Adversarial ML Attack that Secretly Gives a Language Model a Point of ViewMachine learning security is extraordinarily difficult because the attacks are so varied—and it seems...
Author: admin
Attack Surface Management 2022 Midyear Review Part 1
Attack Surface Management 2022 Midyear Review Part 1In our 2022 midyear roundup, we examine the most significant trends and incidents that influenced the cybersecurity landscape in...
Battle with Bots Prompts Mass Purge of Amazon, Apple Employee Accounts on LinkedIn
Battle with Bots Prompts Mass Purge of Amazon, Apple Employee Accounts on LinkedInOn October 10, 2022, there were 576,562 LinkedIn accounts that listed their current employer...
Friday Squid Blogging: The Reproductive Habits of Giant Squid
Friday Squid Blogging: The Reproductive Habits of Giant SquidInteresting: A recent study on giant squid that have washed ashore along the Sea of Japan coast has...
Most Concerning Security Vulnerabilities in Medical Devices
Most Concerning Security Vulnerabilities in Medical DevicesSecurity flaws in a vital signs monitoring device from a China-based manufacturer could allow hackers to launch an attack that...
Uncovering Security Blind Spots in CNC Machines
Uncovering Security Blind Spots in CNC MachinesIndustry 4.0 has given rise to smart factories that have markedly improved machining processes, but it has also opened the...
On the Randomness of Automatic Card Shufflers
On the Randomness of Automatic Card ShufflersMany years ago, Matt Blaze and I talked about getting our hands on a casino-grade automatic shuffler and looking for...
Russian-Speaking Ransomware Gangs Hit New Victim: Russians
Russian-Speaking Ransomware Gangs Hit New Victim: RussiansThe latest edition of the ISMG Security Report discusses how Russian-speaking ransomware gangs have their eyes on a new target,...
LV Ransomware Exploits ProxyShell in Attack on a Jordan-based Company
LV Ransomware Exploits ProxyShell in Attack on a Jordan-based CompanyOur blog entry provides a look at an attack involving the LV ransomware on a Jordan-based company...
Webinar | Why Should Modern Endpoint Protection be Cloud-Based?
Webinar | Why Should Modern Endpoint Protection be Cloud-Based?Contenido de la entradaLeer másDataBreachToday.com RSS Syndication
8 essential ways to prevent ever-infuriating keyless car theft
8 essential ways to prevent ever-infuriating keyless car theftEXECUTIVE SUMMARY: The era of hotwiring cars is long since over. Contemporary car thieves leverage exceedingly sophisticated techniques...
GUEST ESSAY: These advanced phishing tactics should put all businesses on high alert
GUEST ESSAY: These advanced phishing tactics should put all businesses on high alertPhishing attacks are nothing new, but scammers are getting savvier with their tactics. Related:...
Massive cryptomining campaign abuses free-tier cloud dev resources
Massive cryptomining campaign abuses free-tier cloud dev resourcesAn automated and large-scale 'freejacking' campaign abuses free GitHub, Heroku, and Buddy services to mine cryptocurrency at the provider's...
CISOs, Board Members and the Search for Cybersecurity Common Ground
CISOs, Board Members and the Search for Cybersecurity Common GroundContenido de la entradaLeer másProofpoint News Feed
GUEST ESSAY: Restore Us Institute (RUI) aims to protect Americans from online harms and crimes
GUEST ESSAY: Restore Us Institute (RUI) aims to protect Americans from online harms and crimesHow did America and Americans regress to being much less secure than...
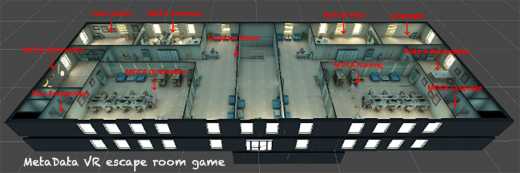
GUEST ESSAY: Privacy risks introduced by the ‘metaverse’ — and how to combat them
GUEST ESSAY: Privacy risks introduced by the ‘metaverse’ — and how to combat themAs digital technologies become more immersive and tightly integrated with our daily lives,...
GUEST ESSAY: A breakout of how Google, Facebook, Instagram enable third-party snooping
GUEST ESSAY: A breakout of how Google, Facebook, Instagram enable third-party snoopingMore and more consumers are using apps every year. In fact, Google Play users downloaded...
MY TAKE: Why the Matter smart home standard portends the coming of the Internet of Everything
MY TAKE: Why the Matter smart home standard portends the coming of the Internet of EverythingStandards. Where would we be without them? Universally accepted protocols give...
Optus data breach: federal police launch ‘Operation Guardian’ to protect identity of 10,000 victims
Optus data breach: federal police launch ‘Operation Guardian’ to protect identity of 10,000 victimsOptus has agreed to repay the cost of replacement passports for those affected...
GUEST ESSAY: Sure steps to achieve a robust employee cybersecurity awareness training regimen
GUEST ESSAY: Sure steps to achieve a robust employee cybersecurity awareness training regimenEmployee security awareness is the most important defense against data breaches. Related: Leveraging security...
Ransomware hunters: the self-taught tech geniuses fighting cybercrime
Ransomware hunters: the self-taught tech geniuses fighting cybercrimeHackers are increasingly taking users’ data hostage and demanding huge sums for its release. They have targeted individuals, businesses,...
Staff at security firm G4S on alert after tax numbers and bank details posted online following hack
Staff at security firm G4S on alert after tax numbers and bank details posted online following hackExclusive: Ransomware attack on Port Phillip prison revealed in July...
Serial cyberstalker Matthew Hardy has jail term cut
Serial cyberstalker Matthew Hardy has jail term cutJail term reduced by a year from original sentencing at Chester crown court The court of appeal has reduced...
FIRESIDE CHAT: Timely employee training, targeted testing needed to quell non-stop phishing
FIRESIDE CHAT: Timely employee training, targeted testing needed to quell non-stop phishingHumans are rather easily duped. And this is the fundamental reason phishing persists as a...
K24084759: Linux kernel vulnerability CVE-2018-9517
K24084759: Linux kernel vulnerability CVE-2018-9517Linux kernel vulnerability CVE-2018-9517 Security Advisory Security Advisory Description In pppol2tp_connect, there is possible memory corruption due to a use after free....
Monday briefing: What one man’s decade of harassment tells us about stalking in the UK
Monday briefing: What one man’s decade of harassment tells us about stalking in the UKIn today’s newsletter: Matthew Hardy’s sentence for stalking is believed to be...
K62201745: OpenSSH vulnerability CVE-2016-10012
K62201745: OpenSSH vulnerability CVE-2016-10012OpenSSH vulnerability CVE-2016-10012 Security Advisory Security Advisory Description The shared memory manager (associated with pre-authentication compression) in sshd in OpenSSH before 7.4 does...
Live Webinar | 10 Ways Asset Visibility Builds an Effective OT Cybersecurity Foundation
Live Webinar | 10 Ways Asset Visibility Builds an Effective OT Cybersecurity FoundationContenido de la entradaLeer másDataBreachToday.com RSS Syndication
K19473400: Linux Kernel vulnerability CVE-2018-9516
K19473400: Linux Kernel vulnerability CVE-2018-9516Linux Kernel vulnerability CVE-2018-9516 Security Advisory Security Advisory Description In hid_debug_events_read of drivers/hid/hid-debug.c, there is a possible out of bounds write due...
Can I tell you a secret? Episode seven: an update
Can I tell you a secret? Episode seven: an updateGuardian producer Lucy Hough and reporter Matthew Weaver give an update on the outcome of Matthew Hardy’s...