April 12, 2023 By Pierluigi Paganini SAP fixed two critical bugs that affect the Diagnostics Agent and the BusinessObjects Business Intelligence Platform. SAP April 2023 security updates include...
Author:
OpenAI launched a bug bounty program
AI company OpenAI launched a bug bounty program and announced payouts of up to $20,000 for security flaws in its ChatGPT chatbot service. OpenAI launched a...
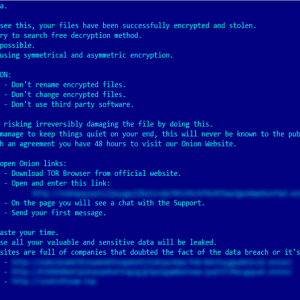
Cybercrime group exploits Windows zero-day in ransomware attacks
Microsoft has addressed a zero-day in the Windows Common Log File System (CLFS) actively exploited in ransomware attacks. Microsoft has addressed a zero-day vulnerability, tracked as...
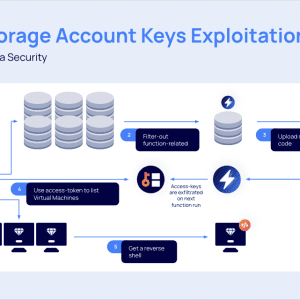
A “By-Design” flaw in Microsoft Azure can allow storage accounts takeover
A flaw in Microsoft Azure could be exploited by attackers to gain access to storage accounts, perform lateral movements, and even execute remote code. Researchers from...
Yum! Brands, the owner of KFC, Taco Bell and Pizza Hut, discloses data breach
Yum! Brands, the company that owns the KFC, Pizza Hut, and Taco Bell brands, disclosed a data breach after the January ransomware attack. On January 13,...
Apple released emergency updates to fix recently disclosed zero-day bugs on older devices
Apple released updates to backport patches addressing two actively exploited zero-day vulnerabilities in older iPhones, iPads, and Macs. Apple has released emergency updates to backport security patches that...
A cyber attack hit the water controllers for irrigating fields in the Jordan Valley
A cyber attack paralyzed the water controllers for irrigating fields in the Jordan Valley that are operated by the Galil Sewage Corporation. A cyberattack blocked several...
CISA adds zero-day bugs in iPhones, Macs, and iPads to its Known Exploited Vulnerabilities catalog
US Cybersecurity and Infrastructure Security Agency (CISA) added two flaws in iPhones, Macs, and iPads to its Known Exploited Vulnerabilities catalog. U.S. Cybersecurity and Infrastructure Security...
SD Worx shuts down UK and Ireland services after cyberattack
Belgian HR giant SD Worx was forced to shut down its IT infrastructure for its UK and Ireland services after a cyber attack. HR and payroll...
Sophos patches three issues in the Sophos Web Security appliance, one of them rated as critical
Sophos addressed three vulnerabilities in Sophos Web Appliance, including a critical flaw that can lead to code execution. Cybersecurity vendor Sophos addressed three vulnerabilities in Sophos...
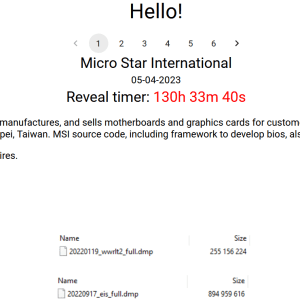
Iran-linked MERCURY APT behind destructive attacks on hybrid environments
Iran-linked APT group MERCURY is behind destructive attacks on hybrid environments masquerading as a ransomware operation. The Microsoft Threat Intelligence team observed a series of destructive attacks...
Samsung employees unwittingly leaked company secret data by using ChatGPT
Samsung employees have unwittingly leaked top secret data by providing them to the popular chatbot service ChatGPT. Samsung employees have shared internal documents, including meeting notes...
Researchers disclose critical sandbox escape bug in vm2 sandbox library
The development team behind the vm2 JavaScript sandbox library addressed a critical Remote Code Execution vulnerability. The developers behind the vm2 JavaScript sandbox module have addressed...
Security Affairs newsletter Round 414 by Pierluigi Paganini – International edition
Privacy Overview This website uses cookies to improve your experience while you navigate through the website. Out of these cookies, the cookies that are categorized as...
Estonian National charged with helping Russia acquire U.S. hacking tools and electronics
Andrey Shevlyakov, an Estonian national, was charged in the US with conspiracy and other charges related to acquiring U.S.-made electronics on behalf of the Russian government...
CISA adds Veritas Backup Exec flaws to its Known Exploited Vulnerabilities catalog
US CISA has added Veritas Backup Exec flaws, which were exploited in ransomware attacks, to its Known Exploited Vulnerabilities catalog. U.S. Cybersecurity and Infrastructure Security Agency...
Apple addressed two actively exploited zero-day flaws
Apple released emergency security updates to address two actively exploited zero-day vulnerabilities impacting iPhones, Macs, and iPads. Apple has released emergency security updates to address two...
Microsoft aims at stopping cybercriminals from using cracked copies of Cobalt Strike
Microsoft announced it has taken legal action to disrupt the illegal use of copies of the post-exploitation tool Cobalt Strike by cybercriminals. Cobalt Strike is a paid...
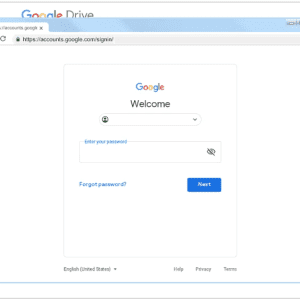
Phishers migrate to Telegram
Experts warn that Telegram is becoming a privileged platform for phishers that use it to automate their activities and for providing various services. Kaspersky researchers have...
OCR Labs exposes its systems, jeopardizing major banking clients
A digital identification tool provided by OCR Labs to major banks and government agencies leaked sensitive credentials, putting clients at severe risk. London-based OCR Labs is...
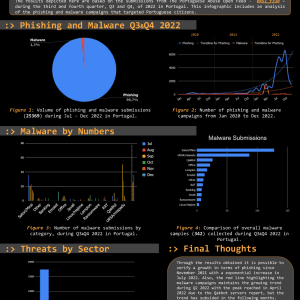
Threat Report Portugal: Q3 & Q4 2022
The Threat Report Portugal: H2 2022 compiles data collected on the malicious campaigns that occurred from July to December, H2, 2022. The Portuguese Abuse Open Feed 0xSI_f33d is...
Analyzing attacks conducted by North Korea-linked ARCHIPELAGO APT group
Google’s Threat Analysis Group (TAG) warns of a North Korea-linked cyberespionage group tracked as ARCHIPELAGO. Google’s Threat Analysis Group (TAG) is warning of the North Korea-linked...
Nexx bugs allow to open garage doors, and take control of alarms and plugs
A series of vulnerabilities in multiple smart devices manufactured by Nexx can be exploited to remotely open garage doors, and take control of alarms and plugs....
Tax preparation and e-file service eFile.com compromised to serve malware
The eFile.com online service, which is authorized by the US Internal Revenue Service (IRS), was spotted serving malicious malware to visitors. eFile.com, the personal online tax...
HP would take up to 90 days to fix a critical bug in some business-grade printers
HP would take up to 90 days to address a critical flaw, tracked as CVE-2023-1707, that resides in the firmware of some business-grade printers. HP is...
CISA JCDC Will Focus on Energy Sector
The CISA ‘s Joint Cyber Defense Collective (JCDC) initiative is going to build operation plans for protecting and responding to cyber threats. What comes to mind...
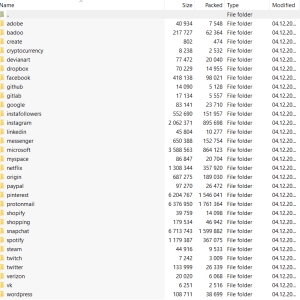
Law enforcement seized the Genesis Market cybercrime marketplace
Law enforcement seized the Genesis Market black marketplace, a platform focused on the sale of stolen credentials, as part of Operation Cookie Monster. The FBI seized the...
STYX Marketplace emerged in Dark Web focused on Financial Fraud
Resecurity has recently identified the STYX Marketplace, a new cybercriminal e-commerce platform with a specialized focus on financial fraud and money laundering. The STYX marketplace was...