Source: www.infosecurity-magazine.com – Author: 1 The UK Government’s Cyber Security Skills in the UK Labour Market 2023 report shows a staggering 50% of all UK businesses...
Day: July 25, 2023
Hacker Claims to Have Stolen Sensitive Medical Records from Egypt’s Ministry of Health – Source: www.infosecurity-magazine.com
Source: www.infosecurity-magazine.com – Author: 1 An ‘established’ threat actor claimed to be in possession of two million data records stolen from the Egyptian Ministry of Health...
Aussie Government Exposed Personal Info Via Security Report – Source: www.infosecurity-magazine.com
Source: www.infosecurity-magazine.com – Author: 1 The Australian home affairs department has been left red faced after accidentally leaking the personal information of participants in a government cybersecurity...
Ivanti Patches Zero-Day Bug Used in Norway Attacks – Source: www.infosecurity-magazine.com
Source: www.infosecurity-magazine.com – Author: 1 A major security breach at the Norwegian government announced yesterday has been traced back to a zero-day vulnerability in an Ivanti security...
Data Breach Costs Hit Record High but Fall For Some – Source: www.infosecurity-magazine.com
Source: www.infosecurity-magazine.com – Author: 1 The average global cost of a data breach now stands at a record $4.45m, up a little over 2% year on...
How to write a killer pentest report – Source: grahamcluley.com
Source: grahamcluley.com – Author: Graham Cluley Graham Cluley Security News is sponsored this week by the folks at PlexTrac. Thanks to the great team there for...
Google blocks staff’s internet access to reduce attacks – but will it work? – Source: www.bitdefender.com
Source: www.bitdefender.com – Author: Graham Cluley Just a moment… Enable JavaScript and cookies to continue Original Post URL: https://www.bitdefender.com/blog/hotforsecurity/google-blocks-staffs-internet-access-to-reduce-attacks-but-will-it-work/ Category & Tags: Google,Guest blog,Malware,Phishing,Security threats –...
What happens if AI is wrong? – Week in security with Tony Anscombe – Source:
Source: – Author: 1 Responses generated by ChatGPT about individual people could be misleading or harmful or spill their personal information. What are the takeaways for...
Spring into action and tidy up your digital life like a pro – Source:
Source: – Author: 1 Spring is in the air and as the leaves start growing again, why not breathe some new life into the devices you...
Twitter ends free SMS 2FA: Here’s how you can protect your account now – Source:
Source: – Author: 1 Twitter’s ditching of free text-message authentication doesn’t mean that you should forgo using 2FA. Instead, switch to another – and, indeed, better...
Understanding Managed Detection and Response – and what to look for in an MDR solution – Source:
Source: – Author: 1 Why your organization should consider an MDR solution and five key things to look for in a service offering Original Post URL:...
What TikTok knows about you – and what you should know about TikTok – Source:
Source: – Author: 1 As TikTok CEO attempts to placate U.S. lawmakers, it’s time for us all to think about the wealth of personal information that...
Highlights from TikTok CEO’s Congress grilling – Week in security with Tony Anscombe – Source:
Source: – Author: 1 Here are some of the key moments from the five hours of Shou Zi Chew’s testimony and other interesting news on the...
Staying safe on OnlyFans: The naked truth – Source:
Source: – Author: 1 How content creators and subscribers can embrace the social media platform without (overly) exposing themselves to the potentially toxic brew of NSFW...
Pig butchering scams: The anatomy of a fast-growing threat – Source:
Source: – Author: 1 How fraudsters groom their marks and move in for the kill using tricks from the playbooks of romance and investment scammers Original...
ESET Research Podcast: A year of fighting rockets, soldiers, and wipers in Ukraine – Source:
Source: – Author: 1 ESET experts share their insights on the cyber-elements of the first year of the war in Ukraine and how a growing number...
World Backup Day: Avoiding a data disaster is a forever topic – Source:
Source: – Author: 1 By failing to prepare you are preparing to fail. Make sure you’re able to bounce back if, or when, a data disaster...
Avoiding data backup failures – Week in security with Tony Anscombe – Source:
Source: – Author: 1 Today is World Backup Day, but maybe we also need a “did you test your backups” day? Original Post URL: Category &...
Why you should spring clean your home network and audit your backups – Source:
Source: – Author: 1 Do you know how many devices are connected to your home network? You don’t? This is precisely why it’s time for a...
SVB’s collapse is a scammer’s dream: Don’t get caught out – Source:
Source: – Author: 1 How cybercriminals can exploit Silicon Valley Bank’s downfall for their own ends – and at your expense Original Post URL: Category &...
Cleaning up your social media and passwords: What to trash and what to treasure – Source:
Source: – Author: 1 Give your social media presence a good spring scrubbing, audit your passwords and other easy ways to bring order to your digital...
Steer clear of tax scams – Week in security with Tony Anscombe – Source:
Source: – Author: 1 In a rush to file your taxes? Watch out for cybercriminals preying on stressed taxpayers as Tax Day looms large on the...
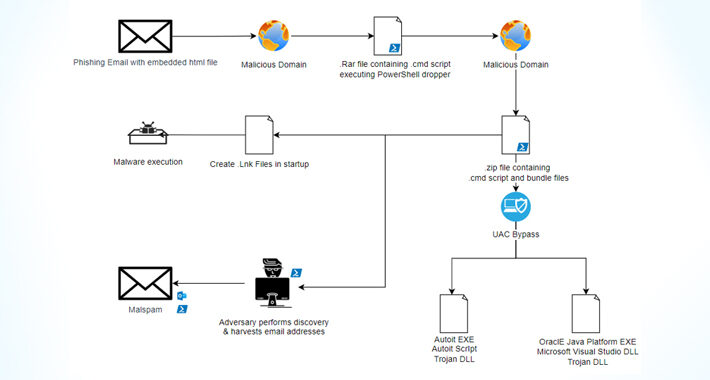
Casbaneiro Banking Malware Goes Under the Radar with UAC Bypass Technique – Source:thehackernews.com
Source: thehackernews.com – Author: . Jul 25, 2023THNMalware / Cyber Threat The financially motivated threat actors behind the Casbaneiro banking malware family have been observed making...
macOS Under Attack: Examining the Growing Threat and User Perspectives – Source:thehackernews.com
Source: thehackernews.com – Author: . Jul 25, 2023The Hacker NewsEndpoint Security / macOS As the number of people using macOS keeps going up, so does the...
TETRA:BURST — 5 New Vulnerabilities Exposed in Widely Used Radio Communication System – Source:thehackernews.com
Source: thehackernews.com – Author: . Jul 25, 2023THNNetwork Security / Vulnerability A set of five security vulnerabilities have been disclosed in the Terrestrial Trunked Radio (TETRA)...
How MDR Helps Solve the Cybersecurity Talent Gap – Source:thehackernews.com
Source: thehackernews.com – Author: . Jul 25, 2023The Hacker NewsCyber Threat Intelligence How do you overcome today’s talent gap in cybersecurity? This is a crucial issue...
Zenbleed: New Flaw in AMD Zen 2 Processors Puts Encryption Keys and Passwords at Risk – Source:thehackernews.com
Source: thehackernews.com – Author: . Jul 25, 2023THNHardware Security / Encryption A new security vulnerability has been discovered in AMD’s Zen 2 architecture-based processors that could...
Atlassian Releases Patches for Critical Flaws in Confluence and Bamboo – Source:thehackernews.com
Source: thehackernews.com – Author: . Jul 25, 2023THNServer Security / Zero Day Atlassian has released updates to address three security flaws impacting its Confluence Server, Data...
Ivanti Releases Urgent Patch for EPMM Zero-Day Vulnerability Under Active Exploitation – Source:thehackernews.com
Source: thehackernews.com – Author: . Jul 25, 2023THNEnterprise Security / Zero Day Ivanti is warning users to update their Endpoint Manager Mobile (EPMM) mobile device management...
Apple Rolls Out Urgent Patches for Zero-Day Flaws Impacting iPhones, iPads and Macs – Source:thehackernews.com
Source: thehackernews.com – Author: . Jul 25, 2023THNEndpoint Security / Zero Day Apple has rolled out security updates to iOS, iPadOS, macOS, tvOS, watchOS, and Safari...