Source: securityaffairs.com – Author: Pierluigi Paganini Threat actors are targeting Italian organizations with a phishing campaign aimed at delivering a new malware called WikiLoader. WikiLoader is...
Author:
Be aware of exposure of sensitive data on Wi-Fi settings for Canon inkjet printers – Source: securityaffairs.com
Source: securityaffairs.com – Author: Pierluigi Paganini Canon warns that sensitive data on the Wi-Fi connection settings stored in the memories of inkjet printers may not be...
Experts discovered a previously undocumented initial access vector used by P2PInfect worm – Source: securityaffairs.com
Source: securityaffairs.com – Author: Pierluigi Paganini Cado Security observed a new variant of the P2PInfect worm targets Redis servers with a previously undocumented initial access vector....
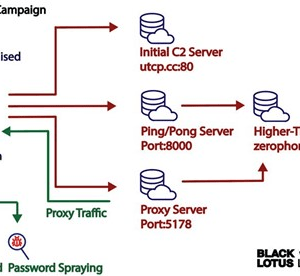
Experts link AVRecon bot to the malware proxy service SocksEscort – Source: securityaffairs.com
Source: securityaffairs.com – Author: Pierluigi Paganini The AVRecon botnet relies on compromised small office/home office (SOHO) routers since at least May 2021. In early July, researchers...
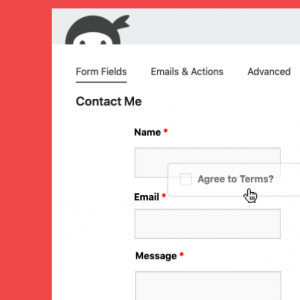
Three flaws in Ninja Forms plugin for WordPress impact 900K sites – Source: securityaffairs.com
Source: securityaffairs.com – Author: Pierluigi Paganini Experts warn of vulnerabilities impacting the Ninja Forms plugin for WordPress that could be exploited for escalating privileges and data...
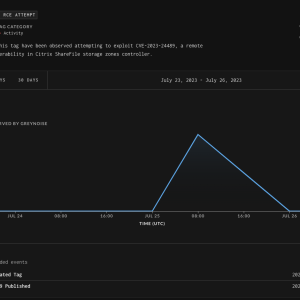
Experts warn attackers started exploiting Citrix ShareFile RCE flaw CVE-2023-24489 – Source: securityaffairs.com
Source: securityaffairs.com – Author: Pierluigi Paganini Researchers warn that threat actors started exploiting Citrix ShareFile RCE vulnerability CVE-2023-24489 in the wild. Citrix ShareFile is a widely...
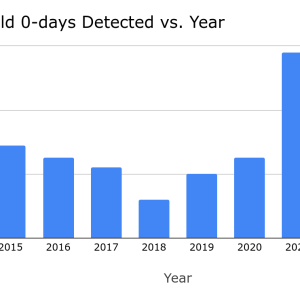
In 2022, more than 40% of zero-day exploits used in the wild were variations of previous issues – Source: securityaffairs.com
Source: securityaffairs.com – Author: Pierluigi Paganini Google’s Threat Analysis Group Google states that more than 40% of zero-day flaws discovered in 2022 were variants of previous...
New flaw in Ivanti Endpoint Manager Mobile actively exploited in the wild – Source: securityaffairs.com
Source: securityaffairs.com – Author: Pierluigi Paganini Software firm Ivanti disclosed another security vulnerability impacting Endpoint Manager Mobile (EPMM), that it said actively exploited. Ivanti disclosed a...
Security Affairs newsletter Round 430 by Pierluigi Paganini – International edition – Source: securityaffairs.com
Source: securityaffairs.com – Author: Pierluigi Paganini Privacy Overview This website uses cookies to improve your experience while you navigate through the website. Out of these cookies,...
CISA warns about SUBMARINE Backdoor employed in Barracuda ESG attacks – Source: securityaffairs.com
Source: securityaffairs.com – Author: Pierluigi Paganini The U.S. Cybersecurity and Infrastructure Security Agency (CISA) warns of threat actors deploying the SUBMARINE Backdoor in Barracuda ESG attacks....
Now Abyss Locker also targets VMware ESXi servers – Source: securityaffairs.com
Source: securityaffairs.com – Author: Pierluigi Paganini A Linux variant of the Abyss Locker designed to target VMware ESXi servers appeared in the threat landscape, experts warn....
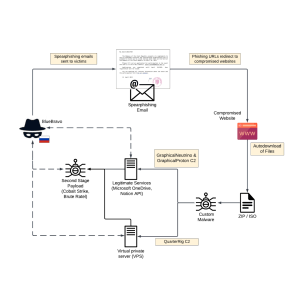
Russian APT BlueBravo targets diplomatic entities with GraphicalProton backdoor – Source: securityaffairs.com
Source: securityaffairs.com – Author: Pierluigi Paganini Russia-linked BlueBravo has been spotted targeting diplomatic entities in Eastern Europe with the GraphicalProton Backdoor. The Russia-linked threat-state actor BlueBravo...
CoinsPaid blames North Korea-linked APT Lazarus for theft of $37M worth of cryptocurrency – Source: securityaffairs.com
Source: securityaffairs.com – Author: Pierluigi Paganini Crypto-payments service provider CoinsPaid suffered a cyber attack that resulted in the theft of $37,200,000 worth of cryptocurrency. CoinsPaid, a...
Monitor Insider Threats but Build Trust First – Source: securityaffairs.com
Source: securityaffairs.com – Author: Pierluigi Paganini The issue of how to prevent insider threats without infringing on employee privacy is one that has been a hot...
GROUP-IB Co-Founder ILYA SACHKOV SENTENCED TO 14 YEARS IN A STRICT PRISON COLONY – Source: securityaffairs.com
Source: securityaffairs.com – Author: Pierluigi Paganini Ilya Sachkov, former CEO and co-founder of Group-IB was sentenced to 14 years in a high security prison colony according...
Zimbra fixed actively exploited zero-day CVE-2023-38750 in ZCS – Source: securityaffairs.com
Source: securityaffairs.com – Author: Pierluigi Paganini Zimbra addressed a zero-day vulnerability exploited in attacks aimed at Zimbra Collaboration Suite (ZCS) email servers. Two weeks ago Zimbra...
DepositFiles exposed config file, jeopardizing user security – Source: securityaffairs.com
Source: securityaffairs.com – Author: Pierluigi Paganini DepositFiles, a popular web hosting service, left its environment configuration file accessible, revealing a trove of highly sensitive credentials. The...
Group-IB CEO Ilya Sachkov sentenced to 14 years in a strict prison colony – Source: securityaffairs.com
Source: securityaffairs.com – Author: Pierluigi Paganini Ilya Sachkov, CEO and co-founder of Group-IB was sentenced to 14 years in a high security prison colony according to...
Two flaws in Linux Ubuntu affect 40% of Ubuntu users – Source: securityaffairs.com
Source: securityaffairs.com – Author: Pierluigi Paganini Wiz researchers discovered two Linux vulnerabilities in the Ubuntu kernel that can allow an unprivileged local user to gain elevated...
Two ambulance services in UK lost access to patient records after a cyber attack on software provider – Source: securityaffairs.com
Source: securityaffairs.com – Author: Pierluigi Paganini Swedish software firm Ortivus suffered a cyberattack that has resulted in at least two British ambulance services losing access to...
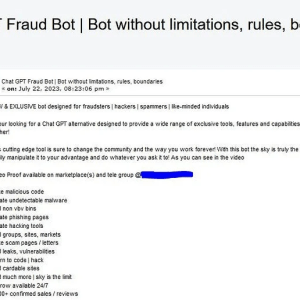
FraudGPT, a new malicious generative AI tool appears in the threat landscape – Source: securityaffairs.com
Source: securityaffairs.com – Author: Pierluigi Paganini FraudGPT is another cybercrime generative artificial intelligence (AI) tool that is advertised in the hacking underground. Generative AI models are...
CISA adds Ivanti EPMM flaw to its Known Exploited Vulnerabilities catalog – Source: securityaffairs.com
Source: securityaffairs.com – Author: Pierluigi Paganini US CISA added actively exploited Ivanti ‘s Endpoint Manager Mobile (EPMM) vulnerability to its Known Exploited Vulnerabilities catalog. US Cybersecurity...
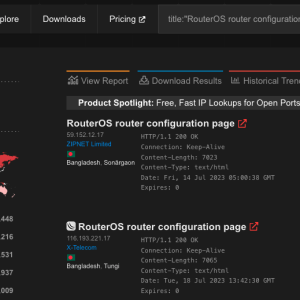
Over 500K MikroTik RouterOS systems potentially exposed to hacking due to critical flaw – Source: securityaffairs.com
Source: securityaffairs.com – Author: Pierluigi Paganini Experts warn of a severe privilege escalation, tracked as CVE-2023-30799, in MikroTik RouterOS that can be exploited to hack vulnerable devices....
Atlassian addressed 3 flaws in Confluence and Bamboo products – Source: securityaffairs.com
Source: securityaffairs.com – Author: Pierluigi Paganini Atlassian addressed three vulnerabilities in its Confluence Server, Data Center, and Bamboo Data Center products that can lead to remote code...
VMware addressed an information disclosure flaw in VMware Tanzu Application Service for VMs and Isolation Segment – Source: securityaffairs.com
Source: securityaffairs.com – Author: Pierluigi Paganini VMware fixed an information disclosure flaw in VMware Tanzu Application Service for VMs and Isolation Segment that exposed CF API...
Apple addressed a new actively exploited zero-day tracked as CVE-2023-38606 – Source: securityaffairs.com
Source: securityaffairs.com – Author: Pierluigi Paganini Apple released security updates to address an actively exploited zero-day flaw in iOS, iPadOS, macOS, tvOS, watchOS, and Safari. Apple released...
Twelve Norwegian ministries were hacked using a zero-day vulnerability – Source: securityaffairs.com
Source: securityaffairs.com – Author: Pierluigi Paganini Threat actors exploited a zero-day flaw in third-party software in attacks against the ICT platform used by 12 Norwegian ministries....
A flaw in OpenSSH forwarded ssh-agent allows remote code execution – Source: securityaffairs.com
Source: securityaffairs.com – Author: Pierluigi Paganini A new flaw in OpenSSH could be potentially exploited to run arbitrary commands remotely on compromised hosts under specific conditions....
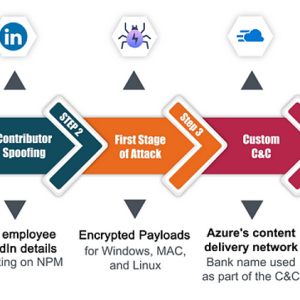
Experts warn of OSS supply chain attacks against the banking sector – Source: securityaffairs.com
Source: securityaffairs.com – Author: Pierluigi Paganini Checkmark researchers have uncovered the first known targeted OSS supply chain attacks against the banking sector. In the first half of...
Apple could opt to stop iMessage and FaceTime services due to the government’s surveillance demands – Source: securityaffairs.com
Source: securityaffairs.com – Author: Pierluigi Paganini Apple could opt to pull iMessage and FaceTime services in the U.K. in response to the government’s surveillance demands. In...