Source: www.theguardian.com – Author: Henry Belot Sensitive and personal government information has been stolen from law firm HWL Ebsworth by a Russian ransomware gang and posted...
Day: July 5, 2023
Japan’s largest port stops operations after ransomware attack – Source: www.bleepingcomputer.com
Source: www.bleepingcomputer.com – Author: Bill Toulas The Port of Nagoya, the largest and busiest port in Japan, has been targeted in a ransomware attack that currently...
Hackers Steal and Sell Victims’ Bandwidth Using ProxyHacking – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 Cybercrime , Cybercrime as-a-service , Endpoint Security Attackers List Compromised Servers on Bandwidth Sharing Platforms for Profit Akshaya Asokan (asokan_akshaya) •...
Banking Tech Forecast: Cloudy, With a Chance of Cyber Risk – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 3rd Party Risk Management , Cloud Security , Governance & Risk Management Cloud Adoption in Financial Services has Soared – as...
Secrets, Secrets Are No Fun. Secrets, Secrets (Stored in Plain Text Files) Hurt Someone – Source:thehackernews.com
Source: thehackernews.com – Author: . Secrets are meant to be hidden or, at the very least, only known to a specific and limited set of individuals...
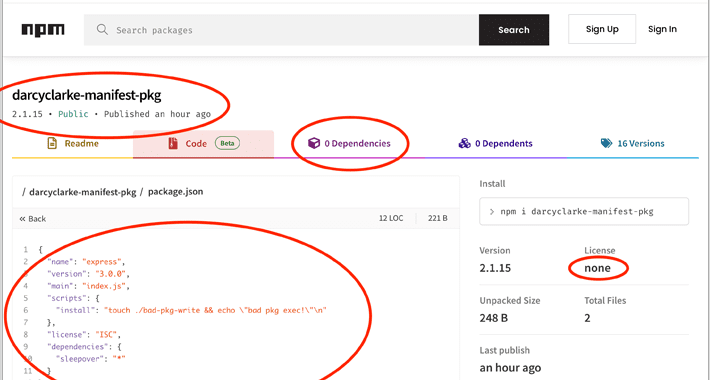
Node.js Users Beware: Manifest Confusion Attack Opens Door to Malware – Source:thehackernews.com
Source: thehackernews.com – Author: . Jul 05, 2023Ravie LakshmananSupply Chain / Software Security The npm registry for the Node.js JavaScript runtime environment is susceptible to what’s...
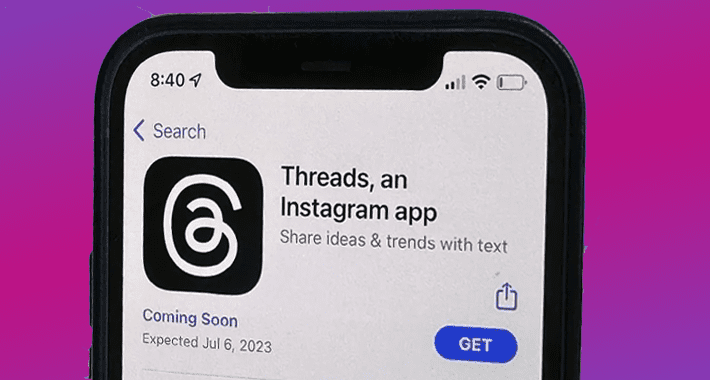
Instagram’s Twitter Alternative ‘Threads’ Launch Halted in Europe Over Privacy Concerns – Source:thehackernews.com
Source: thehackernews.com – Author: . Jul 05, 2023Ravie LakshmananPrivacy / Social Media Instagram Threads, the upcoming Twitter competitor from Meta, will not be launched in the...
Hackers Steal and Sell Victims’ Bandwidth Using ProxyHacking – Source: www.govinfosecurity.com
Source: www.govinfosecurity.com – Author: 1 Cybercrime , Cybercrime as-a-service , Endpoint Security Attackers List Compromised Servers on Bandwidth Sharing Platforms for Profit Akshaya Asokan (asokan_akshaya) •...
Banking Tech Forecast: Cloudy, With a Chance of Cyber Risk – Source: www.govinfosecurity.com
Source: www.govinfosecurity.com – Author: 1 3rd Party Risk Management , Cloud Security , Governance & Risk Management Cloud Adoption in Financial Services has Soared – as...
CISA Warning! 8 Actively Exploited Flaws in Samsung and D-Link Devices – Source: heimdalsecurity.com
Source: heimdalsecurity.com – Author: Livia Gyongyoși The US Cybersecurity and Infrastructure Security Agency (CISA) added 6 flaws affecting Samsung smartphones to its Known Exploited Vulnerabilities Catalog....
Charming Kitten’s POWERSTAR Malware Boosts its Techniques – Source: heimdalsecurity.com
Source: heimdalsecurity.com – Author: Madalina Popovici Cybersecurity researchers recently published an advisory on the evolution of POWERSTAR backdoor malware and advanced spear-phishing techniques used by Charming...
HHS Data at Risk After MOVEit Hack Impacted Third-Party Vendors – Source: heimdalsecurity.com
Source: heimdalsecurity.com – Author: Madalina Popovici A third-party security breach at the Department of Health and Human Services (HHS) may have exposed the personal information of...
Report Reveals Companies Unprepared For Darknet Data Leaks – Source: www.infosecurity-magazine.com
Source: www.infosecurity-magazine.com – Author: 1 A new report by the Kaspersky Digital Footprint Intelligence team has revealed that several companies worldwide are severely unprepared when dealing...
Over Two-Thirds of FortiGate Firewalls Still at Risk – Source: www.infosecurity-magazine.com
Source: www.infosecurity-magazine.com – Author: 1 Approximately 69% of FortiGate firewalls affected by a recently discovered FortiOS vulnerability remain unpatched, according to security researchers at Bishop Fox....
Mexican Hacker Unleashes Android Malware on Global Banks – Source: www.infosecurity-magazine.com
Source: www.infosecurity-magazine.com – Author: 1 Security researcher Pol Thill has identified a Mexico-based hacker known as Neo_Net as the mastermind behind a series of cyber-attacks targeting...
Swedish Data Protection Authority Warns Companies Against Google Analytics Use – Source:thehackernews.com
Source: thehackernews.com – Author: . Jul 04, 2023Ravie LakshmananPrivacy / Online Security The Swedish data protection watchdog has warned companies against using Google Analytics due to...