New Malicious Clicker found in apps installed by 20M+ users Authored by SangRyol Ryu Cybercriminals are always after illegal advertising revenue. As we have previously reported,...
Author: admin
Cisco Event Response: September 2022 Semiannual Cisco IOS and IOS XE Software Security Advisory Bundled Publication
Cisco Event Response: September 2022 Semiannual Cisco IOS and IOS XE Software Security Advisory Bundled PublicationContenido de la entradaLeer másCisco Event Responses
Massive Freejacking Campaign Abuses Cloud Dev Resources
Massive Freejacking Campaign Abuses Cloud Dev ResourcesA large-scale freejacking campaign is abusing GitHub, Heroku, and Buddy services to mine cryptocurrency at the expense of the provider....
“This Connection Is Not Private” – What it Means and How to Protect Your Privacy
“This Connection Is Not Private” – What it Means and How to Protect Your Privacy Have you ever been browsing online and clicked a link or...
How to Tell Whether a Website Is Safe or Unsafe
How to Tell Whether a Website Is Safe or Unsafe It’s important to know that not all websites are safe to visit. In fact, some sites...
Big Changes are Afoot: Expanding and Enhancing the Have I Been Pwned API
Big Changes are Afoot: Expanding and Enhancing the Have I Been Pwned APIJust over 3 years ago now, I sat down at a makeshift desk (ok,...
The not-so-Charming Kitten working for Iran
The not-so-Charming Kitten working for IranContenido de la entradaLeer másProofpoint News Feed
The U.K. Company Interserve Fined for Lack of Cybersecurity Measures
The U.K. Company Interserve Fined for Lack of Cybersecurity MeasuresConstruction group Interserve was fined by the UK’s Information Commissioner’s Office (ICO) after a cyberattack that happened...
Guide: Protecting Your Digital Identity
Guide: Protecting Your Digital Identity People in their 20s and 30s are losing it online. And by it, I mean money—thanks to digital identity theft. In its simplest...
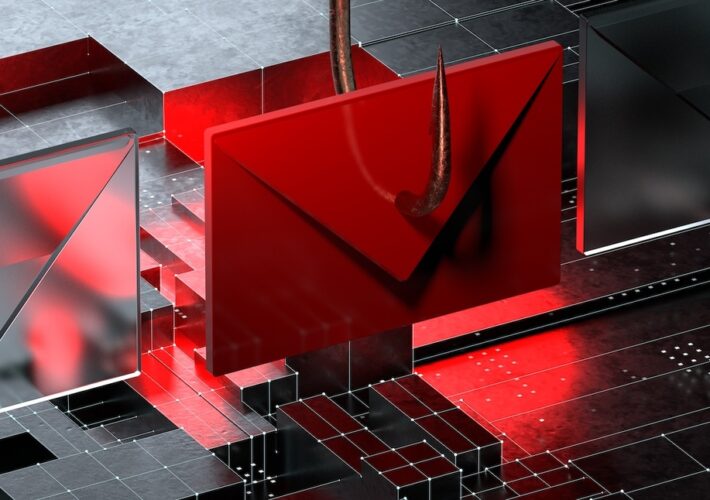
Secure corporate emails with intent-based BEC detection
Secure corporate emails with intent-based BEC detectionBusiness email compromise is a severe threat that might affect any company. One promising way to improve detection on this...
What Are Tailgating Attacks and How to Protect Yourself From Them
What Are Tailgating Attacks and How to Protect Yourself From Them Whether you’re spending time on the web or working in the office, you want peace...
What Is Smishing and Vishing, and How Do You Protect Yourself
What Is Smishing and Vishing, and How Do You Protect Yourself Smishing and vishing are scams where criminals attempt to get users to click a fraudulent...
How to Spot Fake Login Pages
How to Spot Fake Login Pages Have you ever come across a website that just didn’t look quite right? Perhaps the company logo looked slightly misshapen, or the...
Top Signs of Identity Theft
Top Signs of Identity Theft When it comes to identity theft, trust your gut when something doesn’t feel right. Follow up. What you’re seeing could be a problem. A missing bill or a mysterious charge on your...
Protect yourself from scams this Diwali
Protect yourself from scams this Diwali It’s Diwali, a time of light, a time of togetherness, and, of course, a time of celebration. Along with Diwali...
The most dangerous and destructive ransomware groups of 2022
The most dangerous and destructive ransomware groups of 2022As ransomware attacks continued this year, a few key groups inflicted some of the greatest damage to their...
Australia Increases Fines for Massive Data Breaches
Australia Increases Fines for Massive Data BreachesAfter suffering two large, and embarrassing, data breaches in recent weeks, the Australian government increased the fine for serious data...
Battle with Bots Prompts Mass Purge of Amazon, Apple Employee Accounts on LinkedIn
Battle with Bots Prompts Mass Purge of Amazon, Apple Employee Accounts on LinkedInOn October 10, 2022, there were 576,562 LinkedIn accounts that listed their current employer...
Tackling the Growing and Evolving Digital Attack Surface: 2022 Midyear Cybersecurity Report
Tackling the Growing and Evolving Digital Attack Surface: 2022 Midyear Cybersecurity ReportThis blog entry highlights the threats that dominated the first six months of the year,...
Ransomware Masquerading as Microsoft Update Targets Home Computers
Ransomware Masquerading as Microsoft Update Targets Home Computers A new ransomware threat is currently sweeping its way across home computers. And what’s making it extra tricky...
Staying safer online from phishing and other attacks
Staying safer online from phishing and other attacks When you’re online, the world is at your fingertips. You can do amazing things like stream the latest movies while they’re still...
Examining the Effects of Cyberattacks on Patient Care
Examining the Effects of Cyberattacks on Patient CareContenido de la entradaLeer másProofpoint News Feed
For some, accounting is more than just spreadsheets! Vernon’s McAfee Journey
For some, accounting is more than just spreadsheets! Vernon’s McAfee Journey Vernon has been our Manager of Technical Accounting for more than two years, but that...
This highly rated password manager is currently 93% off
This highly rated password manager is currently 93% offPassword Boss can store unlimited login details, with instant sync between devices. Get a lifetime subscription today for...
Google Pixel 7 and Pixel 7 Pro: The next evolution in mobile security
Google Pixel 7 and Pixel 7 Pro: The next evolution in mobile securityDave Kleidermacher, Jesse Seed, Brandon Barbello, Sherif Hanna, Eugene Liderman, Android, Pixel, and Silicon...
Security of Passkeys in the Google Password Manager
Security of Passkeys in the Google Password ManagerPosted by Arnar Birgisson, Software Engineer We are excited to announce passkey support on Android and Chrome for developers...
CISOs, Board Members and the Search for Cybersecurity Common Ground
CISOs, Board Members and the Search for Cybersecurity Common GroundContenido de la entradaLeer másProofpoint News Feed
Here’s how you can become a highly paid ethical hacker
Here’s how you can become a highly paid ethical hackerGet six training courses for just eight dollars each with The Complete 2022 PenTest & Ethical Hacking...
Massive Typosquatting Racket Pushes Malware at Windows, Android Users
Massive Typosquatting Racket Pushes Malware at Windows, Android UsersContenido de la entradaLeer másProofpoint News Feed
Single chip transfers the entire internet’s traffic in a second
Single chip transfers the entire internet’s traffic in a secondEXECUTIVE SUMMARY: A single chip has managed a transfer of over a petabit-per-second, according to new research...