Source: www.bleepingcomputer.com – Author: Bill Toulas

The Australian, US, and UK governments have announced sanctions for Aleksandr Gennadievich Ermakov, a Russian national considered responsible for the 2022 Medibank hack and a member of the REvil ransomware group.
Medibank is a large health insurance provider in Australia that suffered a ransomware attack in October 2022, causing operational and business disruption.
Following an internal investigation, it was determined that hackers had accessed troves of customers’ personal data. In early November 2022, the attacker leaked stolen data for approximately 10 million people.
The leaked data included names, email addresses, phone numbers, physical addresses, passport numbers, health claims information, and health provider details.
Following a lengthy investigation, the Australian authorities identified Ermakov as the person responsible for the Medibank hack and data theft. Authorities also associated multiple online aliases with Ermakov and published photos of the individual.
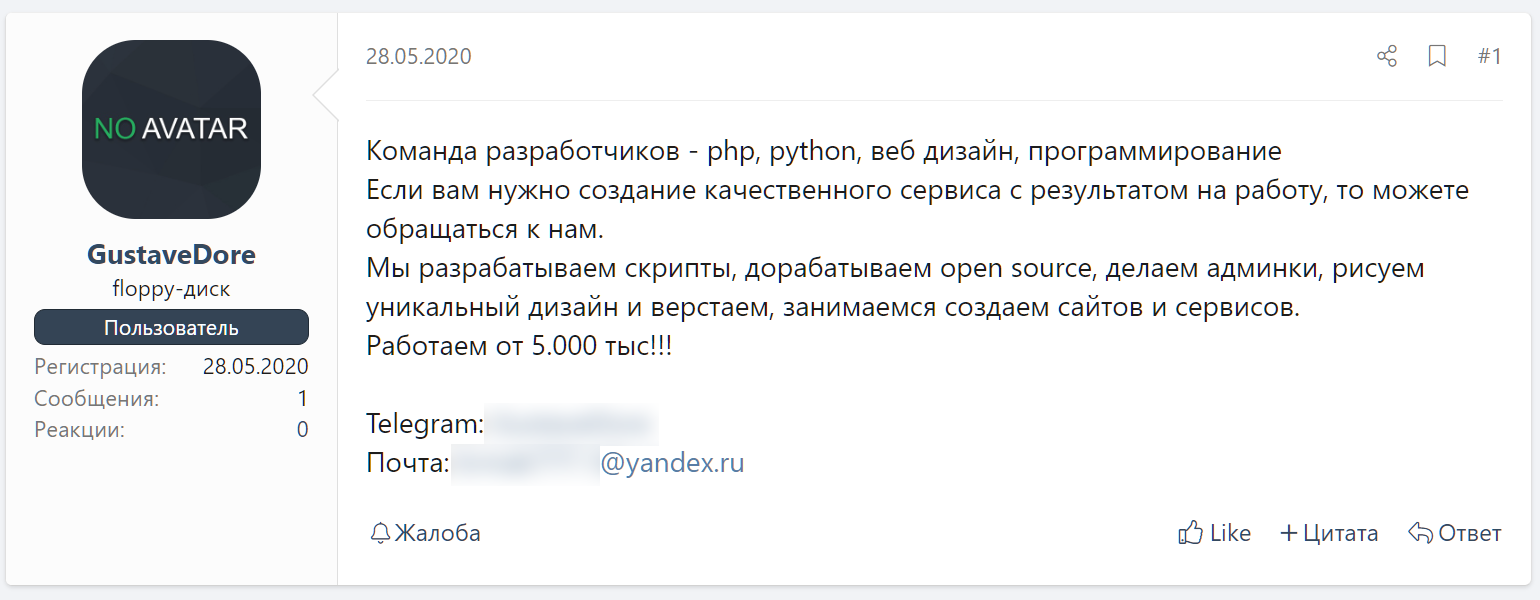
According to the latest amendment of the Autonomous Sanctions document (version F2024L00099), Ermakov used multiple aliases, including GustaveDore, aiiis_ermak, blade_runner, and JimJone.
The United States and United Kingdom also announced sanctions against Ermakov in a coordinated announcement with Australia.
“Russian cyber actors continue to wage disruptive ransomware attacks against the United States and allied countries, targeting our businesses, including critical infrastructure, to steal sensitive data,” said Under Secretary of the Treasury Brian E. Nelson.
“Today’s trilateral action with Australia and the United Kingdom, the first such coordinated action, underscores our collective resolve to hold these criminals to account.”
While not much is known about Ermakov, BleepingComputer found someone using the threat actor’s ‘GustaveDore’ alias to post on the Russian-speaking XSS hacking forum and offering PHP development services.
Responsible for the most damaging cyberattack in Australia’s history, as local media characterized it, was a ransomware gang called ‘BlogXXX‘ who claimed the attack on Medibank.
However, BlogXXX is believed to be a short-lived relaunch of the REvil operation that had shut down in October 2021 amidst unusually publicized arrests by the Russian government.
In a press conference at Canberra, Australia’s Home Affairs and Cyber Security Minister confirmed that Ermakov was a member of the REvil ransomware operation and he was not among the individuals that Russia detained in early 2022 under suspicion of being members of the REvil group.
Although Ermakov may not care about the sanctions or find ways to evade them, his illegal activity is likely to feel the effect of these restrictions. The Head of the Australian Cyber Security Centre, Abigail Bradshaw, explains that “cyber criminals trade in anonymity.”
By naming him, Ermakov can no longer operate unrestricted. His identity is now known not only to “every agency around the world but also anybody who is seeking to operate with him,” Australia’s Deputity Prime Minister said at the conference.
As the sanctions in response to the Medibank Private cyber incident have a financial component, this means that whoever provides assets to Ermakov, including cryptocurrency or ransomware payments, would be committing an offense.
The Australian government believes that this is sufficient to deter others from associating with Ermakov for financial gains, be they legal or not.
Original Post URL: https://www.bleepingcomputer.com/news/security/us-uk-australia-sanction-revil-hacker-behind-medibank-data-breach/
Category & Tags: Security,Legal – Security,Legal
Views: 0




















































