Source: www.databreachtoday.com – Author: 1 Cybercrime , Fraud Management & Cybercrime 400 Potential WeLeakInfo Patrons Warned of Legal Costs of Criminal Wrongdoing Akshaya Asokan (asokan_akshaya) •...
Month: September 2023
Cryptohack Roundup: Private Key Compromise Led to CoinEx Hit – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 Blockchain & Cryptocurrency , Cryptocurrency Fraud , Fraud Management & Cybercrime Also: Mark Cuban Hot Wallet Hack; Crypto Regulation Mihir Bagwe...
Ohio Community College Data Theft Breach Affects Nearly 300K – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 Fraud Management & Cybercrime , Government , Healthcare Researchers Say Breach Illustrates Why Schools Are Major Targets for Cybercriminals Marianne Kolbasuk...
Intel Innovation 2023: Attestation and Fully Homomorphic Encryption Coming to Intel Cloud Services – Source: www.techrepublic.com
Source: www.techrepublic.com – Author: Megan Crouse The attestation service is designed to allow data in confidential computing environments to interact with AI safely, as well as...
Top 5 Ways to Secure Work Data on Your Personal Mac – Source: www.techrepublic.com
Source: www.techrepublic.com – Author: Mackenzie Burke Top 5 Ways to Secure Work Data on Your Personal Mac About Top 5 Ways to Secure Work Data on...
Retailers Are Rapidly Scaling Surveillance of Australian Consumers — Why This Is a Red Flag – Source: www.techrepublic.com
Source: www.techrepublic.com – Author: Matthew Sainsbury IT professionals across sectors that interact with consumers, and retail in particular, need to make themselves aware of the implications...
SSL Certificate Best Practices Policy – Source: www.techrepublic.com
Source: www.techrepublic.com – Author: SSL certificates are essential for encrypting traffic between systems such as clients, which access servers via web browsers or applications that communicate...
Computer Security Incident Response Team (CSIRT): How to Build One – Source: heimdalsecurity.com
Source: heimdalsecurity.com – Author: Andreea Chebac According to the World Economic Forum, “widespread cybercrime and cyber insecurity” is rated as one of the greatest worldwide dangers...
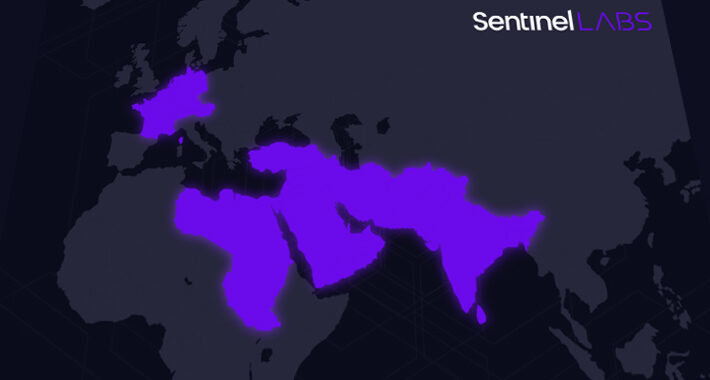
Mysterious ‘Sandman’ Threat Actor Targets Telecom Providers Across Three Continents – Source:thehackernews.com
Source: thehackernews.com – Author: . Sep 21, 2023THNTelecom Security / Cyber Attack A previously undocumented threat actor dubbed Sandman has been attributed to a set of...
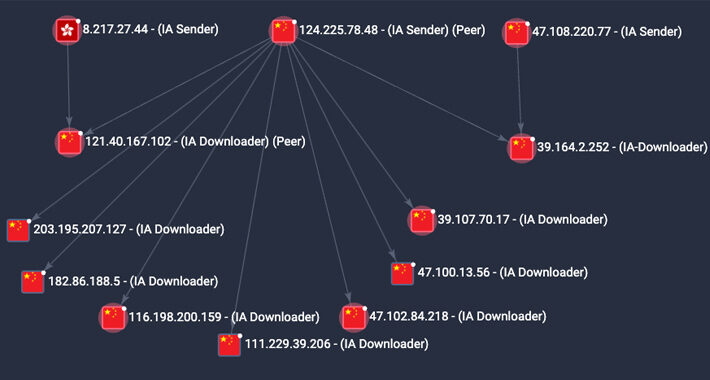
Researchers Raise Red Flag on P2PInfect Malware with 600x Activity Surge – Source:thehackernews.com
Source: thehackernews.com – Author: . Sep 21, 2023THNBotnet / Cyber Threat The peer-to-peer (P2) worm known as P2PInfect has witnessed a surge in activity since late...
The Rise of the Malicious App – Source:thehackernews.com
Source: thehackernews.com – Author: . Sep 21, 2023The Hacker NewsSaaS Security / App Security Security teams are familiar with threats emanating from third-party applications that employees...
Cryptohack Roundup: Private Key Compromise Led to CoinEx Hit – Source: www.govinfosecurity.com
Source: www.govinfosecurity.com – Author: 1 Blockchain & Cryptocurrency , Cryptocurrency Fraud , Fraud Management & Cybercrime Also: Mark Cuban Hot Wallet Hack; Crypto Regulation Mihir Bagwe...
Journey to the Cloud: Navigating the Transformation – Part 3 – Source: www.govinfosecurity.com
Source: www.govinfosecurity.com – Author: 1 Cloud Security , Security Operations Nikko Asset Management’s Marcus Rameke on SaaS or PaaS vs. IaaS or On-Premises HCI CyberEdBoard •...
Canada Confirms DDoS Attack Disrupted Airport Arrival Kiosks – Source: www.govinfosecurity.com
Source: www.govinfosecurity.com – Author: 1 Cyberwarfare / Nation-State Attacks , DDoS Protection , Fraud Management & Cybercrime How in the World Did Self-Proclaimed Hacktivists Hit System...
LIVE Webinar | Identity Security Alchemy: Transforming Governance Challenges into Gold – Source: www.govinfosecurity.com
Source: www.govinfosecurity.com – Author: 1 Wade Ellery VP of Solutions Architects and Senior Technical Evangelist, Radiant Logic Wade has extensive experience in enterprise IT direct and...
Breach Roundup: Effects of ISP Ransomware Attack in Colombia – Source: www.govinfosecurity.com
Source: www.govinfosecurity.com – Author: 1 Cybercrime , Fraud Management & Cybercrime , Incident & Breach Response Also, Clorox Product Shortages; California Passes Data Broker Restrictions Anviksha...
UK Parliament Approves Online Safety Bill – Source: www.govinfosecurity.com
Source: www.govinfosecurity.com – Author: 1 Encryption & Key Management , Geo Focus: The United Kingdom , Geo-Specific Cabinet Ministers Call on Facebook to Stop Rollout of...
New ‘Sandman’ APT Group Hitting Telcos With Rare LuaJIT Malware – Source: www.securityweek.com
Source: www.securityweek.com – Author: Ryan Naraine A new and mysterious APT group has been spotted targeting telco service providers in Europe and Asia as part of...
Every Network Is Now an OT Network. Can Your Security Keep Up? – Source: www.securityweek.com
Source: www.securityweek.com – Author: John Maddison Every network today is now an OT network. Or it will be soon. Of course, part of this transformation is...
Navigating the Digital Frontier in Cybersecurity Awareness Month 2023 – Source: www.securityweek.com
Source: www.securityweek.com – Author: Torsten George This October will mark the 20th anniversary of Cybersecurity Awareness Month, a pivotal initiative launched under the guidance of the...
TransUnion Denies Breach After Hacker Publishes Allegedly Stolen Data – Source: www.securityweek.com
Source: www.securityweek.com – Author: Ionut Arghire Credit reporting firm TransUnion this week denied being breached, after a hacker published online 3Gb of information allegedly stolen from...
Legit Security Raises $40 Million in Series B Financing – Source: www.securityweek.com
Source: www.securityweek.com – Author: Ionut Arghire Application security posture management firm Legit Security on Wednesday announced that it has raised $40 million in a Series B...
Cisco to Acquire Splunk for $28 Billion – Source: www.securityweek.com
Source: www.securityweek.com – Author: Eduard Kovacs Cisco on Thursday announced that it has entered into a definitive agreement to acquire data analysis, security and observability solutions...
Atlassian Security Updates Patch High-Severity Vulnerabilities – Source: www.securityweek.com
Source: www.securityweek.com – Author: Ionut Arghire Atlassian this week announced patches for four high-severity vulnerabilities impacting its Jira, Confluence, Bitbucket, and Bamboo products. Tracked as CVE-2023-22513...
Car Cybersecurity Study Shows Drop in Critical Vulnerabilities Over Past Decade – Source: www.securityweek.com
Source: www.securityweek.com – Author: Eduard Kovacs Research-focused security services provider IOActive has conducted an analysis of car vulnerability trends over the past decade and determined that...
UK’s New Online Safety Law Adds to Crackdown on Big Tech Companies – Source: www.securityweek.com
Source: www.securityweek.com – Author: Associated Press British lawmakers have approved an ambitious but controversial new internet safety law with wide-ranging powers to crack down on digital...
Critical Infrastructure Organizations Warned of Snatch Ransomware Attacks – Source: www.securityweek.com
Source: www.securityweek.com – Author: Ionut Arghire The FBI and the cybersecurity agency CISA on Wednesday published an advisory warning critical infrastructure organizations of ongoing Snatch ransomware...
Snatch ransomware – what you need to know – Source: www.tripwire.com
Source: www.tripwire.com – Author: Graham Cluley What’s happened? The FBI and US Cybersecurity and Infrastructure Security Agency (CISA) have issued a joint advisory warning organisations about...
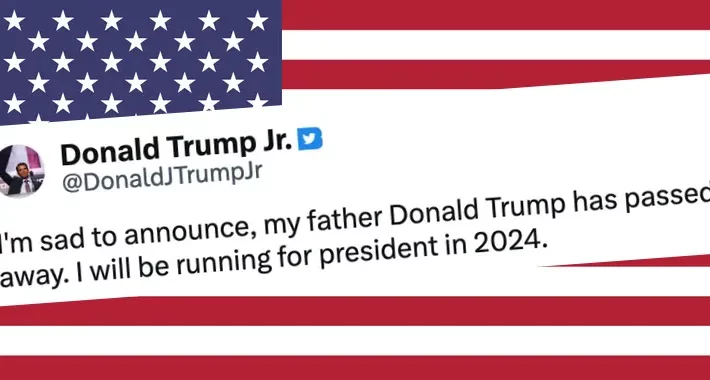
Donald Trump Jr’s hacked Twitter account announces his father has died – Source: grahamcluley.com
Source: grahamcluley.com – Author: Graham Cluley Donald Trump Jr may not have just inherited his famous father’s name. He may also have inherited his bad password...
Smashing Security podcast #340: Heated seats, car privacy, and Graham’s porn video – Source: grahamcluley.com
Source: grahamcluley.com – Author: Graham Cluley Do you know what data your car is collecting about you? Do you think it’s right for a car manufacturer...