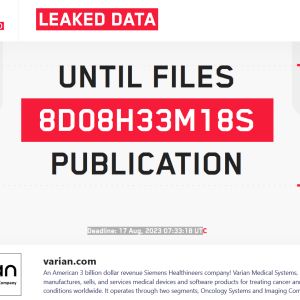
Source: securityaffairs.com – Author: Pierluigi Paganini The LockBit ransomware group threatens to leak medical data of cancer patients stolen from Varian Medical Systems. The LockBit ransomware...
Author:
Microsoft Patch Tuesday for August 2023 fixed 2 actively exploited flaws – Source: securityaffairs.com
Source: securityaffairs.com – Author: Pierluigi Paganini Microsoft Patch Tuesday security updates for August 2023 addressed 74 vulnerabilities, including two actively exploited flaws. Microsoft Patch Tuesday security...
UK Electoral Commission discloses a data breach – Source: securityaffairs.com
Source: securityaffairs.com – Author: Pierluigi Paganini The UK Electoral Commission suffered a data breach that exposed voters’ personal information between 2014 and 2022. The UK Electoral...
43 Android apps in Google Play with 2.5M installs loaded ads when a phone screen was off – Source: securityaffairs.com
Source: securityaffairs.com – Author: Pierluigi Paganini Experts found 43 Android apps in Google Play with 2.5 million installs that displayed advertisements while a phone’s screen was...
Zoom trains its AI model with some user data, without giving them an opt-out option – Source: securityaffairs.com
Source: securityaffairs.com – Author: Pierluigi Paganini Zoom changed its terms of service requiring users to allow AI to train on all their data without giving them...
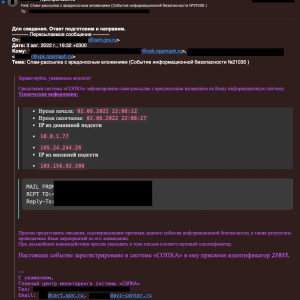
North Korea compromised Russian missile engineering firm NPO Mashinostroyeniya – Source: securityaffairs.com
Source: securityaffairs.com – Author: Pierluigi Paganini Two North Korea-linked APT groups compromised the infrastructure of the major Russian missile engineering firm NPO Mashinostroyeniya. Cybersecurity firm SentinelOne...
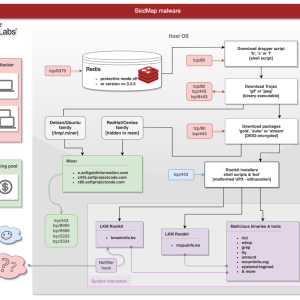
A new sophisticated SkidMap variant targets unsecured Redis servers – Source: securityaffairs.com
Source: securityaffairs.com – Author: Pierluigi Paganini A new campaign targets Redis servers, this time the malware employed in the attacks is a new variant of the...
FBI warns of crooks posing as NFT developers in fraudulent schema – Source: securityaffairs.com
Source: securityaffairs.com – Author: Pierluigi Paganini The FBI is warning about cyber criminals masquerading as NFT developers to steal cryptocurrency and other digital assets. The U.S....
The number of ransomware attacks targeting Finland increased fourfold since it started the process to join NATO – Source: securityaffairs.com
Source: securityaffairs.com – Author: Pierluigi Paganini Senior official reports a quadruple increase in ransomware attacks against Finland since it started the process to join NATO. The...
Microsoft fixed a flaw in Power Platform after being criticized – Source: securityaffairs.com
Source: securityaffairs.com – Author: Pierluigi Paganini Microsoft announced it has addressed a critical flaw in its Power Platform after it was criticized for the delay in fixing...
Colorado Department of Higher Education (CDHE) discloses data breach after ransomware attack – Source: securityaffairs.com
Source: securityaffairs.com – Author: Pierluigi Paganini The Colorado Department of Higher Education (CDHE) finally disclosed a data breach impacting students, past students, and teachers after the...
Security Affairs newsletter Round 431 by Pierluigi Paganini – International edition – Source: securityaffairs.com
Source: securityaffairs.com – Author: Pierluigi Paganini Privacy Overview This website uses cookies to improve your experience while you navigate through the website. Out of these cookies,...
BlueCharlie changes attack infrastructure in response to reports on its activity – Source: securityaffairs.com
Source: securityaffairs.com – Author: Pierluigi Paganini Russia-linked APT group BlueCharlie was observed changing its infrastructure in response to recent reports on its activity. Researchers from Recorded...
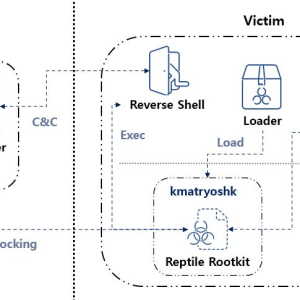
Reptile Rootkit employed in attacks against Linux systems in South Korea – Source: securityaffairs.com
Source: securityaffairs.com – Author: Pierluigi Paganini Researchers observed threat actors that are using an open-source rootkit called Reptile in attacks aimed at systems in South Korea. Reptile is...
New PaperCut flaw in print management software exposes servers to RCE attacks – Source: securityaffairs.com
Source: securityaffairs.com – Author: Pierluigi Paganini Researchers discovered a vulnerability in PaperCut NG/MF print management software that can lead to remote code execution. Cybersecurity researchers at...
A cyberattack impacted operations of multiple hospitals in several US states – Source: securityaffairs.com
Source: securityaffairs.com – Author: Pierluigi Paganini A cyberattack has disrupted the computer systems of multiple hospitals in several states, with a severe impact on their operations....
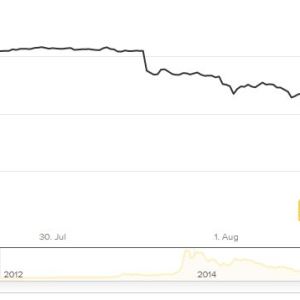
Married couple pleaded guilty to laundering billions in cryptocurrency stolen from Bitfinex in 2016 – Source: securityaffairs.com
Source: securityaffairs.com – Author: Pierluigi Paganini A married couple from New York pleaded guilty this week to laundering billions of dollars stolen from Bitfinex in 2016....
Malicious packages in the NPM designed for highly-targeted attacks – Source: securityaffairs.com
Source: securityaffairs.com – Author: Pierluigi Paganini Researchers discovered a new set of malicious packages on the npm package manager that can exfiltrate sensitive developer data. On...
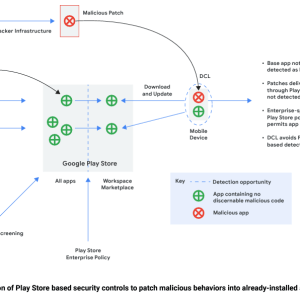
Attackers use dynamic code loading to bypass Google Play store’s malware detections – Source: securityaffairs.com
Source: securityaffairs.com – Author: Pierluigi Paganini Threat actors rely on the ‘versioning’ technique to evade malware detections of malicious code uploaded to the Google Play Store....
CISA, FBI, and NSA published the list of 12 most exploited vulnerabilities of 2022 – Source: securityaffairs.com
Source: securityaffairs.com – Author: Pierluigi Paganini CISA, the FBI, and NSA, along with Five Eyes cybersecurity agencies published a list of the 12 most exploited vulnerabilities...
Decommissioned medical infusion pumps sold on secondary market could reveal Wi-Fi configuration settings – Source: securityaffairs.com
Source: securityaffairs.com – Author: Pierluigi Paganini Experts warn that decommissioned medical infusion pumps sold via the secondary market could expose Wi-Fi configuration settings. The sale of...
OWASP Top 10 for LLM (Large Language Model) applications is out! – Source: securityaffairs.com
Source: securityaffairs.com – Author: Pierluigi Paganini The OWASP Top 10 for LLM (Large Language Model) Applications version 1.0 is out, it focuses on the potential security risks...
Rapid7 found a bypass for the recently patched actively exploited Ivanti EPMM bug – Source: securityaffairs.com
Source: securityaffairs.com – Author: Pierluigi Paganini Researchers discovered a bypass for a recently fixed actively exploited vulnerability in Ivanti Endpoint Manager Mobile (EPMM). Rapid7 cybersecurity researchers...
Russian APT29 conducts phishing attacks through Microsoft Teams – Source: securityaffairs.com
Source: securityaffairs.com – Author: Pierluigi Paganini Russia-linked APT29 group targeted dozens of organizations and government agencies worldwide with Microsoft Teams phishing attacks. Microsoft Threat Intelligence reported...
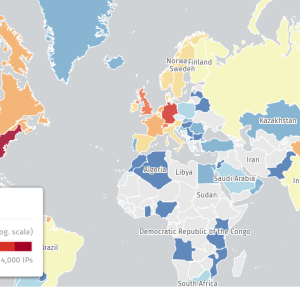
Hackers already installed web shells on 581 Citrix servers in CVE-2023-3519 attacks – Source: securityaffairs.com
Source: securityaffairs.com – Author: Pierluigi Paganini Researchers warn that hundreds of Citrix servers have been hacked in an ongoing campaign exploiting the RCE CVE-2023-3519. Security researchers...
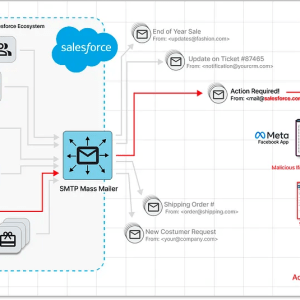
Zero-day in Salesforce email services exploited in targeted Facebook phishing campaign – Source: securityaffairs.com
Source: securityaffairs.com – Author: Pierluigi Paganini Experts spotted a spear-phishing Facebook campaign exploiting a zero-day vulnerability in Salesforce email services. Researchers from Guardio Labs uncovered a...
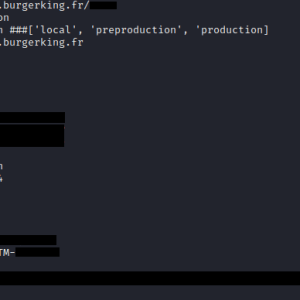
Burger King forgets to put a password on their systems, again – Source: securityaffairs.com
Source: securityaffairs.com – Author: Pierluigi Paganini The fast food giant Burger King put their systems and data at risk by exposing sensitive credentials to the public...
CISA adds second Ivanti EPMM flaw to its Known Exploited Vulnerabilities catalog – Source: securityaffairs.com
Source: securityaffairs.com – Author: Pierluigi Paganini US CISA added a second actively exploited Ivanti ‘s Endpoint Manager Mobile (EPMM) vulnerability to its Known Exploited Vulnerabilities catalog....
NodeStealer 2.0 takes over Facebook Business accounts and targets crypto wallets – Source: securityaffairs.com
Source: securityaffairs.com – Author: Pierluigi Paganini Researchers spotted a Python variant of the NodeStealer that was designed to take over Facebook business accounts and cryptocurrency wallets. Palo Alto...
US govt is hunting a Chinese malware that can interfere with its military operations – Source: securityaffairs.com
Source: securityaffairs.com – Author: Pierluigi Paganini The US government believes that China has deployed malware in key US power and communications networks that can be activated...