Source: – Author: 1 As TikTok CEO attempts to placate U.S. lawmakers, it’s time for us all to think about the wealth of personal information that...
Month: July 2023
Highlights from TikTok CEO’s Congress grilling – Week in security with Tony Anscombe – Source:
Source: – Author: 1 Here are some of the key moments from the five hours of Shou Zi Chew’s testimony and other interesting news on the...
Staying safe on OnlyFans: The naked truth – Source:
Source: – Author: 1 How content creators and subscribers can embrace the social media platform without (overly) exposing themselves to the potentially toxic brew of NSFW...
Pig butchering scams: The anatomy of a fast-growing threat – Source:
Source: – Author: 1 How fraudsters groom their marks and move in for the kill using tricks from the playbooks of romance and investment scammers Original...
ESET Research Podcast: A year of fighting rockets, soldiers, and wipers in Ukraine – Source:
Source: – Author: 1 ESET experts share their insights on the cyber-elements of the first year of the war in Ukraine and how a growing number...
World Backup Day: Avoiding a data disaster is a forever topic – Source:
Source: – Author: 1 By failing to prepare you are preparing to fail. Make sure you’re able to bounce back if, or when, a data disaster...
Avoiding data backup failures – Week in security with Tony Anscombe – Source:
Source: – Author: 1 Today is World Backup Day, but maybe we also need a “did you test your backups” day? Original Post URL: Category &...
Why you should spring clean your home network and audit your backups – Source:
Source: – Author: 1 Do you know how many devices are connected to your home network? You don’t? This is precisely why it’s time for a...
SVB’s collapse is a scammer’s dream: Don’t get caught out – Source:
Source: – Author: 1 How cybercriminals can exploit Silicon Valley Bank’s downfall for their own ends – and at your expense Original Post URL: Category &...
Cleaning up your social media and passwords: What to trash and what to treasure – Source:
Source: – Author: 1 Give your social media presence a good spring scrubbing, audit your passwords and other easy ways to bring order to your digital...
Steer clear of tax scams – Week in security with Tony Anscombe – Source:
Source: – Author: 1 In a rush to file your taxes? Watch out for cybercriminals preying on stressed taxpayers as Tax Day looms large on the...
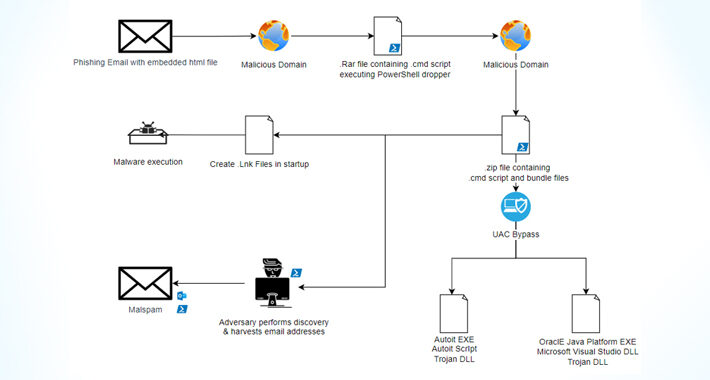
Casbaneiro Banking Malware Goes Under the Radar with UAC Bypass Technique – Source:thehackernews.com
Source: thehackernews.com – Author: . Jul 25, 2023THNMalware / Cyber Threat The financially motivated threat actors behind the Casbaneiro banking malware family have been observed making...
macOS Under Attack: Examining the Growing Threat and User Perspectives – Source:thehackernews.com
Source: thehackernews.com – Author: . Jul 25, 2023The Hacker NewsEndpoint Security / macOS As the number of people using macOS keeps going up, so does the...
TETRA:BURST — 5 New Vulnerabilities Exposed in Widely Used Radio Communication System – Source:thehackernews.com
Source: thehackernews.com – Author: . Jul 25, 2023THNNetwork Security / Vulnerability A set of five security vulnerabilities have been disclosed in the Terrestrial Trunked Radio (TETRA)...
How MDR Helps Solve the Cybersecurity Talent Gap – Source:thehackernews.com
Source: thehackernews.com – Author: . Jul 25, 2023The Hacker NewsCyber Threat Intelligence How do you overcome today’s talent gap in cybersecurity? This is a crucial issue...
Zenbleed: New Flaw in AMD Zen 2 Processors Puts Encryption Keys and Passwords at Risk – Source:thehackernews.com
Source: thehackernews.com – Author: . Jul 25, 2023THNHardware Security / Encryption A new security vulnerability has been discovered in AMD’s Zen 2 architecture-based processors that could...
Atlassian Releases Patches for Critical Flaws in Confluence and Bamboo – Source:thehackernews.com
Source: thehackernews.com – Author: . Jul 25, 2023THNServer Security / Zero Day Atlassian has released updates to address three security flaws impacting its Confluence Server, Data...
Ivanti Releases Urgent Patch for EPMM Zero-Day Vulnerability Under Active Exploitation – Source:thehackernews.com
Source: thehackernews.com – Author: . Jul 25, 2023THNEnterprise Security / Zero Day Ivanti is warning users to update their Endpoint Manager Mobile (EPMM) mobile device management...
Apple Rolls Out Urgent Patches for Zero-Day Flaws Impacting iPhones, iPads and Macs – Source:thehackernews.com
Source: thehackernews.com – Author: . Jul 25, 2023THNEndpoint Security / Zero Day Apple has rolled out security updates to iOS, iPadOS, macOS, tvOS, watchOS, and Safari...
How to Create a Custom Security & Threat Dashboard in Power BI – Source: www.techrepublic.com
Source: www.techrepublic.com – Author: Mary Branscombe Image: monticellllo/Adobe Stock In many ways, you can treat Microsoft Power BI as the next generation of Excel. And like...
OpenAI, Google and More Agree to White House List of Eight AI Safety Assurances – Source: www.techrepublic.com
Source: www.techrepublic.com – Author: Megan Crouse on July 24, 2023, 6:19 PM EDT OpenAI, Google and More Agree to White House List of Eight AI Safety...
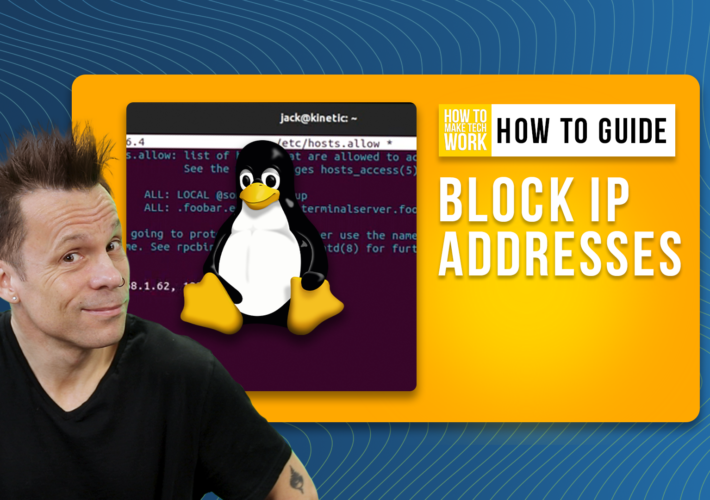
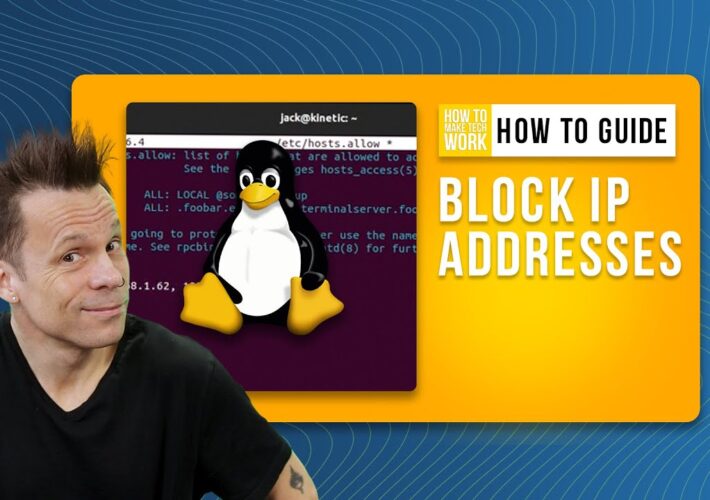
How to Easily Block IP Addresses From Accessing a Desktop or Server – Source: www.techrepublic.com
Source: www.techrepublic.com – Author: Jack Wallen on July 24, 2023, 5:53 PM EDT How to Easily Block IP Addresses From Accessing a Desktop or Server In...
Independent Ada Lovelace Institute Asks UK Government to Firm up AI Regulation Proposals – Source: www.techrepublic.com
Source: www.techrepublic.com – Author: Megan Crouse on July 24, 2023, 5:49 PM EDT Independent Ada Lovelace Institute Asks UK Government to Firm up AI Regulation Proposals...
How to Easily Block IP Addresses From Accessing a Desktop or Server – Source: www.techrepublic.com
Source: www.techrepublic.com – Author: Jack Wallen TechRepublic Premium TechRepublic Premium Checklist: Onboarding/Offboarding C-Level Executives C-level executives commonly present a unique combination of advanced permissions, mobility requirements...
Hardware-bound passkeys are still ultimate in security: Yubico VP – Source: www.techrepublic.com
Source: www.techrepublic.com – Author: Karl Greenberg YubiKey 5 Series multi-protocol hardware authentication device. (Image: Yubico) Derek Hanson, an expert on hardware-bound and syncable passkeys, works very...
Norway says Ivanti zero-day was used to hack govt IT systems – Source: www.bleepingcomputer.com
Source: www.bleepingcomputer.com – Author: Sergiu Gatlan The Norwegian National Security Authority (NSM) has confirmed that attackers used a zero-day vulnerability in Ivanti’s Endpoint Manager Mobile (EPMM)...
Microsoft Sharepoint outage caused by use of wrong TLS certificate – Source: www.bleepingcomputer.com
Source: www.bleepingcomputer.com – Author: Lawrence Abrams Microsoft Sharepoint and OneDrive for Business were briefly interrupted today after a German TLS certificate was mistakenly added to the...
Zenbleed attack leaks sensitive data from AMD Zen2 processors – Source: www.bleepingcomputer.com
Source: www.bleepingcomputer.com – Author: Bill Toulas Google’s security researcher Tavis Ormandy discovered a new vulnerability impacting AMD Zen2 CPUs that could allow a malicious actor to...
Lazarus hackers hijack Microsoft IIS servers to spread malware – Source: www.bleepingcomputer.com
Source: www.bleepingcomputer.com – Author: Bill Toulas The North Korean state-sponsored Lazarus hacking group is breaching Windows Internet Information Service (IIS) web servers to hijack them for...
Ivanti patches MobileIron zero-day bug exploited in attacks – Source: www.bleepingcomputer.com
Source: www.bleepingcomputer.com – Author: Sergiu Gatlan US-based IT software company Ivanti has patched an actively exploited zero-day authentication bypass vulnerability impacting its Endpoint Manager Mobile (EPMM) mobile...