Source: securityaffairs.com – Author: Pierluigi Paganini.
Print management software provider PaperCut confirmed ongoing active exploitation of CVE-2023-27350 vulnerability.
On April 19th, Print management software provider PaperCut confirmed that it is aware of the active exploitation of the CVE-2023-27350 vulnerability.
The company received two vulnerability reports from the cybersecurity firm Trend Micro for high/critical severity security issues in PaperCut MF/NG.
Trend Micro announced they will disclose further information (TBD) about the vulnerability on 10th May 2023.
The company addressed both vulnerabilities with the release of PaperCut MF and PaperCut NG versions 20.1.7, 21.2.11 and 22.0.9 and later, it highly recommends upgrading to one of these versions containing the fix
“We have evidence to suggest that unpatched servers are being exploited in the wild.” reads the advisory published by PaperCut. “PaperCut received our first report from a customer of suspicious activity on their PaperCut server on the 18th April at 03:30 AEST / 17th April 17:30 UTC. PaperCut has conducted analysis on all customer reports, and the earliest signature of suspicious activity on a customer server potentially linked to this vulnerability is 14th April 01:29 AEST / 13th April 15:29 UTC.”
The CVE-2023-27350 (CVSS score – 9.8) is a PaperCut MF/NG Improper Access Control Vulnerability. PaperCut MF/NG contains an improper access control vulnerability within the SetupCompleted class that allows authentication bypass and code execution in the context of system.
Last week, the U.S. Cybersecurity and Infrastructure Security Agency (CISA) added it to its Known Exploited Vulnerabilities Catalog.
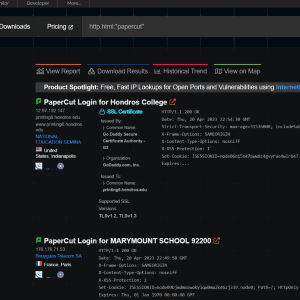
Huntress researchers have observed post-exploitation activities within its partner environments after attackers exploited the above PaperCut MF/NG vulnerabilities.
Huntress security researcher Caleb Stewart also devised a proof-of-concept exploit for these threats, below is the video PoC shared by the company:
“From our recreated proof-of-concept, we observed child processes spawned underneath the pc-app.exe process. The screenshot below showcases a simple test of invoking PowerShell to call out to another location, demonstrating the achieved code execution.” reads the report published by Huntress.”
The researchers noticed that the domain hosting the tools employed in the attack, windowservicecemter[.]com, was registered on April 12, 2023. It is interesting to note that the domain was also hosting malware a variant of the TrueBot malware.
Truebot has been active since 2017 and some researchers linked it to the Russian Silence Group, while a recent investigation linked it to threat actor TA505 (aka Evil Corp).
“While the ultimate goal of the current activity leveraging PaperCut’s software is unknown, these links (albeit somewhat circumstantial) to a known ransomware entity are concerning. Potentially, the access gained through PaperCut exploitation could be used as a foothold leading to follow-on movement within the victim network, and ultimately ransomware deployment.” concludes the report published by Huntress.
Please vote for Security Affairs (https://securityaffairs.com/) as the best European Cybersecurity Blogger Awards 2022 – VOTE FOR YOUR WINNERS
Vote for me in the sections:
- The Teacher – Most Educational Blog
- The Entertainer – Most Entertaining Blog
- The Tech Whizz – Best Technical Blog
- Best Social Media Account to Follow (@securityaffairs)
Please nominate Security Affairs as your favorite blog.
Nominate here: https://docs.google.com/forms/d/e/1FAIpQLSfaFMkrMlrLhOBsRPKdv56Y4HgC88Bcji4V7OCxCm_OmyPoLw/viewform
Follow me on Twitter: @securityaffairs and Facebook and Mastodon
(SecurityAffairs – hacking, PaperCut)
Original Post URL: https://securityaffairs.com/145190/hacking/russian-hackers-papercut-flaws-attacks.html
Category & Tags: Breaking News,Hacking,Security,hacking news,IT Information Security,PaperCut,Pierluigi Paganini,Security Affairs,Security News – Breaking News,Hacking,Security,hacking news,IT Information Security,PaperCut,Pierluigi Paganini,Security Affairs,Security News
Views: 1