Source: www.databreachtoday.com – Author: 1 Breach Notification , Critical Infrastructure Security , Cybercrime MGM Resorts Continuing to Be Extorted by the Same Alphv/BlackCat Ransomware Group Mathew...
Author:
Lessons to Learn From Clop’s MOVEit Supply-Chain Attacks – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 3rd Party Risk Management , Governance & Risk Management Data Minimization and Encryption Mitigate Fallout, Says FS-ISAC’s Teresa Walsh Mathew J....
Cloud to Blame for Almost all Security Vulnerabilities – Source: www.infosecurity-magazine.com
Source: www.infosecurity-magazine.com – Author: 1 Four out of five (80.3%) security vulnerabilities observed in organizations across all sectors come from a cloud environment, Palo Alto Networks’...
China’s Malicious Cyber Activity Informing War Preparations, Pentagon Says – Source: www.infosecurity-magazine.com
Source: www.infosecurity-magazine.com – Author: 1 China’s malicious cyber activity informs its preparations for a potential military conflict with the US, a new report from the Department...
Pirated Software Likely Cause of Airbus Breach – Source: www.infosecurity-magazine.com
Source: www.infosecurity-magazine.com – Author: 1 A major data breach at Airbus revealed earlier this week stemmed from a RedLine info-stealer likely hidden in a pirated copy...
Iranian Threat Group Hits Thousands With Password Spray Campaign – Source: www.infosecurity-magazine.com
Source: www.infosecurity-magazine.com – Author: 1 An Iranian state-backed APT group carried out a “wave” of cyber-espionage attacks against thousands of global targets over a six-month period,...
Caesars Entertainment Reveals Major Ransomware Breach – Source: www.infosecurity-magazine.com
Source: www.infosecurity-magazine.com – Author: 1 Yet another Nevadan casino and hotel chain giant has been compromised by ransomware threat actors, after Caesars Entertainment reported a serious...
How the U.S. Government Views the Bright, Dark Sides of AI – Source: www.govinfosecurity.com
Source: www.govinfosecurity.com – Author: 1 Artificial Intelligence & Machine Learning , Next-Generation Technologies & Secure Development White House, DOD, DHS Leaders Reveal How their Agencies Use...
Breach Roundup: Pegasus on Exiled Russian Journalist’s Phone – Source: www.govinfosecurity.com
Source: www.govinfosecurity.com – Author: 1 Also: 9-Year Prison Sentence for Insider Trading Fueled by Password Theft Anviksha More (AnvikshaMore) • September 14, 2023 Image:...
Panel | Secrets on the Loose: How to Get the Most out of Your Secrets Management Program – Source: www.govinfosecurity.com
Source: www.govinfosecurity.com – Author: 1 Robert Sawyer Sr. Director of Solutions Marketing, CyberArk Robert Sawyer is a software engineer turned marketing leader with over 20 years...
Live Fireside Chat | Getting Governance that Works – Source: www.govinfosecurity.com
Source: www.govinfosecurity.com – Author: 1 Thank you for registering with ISMG Complete your profile and stay up to date Need help registering? Contact Support Original Post...
China Denies Banning Government Use of Apple iPhones – Source: www.govinfosecurity.com
Source: www.govinfosecurity.com – Author: 1 Geo Focus: Asia , Geo-Specific , Government China Cites Apple Security Flaws in Warning to Foreign Mobile Device Manufacturers Jayant Chakravarti...
U.S. Senator Seeks Input on Ways to Protect Patient Privacy – Source: www.govinfosecurity.com
Source: www.govinfosecurity.com – Author: 1 Healthcare , HIPAA/HITECH , Industry Specific Inquiry is Latest Move by a Lawmaker Hinting of New Data Protection Legislation Marianne Kolbasuk...
Manchester Police Officers’ Data Breached in Third-Party Attack – Source: www.infosecurity-magazine.com
Source: www.infosecurity-magazine.com – Author: 1 Officers working undercover or in sensitive roles like intelligence could be exposed Original Post URL: https://www.infosecurity-magazine.com/news/manchester-police-data-breached/ Category & Tags: – Views:...
Elon Musk in Hot Water With FTC Over Twitter Privacy Issues – Source: www.infosecurity-magazine.com
Source: www.infosecurity-magazine.com – Author: 1 A new court filing from the US Department of Justice suggests the billionaire “may have jeopardized data privacy and security” at...
Lazarus Group Blamed For $53m Heist at CoinEx – Source: www.infosecurity-magazine.com
Source: www.infosecurity-magazine.com – Author: 1 North Korean actors have become prolific crypto-thieves Original Post URL: https://www.infosecurity-magazine.com/news/lazarus-group-blamed-53m-heist-at/ Category & Tags: – Views: 0
Wake-Up Call as 3AM Ransomware Variant Is Discovered – Source: www.infosecurity-magazine.com
Source: www.infosecurity-magazine.com – Author: 1 Symantec says it was used in a failed LockBit attack Original Post URL: https://www.infosecurity-magazine.com/news/3am-ransomware-variant-discovered/ Category & Tags: – Views: 1
Cloud Vulnerabilities Surge 200% in a Year – Source: www.infosecurity-magazine.com
Source: www.infosecurity-magazine.com – Author: 1 But IBM warns credential compromise is number one initial access vector Original Post URL: https://www.infosecurity-magazine.com/news/cloud-cves-surge-200-in-a-year/ Category & Tags: – Views: 0
How the U.S. Government Views the Bright, Dark Sides of AI – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 Artificial Intelligence & Machine Learning , Next-Generation Technologies & Secure Development White House, DOD, DHS Leaders Reveal How their Agencies Use...
Breach Roundup: Pegasus on Exiled Russian Journalist’s Phone – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 Also: 9-Year Prison Sentence for Insider Trading Fueled by Password Theft Anviksha More (AnvikshaMore) • September 14, 2023 Image:...
Panel | Secrets on the Loose: How to Get the Most out of Your Secrets Management Program – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 Robert Sawyer Sr. Director of Solutions Marketing, CyberArk Robert Sawyer is a software engineer turned marketing leader with over 20 years...
China Denies Banning Government Use of Apple iPhones – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 Geo Focus: Asia , Geo-Specific , Government China Cites Apple Security Flaws in Warning to Foreign Mobile Device Manufacturers Jayant Chakravarti...
U.S. Senator Seeks Input on Ways to Protect Patient Privacy – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 Healthcare , HIPAA/HITECH , Industry Specific Inquiry is Latest Move by a Lawmaker Hinting of New Data Protection Legislation Marianne Kolbasuk...
DOD Cyber Strategy Aims to Disrupt Hackers, Deepen Ally Work – Source: www.govinfosecurity.com
Source: www.govinfosecurity.com – Author: 1 Active Defense & Deception , Fraud Management & Cybercrime , Next-Generation Technologies & Secure Development Defense Department Will Conduct Defensive Ops...
Journey to the Cloud: Navigating the Transformation – Part 1 – Source: www.govinfosecurity.com
Source: www.govinfosecurity.com – Author: 1 Cloud Security , Security Operations Nikko Asset Management’s Marcus Rameke Defines the Requirements CyberEdBoard • September 13, 2023 Marcus,...
Chinese APT41 Implicated in Asian National Power Grid Hack – Source: www.govinfosecurity.com
Source: www.govinfosecurity.com – Author: 1 Critical Infrastructure Security , Cyberwarfare / Nation-State Attacks , Fraud Management & Cybercrime Symantec Finds APT41 Fingerprint in a ShadowPad Trojan...
Microsoft Patches Fix Word and Streaming Services Zero-Days – Source: www.govinfosecurity.com
Source: www.govinfosecurity.com – Author: 1 Governance & Risk Management , Patch Management Patch Contains 59 Bugs Fixes, Including 5 Critical Ones Mihir Bagwe (MihirBagwe) • September...
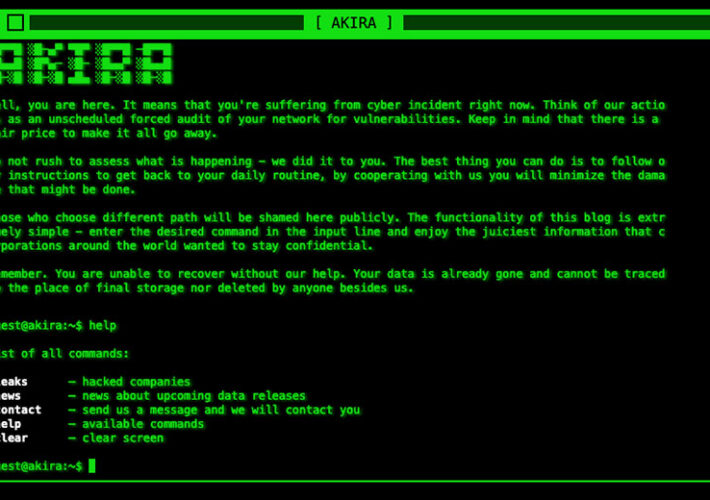
Feds Warn Healthcare Sector of Akira Ransomware Threats – Source: www.govinfosecurity.com
Source: www.govinfosecurity.com – Author: 1 Fraud Management & Cybercrime , Governance & Risk Management , Healthcare HHS: Group Seems to Favor Targeting Small & Midsized Entities...
New Microsoft Teams Phishing Campaign Targets Corporate Employees – Source: www.infosecurity-magazine.com
Source: www.infosecurity-magazine.com – Author: 1 Microsoft has detailed a new phishing campaign in which corporate employees are targeted via MS Teams. The tech giant said the...
MGM Criticized for Repeated Security Failures – Source: www.infosecurity-magazine.com
Source: www.infosecurity-magazine.com – Author: 1 As the dust settles for MGM and systems are restored following a suspected cyber-attack, cybersecurity experts are now scrutinizing the hospitality...