Governance & Risk Management , Healthcare , HIPAA/HITECH Proposed Rule Would Prohibit Certain PHI Disclosures, Uses for Law Enforcement Marianne Kolbasuk McGee (HealthInfoSec) • April 12,...
Author:
Will Generative AI’s Use in Cyber Tools Exceed Expectations?
Artificial Intelligence & Machine Learning , Cloud Security , Next-Generation Technologies & Secure Development To What Extent Will Security Tools Benefit From Linking Arms With OpenAI’s...
Researchers Uncover 7000 Malicious Open Source Packages
Security vendor Sonatype detected 6933 malicious open source packages in the month of March alone, bringing the total discovered since 2019 to 115,165. Info-stealers comprised a...
New Zero-Click iOS Exploit Deploys Israeli Spyware
Security researchers have discovered a new zero-click, zero-day exploit that targeted iPhone users in 2021 with commercial spyware produced by secretive Israeli firm QuaDream. Microsoft and...
Ethical Hackers Could Earn up to $20,000 Uncovering ChatGPT Vulnerabilities
OpenAI is offering white hat hackers up to $20,000 to find security flaws as part of its bug bounty program launched on April 11, 2023. The...
Microsoft Fixes Zero-Day Bug This Patch Tuesday
Microsoft’s Patch Tuesday release this month included a security update for a Windows zero-day vulnerability being actively exploited in the wild. The bug in question, CVE-2023-28252,...
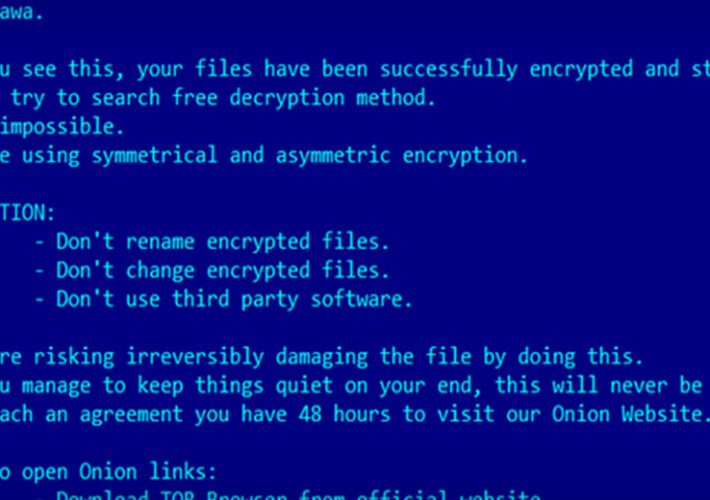
Microsoft Patches Zero-Day Bug Exploited by Ransomware Group
Application Security , Attack Surface Management , Cybercrime Attackers Drop Nokoyawa Ransomware; Experts See Increasing Criminal Sophistication Mihir Bagwe (MihirBagwe) , Mathew J. Schwartz (euroinfosec) •...
Cybercrime: Ransomware Hits and Initial Access Listings Grow
Cybercrime , Fraud Management & Cybercrime , Ransomware But If Hydra Takedown Is a Guide, Fresh Disruptions May Take Big Bite Out of Market Mathew J....
Latitude Financial Refuses to Pay Ransom
Fraud Management & Cybercrime , Geo Focus: Australia , Geo-Specific Ongoing Cyberattack Still Causing Service Disruptions Prajeet Nair (@prajeetspeaks) • April 11, 2023 A...
Proposed Health IT Certification Rules Target AI, Privacy
Healthcare , HIPAA/HITECH , Industry Specific HHS Rules Aimed at Beefing Up Health IT Systems, Patient Data Privacy, Security Marianne Kolbasuk McGee (HealthInfoSec) • April 11,...
Feds Call For Certifying, Assessing Veracity of AI Systems
Artificial Intelligence & Machine Learning , Next-Generation Technologies & Secure Development , Standards, Regulations & Compliance Biden Administration Wants to Ensure AI Tech Works as Intended...
US Scrambles to Investigate Military Intel Leak
Pentagon officials are reportedly racing to identify the source of a leak of military intelligence, which could disrupt Ukraine’s planned spring offensive against Russian troops. Scores...
KFC Owner Discloses Data Breach
A leading US fast food company has been sending out breach notification letters to individuals impacted by a ransomware incident that occurred in January. Yum Brands...
Latitude Financial Refuses to Pay Ransom
A leading Australian lender has refused to pay online extorters demanding a ransom for the personal data they stole on an estimated 14 million customers. Latitude...
White House Probes Classified Intelligence ‘Discord Leaks’
Critical Infrastructure Security , Government , Industry Specific Leaks Likely as Significant as Snowden Files, Vault 7, Shadow Brokers, Expert Says Mathew J. Schwartz (euroinfosec) •...
How Much Damage Would US Action Against Kaspersky Inflict?
Cyberwarfare / Nation-State Attacks , Endpoint Security , Fraud Management & Cybercrime Enforcement Action Could Deal Fatal Blow to Kaspersky’s North American Business Michael Novinson (MichaelNovinson)...
(Plenary) How to Win Cyberwars With Military Strategies and Techniques
Thank you for registering with ISMG Complete your profile and stay up to date Need help registering? Contact Support
Live Webinar | Understanding 3rd Party App Risk to Google Workspace Data
Nick Harrahill Director of Support, Spin.AI Nick Harrahill is an experienced cyber security and business leader who is Director of Support at Spin.AI. Nick’s industry experience...
Expert Insights: Safeguarding Your Hybrid Workforce with 5 Key SOC Best Practices
Eric Howard Cisco Global Technical Marketing Engineer Eric Howard is a Technical Leader for Cisco’s Threat Intelligence, Detection and Response product team. He leads a team...
ENISA: Software vulnerability prevention initiatives
From heightened risks to increased regulations, senior leaders at all levels are pressured to improve their organizations’ risk management capabilities. But no one is showing them...
Accounting of Disclosures Under the HITECH Act
From heightened risks to increased regulations, senior leaders at all levels are pressured to improve their organizations’ risk management capabilities. But no one is showing them...
FFIEC Final Authentication Guidance
From heightened risks to increased regulations, senior leaders at all levels are pressured to improve their organizations’ risk management capabilities. But no one is showing them...
Annual Report to Congress on Breaches of Unsecured Protected Health Information
From heightened risks to increased regulations, senior leaders at all levels are pressured to improve their organizations’ risk management capabilities. But no one is showing them...
Microsoft Gets Court Order to Sinkhole Cobalt Strike Traffic
Fraud Management & Cybercrime , Healthcare , Industry Specific Order Affects Malicious Domains, Server IP Addresses Hosted by US Data Centers David Perera (@daveperera) • April...
Apple Issues Emergency Fix for Spyware-Style Zero Days
Cybercrime , Endpoint Security , Fraud Management & Cybercrime Apple Recommends Immediate Updating Due to Extensive List of Affected Devices Prajeet Nair (@prajeetspeaks) • April 8,...
EMEA Webinar | What You Don’t Know Can Hurt You: Open Source License Compliance and M&A Activity
Sam Quakenbush Senior Director – Field Innovation & Strategy, Mend Sam Quakenbush has spent the past 10 years working for cyber security companies covering various domains...
Just Who Exactly Should Take Responsibility for Application Security?
Application Security & Online Fraud , Fraud Management & Cybercrime , Security Operations Carol Hilderbrand • March 23, 2023 Recent high-profile software supply chain...
Look Beyond TikTok: Massive Data Collection Is the Real Risk
Fraud Management & Cybercrime , Social Media All Social Media Apps Collect Information on a Scale That Facilitates Surveillance Mathew J. Schwartz (euroinfosec) • March 29,...
Law Enforcement Lures Cybercriminals With Fake DDoS Services
Cybercrime , DDoS Protection , Fraud Management & Cybercrime ‘We’re Running Stresser/Booter Distributed Denial-of-Service Sites,’ Cops Caution Mathew J. Schwartz (euroinfosec) • April 6, 2023 ...
The Persisting Risks Posed by Legacy Medical Devices
Recently enacted U.S. legislation requiring vendors to design cybersecurity into medical devices is a good first step, but healthcare delivery organizations for many years to come...