Summertime Blues: TA558 Ramps Up Attacks on Hospitality, Travel SectorsContenido de la entradaLeer másProofpoint News Feed
Author: admin
Cloud attacks on the supply chain are a huge concern
Cloud attacks on the supply chain are a huge concernContenido de la entradaLeer másProofpoint News Feed
Cybercrime Group TA558 Ramps Up Email Attacks Against Hotels
Cybercrime Group TA558 Ramps Up Email Attacks Against HotelsContenido de la entradaLeer másProofpoint News Feed
Play Ransomware’s Attack Playbook Similar to that of Hive, Nokoyawa
Play Ransomware's Attack Playbook Similar to that of Hive, NokoyawaPlay is a new ransomware that takes a page out of Hive and Nokoyawa's playbook. The many...
Enhancing Cloud Security by Reducing Container Images Through Distroless Techniques
Enhancing Cloud Security by Reducing Container Images Through Distroless TechniquesWe analyzed the Distroless technique for reducing the size of container images and explored its capabilities to...
Cloud security: Increased concern about risks from partners, suppliers
Cloud security: Increased concern about risks from partners, suppliersContenido de la entradaLeer másProofpoint News Feed
Benefits of edge computing
Benefits of edge computingLearn more about how edge computing can reduce latency, boost performance and improve data security among other benefits. The post Benefits of edge...
Credential phishing prevention best practices
Credential phishing prevention best practicesCredential phishing prevention best practices can help your employees prevent cyber attacks that can harm your business. Information security is everyone’s job....
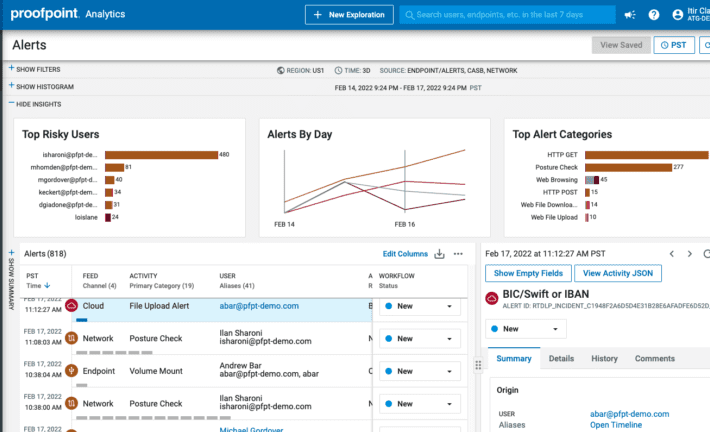
Best Data Security Solution | Proofpoint Information Protection
Best Data Security Solution | Proofpoint Information ProtectionContenido de la entradaLeer másProofpoint News Feed
200,000 North Face accounts hacked in credential stuffing attack
200,000 North Face accounts hacked in credential stuffing attackOutdoor apparel brand 'The North Face' was targeted in a large-scale credential stuffing attack that has resulted in...
Proofpoint Introduces a Smarter Way to Stay Compliant with New Intelligent Compliance Platform
Proofpoint Introduces a Smarter Way to Stay Compliant with New Intelligent Compliance PlatformContenido de la entradaLeer másProofpoint News Feed
Chinese hackers tied to attacks on South China Sea energy firms
Chinese hackers tied to attacks on South China Sea energy firmsContenido de la entradaLeer másProofpoint News Feed
Ukraine dismantles more bot farms spreading Russian disinformation
Ukraine dismantles more bot farms spreading Russian disinformationThe Cyber Department of the Ukrainian Security Service (SSU) dismantled two more bot farms that spread Russian disinformation on...
Three Sentenced in the UK for Selling Drugs on the Darkweb
Three Sentenced in the UK for Selling Drugs on the DarkwebThree drug dealers were sentenced to prison for producing and selling kilogram quantities of drugs on...
SilentHound – Quietly Enumerate An Active Directory Domain Via LDAP Parsing Users, Admins, Groups, Etc.
SilentHound – Quietly Enumerate An Active Directory Domain Via LDAP Parsing Users, Admins, Groups, Etc.Quietly enumerate an Active Directory Domain via LDAP parsing users, admins, groups,...
Chinese hackers target energy sector in Australia, South China Sea
Chinese hackers target energy sector in Australia, South China SeaContenido de la entradaLeer másProofpoint News Feed
Woman Heads to Prison for Hiring a "Hitman” on the Darkweb
Woman Heads to Prison for Hiring a "Hitman” on the DarkwebA Pelahatchie, Mississippi, woman will spend ten years in prison for trying to hire a hitman...
ESP32 Marauder v0.9.12 releases: suite of WiFi/Bluetooth offensive and defensive tools for the ESP32
ESP32 Marauder v0.9.12 releases: suite of WiFi/Bluetooth offensive and defensive tools for the ESP32ESP32 Marauder The ESP32 Marauder is a suite of WiFi/Bluetooth offensive and defensive...
CVE-2022-29154: Rsync client-side arbitrary file write vulnerability
CVE-2022-29154: Rsync client-side arbitrary file write vulnerabilityThe developer of the rsync project has just released new versions of their software to patch a vulnerability (CVE-2022-29154) that......
The secret to managing deepfakes includes AI/DL & provenance
The secret to managing deepfakes includes AI/DL & provenanceKeely Wilkins is an Evangelist with the Office of the CTO as well as a Pre-Sales Security Engineer...
ForceAdmin: Create infinite UAC prompts forcing a user to run as admin
ForceAdmin: Create infinite UAC prompts forcing a user to run as adminForceAdmin ForceAdmin is a c# payload builder, creating infinite UAC pop-ups until the user allows...
Security Scorecards v4.5 releases: OSS Security Scorecards
Security Scorecards v4.5 releases: OSS Security ScorecardsSecurity Scorecards Goals Automate analysis and trust decisions on the security posture of open source projects. Use this data to......
Apache Tomcat Scanner: scan for Apache Tomcat server vulnerabilities
Apache Tomcat Scanner: scan for Apache Tomcat server vulnerabilitiesApache Tomcat Scanner A python script to scan for Apache Tomcat server vulnerabilities. Features Multithreaded workers to search...
Kage – Graphical User Interface For Metasploit Meterpreter And Session Handler
Kage – Graphical User Interface For Metasploit Meterpreter And Session HandlerKage (ka-geh) is a tool inspired by AhMyth designed for Metasploit RPC Server to interact with...
Jersey Teen Sentenced for Buying Amphetamine on Darkweb
Jersey Teen Sentenced for Buying Amphetamine on DarkwebA teenager who bought drugs on the darkweb was given 150 hours of community service. A Jersey teenager who...
NEW TECH SNAPSHOT: The role of ‘MSSPs’ in helping businesses manage cybersecurity
NEW TECH SNAPSHOT: The role of ‘MSSPs’ in helping businesses manage cybersecurityNetwork security has been radically altered, two-plus years into the global pandemic. Related: ‘Attack surface...
SHARED INTEL: The cybersecurity sea change coming with the implementation of ‘CMMC’
SHARED INTEL: The cybersecurity sea change coming with the implementation of ‘CMMC’Finally, Uncle Sam is compelling companies to take cybersecurity seriously. Related: How the Middle East...
GUEST ESSAY: The drivers behind persistent ransomware — and defense tactics to deploy
GUEST ESSAY: The drivers behind persistent ransomware — and defense tactics to deployThe internet has drawn comparisons to the Wild West, making ransomware the digital incarnation...
K21037322: Multiple MySQL vulnerabilities CVE-2022-21534 CVE-2022-21535 CVE-2022-21537 CVE-2022-21538 CVE-2022-21539
K21037322: Multiple MySQL vulnerabilities CVE-2022-21534 CVE-2022-21535 CVE-2022-21537 CVE-2022-21538 CVE-2022-21539Multiple MySQL vulnerabilities CVE-2022-21534 CVE-2022-21535 CVE-2022-21537 CVE-2022-21538 CVE-2022-21539 Security Advisory Security Advisory Description CVE-2022-21534 Vulnerability in the MySQL...
K35802610: Multiple MySQL vulnerabilities CVE-2022-21569, CVE-2022-21824, CVE-2022-22968, CVE-2022-23308, CVE-2022-27778
K35802610: Multiple MySQL vulnerabilities CVE-2022-21569, CVE-2022-21824, CVE-2022-22968, CVE-2022-23308, CVE-2022-27778Multiple MySQL vulnerabilities CVE-2022-21569, CVE-2022-21824, CVE-2022-22968, CVE-2022-23308, CVE-2022-27778 Security Advisory Security Advisory Description CVE-2022-21569 Vulnerability in the ......