Source: www.govinfosecurity.com – Author: 1 Governance & Risk Management , Patch Management Expert Warns of Maximum-Severity Flaw ‘You Need to Patch Right Now!’ Prajeet Nair (@prajeetspeaks)...
Author:
Data Theft Overtakes Ransomware as Top Concern for IT Decision Makers – Source: www.infosecurity-magazine.com
Source: www.infosecurity-magazine.com – Author: 1 Data theft is a primary concern for IT decision makers, ahead of ransomware attacks, according to a survey conducted by Integrity...
Hackers Impersonate Meta Recruiter to Target Aerospace Firm – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 Cyberwarfare / Nation-State Attacks , Fraud Management & Cybercrime , Social Engineering Lazarus Deploys New Backdoor to Target Aerospace Firm Prajeet...
Hackers Impersonate Meta Recruiter to Target Aerospace Firm – Source: www.govinfosecurity.com
Source: www.govinfosecurity.com – Author: 1 Cyberwarfare / Nation-State Attacks , Fraud Management & Cybercrime , Social Engineering Lazarus Deploys New Backdoor to Target Aerospace Firm Vasudevan...
Vulns Found In Another Progress Software File Transfer App – Source: www.govinfosecurity.com
Source: www.govinfosecurity.com – Author: 1 Governance & Risk Management , Patch Management ‘There’s a 10-out-10 severity bug you need to patch right now!’ Prajeet Nair (@prajeetspeaks)...
Inside Look: FDA’s Cyber Review Process for Medical Devices – Source: www.govinfosecurity.com
Source: www.govinfosecurity.com – Author: 1 Endpoint Security , Hardware / Chip-level Security , Healthcare Jessica Wilkerson of the FDA Details Agency’s ‘Refuse to Accept’ Policy and...
CrowdStrike Boosts Israeli Startup Ties With AWS Partnership – Source: www.govinfosecurity.com
Source: www.govinfosecurity.com – Author: 1 Next-Generation Technologies & Secure Development AWS & CrowdStrike Cybersecurity Startup Accelerator Will Incubate Early-Stage Firms Michael Novinson (MichaelNovinson) • September 29,...
Editors’ Panel: What Impact Will Cisco’s Splunk Acquisition Have on Industry? – Source: www.govinfosecurity.com
Source: www.govinfosecurity.com – Author: 1 Governance & Risk Management , Operational Technology (OT) , Security Information & Event Management (SIEM) Also: OT Security Trends, Challenges; FDA...
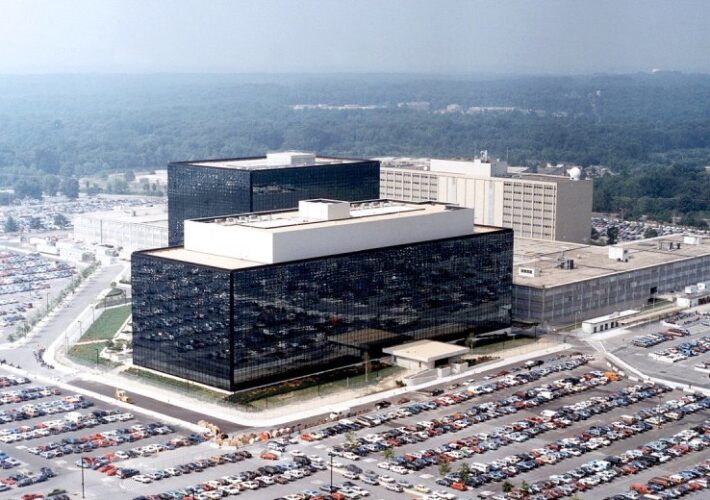
NSA Stands Up New Organization to Harness AI – Source: www.govinfosecurity.com
Source: www.govinfosecurity.com – Author: 1 Artificial Intelligence & Machine Learning , Next-Generation Technologies & Secure Development A US Advantage on AI Should ‘Not Be Taken For...
Vulns Found In Another Progress Software File Transfer App – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 Governance & Risk Management , Patch Management ‘There’s a 10-out-10 severity bug you need to patch right now!’ Prajeet Nair (@prajeetspeaks)...
Inside Look: FDA’s Cyber Review Process for Medical Devices – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 Endpoint Security , Hardware / Chip-level Security , Healthcare Jessica Wilkerson of the FDA Details Agency’s ‘Refuse to Accept’ Policy and...
CrowdStrike Boosts Israeli Startup Ties With AWS Partnership – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 Next-Generation Technologies & Secure Development AWS & CrowdStrike Cybersecurity Startup Accelerator Will Incubate Early-Stage Firms Michael Novinson (MichaelNovinson) • September 29,...
Editors’ Panel: What Impact Will Cisco’s Splunk Acquisition Have on Industry? – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 Governance & Risk Management , Operational Technology (OT) , Security Information & Event Management (SIEM) Also: OT Security Trends, Challenges; FDA...
NSA Stands Up New Organization to Harness AI – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 Artificial Intelligence & Machine Learning , Next-Generation Technologies & Secure Development A US Advantage on AI Should ‘Not Be Taken For...
Russian Company Offers $20m For Non-NATO Mobile Exploits – Source: www.infosecurity-magazine.com
Source: www.infosecurity-magazine.com – Author: 1 The Russian firm Operation Zero has announced a staggering $20m reward for hacking tools capable of compromising iPhones and Android devices. ...
Microsoft’s Bing AI Faces Malware Threat From Deceptive Ads – Source: www.infosecurity-magazine.com
Source: www.infosecurity-magazine.com – Author: 1 Microsoft’s Bing Chat has come under scrutiny due to a significant security concern – the infiltration of malicious ads. Malwarebytes researchers...
Phishing, Smishing Surge Targets US Postal Service – Source: www.infosecurity-magazine.com
Source: www.infosecurity-magazine.com – Author: 1 Recent weeks have witnessed a significant increase in cyber-attacks targeting the US Postal Service (USPS), mainly through phishing and smishing campaigns. ...
Chrome Patches 0-Day Exploited by Commercial Spyware Vendor – Source: www.govinfosecurity.com
Source: www.govinfosecurity.com – Author: 1 Governance & Risk Management , Patch Management Limited Details Disclosed but Google said it is a Heap-based Buffer Overflow Bug Mihir...
Zero Trust, Auditability and Identity Governance – Source: www.govinfosecurity.com
Source: www.govinfosecurity.com – Author: 1 Two years after President Biden’s landmark cybersecurity Executive Order, the question remains: How are federal agencies adapting to the new focus...
Study Reveals Conti Affiliates Money Laundering Practices – Source: www.govinfosecurity.com
Source: www.govinfosecurity.com – Author: 1 Cryptocurrency Fraud , Fraud Management & Cybercrime , Ransomware Affiliates Relied on Less Complex, Trackable Methods, It Says Akshaya Asokan (asokan_akshaya)...
Infusion Firm Faces Lawsuit After Hackers Hit Parent Company – Source: www.govinfosecurity.com
Source: www.govinfosecurity.com – Author: 1 Cybercrime , Fraud Management & Cybercrime , Governance & Risk Management Proposed Class Action Claim Against Amerita Linked to Larger PharMerica...
Nord Security Raises $100M on $3B Valuation to Go After M&A – Source: www.govinfosecurity.com
Source: www.govinfosecurity.com – Author: 1 Security Operations , Web Application Firewalls (WAF) VPN Service Behemoth Doubles Valuation In Just 17 Months Despite Economic Headwinds Michael Novinson...
Privacy Regulator Orders End to Spreadsheet FOI Responses – Source: www.infosecurity-magazine.com
Source: www.infosecurity-magazine.com – Author: 1 The UK’s information commissioner has called for an immediate end to the use of excel spreadsheets to publish Freedom of Information (FOI)...
Microsoft Breach Exposed 60,000 State Department Emails – Source: www.infosecurity-magazine.com
Source: www.infosecurity-magazine.com – Author: 1 A sophisticated Chinese cyber-espionage campaign targeting Microsoft Outlook accounts gave Beijing access to tens of thousands of private US government emails,...
MOVEit Developer Patches Critical File Transfer Bugs – Source: www.infosecurity-magazine.com
Source: www.infosecurity-magazine.com – Author: 1 Progress Software has urged customers to patch a critical new vulnerability in one of its flagship file transfer software products, which...
Chrome Patches 0-Day Exploited by Commercial Spyware Vendor – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 Governance & Risk Management , Patch Management Limited Details Disclosed but Google said it is a Heap-based Buffer Overflow Bug Mihir...
Study Reveals Conti Affiliates Money Laundering Practices – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 Cryptocurrency Fraud , Fraud Management & Cybercrime , Ransomware Affiliates Relied on Less Complex, Trackable Methods, It Says Anviksha More (AnvikshaMore)...
Infusion Firm Faces Lawsuit After Hackers Hit Parent Company – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 Cybercrime , Fraud Management & Cybercrime , Governance & Risk Management Proposed Class Action Claim Against Amerita Linked to Larger PharMerica...
Nord Security Raises $100M on $3B Valuation to Go After M&A – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 Security Operations , Web Application Firewalls (WAF) VPN Service Behemoth Doubles Valuation In Just 17 Months Despite Economic Headwinds Michael Novinson...
Budworm APT Evolves Toolset, Targets Telecoms and Government – Source: www.infosecurity-magazine.com
Source: www.infosecurity-magazine.com – Author: 1 The Budworm advanced persistent threat (APT) group, also known as LuckyMouse, Emissary Panda or APT27, has once again demonstrated its active development...