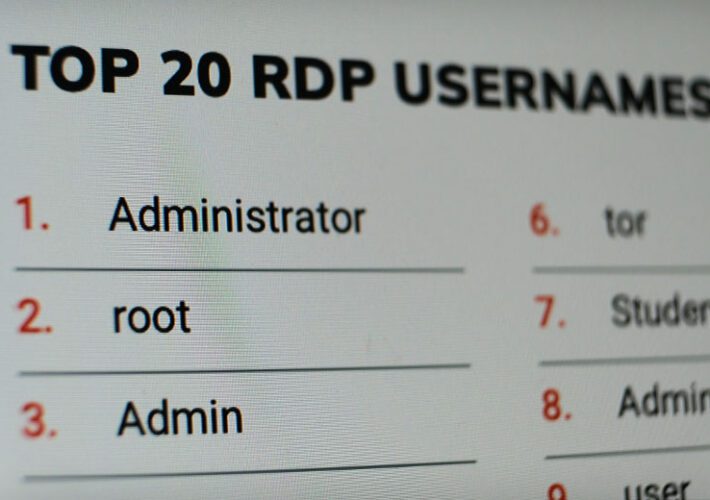
Why Are We So Stupid About Passwords? SSH and RDP EditionPoor Credential Hygiene Leaves Remote Services at Risk of Brute Force AttacksIf remote access to corporate...
Author: admin
OldGremlin Ransomware Targeted Over a Dozen Russian Entities in Multi-Million Scheme
OldGremlin Ransomware Targeted Over a Dozen Russian Entities in Multi-Million SchemeA Russian-speaking ransomware group dubbed OldGremlin has been attributed to 16 malicious campaigns aimed at entities...
Stronger Cloud Security in Azure Functions Using Custom Cloud Container
Stronger Cloud Security in Azure Functions Using Custom Cloud ContainerIn this entry, we discuss how developers can use custom cloud container image and the distroless approach...
Hackers Using New Version of FurBall Android Malware to Spy on Iranian Citizens
Hackers Using New Version of FurBall Android Malware to Spy on Iranian CitizensThe Iranian threat actor known as Domestic Kitten has been attributed to a new...
Microsoft Confirms Server Misconfiguration Led to 65,000+ Companies’ Data Leak
Microsoft Confirms Server Misconfiguration Led to 65,000+ Companies' Data LeakMicrosoft this week confirmed that it inadvertently exposed information related to thousands of customers following a security...
Google Launches GUAC Open Source Project to Secure Software Supply Chain
Google Launches GUAC Open Source Project to Secure Software Supply ChainGoogle on Thursday announced that it's seeking contributors to a new open source initiative called Graph...
POLONIUM targets Israel with Creepy malware
POLONIUM targets Israel with Creepy malwareESET researchers analyzed previously undocumented custom backdoors and cyberespionage tools deployed in Israel by the POLONIUM APT group The post POLONIUM...
Hackers Started Exploiting Critical “Text4Shell” Apache Commons Text Vulnerability
Hackers Started Exploiting Critical "Text4Shell" Apache Commons Text VulnerabilityWordPress security company Wordfence on Thursday said it started detecting exploitation attempts targeting the newly disclosed flaw in...
A Quick Look at the “Strengthening America’s Cybersecurity” Initiative
A Quick Look at the "Strengthening America's Cybersecurity" InitiativeAcknowledging that you have a problem is the first step to addressing the problem in a serious way....
What Is A Keylogger? Definition, Types, Examples and Prevention
What Is A Keylogger? Definition, Types, Examples and PreventionA keylogger is a software or hardware component that records everything typed on your computer’s keyboard. The term...
Emotet Botnet Distributing Self-Unlocking Password-Protected RAR Files to Drop Malware
Emotet Botnet Distributing Self-Unlocking Password-Protected RAR Files to Drop MalwareThe notorious Emotet botnet has been linked to a new wave of malspam campaigns that take advantage of password-protected...
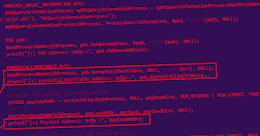
Multiple Campaigns Exploit VMware Vulnerability to Deploy Crypto Miners and Ransomware
Multiple Campaigns Exploit VMware Vulnerability to Deploy Crypto Miners and RansomwareA now-patched vulnerability in VMware Workspace ONE Access has been observed being exploited to deliver both...
CISA Warns of Daixin Team Hackers Targeting Health Organizations With Ransomware
CISA Warns of Daixin Team Hackers Targeting Health Organizations With RansomwareU.S. cybersecurity and intelligence agencies have published a joint advisory warning of attacks perpetrated by a...
Why Ransomware in Education on the Rise and What That Means for 2023
Why Ransomware in Education on the Rise and What That Means for 2023The breach of LA Unified School District (LAUSD) highlights the prevalence of password vulnerabilities,...
10 common Zelle scams – and how to avoid them
10 common Zelle scams – and how to avoid themFraudsters use various tactics to separate people from their hard-earned cash on Zelle. Here’s how to keep...
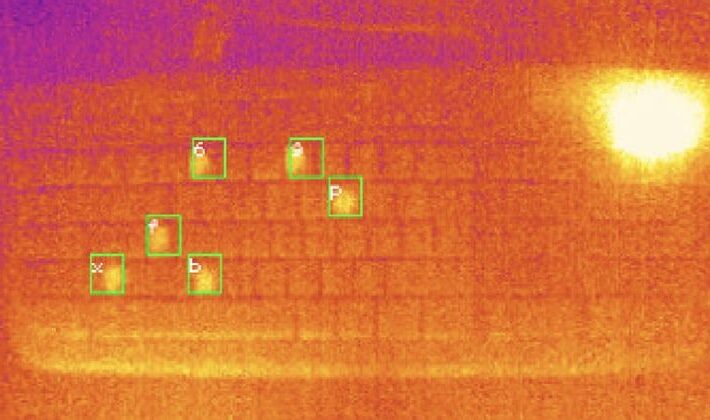
Heat left by users’ fingertips could help hackers crack passwords, researchers claim
Heat left by users’ fingertips could help hackers crack passwords, researchers claimBoffins at the University of Glasgow, in Scotland, have developed a system which they claim...
Critical Flaw Reported in Move Virtual Machine Powering the Aptos Blockchain Network
Critical Flaw Reported in Move Virtual Machine Powering the Aptos Blockchain NetworkResearchers have disclosed details about a now-patched critical flaw in the Move virtual machine that...
Download eBook: Top virtual CISOs share 7 tips for vCISO service providers
Download eBook: Top virtual CISOs share 7 tips for vCISO service providersVirtual Chief Information Security Officer (vCISO) services (also known as 'Fractional CISO' or 'CISO-as-a-Service') are...
SideWinder APT Using New WarHawk Backdoor to Target Entities in Pakistan
SideWinder APT Using New WarHawk Backdoor to Target Entities in PakistanSideWinder, a prolific nation-state actor mainly known for targeting Pakistan military entities, compromised the official website...
Kolide, endpoint security for teams that want to meet SOC 2 compliance goals without sacrificing privacy
Kolide, endpoint security for teams that want to meet SOC 2 compliance goals without sacrificing privacyGraham Cluley Security News is sponsored this week by the folks...
Life in pursuit of answers: In the words of Ada Yonath
Life in pursuit of answers: In the words of Ada YonathFrom a little girl financially helping her family in Jerusalem to a Nobel Prize laureate. That is...
Apple Releases Patch for New Actively Exploited iOS and iPadOS Zero-Day Vulnerability
Apple Releases Patch for New Actively Exploited iOS and iPadOS Zero-Day VulnerabilityTech giant Apple on Monday rolled out updates to remediate a zero-day flaw in iOS...
Water Labbu Abuses Malicious DApps to Steal Cryptocurrency
Water Labbu Abuses Malicious DApps to Steal CryptocurrencyThe parasitic Water Labbu capitalizes on the social engineering schemes of other scammers, injecting malicious JavaScript code into their...
Why Palo Alto Networks Now Wants Cider Security, Not Apiiro
Why Palo Alto Networks Now Wants Cider Security, Not ApiiroPalo Alto in Talks to Buy Cider for $200M, Walks Away From $600M Apiiro DealPalo Alto Networks...
Ukrainian Governmental Agencies Targeted by Ransomware Attacks
Ukrainian Governmental Agencies Targeted by Ransomware AttacksAn alert has been issued by the Computer Emergency Response Team of Ukraine (CERT-UA) on October 21st regarding Cuba Ransomware...
ESET research into POLONIUM’s arsenal – Week in security with Tony Anscombe
ESET research into POLONIUM’s arsenal – Week in security with Tony AnscombeMore than a dozen organizations operating in various verticals were attacked by the threat actor...
5 steps to protect your school from cyberattacks
5 steps to protect your school from cyberattacksWhat can schools, which all too often make easy prey for cybercriminals, do to bolster their defenses and keep...
Why Cybereason Went From IPO Candidate to Seeking a Buyer
Why Cybereason Went From IPO Candidate to Seeking a BuyerStiff Competition, Muddled Go-to-Market Strategy Put Cybereason on Path to SellingCybereason has abandoned its IPO plans altogether...
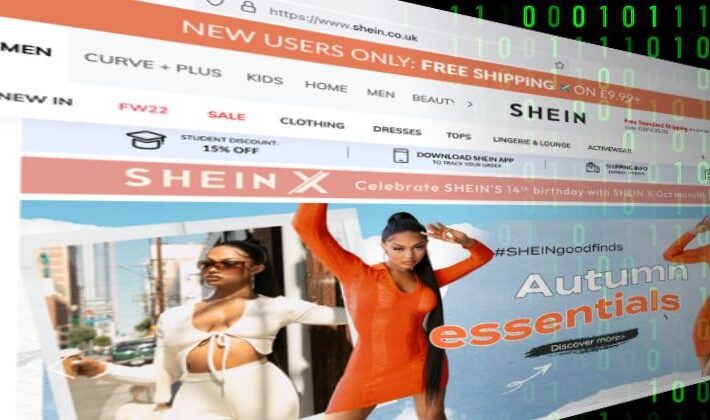
Fine for Shein! Fashion site hit with $1.9 million bill after lying about data breach
Fine for Shein! Fashion site hit with $1.9 million bill after lying about data breachThe parent company of women's fashion site Shein has been fined $1.9...
Emotet Botnet Drops Malware via Self-Unlocking Password-Protected RAR Files
Emotet Botnet Drops Malware via Self-Unlocking Password-Protected RAR FilesA surge of malspam campaigns has been recently attributed to Emotet botnet. Taking advantage of password-protected archive files, the notorious...