- Home
- About Us
- Contact Us
- Register to apply for a free CISO2CISO Membership
- CISO2CISO Network
- CISO2CISO Services
- Sitemap
- Submit News
IT Information Security
MORE RESOURCES
CISO Strategics

cyber operations & soc

red - blue & purple teams

THREAT INTELLIGENCE

VULNERABILITIES

CYBER ATTACKS

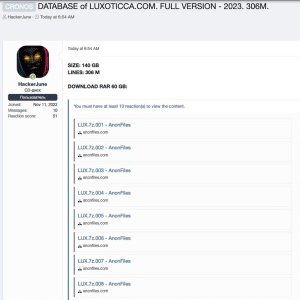
DATA BREACH
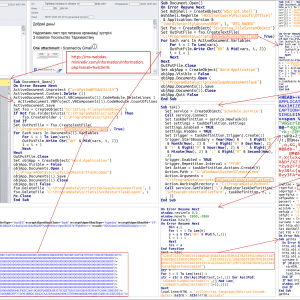
MALLWARE

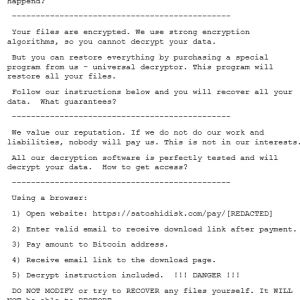
RANSOMWARE
DDOS ATTACKS

CLOUD SECURITY

IOT SECURITY

hacking

CISO
STRATEGICS
- CISO Strategics
- CISO Learn & Leadership
- Cybersecurity for C-Levels
- Cybersecurity Trends & Insights
- Cyberseurity Awareness
- Cybercrimen Ecosystem
- Cybersecurity Measure & Metrics
- Cybersecurity Frameworks
- Cybersecurity Policy & Standars
- Fraud
- Information Security
- Osint - Humint
- Privacy
- Risk & Compliance
- Resilience
- Social Engineering
- Supply Chain Security
CYBER
ARCHITECTURE
- API Security
- Application Security
- Blockchain Security
- Cloud Security
- Data Security
- Defense in Depth
- DevSecOps
- Endpoint Security
- IA Security
- IOT Security
- MAC-OS Security
- Metaverse Security
- Micro segmentation
- Mitre Att&ck
- Mobile & 5G Security
- Network Security
- OT Security
- OWASP Security
- Perimeter Security
- SAP Security
- Telco & Carrier Security
- Zero Trust Security
SOC CSIRT
OPERATIONS
- Cyber Incidents & Attacks Notepad
- CSIRT Operations
- Data Leak & Breach Incidents Notepad
- DDOS Attacks
- DFIR - Forensics & Incident Response
- Dark & Deep Web
- SOC Operations
- SIEM Use Cases & Playbooks
- SOAR Authomation & Playbooks
- Malware & Ransomware
- Red - Blue & Purple Teams Operations
- Threat Intelligence
- Threat Hunting
- Vulnerabilities
CYBERSECURITY
VENDORS
- Akamai
- A10 Networks
- Blackberry Cylance
- Cisco
- Cyberark
- Cloudfare
- Crowdstrike
- Checkpoint
- F5 Networks
- FyreEye
- Fortinet
- Guardicore
- IBM
- Kaspersky
- Mcafee - Trellix
- Mandiant
- Maltego
- Microsoft
- Netscope
- Palo Alto Networks
- RSA Security
- Redhat
- Splunk
- Symantec
- Tenable
- Trendmicro
CYBERSECURITY
MSSP
- Accenture
- Attos
- AT&T Cybersecurity
- BT Security
- BASE 4 - Hispam
- Deloitte
- Entelgy Security
- KPMG
- NTT Security
- Novared - Hispam
- Neosecure - Hispam
- Orange Cyberdefense
- PwC
- Telefonica Tech
- Thales
- Verizon Security