Source: heimdalsecurity.com – Author: Adelina Deaconu In this comprehensive guide, we look into the topic of XDR (Extended Detection and Response) software, shedding light on its...
Day: August 23, 2023
New Ivanti Zero-Day Vulnerability Allows Hackers to Access Sensitive APIs – Source: heimdalsecurity.com
Source: heimdalsecurity.com – Author: Livia Gyongyoși Researchers observed a critical Ivanti Sentry API authentication bypass vulnerability exploited in the wild. The flaw was dubbed CVE-2023-38035 and...
Exploring the Top ManageEngine Competitors & Alternatives in 2023 – Source: heimdalsecurity.com
Source: heimdalsecurity.com – Author: Mihaela Popa ManageEngine has long been a prominent player in the IT management software landscape. However, several viable ManageEngine competitors and alternatives have...
Threat Actors Leak 2.6 Million DuoLingo Users` Data on Hacking Forum – Source: heimdalsecurity.com
Source: heimdalsecurity.com – Author: Livia Gyongyoși Malicious actors exposed 2.6 million DuoLingo users` data on the dark web. The announcement posted on August 22nd made the...
Generative AI: Cybersecurity Weapon, But Not Without Adaptable, Creative (Human) Thinkers – Source: www.techrepublic.com
Source: www.techrepublic.com – Author: Karl Greenberg Image: PB Studio Photo/Adobe Stock Generative AI was — not surprisingly — the conversational coin of the realm at Black...
Electronic Communication Policy – Source: www.techrepublic.com
Source: www.techrepublic.com – Author: This policy provides guidelines for the appropriate use of electronic communications. It covers topics such as privacy, confidentiality and security; ensures electronic...
BlackCat ransomware gang claims credit for Seiko data breach – Source: grahamcluley.com
Source: grahamcluley.com – Author: Graham Cluley The BlackCat ransomware gang has claimed credit for a cybersecurity attack against Japanese watchmaker Seiko. BlackCat (also known as ALPHAV)...
A Bard’s Tale – how fake AI bots try to install malware – Source:
Source: – Author: 1 The AI race is on! It’s easy to lose track of the latest developments and possibilities, and yet everyone wants to see...
Evacuation of 30,000 hackers – Week in security with Tony Anscombe – Source:
Source: – Author: 1 DEF CON, the annual hacker’s convention in Las Vegas, was interrupted on Saturday evening when authorities evacuated the convention due to a...
DEF CON 31: US DoD urges hackers to go and hack ‘AI’ – Source:
Source: – Author: 1 The limits of current AI need to be tested before we can rely on their output Original Post URL: Category & Tags:...
Mass-spreading campaign targeting Zimbra users – Source:
Source: – Author: 1 ESET researchers have observed a new phishing campaign targeting users of the Zimbra Collaboration email server. Original Post URL: Category & Tags:...
DEF CON 31: Robot vacuums may be doing more than they claim – Source:
Source: – Author: 1 When it comes to privacy, it remains complicated and near impossible for a consumer to make an informed decision. Original Post URL:...
Black Hat 2023: Hacking the police (at least their radios) – Source:
Source: – Author: 1 Hiding behind a black box and hoping no one will hack it has been routinely proven to be unwise and less secure....
Black Hat 2023: How AI changes the monetization of search – Source:
Source: – Author: 1 Search engines, AI, and monetization in the new era Original Post URL: Category & Tags: – Views: 15
Black Hat 2023: AI gets big defender prize money – Source:
Source: – Author: 1 Black Hat is big on AI this year, and for a good reason Original Post URL: Category & Tags: – Views: 16
Black Hat 2023: ‘Teenage’ AI not enough for cyberthreat intelligence – Source:
Source: – Author: 1 Current LLMs are just not mature enough for high-level tasks Original Post URL: Category & Tags: – Views: 14
20k security folks in the desert – Week in security with Tony Anscombe – Source:
Source: – Author: 1 Unsurprisingly, artificial intelligence took the center stage at this year’s edition of Black Hat, one of the world’s largest gatherings of cybersecurity...
Black Hat 2023: Cyberwar fire-and-forget-me-not – Source:
Source: – Author: 1 What happens to cyberweapons after a cyberwar? Original Post URL: Category & Tags: – Views: 17
MoustachedBouncer: Espionage against foreign diplomats in Belarus – Source:
Source: – Author: 1 Long-term espionage against diplomats, leveraging email-based C&C protocols, C++ modular backdoors, and adversary-in-the-middle (AitM) attacks… Sounds like the infamous Turla? Think again!...
Time is money, and online game scammers have lots of it – Source:
Source: – Author: 1 Gamers and cybersecurity professionals have something in common – the ever-terrible presence of hacking, scams, and data theft – but how and...
Check cybersecurity pre-invest – Week in security with Tony Anscombe – Source:
Source: – Author: 1 When you invest in a company, do you check its cybersecurity? The U.S. Securities and Exchange Commission has adopted new cybersecurity rules....
Fingerprints all over: Can browser fingerprinting increase website security? – Source:
Source: – Author: 1 Browser fingerprinting is supposedly a more privacy-conscious tracking method, replacing personal information with more general data. But is it a valid promise?...
Spacecolon Toolset Fuels Global Surge in Scarab Ransomware Attacks – Source:thehackernews.com
Source: thehackernews.com – Author: . Aug 23, 2023THNRansomware / Malware A malicious toolset dubbed Spacecolon is being deployed as part of an ongoing campaign to spread...
Over a Dozen Malicious npm Packages Target Roblox Game Developers – Source:thehackernews.com
Source: thehackernews.com – Author: . Aug 23, 2023THNSoftware Security / Malware More than a dozen malicious packages have been discovered on the npm package repository since...
Safeguarding your organization from ChatGPT threats – Source: www.cybertalk.org
Source: www.cybertalk.org – Author: slandau Mazhar Hamayun is a cyber security professional with over 20 years of hands-on technology and leadership experience. At Check Point Software,...
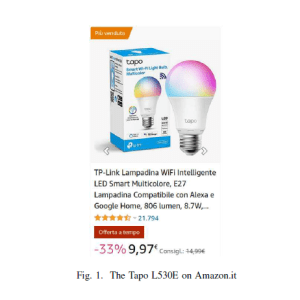
TP-Link Smart Bulb Spills Wi-Fi Passwords – Source: www.infosecurity-magazine.com
Source: www.infosecurity-magazine.com – Author: 1 Security researchers from Italy and London have discovered several vulnerabilities in a popular brand of smart light bulbs, which could allow...
Carderbee APT targets Hong Kong orgs via supply chain attacks – Source: securityaffairs.com
Source: securityaffairs.com – Author: Pierluigi Paganini A previously unknown APT group, tracked as Carderbee, was behind a supply chain attack against Hong Kong organizations. Symantec Threat...
TP-Link Tapo L530E smart bulb flaws allow hackers to steal user passwords – Source: securityaffairs.com
Source: securityaffairs.com – Author: Pierluigi Paganini Four vulnerabilities in the TP-Link Tapo L530E smart bulb and impacting the mobile app used to control them expose users...
Defense contractor Belcan leaks admin password with a list of flaws – Source: securityaffairs.com
Source: securityaffairs.com – Author: Pierluigi Paganini US Government and defense contractor Belcan left its super admin credentials open to the public, Cybernews research team reveals. Belcan...