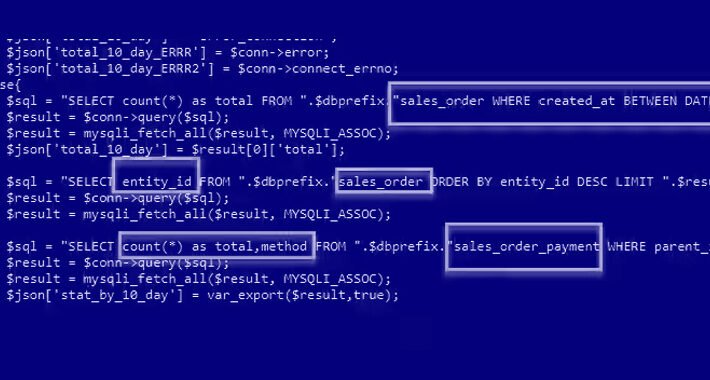
Source: thehackernews.com – Author: . Aug 14, 2023THNWebsite Security / Vulnerability E-commerce sites using Adobe’s Magento 2 software are the target of an ongoing campaign that...
Month: August 2023
Identity Threat Detection and Response: Rips in Your Identity Fabric – Source:thehackernews.com
Source: thehackernews.com – Author: . Why SaaS Security Is a Challenge In today’s digital landscape, organizations are increasingly relying on Software-as-a-Service (SaaS) applications to drive their...
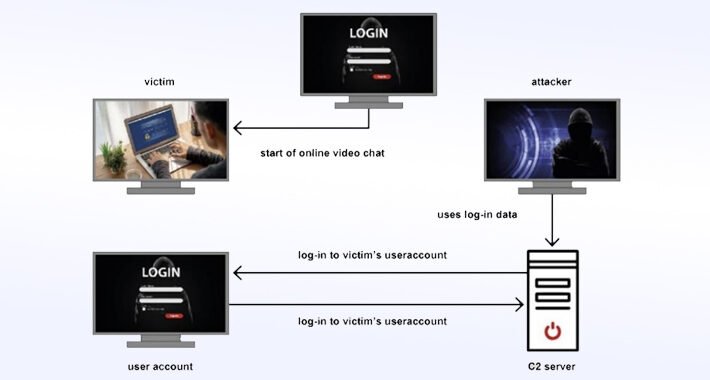
Charming Kitten Targets Iranian Dissidents with Advanced Cyber Attacks – Source:thehackernews.com
Source: thehackernews.com – Author: . Aug 14, 2023THNCyber Espionage Germany’s Federal Office for the Protection of the Constitution (BfV) has warned of cyber attacks targeting Iranian...
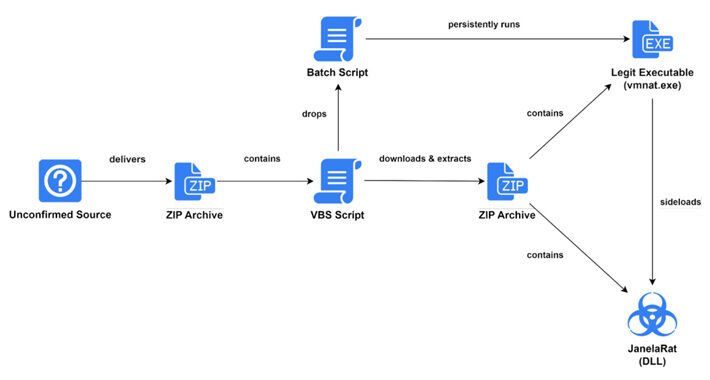
New Financial Malware ‘JanelaRAT’ Targets Latin American Users – Source:thehackernews.com
Source: thehackernews.com – Author: . Aug 14, 2023THNMalware / Cyber Threat Users in Latin America (LATAM) are the target of a financial malware called JanelaRAT that’s...
What is a ‘purple team’ in cyber security? (2023) – Source: www.cybertalk.org
Source: www.cybertalk.org – Author: slandau EXECUTIVE SUMMARY: A purple team provides a critical lens through which organizations can see how to elevate their cyber security. But...
News alert: Fireblocks uncovers vulnerabilities impacting dozens of major wallet providers – Source: www.lastwatchdog.com
Source: www.lastwatchdog.com – Author: bacohido New York, N.Y., Aug.9, 2023 – Today, the Fireblocks Cryptography Research Team announced the findings of multiple zero-day vulnerabilities in some...
News Alert: GhangorCloud selected to demo Deep AI-based capabilities at India’s G20 Summit – Source: www.lastwatchdog.com
Source: www.lastwatchdog.com – Author: bacohido San Jose, Calif., Aug. 7, 2023 – GhangorCloud, a leading provider of Deep AI-based information security and data privacy compliance enforcement...
Alberta Dental Services Security Breach Exposes 1.47M Records – Source: www.infosecurity-magazine.com
Source: www.infosecurity-magazine.com – Author: 1 Alberta Dental Service Corporation (ADSC) has revealed that nearly 1.47 million individuals have been affected by a data breach that occurred...
Several Flaws Found in CyberPower and Dataprobe Products – Source: www.infosecurity-magazine.com
Source: www.infosecurity-magazine.com – Author: 1 A series of security vulnerabilities have been discovered in CyberPower’s PowerPanel Enterprise Data Center Infrastructure Management (DCIM) platform and Dataprobe’s iBoot...
Security Researchers Publish Gigabud Banking Malware Analysis – Source: www.infosecurity-magazine.com
Source: www.infosecurity-magazine.com – Author: 1 Cybersecurity researchers have published a new analysis of the elusive Gigabud banking malware. Originating as an Android Remote Access Trojan (RAT),...
Cumbria Police accidentally publish officers’ names and salaries online – Source: www.bitdefender.com
Source: www.bitdefender.com – Author: Graham Cluley ‘Ello ello ello. What’s all this then? Just days after it was learned that the police had exposed the details...
How to hack casino card-shuffling machines – Source: www.bitdefender.com
Source: www.bitdefender.com – Author: Graham Cluley Security researchers have demonstrated how they were able to exploit a flaw which allowed them to hack the card-shuffling devices...
Ongoing Xurum attacks target Magento 2 e-stores – Source: securityaffairs.com
Source: securityaffairs.com – Author: Pierluigi Paganini Experts warn of ongoing attacks, dubbed Xurum, targeting e-commerce websites using Adobe’s Magento 2 CMS. Akamai researchers warn of ongoing...
Colorado HCPF Department notifies 4 million individuals after IBM MOVEit breach – Source: securityaffairs.com
Source: securityaffairs.com – Author: Pierluigi Paganini The Colorado Department of Health Care Policy & Financing (HCPF) disclose a data breach after MOVEit attack on IBM. The...
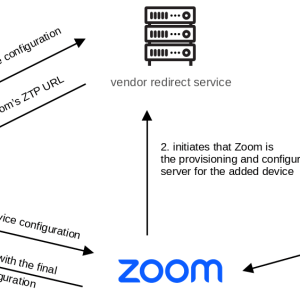
Experts found multiple flaws in AudioCodes desk phones and Zoom’s Zero Touch Provisioning (ZTP) – Source: securityaffairs.com
Source: securityaffairs.com – Author: Pierluigi Paganini Multiple flaws in AudioCodes desk phones and Zoom’s Zero Touch Provisioning (ZTP) can expose to several attacks. Researchers from security...
Nine flaws in CyberPower and Dataprobe solutions expose data centers to hacking – Source: securityaffairs.com
Source: securityaffairs.com – Author: Pierluigi Paganini Multiple vulnerabilities in CyberPower PowerPanel Enterprise DCIM platform and Dataprobe PDU could expose data centers to hacking. Researchers from Trellix...
MoustachedBouncer: Espionage against foreign diplomats in Belarus – Source:
Source: – Author: 1 Long-term espionage against diplomats, leveraging email-based C&C protocols, C++ modular backdoors, and adversary-in-the-middle (AitM) attacks… Sounds like the infamous Turla? Think again!...
Time is money, and online game scammers have lots of it – Source:
Source: – Author: 1 Gamers and cybersecurity professionals have something in common – the ever-terrible presence of hacking, scams, and data theft – but how and...
Check cybersecurity pre-invest – Week in security with Tony Anscombe – Source:
Source: – Author: 1 When you invest in a company, do you check its cybersecurity? The U.S. Securities and Exchange Commission has adopted new cybersecurity rules....
Fingerprints all over: Can browser fingerprinting increase website security? – Source:
Source: – Author: 1 Browser fingerprinting is supposedly a more privacy-conscious tracking method, replacing personal information with more general data. But is it a valid promise?...
The grand theft of Jake Moore’s voice: The concept of a virtual kidnap – Source:
Source: – Author: 1 With powerful AI, it doesn’t take much to fake a person virtually, and while there are some limitations, voice-cloning can have some...
Quantum computing: Will it break crypto security within a few years? – Source:
Source: – Author: 1 Current cryptographic security methods watch out – quantum computing is coming for your lunch. Original Post URL: Category & Tags: – Views:...
Is backdoor access oppressive? – Week in security with Tony Anscombe – Source:
Source: – Author: 1 Bills granting access to end-to-end encrypted systems, opportunity for cybercriminals, abuse by authority, human rights, and tech companies leaving the UK? Original...
Gathering dust and data: How robotic vacuums can spy on you – Source:
Source: – Author: 1 Mitigate the risk of data leaks with a careful review of the product and the proper settings. Original Post URL: Category &...
Dear all, What are some common subject lines in phishing emails? – Source:
Source: – Author: 1 Scammers exploit current ongoing events, account notifications, corporate communication, and a sense of urgency. Original Post URL: Category & Tags: – Views:...
What happens if AI is wrong? – Week in security with Tony Anscombe – Source:
Source: – Author: 1 Responses generated by ChatGPT about individual people could be misleading or harmful or spill their personal information. What are the takeaways for...
8 common work-from-home scams to avoid – Source:
Source: – Author: 1 That ‘employer’ you’re speaking to may in reality be after your personal information, your money or your help with their illegal activities...
Child identity theft: how do I keep my kids’ personal data safe? – Source:
Source: – Author: 1 Why is kids’ personal information in high demand, how do criminals steal it, and what can parents do to help prevent child...
Protect yourself from ticketing scams ahead of the Premier League Summer Series USA Tour – Source:
Source: – Author: 1 There is a significant secondary marketplace where tickets can sell for several times their original value, opening the opportunity for scammers and...
Key findings from ESET Threat Report H1 2023 – Week in security with Tony Anscombe – Source:
Source: – Author: 1 Here’s how cybercriminals have adjusted their tactics in response to Microsoft’s stricter security policies, plus other interesting findings from ESET’s new Threat...