The leading community for cybersecurity executives
Where Cybersecurity Leaders Shape the Future of AI Security
Connect. Exchange. Lead. Join senior cybersecurity executives sharing real-world insight, navigating emerging risk and building a more resilient digital future.
10 pillars · 3 Hubs · one place
190K+
Cybersecurity Professionals
70+
Countries Worldwide
15+
Years of Trust & Impact
10K+
Curated Resources & Frameworks
150+
Events & Webinars Annually
500+
Executive Discussions Monthly
Intelligence Hubs
Security Intelligence Maps
Interactive capability maps with vendor coverage and executive frameworks
AI Security
AI Security Intelligence Map
9 domains · 54 capabilities · 79 vendors
OT Security
OT Security Intelligence Map
9 domains · 45 capabilities · 42 vendors
Cloud Security
Cloud Security Intelligence Map
9 domains · 45 capabilities · 60+ vendors
Identity Security
Identity Security Intelligence Map
9 domains · 45 capabilities · 50+ vendors
Zero Trust
Zero Trust Intelligence Map
9 domains · 45 capabilities · 50 vendors
Endpoint Security
Endpoint Security Intelligence Map
9 domains · 45 capabilities · 50+ vendors
SASE
SASE Intelligence Map
9 domains · 45 capabilities · 55 vendors
Data Security
Data Security Intelligence Map
9 domains · 45 capabilities · 50+ vendors
API Security
API Security Intelligence Map
9 domains · 45 capabilities · 45 vendors
Executive Cyber Intelligence
What cyber leaders are reading
Curated intelligence for security executives and board-level decisions
Featured Executive Insight
The Future Cyber Workforce Problem Nobody Is Solving
The cybersecurity industry is focused on how AI will reduce the demand for repetitive security work. Almost nobody is focused on the downstream consequence — that removing the repetitive work also removes the learning environment through which most security expertise has historically been developed.
Read article →Cyber Operations
AI-driven SOC transformation
How AI is reshaping detection, triage and managed security operations.
Board Risk
Cyber resilience replacing maturity metrics
Boards want resilience outcomes, not compliance scoring.
AI Security
Prompt security is becoming operational
Organizations moving from theory into practical AI control implementation.
Third-party Risk
Dependency concentration concerns rising
CISOs reassessing cloud and SaaS concentration exposure.
 Strategy
StrategyBoard Strategy
The Hardest Question a CISO Faces: Could This Happen to Us?
 Trust
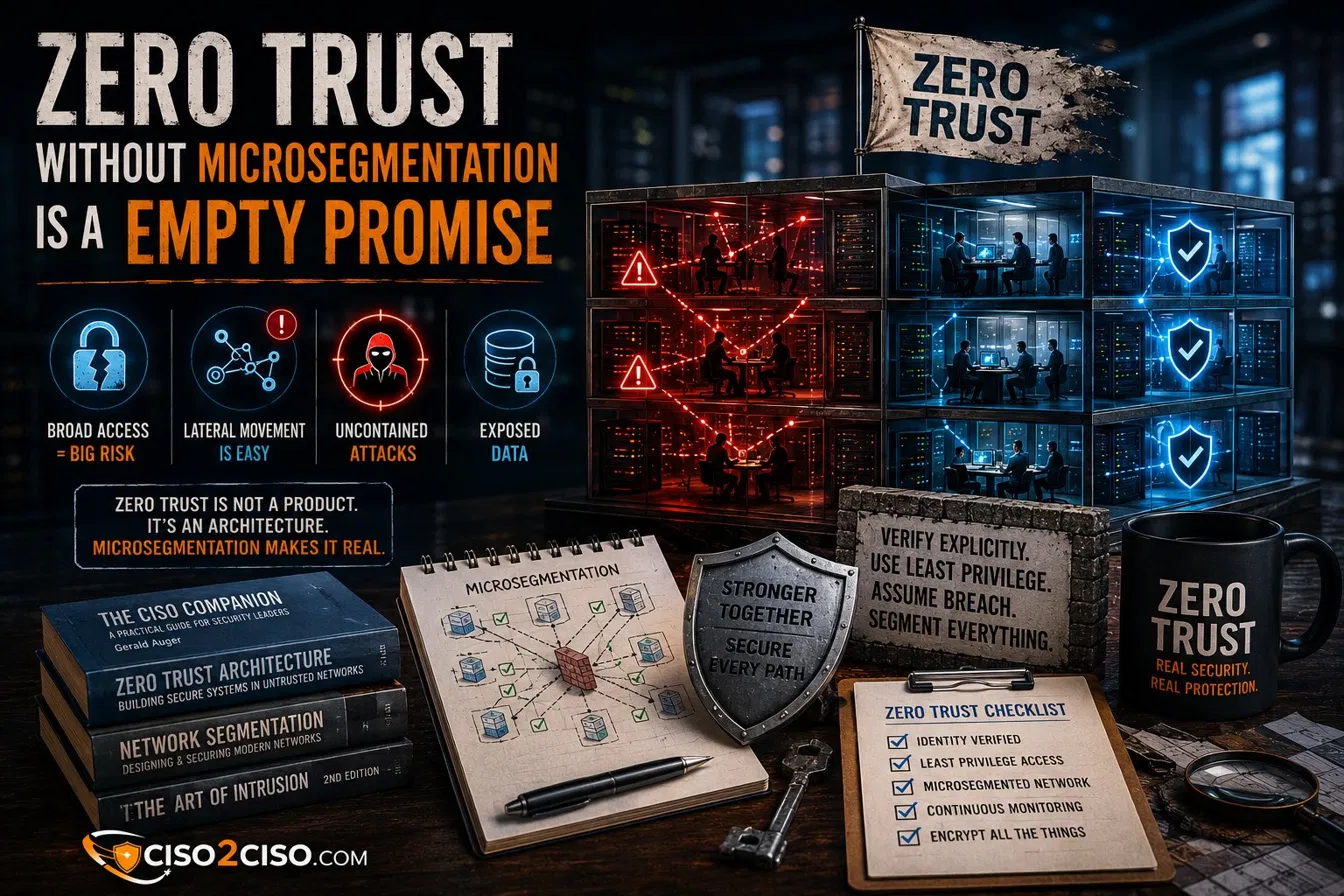
TrustZero Trust
Without Microsegmentation, Zero Trust Is an Empty Promise
 Risk
RiskCyber Risk
Geopolitical Risk Has Become a Cybersecurity Problem
 Strategy
StrategyBoard Strategy
If You Cannot Measure It, You Cannot Govern It
 Risk
RiskCyber Risk
M&A Due Diligence Has a Cyber Problem
 Risk
RiskCyber Risk
Security Debt Is the Risk Nobody Wants to Talk About
 Strategy
StrategyBoard Strategy
The CISO Is No Longer a Technical Role
 Security
SecurityCloud Security
The Cloud Shared Responsibility Model Has a Gap — And It Is Yours
Featured Strategic Publications
Selected editorial series
 AI Security Controls
AI Security ControlsAI Security
AI Security Is Moving from Frameworks to Operating Models
CISOs are shifting AI security from theoretical controls into implementable ecosystems across models, data, agents, applications and governance. The question is no longer whether controls exist — it is whether they are operational, owned and evidenced.
 OT Security Resilience
OT Security ResilienceOT Security
OT Security Is Becoming an Enterprise Resilience Challenge
IT/OT convergence is transforming industrial security from a plant-level protection problem into a strategic business continuity issue. OT incidents now carry consequences that reach far beyond the plant floor — into production, safety, supply chain and regulatory liability.
 Secure AI Engineering
Secure AI EngineeringAI Security
Vibe Coding Accelerates Prototypes — But Production Requires Security Architecture
AI-assisted development is accelerating delivery across enterprise teams. The risk is not the technology — it is the false production maturity that occurs when prototypes move into enterprise environments without the security architecture that production requires.
Live Executive Signals
This week's intelligence
AI Security
The Hacker News
Attackers Use LLM Agent for Post-Exploitation After Marimo CVE-2026-39987 Exploit
Cloud Governance
Microsoft Security
Typosquatted npm packages used to steal cloud and CI/CD secrets
AI Security
CSO Online
DNS-AID will make AI agents easier to discover, says Linux Foundation
Editorial Library
More executive reads
 Operations
OperationsSecurity Operations
The Death of the Traditional SOC?
 Trust
TrustZero Trust
Identity Is the New Enterprise Perimeter
 Security
SecurityAI Security
AI Security Is Moving from Frameworks to Operating Models
 Security
SecurityAI Security
The Rise of Agentic Attack Surfaces
 Security
SecurityOT Security
OT Security Is Becoming a Board-Level Issue
 Strategy
StrategyBoard Strategy
The New Cyber Risk Conversation with Boards
 Security
SecurityAI Security
The Rise of AI-Augmented Cyber Operations
 Strategy
StrategyBoard Strategy
Executive Lessons from Recent Ransomware Cases
The Power of Community
Stronger Together.
Safer Together.
Connect with global CISO peers, share real-world insights and stay ahead of emerging threats. 190K+ professionals worldwide.
Curated Sessions
Upcoming Events
AI Security Leaders Roundtable
Building Guardrails for AI at Scale
Virtual · 12:00 PM ET
Board Cyber Risk Briefing
AI Risk, Compliance & Governance
Virtual · 1:00 PM ET
OT Security Executive Workshop
Hands-on Controls & Patterns
Virtual · 10:00 AM ET
Private Briefings
Executive-level conversations designed for CISOs, security leaders and cyber risk decision-makers.
Intelligence Sources
Trusted external references
CISA
Advisories & alerts
Mandiant
Threat intelligence
Microsoft
Security research
Dark Reading
Breaking news
CSO Online
Enterprise risk
CrowdStrike
Threat research
SecurityWeek
Cyber news
The Record
Policy & crime
BleepingComputer
Vulnerabilities
Palo Alto U42
Cloud & incidents
NSA Cyber
Hardening guides
Cybersecurity Dive
Strategy & risk
SANS ISC
Technical alerts
Krebs on Security
Investigative
ENISA
EU cyber policy