The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
Author: admin
Undestanding Networks Hacks – Attack and Defense with Python 2nd Edition by Bastian Ballman – Springer
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
MITRE ATT&CK in Google Cloud Platform (GCP) – A defender’s cheat sheet by expel
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
TOP 250 MSSPs Services Providers 2022 edition by MSSP Alert – A CyberRisk Alliance Resource .
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
Zero Trust Matutity Model by CISA
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
Beat Cybercriminals at Their Own Game – A Guide to Winning the Vulnerability Race and Protecting Your Organization by TrendMicro
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
The Financial Impact of Malware
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
DevSecOps Fundamentals Guidebook – Tools & Activities by American Deparment of Defense
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
Blockchain Security and AML Analysis Report 2022 Mid-Year by SLOWMIST
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
Enhancing Cyber Resilience in Electricy Systems by International Energy Agency
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
The Metaverse – Concepts and Issues for Congress by Congressional Research Service
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
Value creation in the metaverse – The Real business of the virtual world by McKinsey & Company – June 2022
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
Introduction to Doxing- OSINT methods for information gathering by HADESS
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
2022 ThreatLabz Research Team – State of Ransomware Report by Zscaler
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
Global Incident Response Threat Report 2022 by vmware
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
Threat Hunting Playbook – Learn how to embrace a proactive security posture by Rank.
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
The Cyber Intelligence Analyst’s Cookbook by The OPEN RESEARCH SOCIETY
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
A checklist for efective Threath Hunting by SecurityHQ
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
Blockchain Security – A Framework for Trust and Adoption by Dutch Blockchain Coalition
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
Building an Effective Cyber Security Strategy in four parts approach by Silent Breach
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
The Cyber Risk Playbook – What boards of directors and executives should know about Cyber Risk by FireEye.
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
Threat Hunting Playbooks for MITRE Tactics – Starting your first threat hunting today by PRASANNAKUMAR B MUNDAS
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
Security Operations Center Guidebook – A Practical Guide for a Successful SOC
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
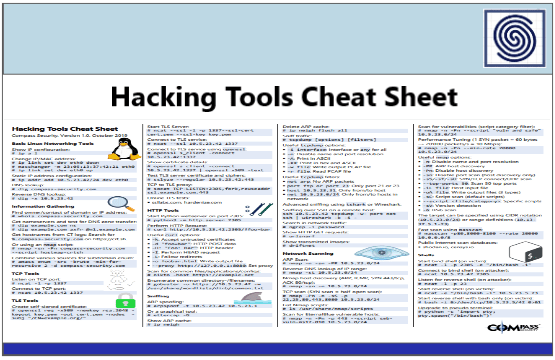
Hacking Tools Cheat Sheet by Compass Security
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
ENISA THREAT LANDSCAPE FOR RANSOMWARE ATTACK REPORT JULY 2022
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
A SANS 2021 survey – Security operations center
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
State of Kubernetes Security Report 2022 by RedHat
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
Effective Purple Teaming by PlexTrac
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
Advancing Supply Chain Security in Oil and Gas an Industry Analysis by World Economic Forum
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
TELECOM SECURITY INCIDENTS REPORT 2021 BY ENISA
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...