Imperva mitigated long-lasting, 25.3 billion request DDoS attackInternet security company Imperva has announced its DDoS (distributed denial of service) mitigation solution has broken a new record,...
Author: admin
Did hackers gain full access to Uber’s critical IT systems?
Did hackers gain full access to Uber’s critical IT systems?EXECUTIVE SUMMARY: Last week, Uber Technologies Inc. experienced a high-impact cyber attack. “They pretty much have full...
The prevention-first approach for SOC that your team needs to adopt
The prevention-first approach for SOC that your team needs to adoptAlon Bar, Product Marketing, Threat Prevention at Check Point Software Technologies Your SOC team works around...
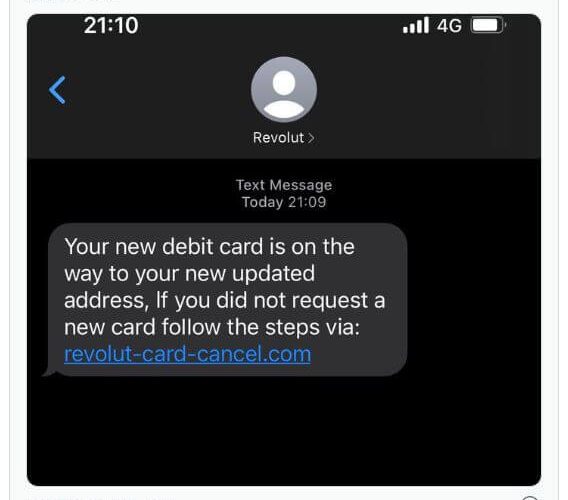
Revolut cyber attack exposes data belonging to thousands of customers
Revolut cyber attack exposes data belonging to thousands of customersEXECUTIVE SUMMARY: The London-based FinTech startup known as Revolut recently confirmed a breach that affected a “small...
What is Managed Detection and Response (MDR)?
What is Managed Detection and Response (MDR)?The term managed detection and response (MDR) refers to a cybersecurity service that employs advanced technologies and human expertise to...
What Is Privileged Identity Management (PIM)?
What Is Privileged Identity Management (PIM)?When we talk about Privileged Access Management (PAM), Privileged Identity Management (PIM), Identity and Access Management (IAM), and other access management...
Starbucks Singapore Customer Data Accessed Illegally in Data Leak
Starbucks Singapore Customer Data Accessed Illegally in Data LeakStarbucks Singapore notifies members of its Rewards loyalty programme that personal information, including phone numbers, addresses, and birthdays...
Malware vs. Ransomware: Do You Know the Difference?
Malware vs. Ransomware: Do You Know the Difference?When it comes to cybersecurity, few domains can match its ever-growing lexicon and branching categories. It is no wonder...
Empress EMS Discloses Data Breach Following Ransomware Attack
Empress EMS Discloses Data Breach Following Ransomware AttackNew York-based company, Empress EMS (Emergency Medical Services), has disclosed through an official notification that it’s been the victim...
The European Union Prepares New Cybersecurity Regulations for IoT Devices
The European Union Prepares New Cybersecurity Regulations for IoT DevicesThe European Commission has suggested a new “EU Cyber Resilience Act.” The act intends to protect customers...
Revolut Suffers Data Breach
Revolut Suffers Data BreachOver 50,000 people’s personal information was compromised as a result of a cyberattack on Revolut. After a Revolut employee fell for a phishing...
Allies Warn of Iranian Ransom Attacks Using Log4Shell
Allies Warn of Iranian Ransom Attacks Using Log4ShellUS authorities indict and sanction in fresh crackdownLeer másUS authorities indict and sanction in fresh crackdown
No Customer Data or Encrypted Password Vaults Were Breached in LastPass Incident
No Customer Data or Encrypted Password Vaults Were Breached in LastPass IncidentIn an update to the notification regarding the cyberattack suffered in August, LastPass, one of...
CISA Expands Vulnerabilities Catalog With Old, Exploited Flaws
CISA Expands Vulnerabilities Catalog With Old, Exploited FlawsFour of the CVEs posted are from 2013, and one is from 2010Leer másFour of the CVEs posted are...
New Spear Phish Methodology Relies on PuTTY SSH Client to Infect Systems
New Spear Phish Methodology Relies on PuTTY SSH Client to Infect SystemsIt tried to trick victims into clicking on malicious files as part of a fake...
American Airlines Suffers Data Breach After Email Compromise
American Airlines Suffers Data Breach After Email CompromiseAmerican Airlines notified its clients on Friday, September 16th, that they have been the victims of a cyberattack after...
Rockstar Games Confirms Hacker Stole Early Grand Theft Auto VI Footage
Rockstar Games Confirms Hacker Stole Early Grand Theft Auto VI FootageAmerican video game publisher Rockstar Games on Monday revealed it was a victim of a "network...
Uber Blames Lapsus$ for Breach
Uber Blames Lapsus$ for BreachThreat actor bombarded Uber contractor with 2FA requestsLeer másThreat actor bombarded Uber contractor with 2FA requests
Emotet Botnet Started Distributing Quantum and BlackCat Ransomware
Emotet Botnet Started Distributing Quantum and BlackCat RansomwareThe Emotet malware is now being leveraged by ransomware-as-a-service (RaaS) groups, including Quantum and BlackCat, after Conti's official retirement from the...
Microsoft Teams’ GIFShell Attack: What Is It and How You Can Protect Yourself from It
Microsoft Teams' GIFShell Attack: What Is It and How You Can Protect Yourself from ItOrganizations and security teams work to protect themselves from any vulnerability, and...
Uber Blames LAPSUS$ Hacking Group for Recent Security Breach
Uber Blames LAPSUS$ Hacking Group for Recent Security BreachUber on Monday disclosed more details related to the security incident that happened last week, pinning the attack on a...
FBI Lessons on Fighting Cybercrime: Three Tips on How to Improve Cybersecurity
FBI Lessons on Fighting Cybercrime: Three Tips on How to Improve CybersecurityOver 2,700 participants from 29 countries gathered for an event that was jam-packed with news about...
Russian Sandworm Hackers Impersonate Ukrainian Telecoms to Distribute Malware
Russian Sandworm Hackers Impersonate Ukrainian Telecoms to Distribute MalwareA threat cluster linked to the Russian nation-state actor tracked as Sandworm has continued its targeting of Ukraine...
Revolut Breach May Have Hit 50,000+ Customers
Revolut Breach May Have Hit 50,000+ CustomersMajor phishing risk as personal details are compromisedLeer másMajor phishing risk as personal details are compromised
American Airlines Breach Exposes Customer and Staff Information
American Airlines Breach Exposes Customer and Staff InformationAn undisclosed number of people have been impactedLeer másAn undisclosed number of people have been impacted
Lapsus$ Hacking Group Allegedly Behind the Uber Security Breach
Lapsus$ Hacking Group Allegedly Behind the Uber Security BreachOn Monday, September 19, Uber posted on its blog updates about the security breach that happened on September...
Quantum Computing Already Putting Data at Risk, Cyber Pros Agree
Quantum Computing Already Putting Data at Risk, Cyber Pros AgreeIn the Deloitte poll, 50.2% of respondents said their organization is at risk of ‘harvest now, decrypt...
Hackers Admit Destroying InterContinental Hotels Group’s Data ‘For Fun’
Hackers Admit Destroying InterContinental Hotels Group's Data 'For Fun'They tried to conduct a ransomware attack against IHG and upon failing, decided to delete the dataLeer másThey...
Chinese hackers target energy sector in Australia, South China Sea
Chinese hackers target energy sector in Australia, South China SeaContenido de la entradaLeer másProofpoint News Feed
Microsoft Support Diagnostic Tool Vulnerability: What to Learn from It and How to Stay Safe
Microsoft Support Diagnostic Tool Vulnerability: What to Learn from It and How to Stay SafeBy Dirk Schrader, Resident CISO (EMEA) and VP of Security Research, Netwrix...