Security Affairs newsletter Round 380A new round of the weekly SecurityAffairs newsletter arrived! Every week the best security articles from Security Affairs free for you in...
Author: admin
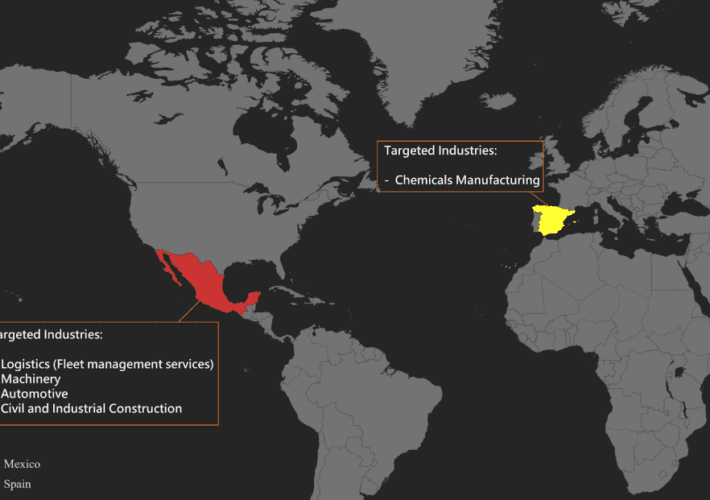
Grandoreiro banking malware targets Mexico and Spain
Grandoreiro banking malware targets Mexico and SpainA new Grandoreiro banking malware campaign is targeting organizations in Mexico and Spain, Zscaler reported. Zscaler ThreatLabz researchers observed a...
Threat actors are stealing funds from General Bytes Bitcoin ATM
Threat actors are stealing funds from General Bytes Bitcoin ATMThreat actors have exploited a zero-day vulnerability in the General Bytes Bitcoin ATM servers to steal BTC...
Fake DDoS protection pages on compromised WordPress sites lead to malware infections
Fake DDoS protection pages on compromised WordPress sites lead to malware infectionsThreat actors compromise WordPress sites to display fake Cloudflare DDoS protection pages to distribute malware. DDoS...
Donot Team cyberespionage group updates its Windows malware framework
Donot Team cyberespionage group updates its Windows malware frameworkThe Donot Team threat actor, aka APT-C-35, has added new capabilities to its Jaca Windows malware framework. The Donot Team has been...
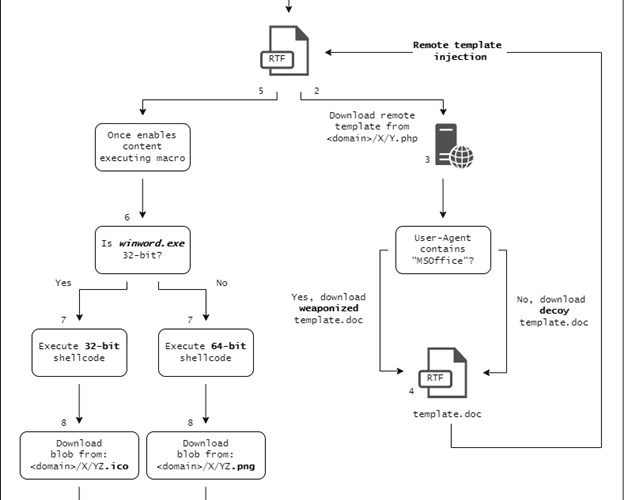
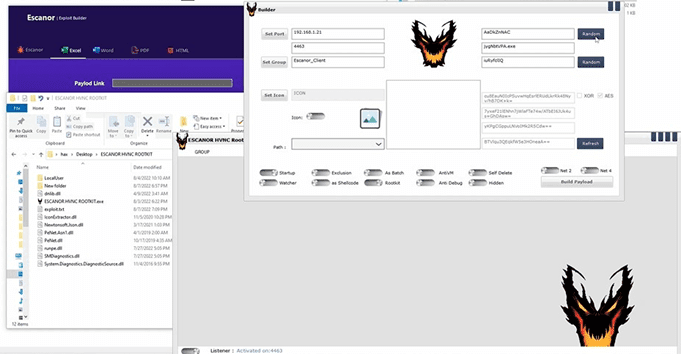
Escanor Malware delivered in Weaponized Microsoft Office Documents
Escanor Malware delivered in Weaponized Microsoft Office DocumentsResearchers spotted a new RAT (Remote Administration Tool) advertised in Dark Web and Telegram called Escanor Resecurity, a Los...
Zero-day Vulnerability Abused by Cybercriminals to Steal Crypto from Bitcoin ATMs
Zero-day Vulnerability Abused by Cybercriminals to Steal Crypto from Bitcoin ATMsMalicious actors have taken advantage of a zero-day flaw in General Bytes Bitcoin ATM servers to...
3 Ways Asset Management Companies Can Reduce Cyber Risk
3 Ways Asset Management Companies Can Reduce Cyber RiskFund managers should not get caught out thinking they are a low-priority target: here’s how to identify risks...
A Modern Cybersecurity Fight Requires a Modern Approach to Regulatory Oversight
A Modern Cybersecurity Fight Requires a Modern Approach to Regulatory OversightBy Charlie Moskowitz, Vice President, Policy and Public Sector at SecurityScorecard Cybercriminals never stop. Often they...
The main challenges facing CISOs
The main challenges facing CISOsHow CISOs can help their organizations avoid cyber risks by choosing the right tools and ensuring they have compiled a rigorous risk...
Iron Tiger Compromises Chat Application Mimi, Targets Windows, Mac, and Linux Users
Iron Tiger Compromises Chat Application Mimi, Targets Windows, Mac, and Linux UsersWe found APT group Iron Tiger's malware compromising chat application Mimi’s servers in a supply...
Oil and Gas Cybersecurity: Recommendations Part 3
Oil and Gas Cybersecurity: Recommendations Part 3In the final part of our series, we look at the APT33 case study and several recommendations from our expert...
What Exposed OPA Servers Can Tell You About Your Applications
What Exposed OPA Servers Can Tell You About Your ApplicationsThis blog entry discusses what an OPA is and what it’s for, what we’ve discovered after identifying...
Protecting S3 from Malware: The Cold Hard Truth
Protecting S3 from Malware: The Cold Hard TruthCloud object storage is a core component of any modern application, but most cloud file storage security is insufficient.Leer...
Analyzing the Hidden Danger of Environment Variables for Keeping Secrets
Analyzing the Hidden Danger of Environment Variables for Keeping SecretsWhile DevOps practitioners use environment variables to regularly keep secrets in applications, these could be conveniently abused...
Our Quest: Advancing Product Labels to Help Consumers Consider Cybersecurity
Our Quest: Advancing Product Labels to Help Consumers Consider CybersecurityFor many decades, consumers have relied on labels to help them make decisions about which products to...
Are ethical hackers the digital security answer?
Are ethical hackers the digital security answer?TechRepublic speaks to HackerOne about how ethical hackers are helping to shrink the broader attack surface of cyber criminals. The...
Kolide is an endpoint security solution for teams that want to meet their compliance goals without sacrificing privacy.
Kolide is an endpoint security solution for teams that want to meet their compliance goals without sacrificing privacy.If you’re considering a third-party audit like SOC 2...
How to deploy the Bitwarden self-hosted server with Docker
How to deploy the Bitwarden self-hosted server with DockerJack Wallen walks you through the process of deploying a Bitwarden vault server with the help of Docker...
Seaborgium targets sensitive industries in several countries
Seaborgium targets sensitive industries in several countriesThe cyberespionage threat actor is aligned with Russian interests and has hit numerous organizations since 2017, aiming at stealing sensitive...
Browser extension threat targets millions of users
Browser extension threat targets millions of usersBrowser extensions are amazing tools but sometimes not what they pretend to be. Some are in fact malicious and might...
How phishing attacks are exploiting Amazon Web Services
How phishing attacks are exploiting Amazon Web ServicesBy using a legitimate service like AWS to create phishing pages, attackers can bypass traditional security scanners, says Avanan....
Apple users urged to install latest updates to combat hacking
Apple users urged to install latest updates to combat hackingThe new updates patch security flaws in iOS/iPadOS, macOS and Safari that could be exploited by hackers...
LockBit claims ransomware attack on security giant Entrust, leaks data
LockBit claims ransomware attack on security giant Entrust, leaks dataThe LockBit ransomware gang has claimed responsibility for the June cyberattack on digital security giant Entrust. [...]Leer...
Russian APT29 hackers abuse Azure services to hack Microsoft 365 users
Russian APT29 hackers abuse Azure services to hack Microsoft 365 usersThe state-backed Russian cyberespionage group Cozy Bear has been particularly prolific in 2022, targeting Microsoft 365...
Alternatives to facial recognition authentication
Alternatives to facial recognition authenticationLearn the problem with facial recognition as well as software and hardware alternatives to the technology. The post Alternatives to facial recognition...
How to unlock 1Password on a Mac
How to unlock 1Password on a MacGet access to your passwords in a snap with 1Password on your macOS device. The post How to unlock 1Password...
CISA adds 7 vulnerabilities to list of bugs exploited by hackers
CISA adds 7 vulnerabilities to list of bugs exploited by hackersThe U.S. Cybersecurity and Infrastructure Security Agency (CISA) has added seven vulnerabilities to its list of...
New tool checks if a mobile app’s browser is a privacy risk
New tool checks if a mobile app's browser is a privacy riskA new online tool named 'InAppBrowser' lets you analyze the behavior of in-app browsers embedded within...
How to strengthen the human element of cybersecurity
How to strengthen the human element of cybersecuritySecurity expert explains how IT leaders can work with employees to ensure security strategies and techniques are actually implemented....