The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
Author: Constanza Rodriguez
Ultimate SplunkforCybersecurity
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
Splunk – SIEM Log Monitoring
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
Spam and Phishing Report for 2023
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
SOC Audit Report Type1 Type2
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
Secure Cloud Business Applications
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
Security Basics for ProtectingCritical Infrastructure fromCyber Threats
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
TIPS TOAVOID ROMANCE SCAMS
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
Securityto go: A Risk Management Toolkit for Humanitarianaid Agencies
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
R I S K A P P E T I T E –C R I T I C A L TOSUCCESS U S I N G R I S K A P P E T I T E T O T H R I V E I N A C H A N G I N G W O R L D
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
Reporting Cybersecurity Risk to the Board of Directors
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
Reporting Cyber Risk to Boards
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
Red Team Operations Concepts
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
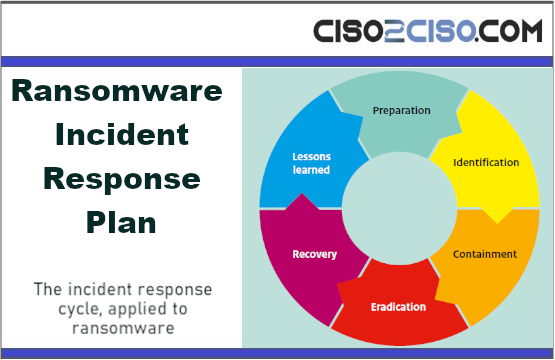
Ransomware Incident Response Plan The incident response cycle, applied to ransomware
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
Gestión deincidentes de ransomware INFORME DE BUENAS PRÁCTICAS
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
Public Sector Cyber Security Baseline Standards
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
Privacy By Design:From Principles toRequirements
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
DemystifyingPublic KeyInfrastructure (PKI)& CertificateLifecycle Management
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
Red Report 2024 The Top 10 Most Prevalent MITRE ATT&CK® Techniques
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
Windows Malware Investigations
“We were targeted by a sophisticated, advanced persistent threat.” The document provides a comprehensive overview of malware analysis, with a specific focus on the Qbot malware,...
Windows Hacking
A long time ago there existed a time and space where the 6502 processor was everywhere. There was no internet, there was no cell phone and...
The Threat Intelligence Handbook Second Edition
Moving Toward a Security Intelligence Program Today, cyber threats are coming from everywhere — the open web and dark web, but also partners and other third...
State of the UAE Cybersecurity Landscape
In the dynamic cyber landscape of the United Arab Emirates (UAE), a startling statistic serves as a clarion call to action: the Nation currently hosts at...
Protective Security Guide for CSOs
The role of the Chief Security Officer (CSO) is the key to ensuring the secure delivery of Government business. As a CSO, you are tasked with...
Global Threat Intelligence Report March 2024 by Blackberry Cybersecurity
As we enter 2024, we mark a full calendar year of quarterly BlackBerry® Global Threat Intelligence Reports. And what a year it has been. Over the...
Implement Network Segmentation Encryption Cloud Envir by NSA
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
Active Directory Security Guide
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
Global Threat Intelligence Report March 2024 by Blackberry Cybersecurity
As we enter 2024, we mark a full calendar year of quarterly BlackBerry® Global Threat Intelligence Reports. And what a year it has been. Over the...
Active Directory Security Guide – The Complete Active Directory Security Handbook
Active Directory (AD), introduced with Windows 2000, has become an integral part of modern organizations, serving as the backbone of identity infrastructure for 90% of Fortune...