Source: www.securityweek.com – Author: Kevin Townsend Researchers at cloud security firm Wiz have discovered two easily exploitable privilege escalation vulnerabilities in Ubuntu’s OverlayFS module affecting 40%...
Author:
TETRA Radio Standard Vulnerabilities Can Expose Military Comms, Industrial Systems – Source: www.securityweek.com
Source: www.securityweek.com – Author: Kevin Townsend Five vulnerabilities, two deemed to be critical, have been found in the Terrestrial Trunked Radio (TETRA) standard. TETRA is the...
Nubeva’s Ransomware Key Interception and Decryption Technology Validated in Third-Party Lab – Source: www.securityweek.com
Source: www.securityweek.com – Author: Kevin Townsend NuRR is a product that claims to intercept and capture the encryption keys at the start of a ransomware’s encryption...
Human Cyber-Risk Can Be Demonstrably Mitigated by Behavior Changing Training: Analysis – Source: www.securityweek.com
Source: www.securityweek.com – Author: Kevin Townsend The process of encouraging secure cyber habits in end users is evolving from traditional awareness training toward changing end user...
Security Awareness Training Isn’t Working – How Can We Improve It? – Source: www.securityweek.com
Source: www.securityweek.com – Author: Kevin Townsend Security awareness training isn’t working to the level it needs to. It doesn’t protect all industries and all people all...
Hacker Conversations: Inside the Mind of Daniel Kelley, ex-Blackhat – Source: www.securityweek.com
Source: www.securityweek.com – Author: Kevin Townsend Daniel Kelley is the first ex-Blackhat in SecurityWeek’s series: Hacker Conversations. He spoke openly on his journey into and out...
Inside the Mind of the Hacker: Report Shows Speed and Efficiency of Hackers in Adopting New Technologies – Source: www.securityweek.com
Source: www.securityweek.com – Author: Kevin Townsend The application of artificial intelligence is still in its infancy, but we are already seeing one major effect: the democratization...
CISO Conversations: CISOs of Identity Giants IDEMIA and Ping – Source: www.securityweek.com
Source: www.securityweek.com – Author: Kevin Townsend SecurityWeek talks to Dennis Kallelis (CSO at Idemia) and Jason Kees (CISO at Ping), two of industry’s identity giants. The...
A Cybersecurity Wish List Ahead of NATO Summit – Source: www.securityweek.com
Source: www.securityweek.com – Author: Kevin Townsend As tomorrow’s NATO Summit in Vilnius, Lithuania approaches, SecurityWeek questions what NATO should do about cybersecurity. The Russia/Ukraine conflict offers...
OWASP SwSec 5D Tool Provides SDLC Maturity Ratings, Aids Software Supply Chain – Source: www.securityweek.com
Source: www.securityweek.com – Author: Kevin Townsend The Open Source Foundation for Application Security (OWASP) announced a five-dimensional secure software development maturity reference framework (SwSec 5D) in...
Apple, Civil Liberty Groups Condemn UK Online Safety Bill – Source: www.securityweek.com
Source: www.securityweek.com – Author: Kevin Townsend The latest variant of the crypto wars is happening now, with the UK and EU governments attempting to force backdoors...
Rapid7: Japan Threat Landscape Takes on Global Significance – Source: www.securityweek.com
Source: www.securityweek.com – Author: Kevin Townsend Japan is the world’s third largest economy. It attracts both criminal and nation-state cyberattacks. The effects of these attacks can...
DOE CIO Talks to SecurityWeek About Cybersecurity, Digital Transformation – Source: www.securityweek.com
Source: www.securityweek.com – Author: Kevin Townsend Ann Dunkin is CIO at the US Department of Energy (DOE). Among her responsibilities, she heads IT and oversees cybersecurity....
What is Cyberwar? – Source: www.securityweek.com
Source: www.securityweek.com – Author: Kevin Townsend Ask any three people to define cyberwar and you will get three different answers. But as global geopolitics worsen and...
Bipartisan Bill Proposes Cybersecurity Funds for Rural Water Systems – Source: www.securityweek.com
Source: www.securityweek.com – Author: Kevin Townsend A new bill proposes to increase cybersecurity funding for rural water systems by $7.5 million dollars per year. It’s not...
CISOs’ New Stressors Brought on by Digitalization: Report – Source: www.securityweek.com
Source: www.securityweek.com – Author: Kevin Townsend Whether cloud migration is a cause or effect of digitalization, it is nevertheless a major part of the journey currently...
CISO Conversations: Three Leading CISOs From the Payment Industry – Source: www.securityweek.com
Source: www.securityweek.com – Author: Kevin Townsend SecurityWeek talks to leading Chief Information Security Officers in the payments industry about their role and experience as CISOs. In...
Chrome and Its Vulnerabilities – Is the Web Browser Safe to Use? – Source: www.securityweek.com
Source: www.securityweek.com – Author: Kevin Townsend Like all major applications, Google’s Chrome suffers from vulnerabilities. During 2022, SecurityWeek reported on 456 vulnerabilities (averaging 38 per month),...
Fulfilling Expected SEC Requirements for Cybersecurity Expertise at Board Level – Source: www.securityweek.com
Source: www.securityweek.com – Author: Kevin Townsend The U.S. Securities and Exchange Commission (SEC) is expected to introduce a rule requiring demonstration of cybersecurity expertise at the...
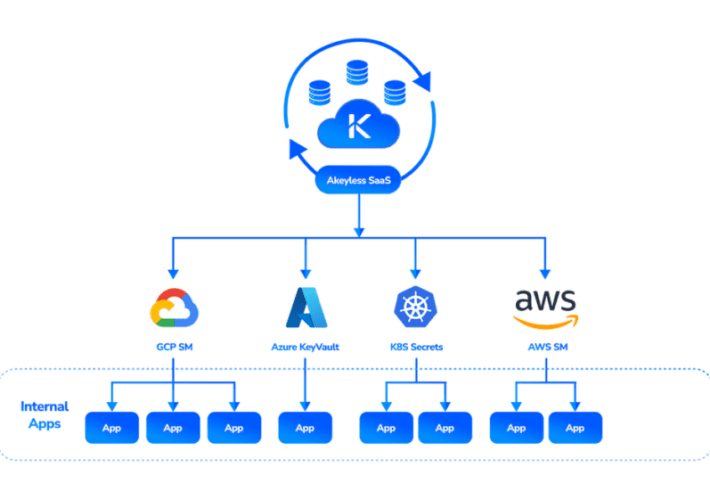
Akeyless Launches SaaS-based External Secrets Manager – Source: www.securityweek.com
Source: www.securityweek.com – Author: Kevin Townsend Secrets are fundamental to cybersecurity. They comprise the secret data that allows individual authorization and access to or between systems....
OT Security Firm Shift5 Adds $33 Million in Funding – Source: www.securityweek.com
Source: www.securityweek.com – Author: Kevin Townsend Arlington, VA-based OT security firm Shift5 has raised an additional $33 million in its Series B financing. $50 million was...
Google Introduces SAIF, a Framework for Secure AI Development and Use – Source: www.securityweek.com
Source: www.securityweek.com – Author: Kevin Townsend The Google SAIF (Secure AI Framework) is designed to provide a security framework or ecosystem for the development, use and...
SaaS Ransomware Attack Hit Sharepoint Online Without Using a Compromised Endpoint – Source: www.securityweek.com
Source: www.securityweek.com – Author: Kevin Townsend Cybersecurity firm Obsidian has observed a successful ransomware attack against Sharepoint Online (Microsoft 365) via a Microsoft Global SaaS admin...
OWASP’s 2023 API Security Top 10 Refines View of API Risks – Source: www.securityweek.com
Source: www.securityweek.com – Author: Kevin Townsend OWASP’s ranking for the major API security risks in 2023 has been published. The list includes many parallels with the...
Zoom Expands Privacy Options for European Customers – Source: www.securityweek.com
Source: www.securityweek.com – Author: Kevin Townsend Zoom has announced a slew of data privacy features, developed in collaboration with the Dutch education and research organization SURF,...
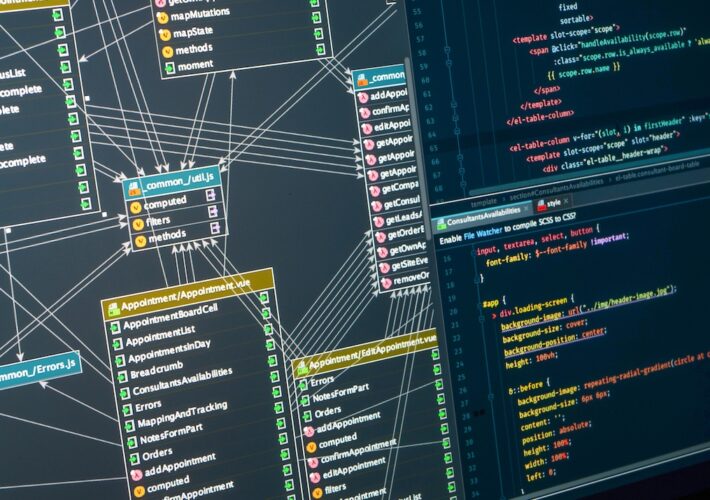
SBOMs – Software Supply Chain Security’s Future or Fantasy? – Source: www.securityweek.com
Source: www.securityweek.com – Author: Kevin Townsend Two years after the requirement for Software Bills of Materials (SBOMs) were announced, we are nowhere near achieving them. Are...
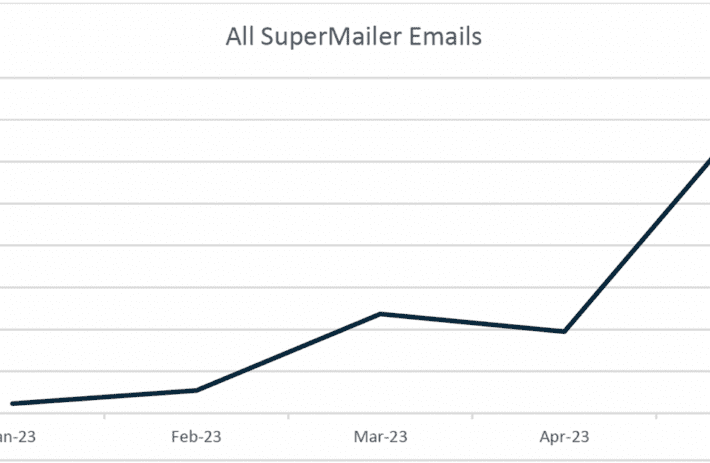
Threat Actor Abuses SuperMailer for Large-scale Phishing Campaign – Source: www.securityweek.com
Source: www.securityweek.com – Author: Kevin Townsend A credential phishing campaign using the legitimate SuperMailer newsletter distribution app has doubled in size each month since January 2023....
Quantum Decryption Brought Closer by Topological Qubits – Source: www.securityweek.com
Source: www.securityweek.com – Author: Kevin Townsend Quantinuum has demonstrated the controlled creation and manipulation of non-Abelian anyons – or, put more simply, brought the arrival of...
IBM Delivers Roadmap for Transition to Quantum-safe Cryptography – Source: www.securityweek.com
Source: www.securityweek.com – Author: Kevin Townsend IBM has introduced a quantum-safe roadmap to help the complex organizational transition to post-quantum cryptography at this year’s annual Think...
CISO Conversations: HP and Dell CISOs Discuss the Role of the Multi-National Security Chief – Source: www.securityweek.com
Source: www.securityweek.com – Author: Kevin Townsend HP and Dell Technologies are two of the world’s largest international computer manufacturers. Their CISOs, Joanna Burkey (HP) and Kevin...