- Turning ON/OFF the intercepted logs, allowing or blocking a domain/sub-domain for the users in your network;
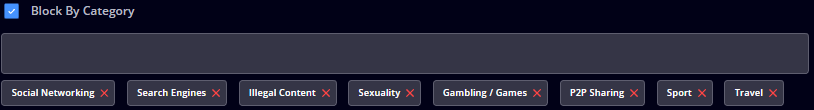
- Blocking groups of domains that are included in a category (for example Social, Sports, Gambling, Finance, Health, and others);
- Adding a custom HTML block page that will replace the default Heimdal block page when Threat Prevention – Network intercepts and blocks access to a malicious domain (or blocklisted domain);

- Adding your Public IP Address(es) to filter traffic through our DNS Servers, and much more.
Threat Prevention – Endpoint View
The collected information refers to the DNS queries that are filtered by the HEIMDAL XDR Agent’s DarkLayer Guard engine, described at the beginning of this article.
On the top, you see a statistic regarding the number of Analyzed Traffic Requests, the number of Prevented Attacks, the percentage of Prevented Attacks, and the number of Category Blocks.
The collected information is placed in the following views:
- Standard
This view displays a table with the following details: Hostname, Username, IP Address, Analyzed Requests, Prevented Attacks, and Risk Level.
- Threat Type
This view displays a table with the following details: Threat Type, Number of matches, Most Targeted Hostname, and Username.
- Hostname/Threats
This view displays a table with the following details: Hostname, Username, Domain Blocked, Threat Type, and Number of matches.
- Latest Threats
This view displays a table with the following details: Hostname, Username, Threat Type, Threat Type, Threat Source, TTPC, and Date.
- TTPC
This view displays a table with the following details: TTPC Detections, Number of matches, Most Targeted Hostname, Username, Most Frequently Detected Infected Domain, and Last Match.
- Category Blocks
This view displays a table with the following details: Hostname, Username, IP Address, and Category Blocked Domains.
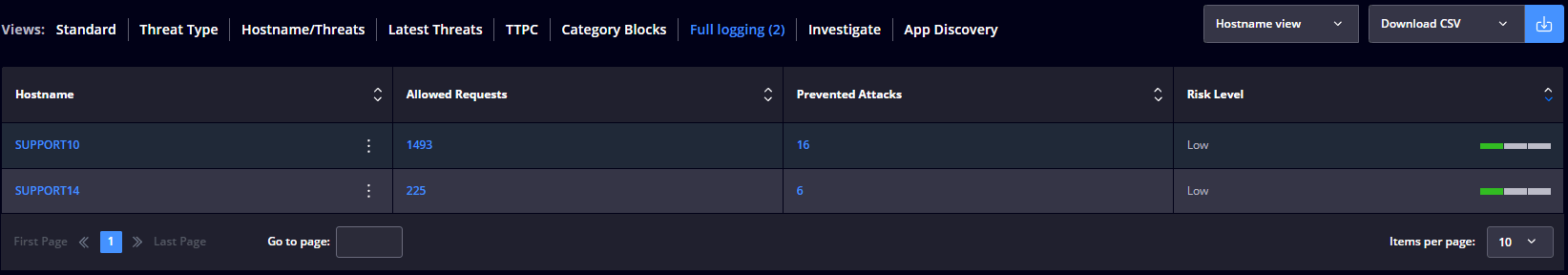
- Full Logging
The Hostname view displays a table with the following details: Hostname, Allowed Requests, Prevented Attacks, and Risk Level.
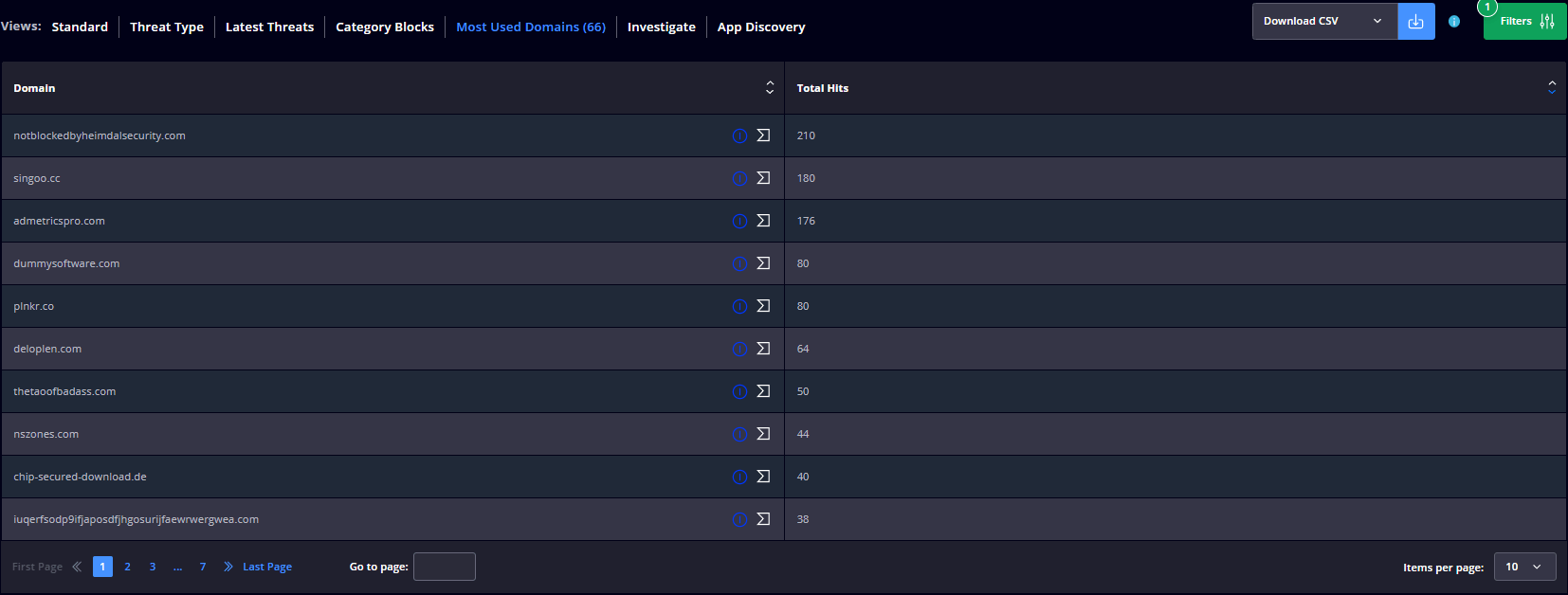
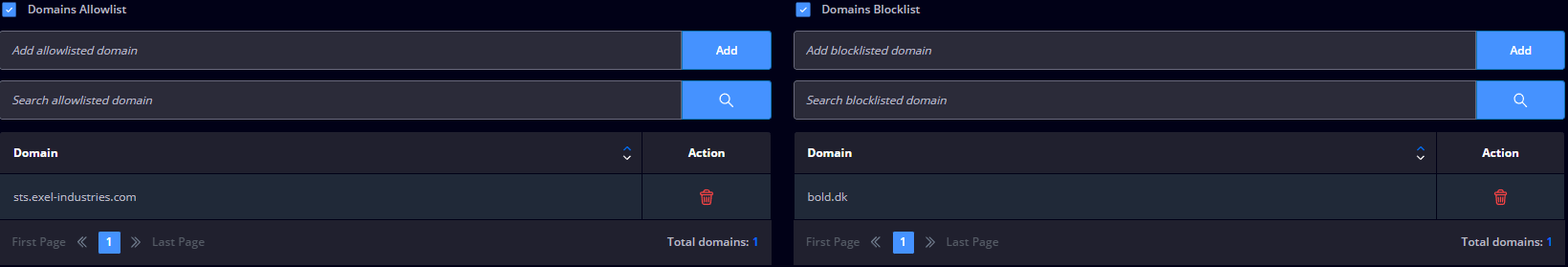
You can effortlessly handle alerts within the Endpoint view through:
- Full logging – Get enriched information on the DNS requests made from the endpoints (we log all the DNS requests made in your environment);
- Domains allowlist – This permits you to allowlist a domain that is blocked by the Heimdal Threat Prevention. You can allowlist domains, subdomains, top-level domains (.com, .co.uk, etc.), or even multiple domains at once by uploading a CSV file;
- Block by Category – This allows you to block groups of domains that are included in a category (for example Social, Sports, Gambling, Finance, Health, and others).
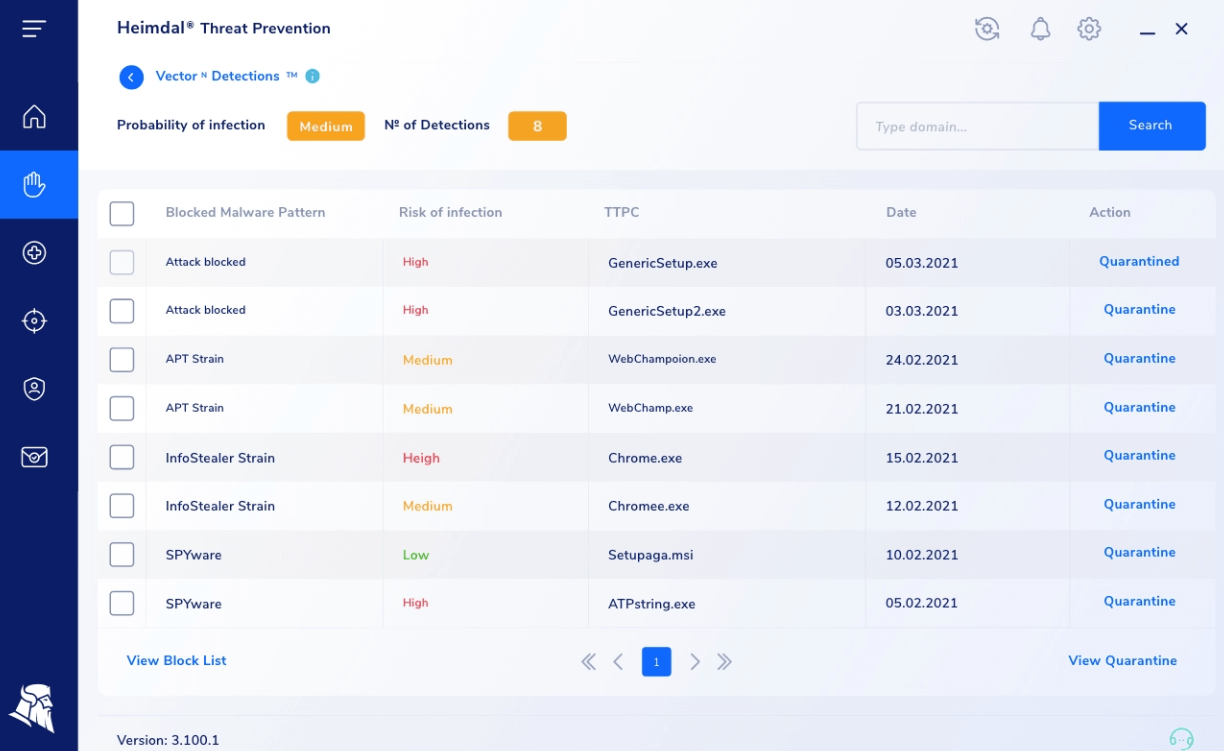
Threat Prevention – VectorN Detection view
The collected information refers to the patterns identified within the DarkLayer Guard domain blocks.

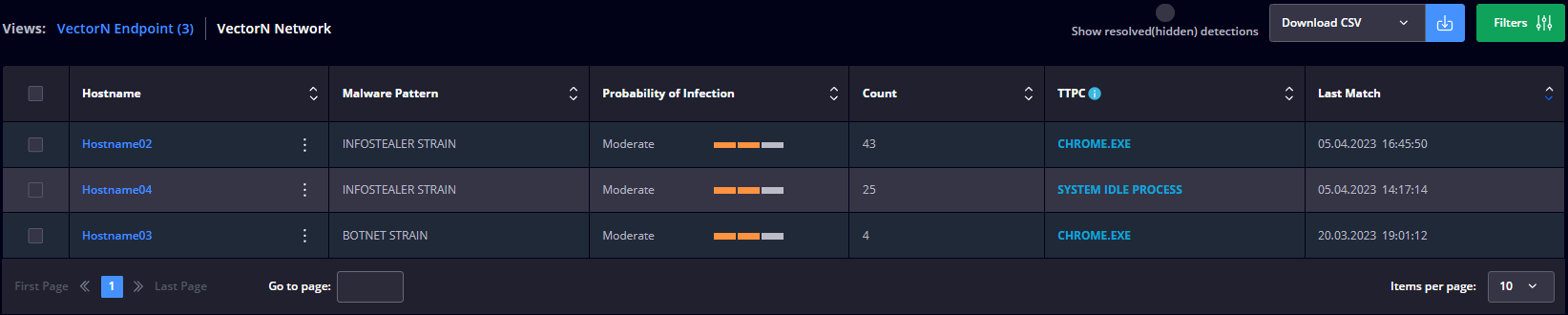
On the top, you see a statistic regarding the number of VectorN Detections.
The collected information is placed in the following views:
- VectorN Endpoint view
This view displays a table with the following details: Hostname, Malware Pattern, Probability of Infection, Count, TTPC, and Last Match.
- VectorN Network view
This view displays a table with the following details: Hostname, Malware Pattern, Probability of Infection, Count, and Last Match.
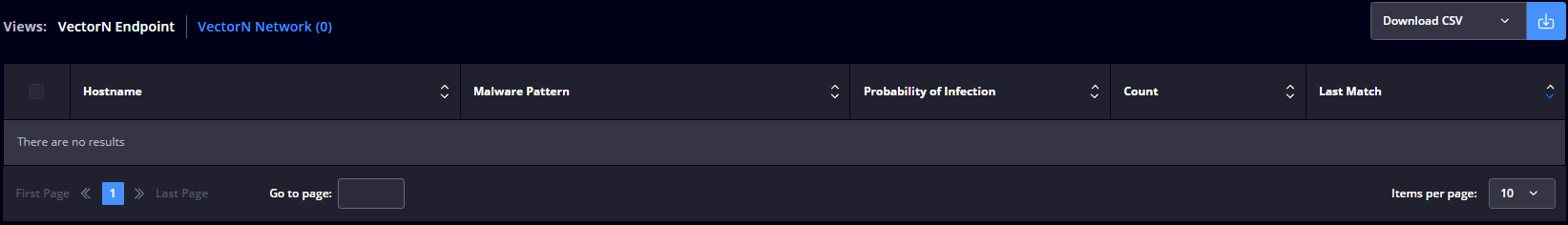
The following features make it simple to manage alerts inside the VectorN Detection view:
- Block by category – Exercise control over clusters of domains grouped under specific categories such as Social, Sports, Gambling, Finance, Health, and more, effectively blocking entire categories in one go.
- Domains allowlist – Grant permission for domains that were initially blocked by Heimdal Threat Prevention. This versatile feature lets you allowlist domains, subdomains, top-level domains (like .com, .co.uk, etc.), and even multiple domains simultaneously by importing a CSV file.
Endpoint Detection – Next-Gen Antivirus & MDM view
The Next-Gen Antivirus & MDM view presents a comprehensive overview of data gathered by the Heimdal XDR Agent on the endpoints within your organization.
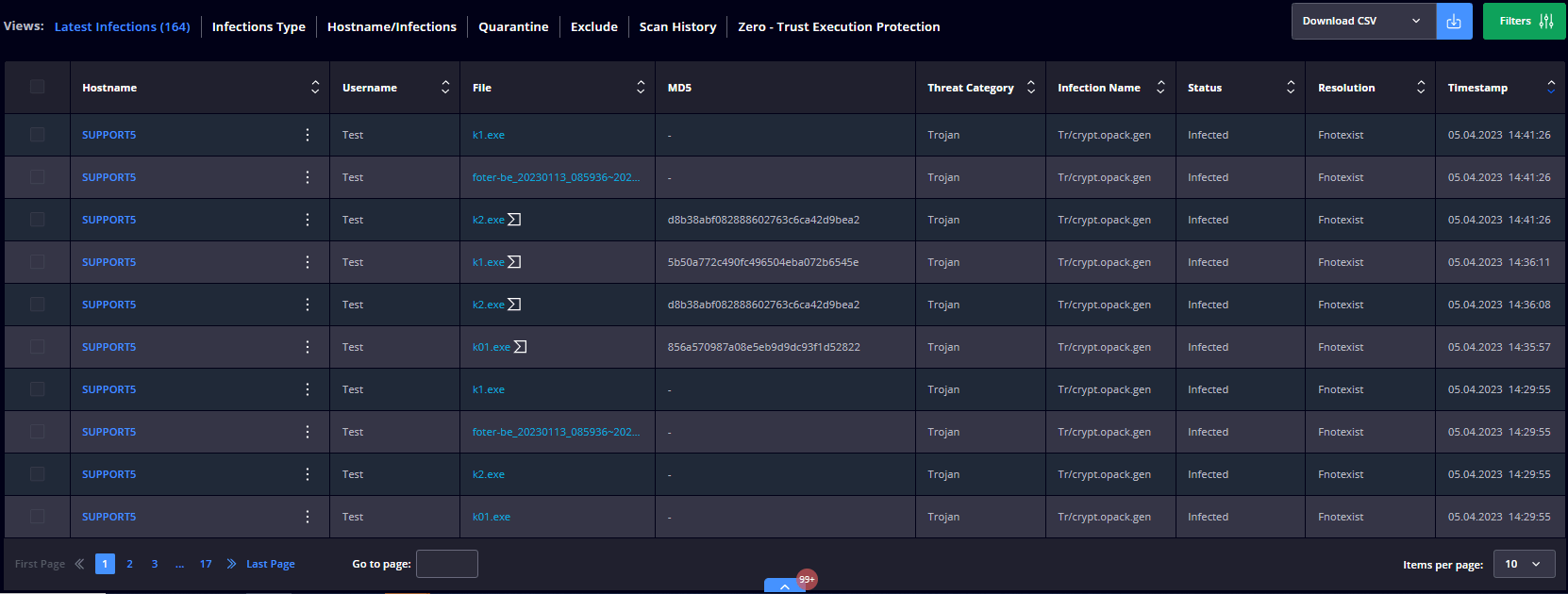
The collected information is placed in the following views:
- Latest Infections
This view allows you to select one or multiple infected files and add to quarantine, delete, or add to storage.
- Infections Type
This view displays a table with the infection type and the following details: Threat Category, Number of Matches, Most Targeted Hostname, Username, and Last match.
- Hostname/Infections
This view displays a table with the hostname/infections and the following details: Hostname, Username, Highest Threat Category, Number of Matches, and Last match.
- Quarantine view
This view displays a table with all quarantined files and the following details: Hostname, Username, File, MD5, Threat Category, Infection Name, Status, Resolution, and Timestamp. This view allows you to select one or multiple quarantined files and Remove them from quarantine or Add them to storage.
- Exclude view
This view displays a table of all exclusions and the following details: Hostname, Username, File, MD5, Threat Category, Infection Name, Status, Resolution, and Timestamp.
- Scan History view
This view displays a table with the computers that were performing scan operations and the following details Hostname, Username, Group Policy, Timestamp, New Infections Found, and Resolution. This view allows you to select one or multiple endpoints and select a scan type (Quick Scan, Full Scan, Active Processes Scan, Hard Drive Scan, Local Drive Scan, Removable Drive Scan, System Scan, Network Drive Scan).
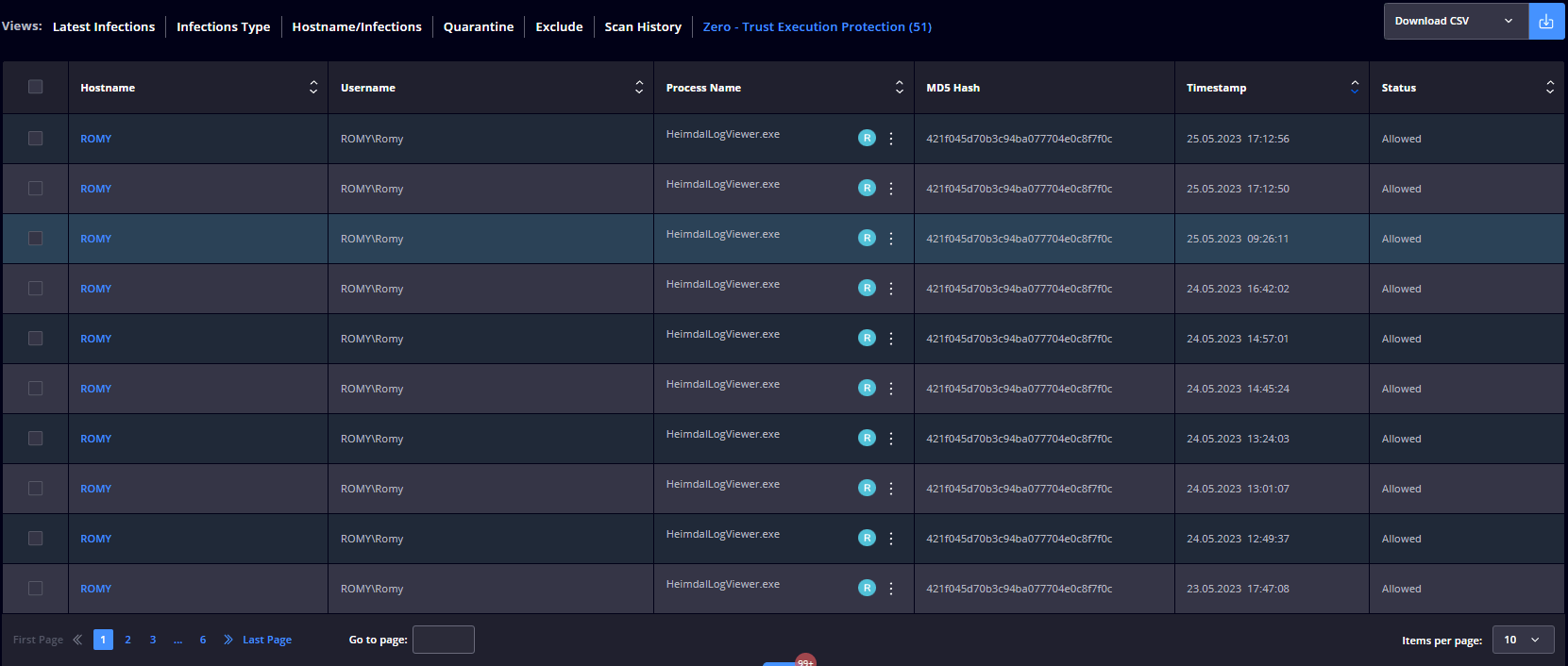
- Zero – Trust Execution Protection view
This view displays a table with the processes (non-signed executable files) intercepted by the Zero-Trust Execution Protection engine and the following details Hostname, Username, Process Name, MD5 Hash, Timestamp, and Status. Clicking the 3-dot button will give you the option to search the file hash on VirusTotal or to Copy the file path to the Clipboard.
You can easily handle Next-Gen Antivirus alerts through:
- Isolate on Tamper Detection – allows you to isolate a computer from the Internet if the HEIMDAL Security services are tampered with;
- Disable USB Ports – allows you to disable Removable Media Devices from being connected to a computer;
- Zero – Trust Execution Protection – checks the unsigned executable files and blocks their execution if deemed untrusted. You can also choose the reporting mode only, meaning that Zero-Trust Execution Protection will only scan and report the processes, without taking any action (allow or block). Also, selecting a file from the list allows you to add it to the exclusion list or upload it to the storage.
- Global Quarantine List – allows you to add a file to quarantine if it is detected by the Antivirus engine (the file will be marked as Suspicious or Infected). Based on the detection, you can also choose to delete, exclude, or remove a file from quarantine.
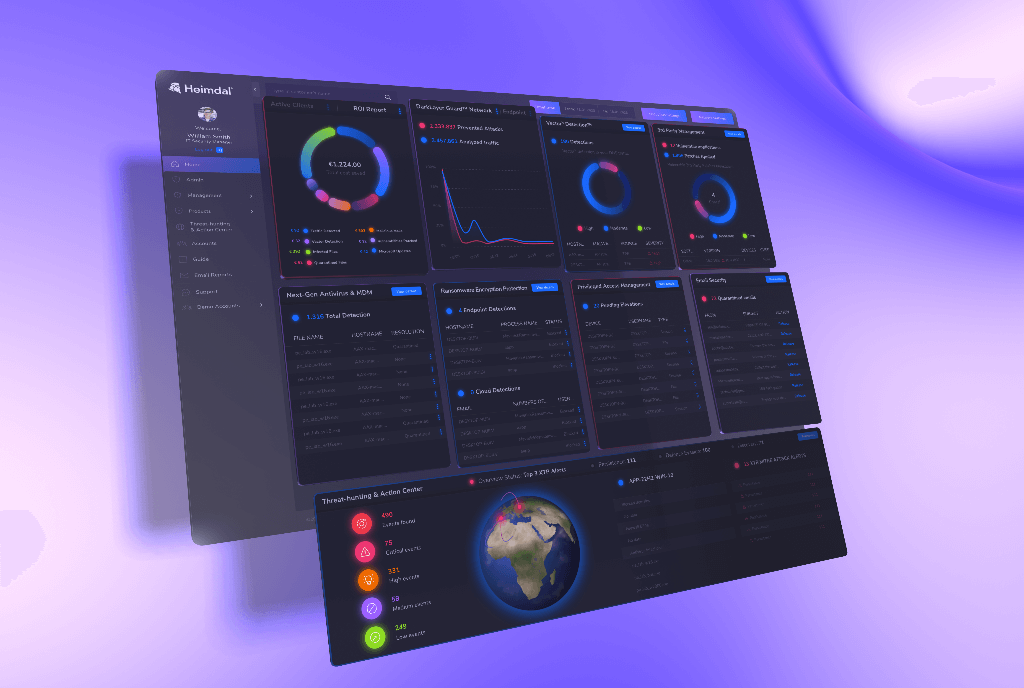
Endpoint Detection Extended Threat Protection (XTP) view
The Extended Threat Protection (XTP) engine provides solid evidence-based insights into complex cybersecurity risks and offers a comprehensive view of vulnerabilities, neatly organized based on MITRE ATT&CK tactics and techniques. This cutting-edge engine relies on information from over 1400 Sigma rules. The collected information is placed in the following views:
- Standard view
This view displays a table with the following details: Hostname, Rule Name, Severity, Process Name, Categories, and Detections.
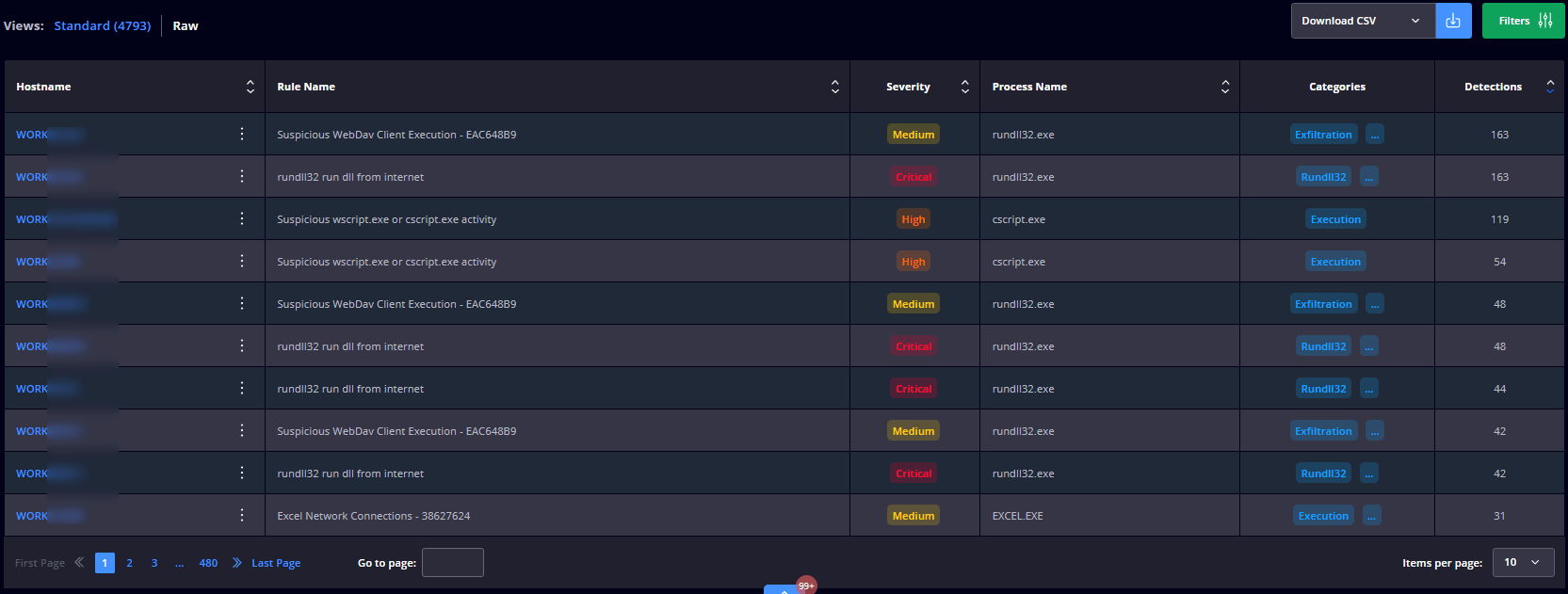
- Raw view
This view displays a table with the following details: Hostname, Rule Name, Severity, Process Name, PID, Categories, Timestamp, and Resolution.
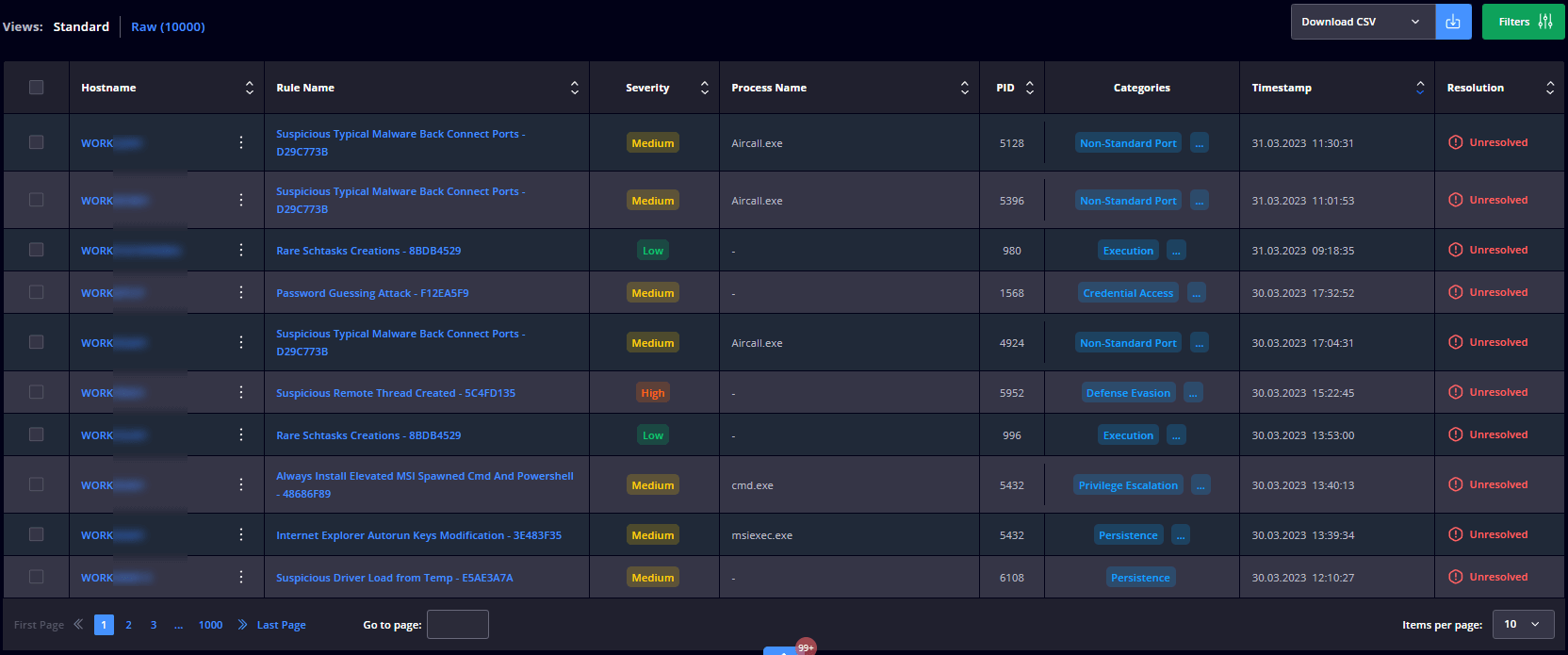
Next-Gen Antivirus with XTP
The addition of the XTP engine will supercharge the current Next-Gen Antivirus with Extended Threat Protection (XTP) capabilities, thus supplying you with evidence-based information about sophisticated cybersecurity risks, offering a holistic view of weaknesses, categorized on MITRE ATT&CK tactics and techniques and, ultimately, providing boundless levels of state-of-the-art protection.
Extended Threat Protection (XTP) stores information based on the system’s audit policies. These events are analyzed by the XTP engine, which can tell when a suspicious event occurred.
- Signature-based detection
Signature-based detection compares files coming into devices to known malware, looking for signature matches;
- Heuristic-based detection
Heuristic-based detection is similar to signature-based detection, however, while signature detection looks for exact matches, heuristic detection looks for similar tendencies or patterns in a file’s code;
- Behavior-based detection:
This form of detection examines how files and programs act, looking for anything out of the ordinary.
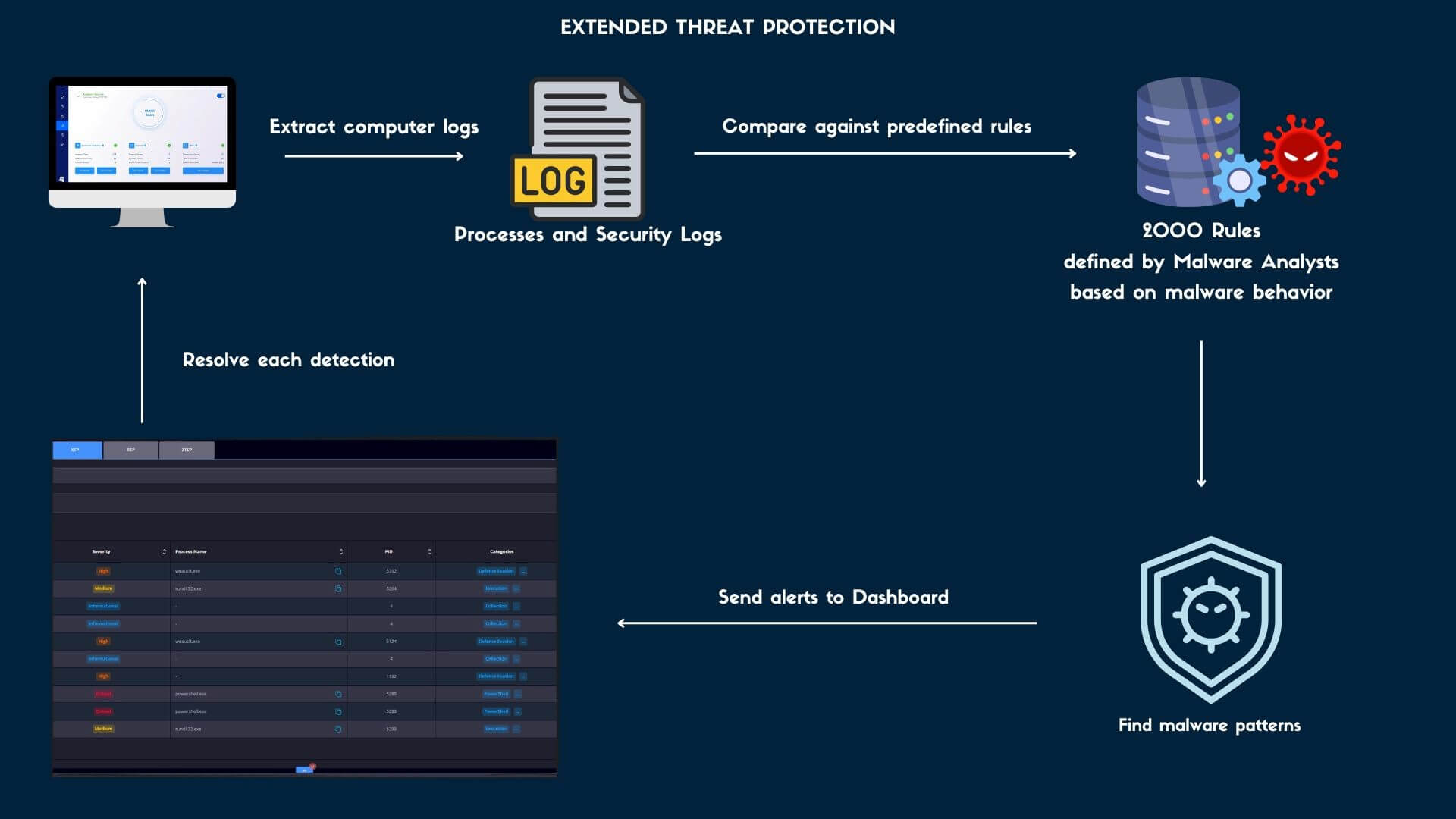
Whether attackers use exploits defense evasion, credential access, or exfiltration, the XTP engine has your back. It gives you an in-depth breakdown of the attack process, how the attack works, and the tactics employed.
You can easily manage XTP alerts through:
- Exclusions – Allows you to exclude a process by filename, file path, directory path, or MD5 by matching it with a rule found in the XTP engine.
- Rules – You can manually disable any of the rules listed under the XTP engine by unticking the Enabled tick box.
- Raw view – The checkbox allows you to select an entry and Resolve or Unresolve the event.
Endpoint Detection – Firewall Alerts view
This view displays a table with the following details: Hostname, Username, Local IP, Attempts Per Username, Attempts Per IP, Detection type, Timestamp, and Risk Level.

The entries that you see in this view include a list of all the unwanted connections that are interpreted as Brute Force Attacks.
You can effortlessly handle brute force attacks by:
- Adding the IP Address to the Brute Force Attack Allowlist.
- Blocking RDP port on brute force detection – automatically blocks the default RDP Port (3389) on the endpoint where an audit breach is detected for both TCP and UDP.
- Changing the default RDP Port (3389) to another port number
- Using automatic rules – allows you to select any of the profiles to enable/disable the Inbound/Outbound connections;
- Allowing isolation -allows you to isolate an endpoint in your network from the rest of the endpoints.
Endpoint Detection – Ransomware Encryption Protection (REP) view
This view displays all the information referring to the detected processes intercepted by the HEIMDAL XDR Agent that is running on the endpoints in your organization.
The Ransomware Encryption Protection module detects processes that perform encryption operations on files on the endpoint with malicious intent. The module is processing kernel events for IO reads, writes, directory enumeration, and file execution.
The collected information is placed in the following views:
- Latest Detections
This view displays a table with the following details: Hostname, Username, Process Name, Blocking Reason, PID, Owner, Status, and Timestamp.

- Hostname/Detections
This view displays a table with the following details: Hostname, Username, Number of Matches.

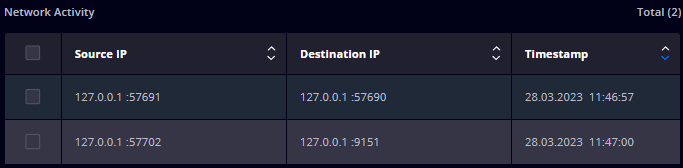
The Process Details gives you information on the parent process and the spawned processes, their PIDs, username, File Name, Path, Command-Line, Thread Count, top 3 encrypted files, Write Operations, Read Operations, MD5, Signature, and Owner.
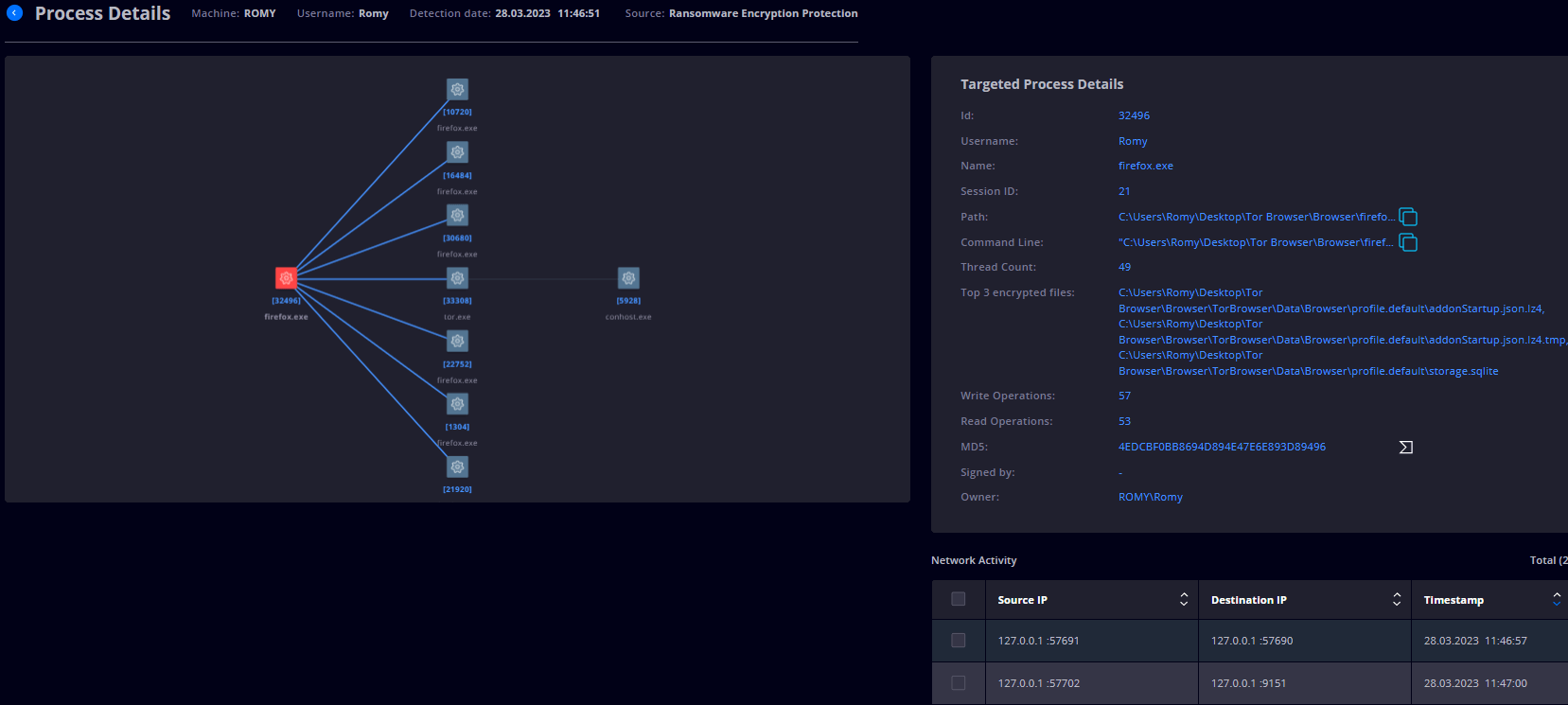
Managing ransomware encryption protection alerts requires a comprehensive approach. That’s why, in this view, you will find vital details and actions steps that you can take in order to minimize the impact on your environment:
How to manage Ransomware Encryption Protection alerts like a Pro with Heimdal XDR:
- The REP view allows you to select one or multiple infected files and exclude it/them or add it/them to storage for a further in-depth investigation;
- In the Process Name column, you can click on the process (or on the Forensics ‘F’ icon) to see the process details or you can click on the VirusTotal icon to get a detailed VirusTotal analysis.
- Get information on the Network Activity of the detected process, where you can select one or multiple IP Addresses to block them in the Firewall (on one, multiple, or all Group Policies).
- Make exclusions by selecting one or more detections and by pressing the Exclude and Apply buttons from the dropdown menu.
- Isolate on Tamper Detection – allows you to turn ON/OFF the isolation feature when a Tamper Detection is being made.
Mastering XDR Alert Management with Heimdal
By following the insights and strategies outlined in this comprehensive user guide, you’re equipped to navigate the dynamic world of threat detection and response. From gaining full visibility into network activities to pinpointing the root causes of alerts, the Heimdal XDR solution empowers you to proactively protect your systems, devices, and sensitive data.
The next level of security – powered by the Heimdal Unified Security Platform
Experience the power of the Heimdal cloud-delivered XDR platform and protect your organization from cyber threats.
- End-to-end consolidated cybersecurity;
- Complete visibility across your entire IT infrastructure;
- Faster and more accurate threat detection and response;
- Efficient one-click automated and assisted actioning
Original Post URL: https://heimdalsecurity.com/blog/how-to-manage-xdr-alerts-with-heimdal/
Category & Tags: Uncategorized – Uncategorized
Views: 5