Cloud attacks on the supply chain are a huge concernContenido de la entradaLeer másProofpoint News Feed
Author: admin
Cybercrime Group TA558 Ramps Up Email Attacks Against Hotels
Cybercrime Group TA558 Ramps Up Email Attacks Against HotelsContenido de la entradaLeer másProofpoint News Feed
CISA orders agencies to patch Chrome, D-Link flaws used in attacks
CISA orders agencies to patch Chrome, D-Link flaws used in attacksCISA has added 12 more security flaws to its list of bugs exploited in attacks, including...
Cloud security: Increased concern about risks from partners, suppliers
Cloud security: Increased concern about risks from partners, suppliersContenido de la entradaLeer másProofpoint News Feed
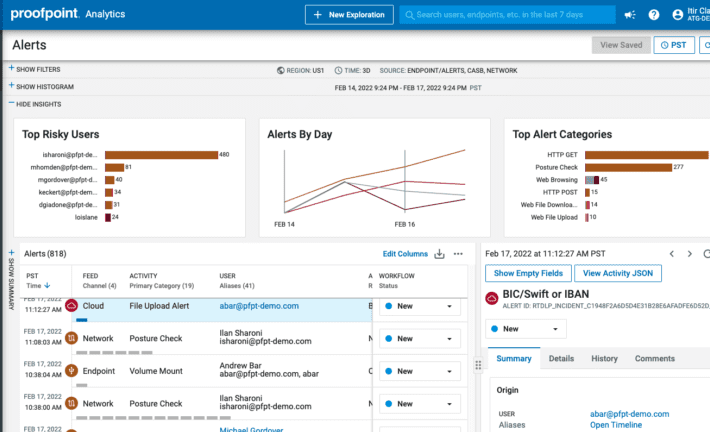
Best Data Security Solution | Proofpoint Information Protection
Best Data Security Solution | Proofpoint Information ProtectionContenido de la entradaLeer másProofpoint News Feed
GIFShell attack creates reverse shell using Microsoft Teams GIFs
GIFShell attack creates reverse shell using Microsoft Teams GIFsA new attack technique called 'GIFShell' allows threat actors to abuse Microsoft Teams for novel phishing attacks and...
Proofpoint Introduces a Smarter Way to Stay Compliant with New Intelligent Compliance Platform
Proofpoint Introduces a Smarter Way to Stay Compliant with New Intelligent Compliance PlatformContenido de la entradaLeer másProofpoint News Feed
Chinese hackers tied to attacks on South China Sea energy firms
Chinese hackers tied to attacks on South China Sea energy firmsContenido de la entradaLeer másProofpoint News Feed
Bumblebee malware adds post-exploitation tool for stealthy infections
Bumblebee malware adds post-exploitation tool for stealthy infectionsA new version of the Bumblebee malware loader has been spotted in the wild, featuring a new infection chain...
Warning of ransomware attacks on schools, here’s how to prepare…
Warning of ransomware attacks on schools, here’s how to prepare…EXECUTIVE SUMMARY: Earlier today, US agencies released a joint advisory pertaining to ransomware attacks on American schools....
Chinese hackers target energy sector in Australia, South China Sea
Chinese hackers target energy sector in Australia, South China SeaContenido de la entradaLeer másProofpoint News Feed
14 ways to secure business data, in layman’s language
14 ways to secure business data, in layman’s languageMazhar Hamayun is a cyber security professional with over 20 years of hands-on technology and leadership experience. At...
Multi-Cloud Networking and Security Makes a Splash at VMware Explore 2022
Multi-Cloud Networking and Security Makes a Splash at VMware Explore 2022The cloud has taken over the way enterprises do everything, from data storage to application development....
Multi-cloud with Continuous Risk-driven Security and Compliance
Multi-cloud with Continuous Risk-driven Security and ComplianceWe reviewed Zero Trust in a series of blogs earlier this month. In this blog, we are discussing a new...
A Pragmatic Response to the Quantum Threat
A Pragmatic Response to the Quantum ThreatYou certainly don't need to panic, but you do need to form a plan to prepare for the post-quantum reality.Leer...
Darktrace Shares Plunge After Thoma Bravo Acquisition Falls Apart
Darktrace Shares Plunge After Thoma Bravo Acquisition Falls ApartNo agreement could be reached on terms of a firm offer, the provider of AI-based cybersecurity products says.Leer...
Report Highlights Prevalence of Software Supply Chain Risks
Report Highlights Prevalence of Software Supply Chain RisksMulticlient research report shows organizations are significantly increasing efforts to secure their supply chains in response to software supply...
EvilProxy Bypasses MFA by Capturing Session Cookies
EvilProxy Bypasses MFA by Capturing Session CookiesThe latest ISMG Security Report discusses a new phishing-as-a-service toolkit designed to bypass multi-factor authentication, the decision by Lloyd's of...
Multi-Cloud Networking and Security Makes a Splash at VMware Explore 2022
Multi-Cloud Networking and Security Makes a Splash at VMware Explore 2022The cloud has taken over the way enterprises do everything, from data storage to application development....
Multi-cloud with Continuous Risk-driven Security and Compliance
Multi-cloud with Continuous Risk-driven Security and ComplianceWe reviewed Zero Trust in a series of blogs earlier this month. In this blog, we are discussing a new...
Multi-Cloud Networking and Security Makes a Splash at VMware Explore 2022
Multi-Cloud Networking and Security Makes a Splash at VMware Explore 2022The cloud has taken over the way enterprises do everything, from data storage to application development....
Multi-cloud with Continuous Risk-driven Security and Compliance
Multi-cloud with Continuous Risk-driven Security and ComplianceWe reviewed Zero Trust in a series of blogs earlier this month. In this blog, we are discussing a new...
Law Firm Says Year-Old Hack Affected PHI of 255,000 People
Law Firm Says Year-Old Hack Affected PHI of 255,000 PeopleBesides a Lag in Reporting, Some of the Compromised Data Was a Decade-OldA Michigan law firm recently...
North Korea Avoids Tornado Cash After US Imposes Sanctions
North Korea Avoids Tornado Cash After US Imposes SanctionsChainalysis Says It Helped Recover $30 Million in Hacked Ronin Bridge CryptoU.S. sanctions on Tornado Cash are driving...
Thief Steals $370,000 in Avalanche-Linked Flash Loan Attack
Thief Steals $370,000 in Avalanche-Linked Flash Loan AttackVictim Nereus Offers 'No Questions Asked' Reward for Return of Stolen FundsAn attacker stole at least $370,000 worth of...
LA School District Forewarned of Malware, Attack Risks
LA School District Forewarned of Malware, Attack RisksAlso: Vice Society Ransomware Gang Claims Credit for AttackThe only surprising aspect of the ransomware attack against Los Angeles...
Password manager LastPass reveals intrusion into development system
Password manager LastPass reveals intrusion into development systemLastPass, maker of a popular password management application, revealed Thursday that an unauthorized party gained access to its development...
Sorting zero-trust hype from reality
Sorting zero-trust hype from realityIt seems as if everyone is playing “buzzword bingo” when it comes to zero trust and its implementation, and it starts with...
Facebook agrees to settle class action lawsuit related to Cambridge Analytica data breach
Facebook agrees to settle class action lawsuit related to Cambridge Analytica data breachFacebook parent Meta Platforms agreed Friday to settle a class action lawsuit seeking damages...
Key takeaways from the Open Cybersecurity Schema Format
Key takeaways from the Open Cybersecurity Schema FormatOne of the most pervasive challenges in the current cybersecurity environment is an overabundance of tooling vendors, all of...