Security Risks in Logistics APIs Used by E-Commerce PlatformsOur research examines the security flaws that we found in the logistics API implementation of e-commerce platforms that...
Author: admin
NIST’s Expanding International Engagement on Cybersecurity
NIST’s Expanding International Engagement on CybersecurityIn providing a foundation for cybersecurity advancements over the years, NIST has taken the global context into account when determining priorities...
Uber exposes Lapsus$ extortion group for security breach
Uber exposes Lapsus$ extortion group for security breachIn last week’s security breach against Uber, the attackers downloaded internal messages from Slack as well as information from...
2K Games says hacked help desk targeted players with malware
2K Games says hacked help desk targeted players with malwareAmerican video game publisher 2K has confirmed that its help desk platform was hacked and used to...
Iranian cyberspies use multi-persona impersonation in phishing threads
Iranian cyberspies use multi-persona impersonation in phishing threadsContenido de la entradaLeer másProofpoint News Feed
Did hackers gain full access to Uber’s critical IT systems?
Did hackers gain full access to Uber’s critical IT systems?EXECUTIVE SUMMARY: Last week, Uber Technologies Inc. experienced a high-impact cyber attack. “They pretty much have full...
Imperva mitigated long-lasting, 25.3 billion request DDoS attack
Imperva mitigated long-lasting, 25.3 billion request DDoS attackInternet security company Imperva has announced its DDoS (distributed denial of service) mitigation solution has broken a new record,...
Death of Queen Elizabeth II exploited to steal Microsoft credentials
Death of Queen Elizabeth II exploited to steal Microsoft credentialsContenido de la entradaLeer másProofpoint News Feed
The Ransomware Files, Episode 11: The Adult Boutique
The Ransomware Files, Episode 11: The Adult BoutiqueDain Drake was CEO of a steel fabrication factory. In June 2019, Drake found himself standing outside a closed...
The prevention-first approach for SOC that your team needs to adopt
The prevention-first approach for SOC that your team needs to adoptAlon Bar, Product Marketing, Threat Prevention at Check Point Software Technologies Your SOC team works around...
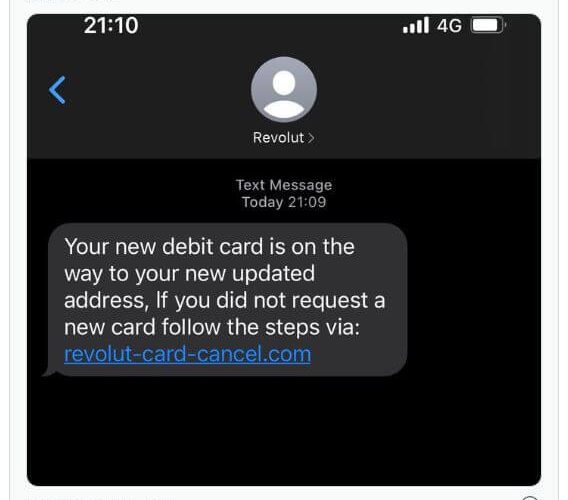
Revolut cyber attack exposes data belonging to thousands of customers
Revolut cyber attack exposes data belonging to thousands of customersEXECUTIVE SUMMARY: The London-based FinTech startup known as Revolut recently confirmed a breach that affected a “small...
Live Webinar | The Privacy and Security Implications of Big Health Data Initiatives
Live Webinar | The Privacy and Security Implications of Big Health Data InitiativesContenido de la entradaLeer másDataBreachToday.com RSS Syndication
SHARED INTEL: Poll highlights the urgency to balance digital resiliency, cybersecurity
SHARED INTEL: Poll highlights the urgency to balance digital resiliency, cybersecurityThe pace and extent of digital transformation that global enterprise organizations have undergone cannot be overstated....
Webinar | The State of Noncompliance in Cyber Risk Management
Webinar | The State of Noncompliance in Cyber Risk ManagementContenido de la entradaLeer másDataBreachToday.com RSS Syndication
K39178480: Perl vulnerability CVE-2018-18311
K39178480: Perl vulnerability CVE-2018-18311Perl vulnerability CVE-2018-18311 Security Advisory Security Advisory Description Perl before 5.26.3 and 5.28.x before 5.28.1 has a buffer overflow via a crafted regular...
MSA-22-0026: No groups filtering in H5P activity attempts report
MSA-22-0026: No groups filtering in H5P activity attempts reportby Michael Hawkins. The H5P activity attempts report did not filter by groups, which in separate groups mode...
The Evolution of the Chromeloader Malware
The Evolution of the Chromeloader MalwareExecutive Summary Chromeloader proves to be an extremely prevalent and persistent malware. It initially drops as an .iso and can be...
MSA-22-0024: Remote code execution risk when restoring malformed backup file from Moodle 1.9
MSA-22-0024: Remote code execution risk when restoring malformed backup file from Moodle 1.9by Michael Hawkins. A remote code execution risk when restoring backup files originating from...
MSA-22-0025: Minor SQL injection risk in admin user browsing
MSA-22-0025: Minor SQL injection risk in admin user browsingby Michael Hawkins. A limited SQL injection risk was identified in the "browse list of users" site administration...
LIVE Webinar | Social Engineering, Phishing & Pen Testing: Hardening Your Soft Spots
LIVE Webinar | Social Engineering, Phishing & Pen Testing: Hardening Your Soft SpotsContenido de la entradaLeer másDataBreachToday.com RSS Syndication
MSA-22-0023: Stored XSS and page denial of service risks due to recursive rendering in Mustache template helpers
MSA-22-0023: Stored XSS and page denial of service risks due to recursive rendering in Mustache template helpersby Michael Hawkins. Recursive rendering of Mustache template helpers containing...
2-Step Email Attack Uses Powtoon Video to Execute Payload
2-Step Email Attack Uses Powtoon Video to Execute PayloadThe attack uses hijacked Egress branding and the legit Powtoon video platform to steal user credentials.Leer másDark ReadingThe...
ChromeLoader Malware Evolves into Prevalent, More Dangerous Cyber Threat
ChromeLoader Malware Evolves into Prevalent, More Dangerous Cyber ThreatMicrosoft and VMware are warning that the malware, which first surfaced as a browser-hijacking credential stealer, is now...
Adopting a Zero Trust Philosophy: A Fireside Chat with John Kindervag
Adopting a Zero Trust Philosophy: A Fireside Chat with John KindervagContenido de la entradaLeer másDataBreachToday.com RSS Syndication
Uber responding to ‘cybersecurity incident’ after hack
Uber responding to ‘cybersecurity incident’ after hackRide-hailing company confirms attack after hacker compromises Slack app and messages employees Uber has been hacked in an attack that...
Hacker Plunders $160M From Crypto Market Maker Wintermute
Hacker Plunders $160M From Crypto Market Maker WintermuteHack May Stem From Known Wallet Addressing VulnerabilityA newly uncovered vulnerability in a wallet addressing tool may be the...
K39178480: Perl vulnerability CVE-2018-18311
K39178480: Perl vulnerability CVE-2018-18311Perl vulnerability CVE-2018-18311 Security Advisory Security Advisory Description Perl before 5.26.3 and 5.28.x before 5.28.1 has a buffer overflow via a crafted regular...
MSA-22-0026: No groups filtering in H5P activity attempts report
MSA-22-0026: No groups filtering in H5P activity attempts reportby Michael Hawkins. The H5P activity attempts report did not filter by groups, which in separate groups mode...
The Evolution of the Chromeloader Malware
The Evolution of the Chromeloader MalwareExecutive Summary Chromeloader proves to be an extremely prevalent and persistent malware. It initially drops as an .iso and can be...
K39178480: Perl vulnerability CVE-2018-18311
K39178480: Perl vulnerability CVE-2018-18311Perl vulnerability CVE-2018-18311 Security Advisory Security Advisory Description Perl before 5.26.3 and 5.28.x before 5.28.1 has a buffer overflow via a crafted regular...