Source: www.lastwatchdog.com – Author: bacohido Westford, Mass., June 27, 2023 – The industry is vying for ever-increasing gigabyte capacities. And yet there are countless applications that...
Day: July 6, 2023
Belgian Tax Hack – Source: www.schneier.com
Source: www.schneier.com – Author: Bruce Schneier HomeBlog Belgian Tax Hack Here’s a fascinating tax hack from Belgium (listen to the details here, episode #484 of “No...
Ongoing Incident Prompts JumpCloud to Reset API Keys – Source: www.infosecurity-magazine.com
Source: www.infosecurity-magazine.com – Author: 1 In response to an ongoing incident, JumpCloud has reset the admin Application Programming Interface (API) keys for affected customers. In a...
Cisco Enterprise Switch Flaw Exposes Encrypted Traffic – Source: www.infosecurity-magazine.com
Source: www.infosecurity-magazine.com – Author: 1 A critical security flaw has been discovered in the Cisco Application Centric Infrastructure (ACI) Multi-Site CloudSec encryption feature, potentially allowing hackers...
Unpatched SolarView Systems Vulnerable to Exploits – Source: www.infosecurity-magazine.com
Source: www.infosecurity-magazine.com – Author: 1 Security researchers at VulnCheck have highlighted the exploitation of vulnerabilities in the SolarView Series, an industrial control systems (ICS) hardware widely...
Human Error the Leading Cause of Cloud Data Breaches – Source: www.infosecurity-magazine.com
Source: www.infosecurity-magazine.com – Author: 1 Around two in five (39%) businesses experienced a data breach in their cloud environment in 2022, a rise of 4% compared...
Experts Warn of Impending TeamTNT Docker Attacks – Source: www.infosecurity-magazine.com
Source: www.infosecurity-magazine.com – Author: 1 Security researchers have warned that the infamous TeamTNT group could be preparing a significant new campaign against cloud-native environments, after spotting...
Police Arrest Suspected OPERA1ER Cybercrime Kingpin – Source: www.infosecurity-magazine.com
Source: www.infosecurity-magazine.com – Author: 1 Police have announced the arrest of an individual they believe to be a key figure in a prolific cybercrime group which...
Suspicious Email Reports Up a Third as NCSC Hails Active Defense – Source: www.infosecurity-magazine.com
Source: www.infosecurity-magazine.com – Author: 1 A leading UK cybersecurity agency has hailed continued progress with its flagship initiative, designed to make the country the safest place...
Free Akira ransomware decryptor released for victims who wish to recover their data without paying extortionists – Source: www.tripwire.com
Source: www.tripwire.com – Author: Graham Cluley There’s good news for any business which has fallen victim to the Akira ransomware. Security researchers at anti-virus company Avast...
Smashing Security podcast #329: Pornhub, Barbie dolls, and can you trust a free TV? – Source: grahamcluley.com
Source: grahamcluley.com – Author: Graham Cluley Just how much do porn websites know about your sexual peccadillos? How are Barbie dolls involved in identity scams? And...
Thales: For Data Breaches, Cloud Assets are Biggest Cybersecurity Headache – Source: www.techrepublic.com
Source: www.techrepublic.com – Author: Karl Greenberg on July 5, 2023, 5:29 PM EDT Thales: For Data Breaches, Cloud Assets are Biggest Cybersecurity Headache Thales cloud security...
Is Quantum Computing Right for Your Business? – Source: www.techrepublic.com
Source: www.techrepublic.com – Author: Megan Crouse Learn about the benefits and use cases of quantum computing. Also, get details about quantum cryptography from an expert. Image:...
Russian Ransomware Group Shuts Down Major Japanese Port – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 Critical Infrastructure Security , Fraud Management & Cybercrime , Ransomware Reported LockBit 3.0 Attack Locks Up Systems, Delays Shipping of Toyota...
Webinar | Building Security Resilience and Preventing Burnout – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 Silvia Rodriguez Garcia Principal Solutions Architect, Expel Silvia is a Principal Solutions Architect at Expel. She ensures Expel’s customers are secured...
What Should a Chatbot Policy Look Like? – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 Artificial Intelligence & Machine Learning , Next-Generation Technologies & Secure Development , Security Operations CISO Ian Thornton-Trump on Chatbots and the...
Tennessee Clinic: April ‘BianLian’ Attack Affected 559,000 – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 Fraud Management & Cybercrime , Governance & Risk Management , Privacy Cybercrime Group May Have Stolen Patient and Employee Information Marianne...
New Chinese Counterespionage Law Aimed at US Tech Sector – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 Cyberwarfare / Nation-State Attacks , Fraud Management & Cybercrime , Government Experts Say China Aims to Retaliate Against US Tech Companies,...
Surviving the 800 Gbps Storm: Gain Insights from Gcore’s 2023 DDoS Attack Statistics – Source:thehackernews.com
Source: thehackernews.com – Author: . Jul 06, 2023The Hacker News Gcore Radar is a quarterly report prepared by Gcore that provides insights into the current state...
Researchers Uncover New Linux Kernel ‘StackRot’ Privilege Escalation Vulnerability – Source:thehackernews.com
Source: thehackernews.com – Author: . Jul 06, 2023Ravie LakshmananLinux / Endpoint Security Details have emerged about a newly identified security flaw in the Linux kernel that...
How Pen Testing can Soften the Blow on Rising Costs of Cyber Insurance – Source:thehackernews.com
Source: thehackernews.com – Author: . Jul 06, 2023The Hacker NewsPenetration Testing / VAPT As technology advances and organizations become more reliant on data, the risks associated...
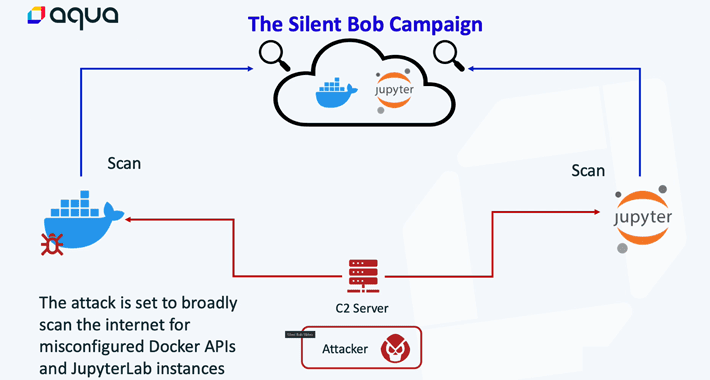
Silentbob Campaign: Cloud-Native Environments Under Attack – Source:thehackernews.com
Source: thehackernews.com – Author: . Jul 06, 2023Ravie LakshmananCloud Security / Server Hacking Cybersecurity researchers have unearthed an attack infrastructure that’s being used as part of...
INTERPOL Nabs Hacking Crew OPERA1ER’s Leader Behind $11 Million Cybercrime – Source:thehackernews.com
Source: thehackernews.com – Author: . Jul 06, 2023Ravie LakshmananCyber Crime / Hacking A suspected senior member of a French-speaking hacking crew known as OPERA1ER has been...
Russian Ransomware Group Shuts Down Major Japanese Port – Source: www.govinfosecurity.com
Source: www.govinfosecurity.com – Author: 1 Critical Infrastructure Security , Fraud Management & Cybercrime , Ransomware Reported LockBit 3.0 Attack Locks Up Systems, Delays Shipping of Toyota...
Live Discussion – Generative AI, Cybersecurity Friend or Foe? – Source: www.govinfosecurity.com
Source: www.govinfosecurity.com – Author: 1 Shawn Surber Senior Director, Technical Account Management, Tanium Shawn Surber is Senior Director of Technical Account Management at Tanium. Over his...
What Should a Chatbot Policy Look Like? – Source: www.govinfosecurity.com
Source: www.govinfosecurity.com – Author: 1 Artificial Intelligence & Machine Learning , Next-Generation Technologies & Secure Development , Security Operations CISO Ian Thornton-Trump on Chatbots and the...
Tennessee Clinic: April ‘BianLian’ Attack Affected 559,000 – Source: www.govinfosecurity.com
Source: www.govinfosecurity.com – Author: 1 Fraud Management & Cybercrime , Governance & Risk Management , Privacy Cybercrime Group May Have Stolen Patient and Employee Information Marianne...
New Chinese Counterespionage Law Aimed at US Tech Sector – Source: www.govinfosecurity.com
Source: www.govinfosecurity.com – Author: 1 Cyberwarfare / Nation-State Attacks , Fraud Management & Cybercrime , Government Experts Say China Aims to Retaliate Against US Tech Companies,...
New tool exploits Microsoft Teams bug to send malware to users – Source: www.bleepingcomputer.com
Source: www.bleepingcomputer.com – Author: Bill Toulas A member of U.S. Navy’s red team has published a tool called TeamsPhisher that leverages an unresolved security issue in Microsoft...
Police arrest suspect linked to notorius OPERA1ER cybercrime gang – Source: www.bleepingcomputer.com
Source: www.bleepingcomputer.com – Author: Sergiu Gatlan Law enforcement has detained a suspect believed to be a key member of the OPERA1ER cybercrime group, which has targeted...