D&O insurance not yet a priority despite criminal trial of Uber’s former CISOThe trial of former Uber CISO Joe Sullivan marks the first time a cybersecurity...
Author: admin
Critical Remote Hack Flaws Found in Dataprobe’s Power Distribution Units
Critical Remote Hack Flaws Found in Dataprobe's Power Distribution UnitsThe U.S. Cybersecurity and Infrastructure Security Agency (CISA) on Tuesday released an industrial control systems (ICS) advisory...
Product Review: Stellar Cyber Open XDR Platform
Product Review: Stellar Cyber Open XDR PlatformAlmost every vendor, from email gateway companies to developers of threat intelligence platforms, is positioning themselves as an XDR player....
S3 Ep100: Browser-in-the-Browser – how to spot an attack [Audio + Text]
S3 Ep100: Browser-in-the-Browser – how to spot an attack [Audio + Text]Latest episode - listen now! Cosmic rockets, zero-days, spotting cybercrooks, and unlocking the DEADBOLT...Leer másNaked...
Why Zero Trust Should be the Foundation of Your Cybersecurity Ecosystem
Why Zero Trust Should be the Foundation of Your Cybersecurity EcosystemFor cybersecurity professionals, it is a huge challenge to separate the “good guys” from the “villains”....
Serious Security: Browser-in-the-browser attacks – watch out for windows that aren’t!
Serious Security: Browser-in-the-browser attacks – watch out for windows that aren’t!Simple but super-sneaky - use a picture of a browser, and convince people it's real...Leer másNaked...
U.S. Adds 2 More Chinese Telecom Firms to National Security Threat List
U.S. Adds 2 More Chinese Telecom Firms to National Security Threat ListThe U.S. Federal Communications Commission (FCC) has added Pacific Network Corp, along with its subsidiary...
Record DDoS Attack with 25.3 Billion Requests Abused HTTP/2 Multiplexing
Record DDoS Attack with 25.3 Billion Requests Abused HTTP/2 MultiplexingCybersecurity company Imperva has disclosed that it mitigated a distributed denial-of-service (DDoS) attack with a total of...
Hackers Targeting Unpatched Atlassian Confluence Servers to Deploy Crypto Miners
Hackers Targeting Unpatched Atlassian Confluence Servers to Deploy Crypto MinersA now-patched critical security flaw affecting Atlassian Confluence Server that came to light a few months ago...
LastPass source code breach – incident response report released
LastPass source code breach – incident response report releasedWondering how you'd handle a data breach report if the worst happened to you? Here's a useful example.Leer...
Over 39,000 Unauthenticated Redis Instances Found Exposed on the Internet
Over 39,000 Unauthenticated Redis Instances Found Exposed on the InternetAn unknown attacker targeted tens of thousands of unauthenticated Redis servers exposed on the internet in an...
S3 Ep100.5: Uber breach – an expert speaks [Audio + Text]
S3 Ep100.5: Uber breach – an expert speaks [Audio + Text]Chester Wisniewski on what we can learn from Uber: "Just because a big company didn't have...
UBER HAS BEEN HACKED, boasts hacker – how to stop it happening to you
UBER HAS BEEN HACKED, boasts hacker – how to stop it happening to youUber is all over the news for a widely-publicised data breach. We help...
Crypto Trading Firm Wintermute Loses $160 Million in Hacking Incident
Crypto Trading Firm Wintermute Loses $160 Million in Hacking IncidentIn what's the latest crypto heist to target the decentralized finance (DeFi) space, hackers have stolen digital...
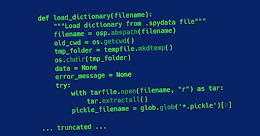
15-Year-Old Unpatched Python Vulnerability Potentially Affects Over 350,000 Projects
15-Year-Old Unpatched Python Vulnerability Potentially Affects Over 350,000 ProjectsAs many as 350,000 open source projects are believed to be potentially vulnerable to exploitation as a result...
Interested in cybersecurity? Join us for Security SOS Week 2022!
Interested in cybersecurity? Join us for Security SOS Week 2022!Four one-on-one interviews with experts who are passionate about sharing their expertise with the community.Leer másNaked SecurityFour...
Our Quest: Advancing Product Labels to Help Consumers Consider Cybersecurity
Our Quest: Advancing Product Labels to Help Consumers Consider CybersecurityFor many decades, consumers have relied on labels to help them make decisions about which products to...
Microsoft 365 phishing attacks impersonate U.S. govt agencies
Microsoft 365 phishing attacks impersonate U.S. govt agenciesAn ongoing phishing campaign targeting U.S. government contractors has expanded its operation to push higher-quality lures and better-crafted documents....
American Airlines discloses data breach after employee email compromise
American Airlines discloses data breach after employee email compromiseAmerican Airlines has notified customers of a recent data breach after attackers compromised an undisclosed number of employee email accounts...
MFA Fatigue: Hackers’ new favorite tactic in high-profile breaches
MFA Fatigue: Hackers’ new favorite tactic in high-profile breachesHackers are more frequently using social engineering attacks to gain access to corporate credentials and breach large networks....
Microsoft Defender for Endpoint will turn on tamper protection by default
Microsoft Defender for Endpoint will turn on tamper protection by defaultMicrosoft says tamper protection will soon be turned on by default for all enterprise customers in...
Top 8 takeaways from the VMWare Cybersecurity Threat Report
Top 8 takeaways from the VMWare Cybersecurity Threat ReportVMware has recently released the 2022 edition of its annual Global Incident Response Threat Report. It is critically...
Hackers steal $162 million from Wintermute crypto market maker
Hackers steal $162 million from Wintermute crypto market makerDigital assets trading firm Wintermute has been hacked and lost $162.2 million in DeFi operations, the company CEO, Evgeny Gaevoy,...
2K game support hacked to email RedLine info-stealing malware
2K game support hacked to email RedLine info-stealing malwareHackers have compromised the support system of American video game publisher 2K and now are sending support tickets...
Windows 11 22H2 is released, here are the new features
Windows 11 22H2 is released, here are the new featuresMicrosoft has released the next version of Windows 11 called "22H2," otherwise known as the Windows 11 2022...
Hive ransomware claims attack on New York Racing Association
Hive ransomware claims attack on New York Racing AssociationThe Hive ransomware operation claimed responsibility for an attack on the New York Racing Association (NYRA), which previously...
Windows 11 22H2 adds kernel exploit protection to security baseline
Windows 11 22H2 adds kernel exploit protection to security baselineMicrosoft has released the final version of security configuration baseline settings for Windows 11, version 22H2, downloadable...
Windows 10 KB5017380 preview update released with new FIDO2 features
Windows 10 KB5017380 preview update released with new FIDO2 featuresMicrosoft has released the optional KB5017380 Preview cumulative update for Windows 10 20H2, Windows 10 21H1, and...
2K Games says hacked help desk targeted players with malware
2K Games says hacked help desk targeted players with malwareAmerican video game publisher 2K has confirmed that its help desk platform was hacked and used to...
Uber exposes Lapsus$ extortion group for security breach
Uber exposes Lapsus$ extortion group for security breachIn last week’s security breach against Uber, the attackers downloaded internal messages from Slack as well as information from...