Source: www.cybertalk.org – Author: slandau EXECUTIVE SUMMARY: In the past year, 80% of organizations have encountered a major cloud-based cyber threat. To limit risk and to...
Author:
6 most common cyber security vulnerabilities you should know in 2023 – Source: www.cybertalk.org
Source: www.cybertalk.org – Author: slandau Contributed by George Mack, Content Marketing Manager, Check Point Software. Nearly all security incidents stem from cyber security vulnerabilities. What is...
Battling DDoS attacks in the cloud – Source: www.cybertalk.org
Source: www.cybertalk.org – Author: slandau Grant Asplund is a proven multi-channel senior sales and marketing executive with history of exemplary achievement introducing/launching new products and establishing...
MGM Resorts had $339M compromised in 10 minutes or less – Source: www.cybertalk.org
Source: www.cybertalk.org – Author: slandau EXECUTIVE SUMMARY: Hackers launched an attack that hit MGM Resorts on Sunday morning, rendering doors to buildings unusable, and ATM machines...
Cloud security monitoring: Benefits, best practices and more – Source: www.cybertalk.org
Source: www.cybertalk.org – Author: slandau EXECUTIVE SUMMARY: What is cloud security monitoring? Cloud security monitoring refers to the practice of overseeing both virtual and physical servers...
Cracking the blockchain code: Expert perspectives on security and vulnerabilities – Source: www.cybertalk.org
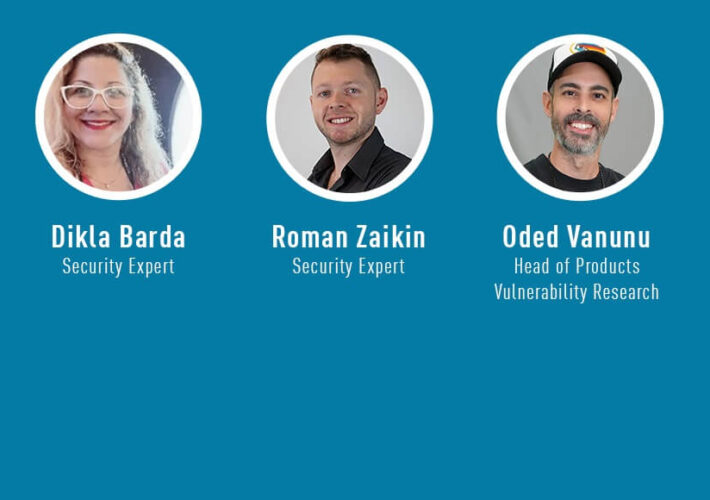
Source: www.cybertalk.org – Author: slandau Are you as knowledgeable as these experts when it comes to blockchain, cryptocurrency and cyber security? In this exceptional interview, the...
A 10-point checklist: Owning your cloud security assessment – Source: www.cybertalk.org
Source: www.cybertalk.org – Author: slandau EXECUTIVE SUMMARY: Nearly 90% of businesses have taken a multi-cloud approach, and 97% of IT leaders intend to expand cloud systems....
A 10-point checklist: Owning your cloud security assessment – Source: www.cybertalk.org
Source: www.cybertalk.org – Author: slandau EXECUTIVE SUMMARY: Nearly 90% of businesses have taken a multi-cloud approach, and 97% of IT leaders intend to expand cloud systems....
Why Australian companies need to adopt zero trust… now – Source: www.cybertalk.org
Source: www.cybertalk.org – Author: slandau By Sadiq Iqbal, Security Engineering Manager and Check Point Evangelist. It might be on the ‘to-do’ lists of many CISOs, yet...
Damaging hack? Compensation could be in the balance – Source: www.cybertalk.org
Source: www.cybertalk.org – Author: slandau EXECUTIVE SUMMARY: Key highlights In 2022, a small number of public companies (86 total) linked chief executive pay to cyber security....
IoMT: The keys to connected care excellence – Source: www.cybertalk.org
Source: www.cybertalk.org – Author: slandau Antoinette Hodes is a Global Solutions Architect, specializing in IoT, and serves as an Evangelist with the Check Point Office of...
Mystery hacking group targets space telescopes – Source: www.cybertalk.org
Source: www.cybertalk.org – Author: slandau EXECUTIVE SUMMARY: Two major astronomy observatories – the Gemini North Telescope in Hawaii and the Gemini South Telescope in Chile –...
Who owns the song you wrote with AI? An expert explains – Source: www.cybertalk.org
Source: www.cybertalk.org – Author: slandau By Douglas Broom, Senior Writer, Forum Agenda. Key Information: Artificial intelligence potentially empowers us all to become creators – but who...
Two brothers on a journey: Unleashing AI to defeat $200B chargeback problem – Source: www.cybertalk.org
Source: www.cybertalk.org – Author: slandau Ariel and Avia Chen, Israeli-American entrepreneurs, have been on a remarkable journey that led them from their passion for technology –...
Autonomous vehicles pros and cons: A comprehensive analysis – Source: www.cybertalk.org
Source: www.cybertalk.org – Author: slandau EXECUTIVE SUMMARY: While 70% of Americans are afraid of self-driving cars, it’s worth noting that a staggering 94% of all traffic...
The synergy between Cyber Security Mesh & the CISO role: Adaptability, visibility and control – Source: www.cybertalk.org
Source: www.cybertalk.org – Author: slandau With over two decades of experience in the cyber security industry, I specialize in advising organizations on how to optimize their...
Japan’s cyber security agency suffers email breach – Source: www.cybertalk.org
Source: www.cybertalk.org – Author: slandau EXECUTIVE SUMMARY: Japan’s National Center of Incident Readiness and Strategy for Cybersecurity (NISC) has experienced a breach. Sensitive network data may...
Eggs-cellent email: How cooking with eggs showcases the promise & peril of email security – Source: www.cybertalk.org
Source: www.cybertalk.org – Author: slandau Jeremy Fuchs is the Content Marketing Specialist for Harmony Email & Collaboration. Previously, he worked at Avanan, which was acquired by...
10 SASE benefits that you should be aware of – Source: www.cybertalk.org
Source: www.cybertalk.org – Author: slandau EXECUTIVE SUMMARY: The Secure Access Service Edge (SASE) framework emerged in 2019, as industry analysts observed new use cases and buying...
These 7 items should be on your CISO checklist for 2024 – Source: www.cybertalk.org
Source: www.cybertalk.org – Author: slandau EXECUTIVE SUMMARY: As a Chief Information Security Officer (CISO), you’re entrusted with orchestrating a harmonious convergence of technology, strategic acumen, and...
How AI turbocharges your threat hunting game – Source: www.cybertalk.org
Source: www.cybertalk.org – Author: slandau EXECUTIVE SUMMARY: Over 90 percent of organizations consider threat hunting a challenge. More specifically, seventy-one percent say that both prioritizing alerts...
EV security: Should you worry about these hacks? – Source: www.cybertalk.org
Source: www.cybertalk.org – Author: slandau EXECUTIVE SUMMARY: The market for electric vehicles (EVs) has expanded exponentially across the past few years and is expected to grow...
10 top corporate account takeover prevention strategies – Source: www.cybertalk.org
Source: www.cybertalk.org – Author: slandau EXECUTIVE SUMMARY: A corporate account takeover can present significant risks for any organization. A corporate account takeover can have detrimental, far-reaching...
Safeguarding your organization from ChatGPT threats – Source: www.cybertalk.org
Source: www.cybertalk.org – Author: slandau Mazhar Hamayun is a cyber security professional with over 20 years of hands-on technology and leadership experience. At Check Point Software,...
10 top corporate account takeover prevention strategies – Source: www.cybertalk.org
Source: www.cybertalk.org – Author: slandau EXECUTIVE SUMMARY: A corporate account takeover can present significant risks for any organization. A corporate account takeover can have detrimental, far-reaching...
Africa Cyber Surge II: $40 million, 20,000 networks & 25 countries – Source: www.cybertalk.org
Source: www.cybertalk.org – Author: slandau EXECUTIVE SUMMARY: The Africa Cyber Surge II operation has led to the take-down of rogue networks that were responsible for financial...
A third of companies hit with ransomware didn’t have to pay…Here’s how they did it – Source: www.cybertalk.org
Source: www.cybertalk.org – Author: slandau By Pete Nicoletti, Check Point Field CISO, Americas One in ten victims of ransomware pay ransoms of over $1 million. With...
What is trap phishing? (2023) – Source: www.cybertalk.org
Source: www.cybertalk.org – Author: slandau EXECUTIVE SUMMARY: In the complex and vast landscape of cyber security, a subtle danger lurks – trap phishing. As organizations and...
The best AI security management (and the ultimate upgrades) – Source: www.cybertalk.org
Source: www.cybertalk.org – Author: slandau EXECUTIVE SUMMARY: Artificial intelligence has transcended its status as a buzzword and has become a true catalyst for digital transformation. As...
Catch rates: 5% can cost you $1.3M in risk per week – Source: www.cybertalk.org
Source: www.cybertalk.org – Author: slandau Keely Wilkins is an Evangelist with the Office of the CTO as well as a Pre-Sales Security Engineer at Check Point....