Source: www.securityweek.com – Author: Ionut Arghire New guidance from the Australian Cyber Security Centre (ACSC), the US Cybersecurity and Infrastructure Security Agency (CISA), and National Security...
Month: July 2023
In Other News: Data Breach Cost Rises, Russia Targets Diplomats, Tracker Alerts in Android – Source: www.securityweek.com
Source: www.securityweek.com – Author: SecurityWeek News SecurityWeek is publishing a weekly cybersecurity roundup that provides a concise compilation of noteworthy stories that might have slipped under...
Exploitation of Recent Citrix ShareFile RCE Vulnerability Begins – Source: www.securityweek.com
Source: www.securityweek.com – Author: Ionut Arghire Threat intelligence company Greynoise says it has observed the first attempts to exploit a recent critical remote code execution (RCE)...
Industry Reactions to New SEC Cyber Incident Disclosure Rules: Feedback Friday – Source: www.securityweek.com
Source: www.securityweek.com – Author: Eduard Kovacs The US Securities and Exchange Commission (SEC) has adopted new cybersecurity incident disclosure rules for public companies, but there is...
Zimbra Patches Exploited Zero-Day Vulnerability – Source: www.securityweek.com
Source: www.securityweek.com – Author: Ionut Arghire Zimbra this week released patches for a cross-site scripting (XSS) vulnerability in Collaboration Suite that has been exploited in malicious...
CoinsPaid Blames North Korean Hackers for $37 Million Cryptocurrency Heist – Source: www.securityweek.com
Source: www.securityweek.com – Author: Ionut Arghire Cryptocurrency payments firm CoinsPaid says North Korean hacking group Lazarus is likely responsible for the theft of approximatively $37 million...
Weintek Weincloud Vulnerabilities Allowed Manipulation, Damaging of ICS Devices – Source: www.securityweek.com
Source: www.securityweek.com – Author: Eduard Kovacs Several vulnerabilities discovered by a researcher from industrial cybersecurity firm TXOne Networks in a Weintek product could have been exploited...
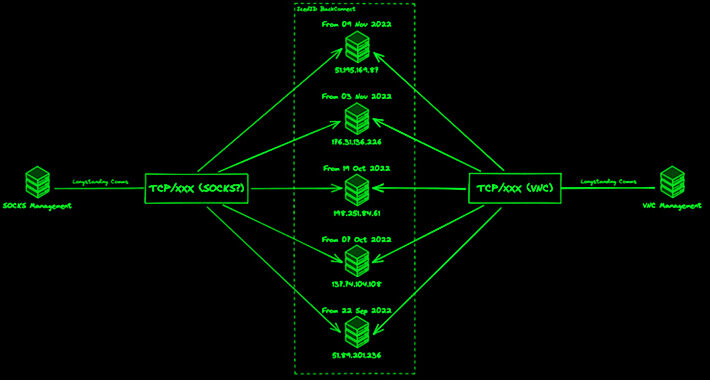
IcedID Malware Adapts and Expands Threat with Updated BackConnect Module – Source:thehackernews.com
Source: thehackernews.com – Author: . Jul 28, 2023THNMalware / Cyber Threat The threat actors linked to the malware loader known as IcedID have made updates to...
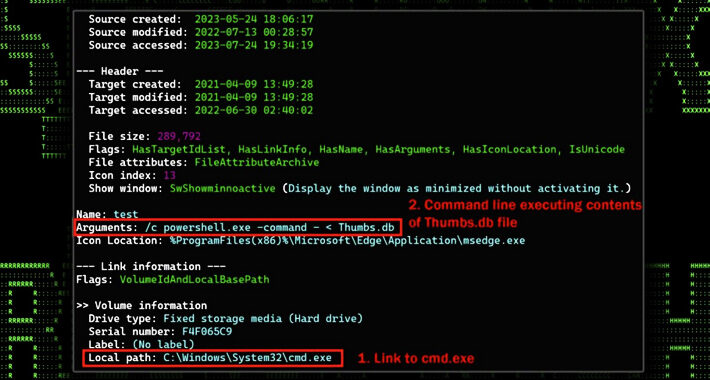
STARK#MULE Targets Koreans with U.S. Military-themed Document Lures – Source:thehackernews.com
Source: thehackernews.com – Author: . Jul 28, 2023THNCyber Attack / Malware An ongoing cyber attack campaign has set its sights on Korean-speaking individuals by employing U.S....
UK MoD Error Sends Emails to Russia’s Ally Instead of US – Source: www.infosecurity-magazine.com
Source: www.infosecurity-magazine.com – Author: 1 The UK’s Ministry of Defence (MoD) is launching an investigation after a typing error reportedly led to classified emails being sent...
New Study Reveals Forged Certificate Attack Risks – Source: www.infosecurity-magazine.com
Source: www.infosecurity-magazine.com – Author: 1 New research has highlighted the severe risks posed by forged certificate attacks, which can lead to unauthorized access to important company...
40% of Ubuntu Cloud Workloads Vulnerable to Exploits – Source: www.infosecurity-magazine.com
Source: www.infosecurity-magazine.com – Author: 1 Two high-priority vulnerabilities have been discovered in the OverlayFS module of Ubuntu Linux, impacting approximately 40% of Ubuntu cloud workloads. According...
Microsoft Accused of Negligence in Recent Email Compromise – Source: www.infosecurity-magazine.com
Source: www.infosecurity-magazine.com – Author: 1 A US Senator has demanded that the Whitehouse holds Microsoft to account for a Chinese cyber campaign that compromised US government...
Australia and US Issue Warning About Web App Threats – Source: www.infosecurity-magazine.com
Source: www.infosecurity-magazine.com – Author: 1 The Australian and US governments have issued a joint advisory about the growing cyber-threats to web applications and application programming interfaces...
SSNDOB Marketplace Admin Pleads Guilty – Source: www.infosecurity-magazine.com
Source: www.infosecurity-magazine.com – Author: 1 A Ukrainian man has pleaded guilty to charges connected with his role as an administrator of notorious cybercrime marketplace SSNDOB. Vitalii...
North Korean Hackers Bag Another $100m in Crypto Heists – Source: www.infosecurity-magazine.com
Source: www.infosecurity-magazine.com – Author: 1 North Korea’s infamous Lazarus hacking group has been linked to two new attacks on cryptocurrency firms which led to the theft...
MOVEit Campaign Claims Millions More Victims – Source: www.infosecurity-magazine.com
Source: www.infosecurity-magazine.com – Author: 1 Another 8–11 million individuals are believed to have had their personal information compromised by the Clop ransomware gang after a US...
How to Use NordVPN Meshnet for Free – Source: www.techrepublic.com
Source: www.techrepublic.com – Author: Lance Whitney Image: chinnarach/Adobe Stock NordVPN is one of many products that can secure your PC with a virtual private network. The...
OpenAI, Microsoft, Google, Anthropic Launch Frontier Model Forum to Promote Safe AI – Source: www.techrepublic.com
Source: www.techrepublic.com – Author: Esther Shein Image: putilov_denis/Adobe Stock OpenAI, Google, Microsoft and Anthropic have announced the formation of the Frontier Model Forum. With this initiative,...
HackerOne: How Artificial Intelligence Is Changing Cyber Threats and Ethical Hacking – Source: www.techrepublic.com
Source: www.techrepublic.com – Author: Megan Crouse Image: NicoElNino/Adobe Stock HackerOne, a security platform and hacker community forum, hosted a roundtable on Thursday, July 27, about the...
Anomaly detection in certificate-based TGT requests – Source: securelist.com
Source: securelist.com – Author: Alexander Rodchenko One of the most complex yet effective methods of gaining unauthorized access to corporate network resources is an attack using...
DNS Protection: A Must-Have Defense Against Cyber Attacks – Source: heimdalsecurity.com
Source: heimdalsecurity.com – Author: Madalina Popovici Picture this scenario: you’re browsing the internet, going about your business, when suddenly a malicious website pops up out of...
How to Prioritize Vulnerabilities Effectively: Vulnerability Prioritization Explained – Source: heimdalsecurity.com
Source: heimdalsecurity.com – Author: Cristian Neagu What Is Vulnerability Prioritization? Vulnerability prioritization is the process of identifying and ranking vulnerabilities based on the potential impact on...
40,000 HRM Enterprises Clients Had Their Credit Card Information Stolen Following Cyberattack – Source: heimdalsecurity.com
Source: heimdalsecurity.com – Author: Cristian Neagu HRM Enterprises, Inc., the owner of the US’s largest independent hardware store, was recently the victim of a cyberattack where...
What is Managed Detection and Response (MDR)? Benefits & Capabilities – Source: heimdalsecurity.com
Source: heimdalsecurity.com – Author: Andreea Chebac The term Managed Detection and Response (MDR) refers to an outsourced cybersecurity service that employs advanced technologies and human expertise....
What Is Secure Remote Access? – Source: heimdalsecurity.com
Source: heimdalsecurity.com – Author: Antonia Din Secure remote access is an effective approach to cybersecurity that combines multiple technologies, such as encryption, multifactor authentication (MFA), VPNs,...
The Road to Redemption: Ransomware Recovery Strategies for Businesses – Source: heimdalsecurity.com
Source: heimdalsecurity.com – Author: Gabriella Antal Ransomware attacks have become one of the most significant cybersecurity threats facing businesses and organizations today. These malicious attacks encrypt...
U.S. Government Contractor Maximus Hit by Massive Data Breach – Source: heimdalsecurity.com
Source: heimdalsecurity.com – Author: Cristian Neagu U.S. government service contracting giant Maximus has disclosed a data breach warning that threat actors stole the personal data (including...
Dark Power Ransomware Abusing Vulnerable Dynamic-Link Libraries in Resolved API Flow – Source: heimdalsecurity.com
Source: heimdalsecurity.com – Author: Vladimir Unterfingher In a previously-published material, Heimdal® has analyzed the emergent Dark Power malware – a ransomware strain written in the NIM...
What Is a Vulnerability Management Program? – Source: heimdalsecurity.com
Source: heimdalsecurity.com – Author: Cristian Neagu What Is Vulnerability Management? Vulnerability Management refers to the security practices that proactively identify, prevent, mitigate, and classify vulnerabilities within...